With this ebook, we'll help you prioritize which vendors need the most attention with an in-depth security assessment – such as those with low security ratings, or critical vendors that maintain constant contact with your company’s systems.
Third-Party Risk Management Policy
What is a TPRM policy?
A third-party risk management policy is a structured framework that outlines how an organization identifies, assesses, manages, and mitigates risks associated with its external vendors and suppliers. These third-party relationships, while essential to business operations, can significantly expand an organization’s cyber risk exposure. Effective third-party risk management (TPRM) policies are crucial for reducing vulnerabilities, safeguarding sensitive data, ensuring regulatory compliance, and ultimately maintaining business resilience.
A comprehensive third-party risk management policy serves as a foundational document that guides an organization's security posture concerning its vendor ecosystem. It clearly communicates expectations internally and externally, supports accountability, and helps align third-party management processes with broader business goals.
The importance of vendor risk management policy
If you’re experiencing frustrating delays and procedural roadblocks during your vendor management process, you’re not alone. Security managers are seeing an increase in the number of third parties integrating with their business, and Gartner reports that “60% of organizations are now working with more than 1,000 third parties.”
The problem lies in inefficient programs that can’t handle the onslaught of new vendors from relying on manual coordination with the right business departments needed to manage a vendor. Onboarding, sometimes dreaded by those on a company’s security team or legal department, requires resources and cooperation from both the organization and the vendors to ensure the proper documentation and data is communicated between the two companies.
The organization is responsible for properly evaluating a third party during onboarding to ensure their processes are aligned. Whatever a company misses during onboarding is on them, which is why time is taken to cover all the bases. Onboarding does not have to be a time consuming and costly process if security leaders have the right vendor management policies in place to work together with their business teams.
Key components of third-party risk management policy
An effective TPRM policy should include the following critical components:
- Clearly defined roles and responsibilities to ensure accountability, from risk analysts and procurement teams to senior executives
- Standardized vendor assessment procedures that provide consistent criteria for evaluating third-party security posture, leveraging objective data, such as continuous monitoring results, to validate vendor responses
- Defined risk categorization criteria to prioritize vendors according to their potential impact on security and compliance
- Continuous monitoring for real-time insights into vendor security performance, enabling rapid response to emerging threats
- Incident management procedures to swiftly address third-party security breaches or vulnerabilities, minimizing business disruption
Integrating TPRM into broader enterprise risk management and governance programs is a critical best practice. This holistic approach ensures that third-party risks are not managed in isolation but are instead contextualized within the organization's overall risk profile and business objectives. Regularly reviewing and updating the policy to adapt to evolving threats, technological changes, and regulatory requirements ensures ongoing effectiveness and relevance.
Third-party risk management policy template
Implementing a consistent and thorough third-party risk management policy can be streamlined through a well-structured template. Such a template typically includes sections such as:
- Scope and objectives
- Roles and responsibilities
- Risk assessment procedures
- Vendor categorization
- Monitoring and continuous evaluation
- Incident response protocols
- Regulatory compliance requirements
This template should be adaptable to an organization’s specific risk tolerance and business objectives, making the complex task of policy creation more efficient.
Leveraging pre-existing, robust templates provided by cybersecurity risk management platforms like Bitsight can accelerate policy development. These templates often integrate evidence-based cyber risk intelligence, automating the assessment and onboarding processes, thus improving both speed and reliability in vendor evaluations.
Where can you adapt your TPRM policy process?
As part of the procurement process, it is a security professional’s job to evaluate potential vendor’s security position and management. When someone on your company's HR team comes to you with a new, potentially cheaper vendor to manage employee benefits, what are the policies that come into play? Maybe the first step is pulling up the standardized document of “new vendor due diligence” requirements and forwarding it to the vendor, or discussing the budget for new vendors with the finance team. These steps are common in many organizations when it comes to vendor management.
Just because there are common vendor onboarding strategies doesn’t always mean they are the most efficient way to go about the process. What if there were security standards set before a third party was even introduced to a company that would eliminate them from consideration? Including security guidelines as your policy for new vendors that are available across the organization enables the business by keeping cybersecurity at the forefront of third-party risk management.
Establishing a risk tolerance
Deciding on what the maximum risk you’re willing to take with a vendor will help narrow down the list of vendors to evaluate, giving the security team back some of the time they spent evaluating vendors. Instead of spreading their resources thin, security professionals can focus deeper on the companies that matter to them.
One way to establish the risk you're willing to take with your vendors, as well as how to keep that standard even across all departments, is through a security rating. Bitsight for Third-Party Risk Management provides an external, objective view into a vendor’s cybersecurity to help users obtain a real, trusted view of their third parties.
Bitsight allows users to compare their third parties’ security ratings, even when the companies have experienced different types of cybersecurity events. If a company can use a Bitsight security rating to weed out third parties who fall below the allowed risk threshold, the vendor selection and onboarding process can be narrowed down to only companies that have secure systems in place.
Setting tiers to enable easier onboarding
Finding a risk threshold your organization is comfortable with for new vendors is a great way to implement efficient vendor management policies. An impactful step you can then take to further enable your third-party risk program to grow and properly manage your vendors is to tier your third parties based on risk and criticality.
Vendor criticality is one factor to consider when deciding on the inherent risk a third-party holds, and can also be used to help group your vendors into easy-to-manage tiers. Tiering your third parties will group all of your existing vendors into tiers based on how close they are to sensitive company information. With Bitsight, organizations can see a suggested tier for each vendor determined by the nature of the third party and how risky their cybersecurity standings are.
Policy change as a result of tiering
When a company tiers their vendors, they can then implement policies for all vendors that fall into specific tiers, removing the inefficiencies when certain vendors are over-assessed or under-assessed. Top-tier vendors might require continuous monitoring of their cybersecurity standings to prevent malicious activity before it happens, because even a slight breach in their systems could lead to major damage to the companies they’re operating with. Lower-tier vendors might only need to be evaluated when a breach is detected.
Where the third party falls in your organization’s tiering system can help determine the level of vendor risk assessment they require. Tiering removes excessive work on vendors that don’t require it so that the same resources can be used to better manage top-tier vendors.
Where you’ll see improved efficiency
Finding the right third-party management policies can make a huge difference on program efficiency, which in turn allows the company as a whole to function without cybersecurity as a roadblock. The right vendor management policies will save the company money by speeding up the process of onboarding vendors using their Bitsight security rating. Security ratings allow companies’ security programs to be compared with each other because they are calculated looking at the same types of data and independent of the size of the organization.
Tiering and using risk thresholds creates a standard way of looking at a vendor across all company units because everyone who deals with vendors is clear on what the company risk tolerance is. When everyone is on the same page there is limited room for confusion or need for multiple meetings when working with a new vendor. Implementing the right vendor management policies will allow your security team to do more with the same resources they already have.
Transform your vendor management policy
Many businesses are being forced to accept change in their processes already with the new pandemic-focused world. While you are already experiencing change in your business, now is a great time to introduce cybersecurity policies that highlight efficiency and can save your organization time and money.
40 questions you should have in your vendor security assessment
The 'F' Word: Rethinking Security Frameworks for an AI-Driven World
How to Create a TPRM Program
Third-party risk management program best practices
As digital transformation picks up pace, companies are working with more vendors than ever. According to Gartner, 60% of organizations now work with more than 1,000 third-party vendors — including partners, sub-contractors, and suppliers.
These third parties are essential to helping businesses grow and stay competitive, but third parties can also introduce unwanted cyber risk and overhead into the organization.
This presents a unique set of challenges and potential risks for security professionals. Cybersecurity can’t be an obstacle to business growth, in fact it must be a facilitator. As such, security teams must keep up with the needs of the business and move faster to onboard vendors. They must also prioritize their limited resources to achieve the highest risk reduction in the most efficient way.
To achieve this, security managers must find ways to drive greater maturity across their third-party risk management (TPRM) program. Here are five areas where improved processes and technology can help.
1. Apply TPRM process, policy, & procedures consistently
Critical to creating any successful third party risk management program is ensuring that all business functions – particularly marketing, finance, legal, and procurement – agree upon and consistently apply third party risk management processes, policies, and procedures when onboarding new vendors.
To establish these procedures, security managers should work with the business to determine acceptable risk threshold policies and pre-screen vendors accordingly. If a third-party doesn’t meet these security guidelines, they can then be eliminated from the procurement process – allowing security teams to focus already stretched resources on evaluating vendors that have more desirable security postures.
Another crucial consideration is whether to adapt security assessments based on the partnership the organization will have with the vendor in question. After all, no two vendors are the same. Each third-party presents different risk levels, and therefore merits different treatment.
Security leaders should also consult with legal and finance teams to devise contractual controls and enforceable language to ensure compliance with those thresholds throughout the life of contracts.
2. Align cross-functional teams around risk reduction
A key characteristic of organizations with immature third-party programs is that various business disciplines often tackle third-party cyber risk reduction in siloes. Legal or procurement teams may have their own vendor screening criteria that are at odds with policy and procedures adopted by security professionals.
By contrast, in successful and mature third-party programs, these cross-functional teams are aligned around cyber risk reduction. They understand why it’s important, and they have adopted a collaborative vendor onboarding and risk management process that doesn’t roadblock them but keeps up with the speed of the business and what it’s trying to accomplish.
3. Champion TPRM outcomes in the boardroom
Cyber risk is a huge priority for the board, including the risk posed by third-party vendors and suppliers. They want greater oversight of these parties’ security risk profile through metrics and cyber security KPIs, but they also want security managers to link cybersecurity to business outcomes.
In a successful TPRM program, security leaders champion their achievements in the boardroom and communicate the impact of their TPRM initiatives through the lens of business value whether it’s reducing the time and costs involved in onboarding new vendors, driving cross-team collaboration around risk reduction, or enabling the business to move with confidence into new areas of growth.
Armed with this information, the board can focus on getting further behind security initiatives or adding additional resources.
4. Adopt third party risk management technology & automation
Immature programs have traditionally relied on questionnaires and spreadsheets to assess and track third-party risk. These manual tools are sufficient if the organization is starting out. However, as it expands and adds more suppliers, security leaders should consider adding purpose-built TPRM technology and automation tools to manage a successful program at scale.
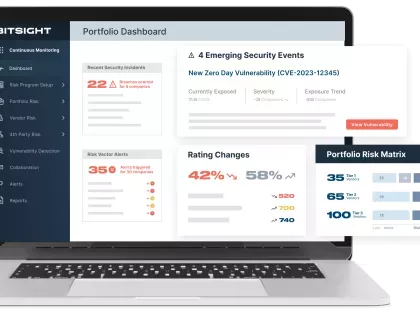
For instance, using Bitsight Vendor Risk Management (VRM) as part of a comprehensive third-party cyber risk management program, security professionals can immediately and automatically expose third-party cyber risk during the onboarding process. Then, instead of wasting time doing long, full-blown assessments on every vendor, they can allocate resources to critical vendors that require greater due diligence for risk identification. Throughout the vendor lifecycle, Bitsight VRM enables you to evaluate vendors with speed and confidence with automated workflows, pre-populated vendor profiles and objective data and insights.
5. Continuously monitor vendors
Cyberspace is constantly evolving, as is third-party risk. It’s important, therefore, that an organization’s security assessments go beyond point-in-time snapshots.
Once the vendor onboarding stage is complete, companies can use Bitsight Security Ratings to continuously monitor for any shifts or changes in their vendors’ security posture and receive alerts when these ratings drop below previously agreed-upon risk thresholds. If the alerts are critical, companies can then use Bitsight VRM to follow-up with the vendor to conduct further assessments and mitigate the identified risk.
With the help of Bitsight, organizations can obtain a comprehensive perspective of risk in their supplier portfolio, allowing them to easily identify and prioritize critical third-party risk matters over less pressing ones.
Based on these insights, organizations can then have honest, data-driven conversations with their vendors about their cybersecurity postures, communicate exactly where risk may be present, and work collaboratively towards remediation.
Move beyond a checkbox approach to third party risk management
A successful and mature TPRM program transforms the way organizations manage third-party cyber risk helping them overcome one of the largest obstacles to digital transformation and business growth. Importantly, organizations at the top of the maturity ladder view third-party risk management through an operational efficiency lens – finding ways to reduce vendor onboarding time and costs – rather than solely as a check in the box or compliance necessity.

Comprehensive TPRM: A 10-Point Framework
Strengthen your third-party defenses—and when vulnerabilities hit, deploy AI-accelerated workflows to prioritize threats and drive rapid response.
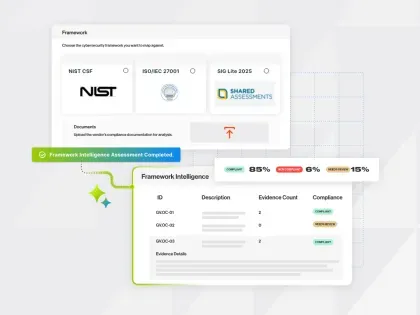
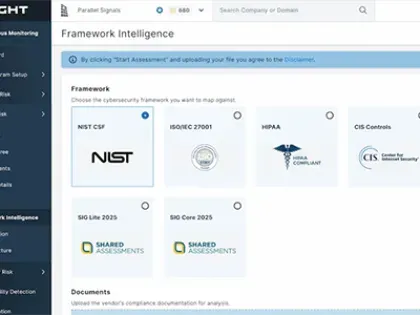
Framework Intelligence
The Vendor Management Lifecycle
The vendor management lifecycle
The vendor management lifecycle is the structured approach organizations take to manage their relationships with third-party suppliers from initial selection through the end of the partnership. This comprehensive process ensures that vendors deliver value, reduce risks, and comply with regulatory requirements throughout the duration of their engagement. Effective vendor management goes beyond procurement, emphasizing continuous risk management and strategic alignment with business objectives.
The more technology your organization adopts, the more exposed it becomes to third-party risks. Consider these statistics:
- 79% of businesses are adopting technologies faster than they can address related security issues.
- 73% of organizations have experienced at least one significant disruption caused by a third-party.
Organizations have responded to these risks by implementing robust third-party risk assessment procedures. However, a common mistake is to view vendor risk management as a one-time activity, typically conducted prior to onboarding a new vendor.
Since third-party risks are constantly evolving, it's crucial to evaluate vendor security at every phase of the vendor lifecycle. Let’s look at the three distinct phases of your vendor lifecycle management process and steps you can take to assess and remediate vendor risk along the way.
Phases of the vendor lifecycle
Understanding the phases of the vendor lifecycle is crucial for maintaining control over your third-party relationships and mitigating risks. The vendor lifecycle typically includes the following phases:
Phase 1: Vendor selection and due diligence
The process begins with clearly defining business requirements and identifying potential vendors that align with these objectives. Many teams are involved in sourcing new vendors, each with conflicting priorities. For example, the marketing team considers the software solution's features, procurement considers its cost and value, and security and risk management teams consider its security controls. It can be helpful to narrow down vendor selections using documents like RFIs and RFPs.
As soon as you have narrowed down your list of vendors, it's time to start due diligence. Security questionnaires are an important part of this process, but questionnaires offer a single point-in-time view, and vendor responses may be subjective and difficult to verify.
Furthermore, this stage of the vendor lifecycle management process is highly manual, involving one-off spreadsheets to track and compare responses, multiple follow-ups via email, and calendar reminders.
Automated vendor risk assessment capabilities and tools – like Bitsight Vendor Risk Management (VRM) – can solve these problems. Bitsight VRM automates the security assessment process and reduces dependency on email follow-up and other manual workflows. The platform also layers in independent validation of vendor responses using security ratings, so that you can quickly understand a vendor’s true security posture and detect red flags in their responses.
Once you’ve gathered all necessary documentation, you can store it centrally, streamline document sharing across internal stakeholders, and invite your vendors to connect and collaborate for more expeditious risk discovery and remediation – before they enter your supply chain.
Phase 2: Contract and onboarding
Efficient vendor onboarding establishes clear expectations and integrates the vendor into organizational processes. During onboarding, critical documentation, contracts, and SLAs (service level agreements) are finalized, ensuring both parties clearly understand their obligations. This phase includes other critical steps to the vendor management process:
1. Performance management
Regularly assessing vendor performance against established KPIs and SLAs is essential. After a vendor is awarded a contract, it’s important to keep a pulse on that vendor’s security performance across the life of the relationship. Typically, this involves conducting periodic security assessments or audits. While these assessments are important, third-party cyber risk can emerge at any time. The answer: continuous monitoring.
Continuous monitoring tools and periodic reviews help organizations detect and mitigate emerging risks quickly, maintaining supplier accountability and quality of service.
2. Risk management
Throughout the vendor relationship, ongoing risk management practices, including cybersecurity monitoring and compliance audits, are critical. Proactively managing third-party risks protects organizations from potential threats, data breaches, and regulatory non-compliance.
Instead of a point-in-time cybersecurity audit, Bitsight TPRM delivers a near real-time snapshot of your third parties’ security performance from onboarding to contract termination.
Using Bitsight TPRM, you can automatically and continuously discover evolving supply chain threats and remediate any security gaps a threat actor may exploit. These can include misconfigured and unpatched systems, open access ports, and even human behavior. Whenever a risk is detected, you are alerted so you can act quickly.
Bitsight can also shine a light on vendors who warrant more periodic in-depth assessments, such as those whose security ratings consistently fall below pre-agreed security thresholds or SLAs.
Phase 3: Post-contract (Renewal or termination)
The final step in the vendor lifecycle management program is Renewal or Termination. At this final phase, organizations evaluate the vendor relationship to determine whether to renew contracts, renegotiate terms, or terminate the partnership based on performance outcomes, evolving business needs, and risk exposure. Even if a vendor is offboarded, third-party cyber risk can continue beyond the end of the contract, especially if the vendor had access to your sensitive data, such as a cloud service provider or payroll company.
To mitigate this risk, review the vendor’s contract to determine access levels. Then, take steps to ensure that all access has been severed and all sensitive information erased. Don’t forget the extended supply chain. Use Bitsight to visualize upstream and downstream dependencies within your vendor relationships. In this way, you can determine if any of your vendors' vendors had access to your data and remove these connections.
Vendor lifecycle management best practices
Managing outside vendors effectively can place you ahead of your peers, but finding which areas of vendor lifecycle management you can improve on is difficult with competing priorities. Focusing on the critical onboarding phase, your reassessment process, and the way you communicate your risk summaries to the board are three areas where you can start.
Bringing on a new vendor might seem simple: You just pick a vendor with the right capabilities and the right price and get the paperwork signed. But those who have to manage third party risk know that it’s rarely so simple. That’s because third-party risk management is a complex task that is full of difficult decisions and requires cooperation with multiple business departments like legal, procurement and finance, as well as the hard work of assessment and onboarding the vendor and managing them over the course of the vendor lifecycle.
As you think about your TPRM program, ask yourself these questions:
- Are you doing things the way you are because you’ve always done them that way?
- Are there opportunities to make your program more efficient or reduce cost?
- Is your program struggling to approach TPRM from a business enablement perspective?
If you’ve answered yes to any of them, then it’s probably time to rethink the policies, processes and communication strategies for your TPRM program. Below are three critical stages of your program that may be ripe for a revamp.
1. Set the right onboarding policies
It is crucial to find efficient onboarding policies during your vendor onboarding stage to ensure that you are working with the most secure third-parties. Having a stable and readily followed onboarding processes with policies that are supported across the business will also present your company as a reliable organization to partner with, and will help you attract the best vendors in the industry.
Here are three areas you can optimize your policies to ensure efficiency in this area of your TPRM program:
- Setting a minimum requirement for security measures your third-parties have to hit before they can be onboarded into your internal systems efficiently narrows down your daunting list of vendors. Bitsight for Third-Party Risk Management provides third-party security ratings to help decide between vendors in a fraction of the time.
- In the current climate of primarily remote workforces, ensuring quick communication and approvals can be difficult if the steps were not previously mapped out prior to the COVID-19 pandemic. Procurement, legal, and finance will all need to be involved at some point throughout the onboarding process for various approvals and contract points, so try bringing a representative from each department early during vendor assessment.
- Communicate policies and third-party decisions to all functional business unit leaders and managers. Problems arise when information isn’t clearly communicated across the board to all departments. Connecting the security team to the rest of the organization is important when securing resources from the board. Including all business units when giving updates on third-parties is a good policy for enabling the individual parts of the business to support each other.
2. Maximize efficiencies within the reassessment process
Failing to focus on efficiency throughout the entire lifecycle can end up erasing your hard work during onboarding. Promoting efficiency during the assessment stages allows for successful risk mitigation, even as your list of vendors continues to grow. Often we see security professionals relying on traditional methods when evaluating vendors, like long lists of vendor questionnaires. Maturing your vendor risk management program with a tiering structure and continuous monitoring technology will enable your organization to grow without being held back by outdated vendor management strategies.
Tiering
Security professionals know that some vendors are more important to their organization than others. Grouping these vendors in structured tiers based on the inherent risk you’re willing to accept will help focus your resources during the assessment process. Bitsight for TPRM assists users with tiering vendors by setting rating requirements for different tiers. For vendors working directly with sensitive company information, stricter limits can be placed on how low their rating is allowed to drop before the user is alerted. For the less critical vendors, more flexibility is given to inherent risk. Instead of treating all your third-parties the same, tiering allows security teams to clearly see which third-parties require more frequent and in-depth assessment.
Continuous monitoring
You can also highlight vendor lifecycle efficiency by removing the yearly schedule for assessing your third parties, and instead work under a continuous monitoring system. Continuous monitoring gives security managers full-time insight into the threats and status of their third-party ecosystem to tackle malicious activity to a vendor’s system before even being notified by the vendor themselves. Bitsight’s TPRM software will notify users when a third-party experiences a sudden drop in their score, and point the security team directly to the vulnerability point. Continuous monitoring also takes security management back into the hands of the TPRM team. You don’t need to rely on your vendors being timely and forward in a security report if you have access to the data on your own account.
3. Successfully communicate risk
Security professionals can’t afford to overlook the importance of communicating with your organization’s leadership team. Generally speaking, being prepared to discuss third-party risk initiatives and positioning with your organization’s leaders will help secure cybersecurity resources. Minimizing confusion with the board with help build trust between the security leaders and the company decision makers. Here are two important factors to consider to practice efficient communication with company leaders:
- Context: Many security leaders forget that the metrics and terminology they use in their day-to-day operations are not commonly used by the board, which adds a layer of difficulty and skepticism when it comes to communicating the numbers and requesting budget. It is important to also include context surrounding how the metrics relate to the overall business. Connecting the dots for how your numbers are impacting the company’s overall goals, including information about the industry averages and your company’s historical performance, and providing a high-level overview describing different malicious activities you might discuss to help when communicating with your board.
- Solutions: When board members are presented with the status of how our security systems are performing, the next step is to consider what will be worked on in the future to either continue or improve what’s being done. A security professional should bring both tactical and strategic examples of team goals for the future in order to best communicate trust with the board. Tactical steps are good for board members to see a detailed, specific set of steps the security team can take to reach their program goals. Also taking a strategic approach to discussing vendor management will help the board compare your team to company competitors.
Automate the vendor lifecycle management process
Navigating the vendor lifecycle management process can be challenging – especially as your vendor portfolio grows. Traditional methods are highly-manual, time-consuming, and error-prone. They are also hard to scale across the evolving third-party risk landscape.
But with Bitsight’s suite of powerful automated vendor risk management tools, you can confidently manage risk throughout the entire vendor lifecycle.

10 Critical Elements to Build a Resilient TPRM Program
Working hard to stay on top of vendor risk? We can help. This practical guide outlines 10 critical steps you can take today to reduce exposure, boost collaboration, and drive risk clarity at scale.
What is Zero Trust?
What is Zero Trust?
Zero trust is a cybersecurity approach that restricts network access so only the right people are accessing the specific information they need—and nothing more. Zero Trust is is built on the principle that no user, device, or network segment should be implicitly trusted, regardless of location or identity. Instead, every access request is continuously verified based on contextual factors such as identity, device posture, and real-time risk analysis. In a world increasingly characterized by sophisticated threats and expanding digital ecosystems, Zero Trust emerges as a foundational model for securing modern organizations.
The term was coined by John Kindervag at Forrester Research in 2009, and related frameworks include Google’s BeyondCorp and Gartner’s CARTA. Today, it’s a key component of cybersecurity programs, especially in organizations that outsource business functions to third-party vendors who need remote access to their networks.
Here’s everything you need to know about the basic principles of Zero Trust and how to apply them to your third-party risk management program (TPRM) to create more secure remote access connections.
Zero Trust principles
- Least-privilege access, which means increasing granularity on permissions for internal users and third-party vendor users. Apart from limiting who accesses the network, it also limits what services, devices, or applications; where; and when they’re accessed.
- Logs and audits, which help monitor vendor access and verify that they are not violating any access restrictions, either through malicious activity or just careless actions.
- General security mechanisms to apply advanced controls to third-party relationships, such as multi-factor authentication (MFA), identity access management (IAM), and a strong password policy that also disables identities once they are no longer working for the organization.
What is Zero Trust architecture?
Zero Trust Architecture (ZTA) is the implementation framework that applies the Zero Trust principles to IT environments. At its core, ZTA ensures that every access attempt, whether internal or external, is treated as potentially compromised. This approach removes implicit trust and focuses on continuous authentication and authorization. ZTA employs micro-segmentation to isolate networks and limits user access to only what's absolutely necessary, significantly minimizing potential damage from third-party breaches.
What is Zero Trust security?
Zero Trust Security extends beyond network architecture to encompass comprehensive policy enforcement and continuous monitoring of all access points. It integrates advanced technologies such as identity management, multi-factor authentication (MFA), encryption, endpoint detection, and response (EDR) solutions. By constantly validating users and devices, Zero Trust Security proactively identifies and mitigates threats before they can cause significant damage, dramatically improving an organization's overall cybersecurity posture.
What is Zero Trust in cybersecurity?
In cybersecurity, Zero Trust embodies a fundamental shift from traditional perimeter-based security approaches to one of continuous verification and least-privilege access. Rather than assuming trust based on network location, Zero Trust mandates verification at every step. This strategy significantly reduces the likelihood of lateral movement during cyberattacks, limiting both exposure and impact.
What are 5 pillars of Zero Trust?
The Zero Trust model is built upon five foundational pillars:
- Identity: Ensuring robust authentication and verification of user identities.
- Device: Continuously assessing device security posture and compliance.
- Network: Applying micro-segmentation to secure internal communications.
- Application: Protecting application layers with context-aware access controls.
- Data: Implementing strong encryption and access restrictions around sensitive data.
How to implement Zero Trust
The Zero Trust technique revolves around continuous validation and strict access controls. It leverages advanced analytics and real-time cyber threat intelligence to provide context-aware security decisions. This technique ensures that even legitimate access attempts undergo stringent validation processes, constantly adapting based on the dynamic risk landscape.
Implementing Zero Trust involves several critical steps, beginning with an understanding of your current security landscape and business objectives. Organizations must:
- Identify critical assets and define sensitive data and systems.
- Map transaction flows across network segments and user access points.
- Establish robust identity and access management controls, integrating MFA and least-privilege access.
- Continuously monitor and analyze traffic for anomalous activities using cybersecurity intelligence solutions, such as Bitsight's Cyber Threat Intelligence suite.
- Employ micro-segmentation and encryption strategies to isolate and protect critical resources effectively.
Implementing Zero Trust in your organization
There are some technologies and infrastructure settings that can help organizations.
In August 2020, NIST released the NIST Special Publication 800-207: Zero Trust Architecture, which describes the components of a zero trust architecture, possible design scenarios, and threats. It also offers a roadmap to implement its main principles.
Dedicated solutions like Bitsight Vendor Risk Management (VRM) allow you to manage custom privileges for your third-party vendors based on job titles, departments, and roles. This makes it easier to manage the provisioning and de-provisioning of user permissions, with network access based on the least-privilege principle and granular controls to restrict third-party remote access to only the application they need and nothing else.
How does Zero Trust fit into third-party risk management?
Third-party relationships significantly expand an organization's attack surface, creating substantial cyber risk. Integrating Zero Trust principles into third-party risk management (TPRM) ensures every vendor and external partner undergoes continuous monitoring and strict verification processes. Solutions like Bitsight's Continuous Monitoring for third parties provide real-time insights into the security posture of your entire vendor ecosystem, aligning effectively with Zero Trust methodologies to identify and mitigate risks rapidly.
By adopting Zero Trust, organizations can better manage their cybersecurity risks, secure their extended digital ecosystems, and create resilience against evolving threats.
Why do you need to consider Zero Trust in your TPRM program?
A study by the Ponemon Institute found that:
- 63% of organizations said remote access is becoming their weakest attack surface
- 51% experienced a third-party data breach in the 12 months prior to the study
- 74% said it was the result of giving too much privileged access to third-parties
In addition, the accelerated digital transformation shifted the focus of security teams to more tactical needs, such as enabling remote workers, securing changes in operations to ensure business continuity, migrating to the cloud, re-assessing third-party and supply chain risks, accelerating and increasing vendor onboarding, and more.
In a world where the network perimeter is enlarged and has blurry boundaries, zero trust allows organizations to constantly re-evaluate in real-time anything and anyone that touches their data.
How is Zero Trust different from other approaches?
You’ve probably heard “trust but verify” in the context of cybersecurity and third-party risk. To that, zero trust responds: “Never trust, always verify.”
According to this approach, devices should not be trusted by default, even if they are connected to a permissioned network such as a corporate LAN and even if they were previously verified. Authentication or verification is always needed before granting access to sensitive data or protected resources.
Zero trust deems all resources as external to the organization’s network, and continuously verifies users, resources, devices, and applications before granting the minimum level of access required. In contrast, the traditional approach automatically trusted users and endpoints within the organization’s perimeter.
But time is precious and there aren’t enough hours in the day to review every access attempt. In order to make this concept applicable, zero trust uses broad data sets and dynamic risk-based policies to aid access decisions and perform continuous monitoring.
Another component of a secure third-party vendor ecosystem
Organizations make significant efforts to control and secure the access given to third-party vendors, in order to avoid data breaches, security incidents, or noncompliance. Zero trust is another tool for mature enterprise risk management practices, establishing the framework for minimizing third-party risk on every network access.
With grounds on continuous verification, third-party vulnerabilities and insufficient security practices can be properly addressed.
While no security and defense strategy is immune, and data breaches will continue to happen, zero trust reduces the attack surface and limits the impact of a cyberattack.
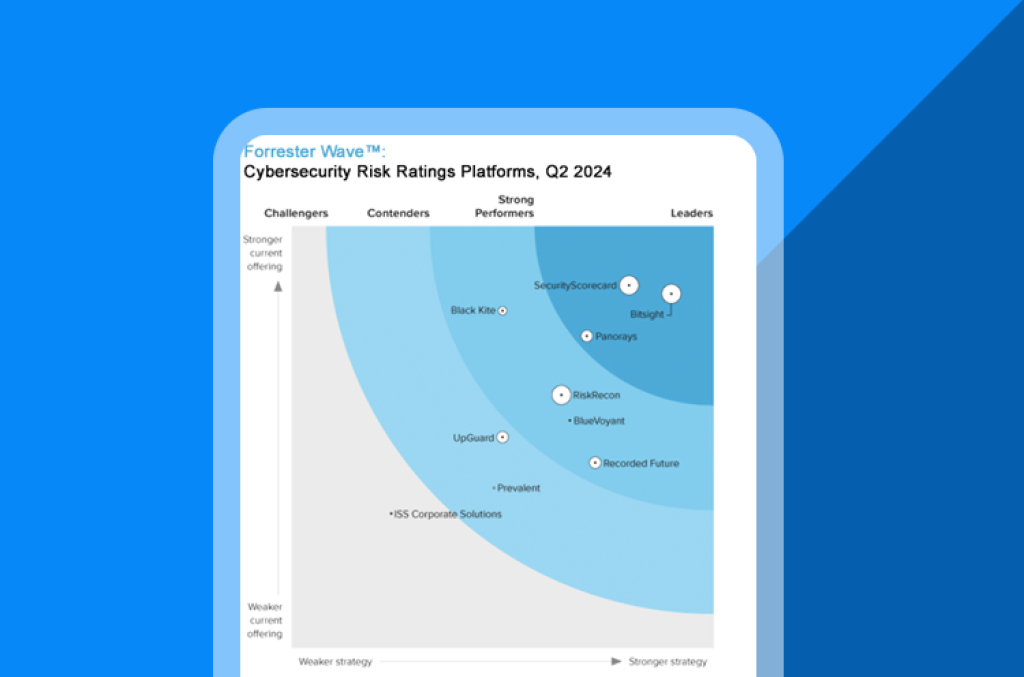
Navigate Cyber Risk Ratings with Confidence
Cyber risk ratings platforms are proliferating—and not all are built equal. Forrester’s 25‑criterion evaluation reveals who’s delivering accuracy, scale, and vendor credibility. Use it to shortlist tools aligned to your risk appetite and control framework.
Bitsight Continuous Monitoring - PPC
Automated visibility across your supply chain: Using AI in practical cases on cyber regulations

Third-Party Risk Management Tools
As the global supply chain landscape grows more complex, organizations increasingly depend on third-party relationships, inevitably expanding their attack surface. Effective third-party risk management (TPRM) tools have become essential, helping cybersecurity teams reduce risk, meet compliance requirements, and enhance visibility across their vendor ecosystem.
Effective third-party risk management, however, can be extremely challenging for even the most mature organizations. Many providers offer tools that claim to make TPRM easier and more comprehensive — but which of these solutions and tools do you really need?
In this guide, we'll explore ways to help you understand, evaluate, and implement the right third-party risk management tools for your organization.
What are third-party risk management (TPRM) tools?
Third-party risk management tools enable cybersecurity teams to assess, monitor, and mitigate risks posed by external partners. Unlike traditional vendor management systems, TPRM solutions offer cybersecurity-specific capabilities designed to handle complexities associated with third-party cyber risk, compliance, and security assessments. These tools automate processes, reducing manual effort and allowing organizations to scale risk management effectively.
Key features and capabilities of third-party risk management tools
When evaluating TPRM tools, look for these essential features:
Automated risk assessments
Streamline the assessment process, minimizing manual efforts and human error.
Continuous monitoring
Real-time alerts and insights into third-party security posture.
Risk scoring & benchmarking
Provides actionable insights by quantifying and prioritizing risks.
Dark Web Intelligence for Supply Chains
Bitsight is the only third-party monitoring solution which offers third-party dark web intelligence to detect early signs of real-world targeting and exposure across your vendor ecosystem beyond what static scores can reveal.
Integration capabilities
Compatibility with your existing security architecture, such as GRC, SIEM, and IAM solutions.
Advanced TPRM tools also offer intuitive dashboards and reporting functionalities, empowering cybersecurity teams with actionable data for decision-making.
Common TPRM tools
There’s no one-size-fits-all approach; a number of variables will determine the best course of action for your business. However, whether you’re launching, growing, or optimizing your TPRM program, there are certain tools that any organization should have.
Integrated risk management software
Even if your organization only has a handful of third-party vendors, it’s still important to use a management system to keep track of objectives and progress. This system can be as complex as integrated risk management (IRM) software, or as simple as a well-organized spreadsheet.
If your organization only has five vendors, for example, a spreadsheet would likely suit your needs and be easy enough to manage. However, if your organization has 500 or 5000 vendors, investing in a dedicated TPRM software platform is probably a better solution — in the long run, it will make the process of scaling your TPRM program much simpler.
Regulations are another factor. Companies in heavily regulated industries like healthcare, finance, and utilities — even if they don’t have a huge vendor roster — might need full-featured TPRM software, which can be used to track the delivery and receipt of security risk assessment questionnaires, schedule penetration tests and on-site visits, manage review and assessment tasks, and generate reports for compliance purposes. Wide-reaching regulations like GDPR are also making TPRM-specific software more essential.
Without a solid cyber security risk assessment tool, it’s easy for things to fall through the cracks, especially as a third-party vendor roster grows. In an area as high-stakes as cybersecurity, organizations can’t afford to let even the little things slip.
Questionnaires
Though they’re not necessarily a “tool,” vendor risk questionnaires are the backbone of most comprehensive TPRM programs. Thorough, consistent, and well-designed security questionnaires for your vendors to complete and return are critical to reducing third-party risk.
While questionnaire templates are a good place to start, the questions should always be tailored to your particular industry and concerns. As your TPRM program matures, you’ll want to start adapting questionnaires for each vendor or partner, taking into consideration their past performance and the systems and data to which they have access.
Traditionally, administering a questionnaire during the onboarding process and following up at regular intervals to ensure that security is being maintained (or better yet, improved) has been best practice. While this may change in the future thanks to third party monitoring technologies, it’s still an important part of TPRM for many companies.
However, questionnaires should not be the only component of a TPRM program — they can become inaccurate fast as new threats emerge and third-party security performance changes. Relying solely on questionnaires to assess cybersecurity gives you an incomplete picture of a third party’s security posture, so questionnaires are best utilized in addition to other TPRM tools.
Security ratings
A 2018 study found that for 88% of organizations, it took over two weeks to assess vendors’ cybersecurity using manual methods such as a cyber security risk assessment questionnaire. When each assessment requires this much effort, it’s not possible to maintain a continuous picture of third-party risk.
Continuous monitoring solutions like security ratings help cover the gaps between questionnaires by allowing companies to track third parties’ cybersecurity performance in near real time. Security ratings are a data-driven, dynamic measurement of an organization’s cybersecurity performance. Ratings are derived from objective, verifiable information and created by independent organizations. Security ratings enable you to quickly ascertain a vendor’s cybersecurity posture, track changes to their performance over time, and identify their biggest vulnerabilities.
In addition, because security ratings are easy-to-understand numbers that reflect actual cyber risk, they provide a clear frame of reference and make it easier to communicate with stakeholders about cybersecurity.
How to evaluate and choose the right TPRM tool
Choosing the right third-party risk management tool involves aligning tool capabilities with your organization's unique needs. Consider these criteria during evaluation:
- Scalability: Ensure the tool can accommodate growth in your vendor ecosystem.
- Ease of use: Select user-friendly platforms that encourage adoption across departments.
- Integration flexibility: Prioritize tools offering seamless integration with your current cybersecurity tools and processes.
- Compliance support: Verify robust support for regulatory requirements like GDPR, HIPAA, ISO 27001, and SOC 2.
Remember, the best tool should simplify and improve your risk management process, not complicate it.
Benefits and ROI of third-party risk management tools
Implementing an effective TPRM solution provides substantial benefits and measurable returns, including:
- Reduced cybersecurity risk: Decrease likelihood and impact of breaches originating from third-party vulnerabilities.
- Time and cost savings: Automating assessments and monitoring saves valuable resources, allowing your team to focus on strategic security initiatives.
- Compliance management: Simplify regulatory compliance, avoiding costly penalties associated with non-compliance.
Organizations leveraging robust TPRM tools typically report improved visibility into vendor risk, better decision-making capabilities, and a notable decrease in third-party security incidents.
Though measuring ROI on TPRM programs is not always straightforward, trusted industry analysts can help point you in the right direction. For example, the 2024 Total Economic Impact™ of Bitsight, a commissioned study conducted by Forrester Consulting, found that Bitsight’s comprehensive External Attack Surface Management and Third Party Risk Management offerings reduced cyber risk, while delivering an investment return of 297% over three years. Additionally, the solution paid for itself in less than 6 months.
Top challenges and best practices for implementing TPRM tools
While TPRM tools provide significant advantages, implementation comes with common challenges, including tool sprawl, inadequate integration, and insufficient internal alignment.
Challenges include:
- Tool redundancy: Organizations often adopt multiple overlapping tools, increasing complexity and costs.
- Limited visibility: Without proper integration, organizations struggle to gain comprehensive views of third-party risks.
Best practices for overcoming these challenges:
- Tool consolidation: Regularly evaluate and consolidate overlapping tools to streamline your vendor risk management efforts.
- Clear internal alignment: Establish clear roles and responsibilities, ensuring collaboration between security, procurement, and compliance teams.
- Comprehensive integration: Prioritize tools that offer extensive integrations, ensuring full visibility across your security landscape.
By addressing these challenges proactively, organizations can optimize their use of third-party risk management tools and realize significant cybersecurity benefits.
Final thoughts
Third-party risk management tools are critical for modern cybersecurity practices. Choosing, implementing, and optimizing the right TPRM solution can significantly reduce your organization's cybersecurity risk, enhance compliance efforts, and deliver tangible ROI.
Stay proactive, continuously assess your toolset, and leverage TPRM solutions effectively to secure your organization's third-party ecosystem.
Bitsight Third-Party Risk Management
Bitsight for Third-Party Risk Management and other Bitsight technologies provide all of the tools required to develop and support a comprehensive TPRM program. With Bitsight, you can:
- Enable your business by bringing on vendors in a timely way: With Bitsight, you can help your organization enjoy the benefits of working with vendors while summarizing and communicating the risk that is associated with each relationship. Bitsight enables you to communicate technical details to stakeholders throughout the organization, using a common language and set of easily understood metrics that enable everyone to make outcomes-based, informed decisions.
- Onboard vendors faster: Smart tiering recommendations, workflow integration, and risk vector breakdowns that identify areas of known risk can help to accelerate onboarding and making your third-party risk management program more scalable.
- Mitigate third-party risk: Make confident, data-driven decisions to prioritize resources, improve operational efficiency, and drive efficient risk reduction across your vendor portfolio.
- Improve executive reporting: Bitsight facilitates data-driven conversations with senior executives and board members by streamlining the reporting process, demonstrating how investments in security directly impact performance, and providing essential metrics and context that enable oversight of your cyber security plan.
- See a clear picture of cyber risk aligned to risk tolerance: With a clear view of critical performance information across the entire portfolio, Bitsight enables risk managers to make confident, data-driven decisions to prioritize resources that drive efficient risk reduction.
- Personalize your monitoring options: Bitsight enables organizations to select the best level of monitoring for each vendor depending on their closeness to sensitive company data, as well as set alerts for when a vendor hits a concerning change in their rating, promoting greater efficiency without overspending or underutilizing risk management technology.

10 Critical Elements to Build a Resilient TPRM Program
Working hard to stay on top of vendor risk? We can help. This practical guide outlines 10 critical steps you can take today to reduce exposure, boost collaboration, and drive risk clarity at scale.