Optimize Your Vendor Onboarding Process With Security Ratings

Third parties can play an essential role in your ability to grow your business and remain competitive. Of course, if you’re not careful, these trusted partnerships may introduce unwanted cyber risk into your organization. This is particularly true as more and more businesses are moving to mandated work-from-home models — because residential IPs account for more than 90% of all observed malware infections and compromised systems. With this widespread workforce shift, new vulnerabilities are being introduced both internally and within your third-party network, thereby increasing risk across your ecosystem as a whole.
As your third-party network continues to expand, it’s more important than ever to ensure each potential vendor goes through the necessary vetting process. But this can be a challenging feat if you don’t have all the information you need to evaluate their cyber risk posture effectively — and even more difficult if you’re facing pressure from above to accelerate your vendor onboarding process.
In order to meet the demands of the business, it’s critical to find a way to perform the necessary assessments while keeping your process as flexible and agile as possible. With Bitsight for Third-Party Risk Management, you can gain immediate visibility into cyber risks within a potential vendor’s ecosystem, enabling you to reduce your onboarding time and cost — and scale your process to assess and monitor all your vendors with the resources you have today.
An efficient and effective process
In the world of third-party onboarding, it’s important to remember one simple truth: No two vendors are the same. If you use a one-size-fits-all assessment approach, you’ll end up wasting time and resources conducting extended, full-blown assessments on non-critical vendors — thereby undermining your efforts to onboard more quickly, go to market faster, and gain a competitive edge.
Each third-party presents different risk levels, and therefore merits different treatment when it comes time to assess their cybersecurity postures. Here are four steps you can take to streamline your assessments and yield better results:
1. Group vendors by criticality
Get the most out of your valuable time by allocating resources to areas that require greater due diligence. Start by grouping or “tiering” your vendors based on how critical they are to your organization. Essentially, a “critical” vendor is one that has access to your sensitive data or provides an important service. When determining whether a particular third-party meets this criteria, consider what they’ll be used for, what type of data they’ll hold, and whether they’ll have persistent access across your network.
By grouping your vendors in this way, you’ll be able to determine whether a particular third-party needs a more in-depth assessment or requires fewer touchpoints — empowering you to achieve greater efficiencies while still effectively managing risk throughout your supply chain.
2. Evaluate third-party risk
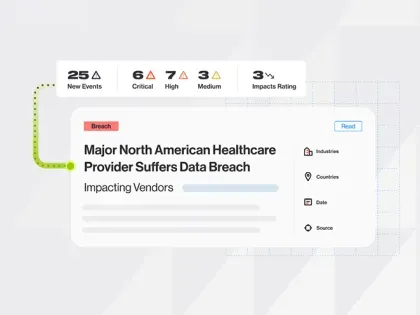
In order to measure and communicate the effectiveness of a vendor’s security program, your organization must have a common, standard set of cyber risk KPIs. Calculated using externally observable and verifiable data, Bitsight Security Ratings give you an instantaneous snapshot of each potential partner’s overall security posture. Armed with this data, you can compare vendors’ security profiles side-by-side and prioritize your assessments according to risk. You may decide, for example, that the assessment process for vendors with high security ratings may not need to be as rigorous, while the process for vendors with lower ratings could be more thorough.
3. Establish acceptable risk thresholds
Determining what your organization considers to be an acceptable risk threshold is a critical step to developing an effective third-party risk management program — but it’s not a decision for security or IT teams to make alone. Partner with legal and finance to set an acceptable risk threshold that all vendors must meet in order to be considered, and then devise policies and enforceable contract language to ensure compliance throughout the length of your partnerships. Establishing this criteria from the onset will help you to accelerate and refine the procurement process.
4. Monitor your vendors continuously
From a security standpoint, your work isn’t done after a vendor signs on the dotted line. Once your third parties are onboarded, it’s critical that you continuously monitor their security postures — ensuring that they maintain the agreed-upon thresholds. Instead of using manual processes involving spreadsheets and calendar reminders, you can save time and resources by leveraging Bitsight Security Ratings. As these ratings are updated on a daily basis, you can easily track how your vendors’ security performance is changing over time — and even set up alerts to notify you of any critical shifts.
Get the most out of your onboarding resources
By taking an adaptive, tiered approach to onboarding, you can turn third-party risk management into a business enabler — instead of a roadblock. With Bitsight Security Ratings data, you’ll be able to determine the appropriate level of assessment every time, based on each prospective vendor’s security posture and relationship to your organization.
Interested in learning more about how to save onboarding time, reduce costs, and scale your program with ease? Download our new guide, 4 Ways to Optimize Your Vendor Onboarding Process With Bitsight Security Ratings.