Cyberattacks can bring economies, public health, and national security to a standstill. Federal agencies, law enforcement, and CERTs need complete visibility into cyber risk and performance to prevent cyber show downs.

Government Cybersecurity
The cost of a data breach in the public sector.
From data breaches and espionage to sabotage of critical infrastructure, the impact of cyberattacks on federal agencies can be profound.
Source: IBM Cost of a Data Breach 2024
Why Bitsight for government organizations.
Bitsight provides the view and analytics to measure and improve security postures, comply with government-specific regulations, and mitigate risks associated with third-party vendors. Our security ratings are correlated to the likelihood of suffering a breach, and we helped shape the Principles for Fair and Accurate Security Ratings published by the US Chamber of Commerce.
Manage and Report on Security Performance.
Continuously monitor digital assets across agencies, departments, regions, or industries, and aggregate their data. Share key findings on current and historical security performance with reports generated for every audience—including policymakers and non-technical stakeholders.
Mitigate Third-Party Cyber Risk From Government Partners.
With many data breaches and security incidents stemming from third-party vendors, understanding and managing the cyber risk posed by contractors, subcontractors, and other third-parties has never been more important. Vet their security performance before bringing them onboard and continuously monitor their security posture.
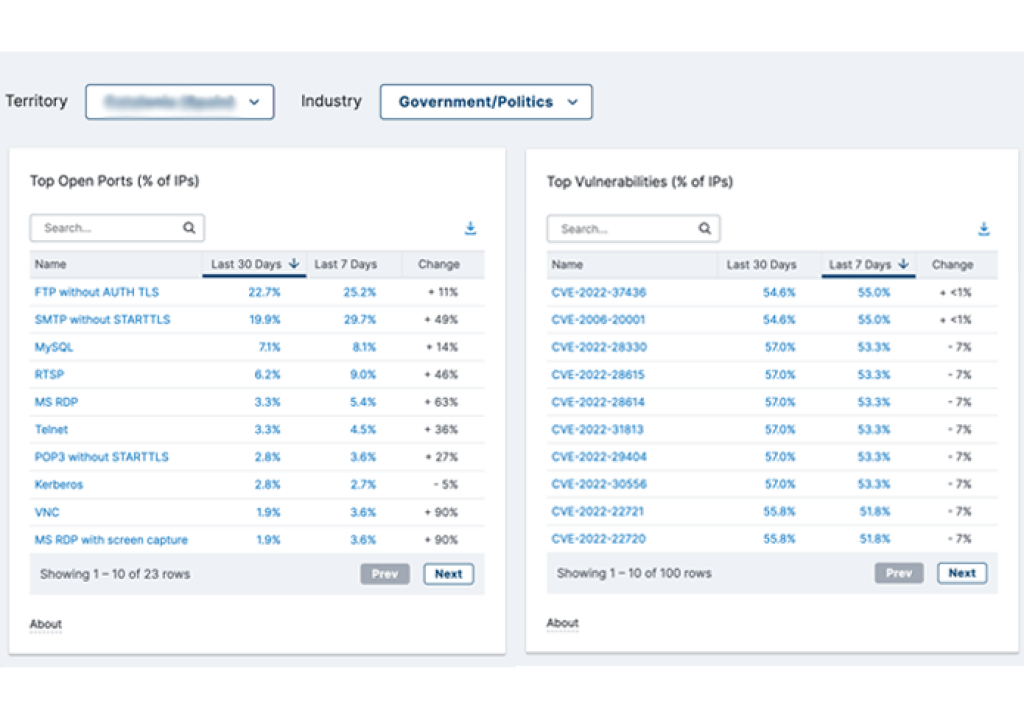
Protect Critical Infrastructure On All Fronts.
More than 180 government agencies around the world use Bitsight to benchmark security performance against other organizations, identify prevalence of vulnerabilities, and pinpoint risks to specific geographies. Use this data to inform decisions and report to senior government officials and stakeholders on the cyber health of critical infrastructure.
Bitsight helps us see where opportunities to improve the country’s cyber health exist, build trust with the community we serve, and support quick wins would otherwise not have been possible."