Detect early signs of real-world targeting and exposure across your vendor ecosystem beyond what static scores can reveal.
Dark web intelligence for supply chains
See third-party threats before they see you.
Modern cyberattacks often stem from third-party ecosystems, surfacing only after harm is done. Staying ahead requires GRC, TPRM, and SOC teams to work together using real-time insight into which vendors are actively being targeted.
Bitsight’s Dark Web Intelligence for Supply Chains features, part of the Continuous Monitoring product, deliver continuous visibility into threat activity across your vendors, suppliers, and partners. These features correlate dark web signals to help GRC and third-party risk teams detect, communicate, and remediate threats in partnership with security operations.
Align risk and security teams around shared intelligence.
Fragmented vendor monitoring leads to blind spots, operational disruption, and reputational damage. With Dark Web Intelligence, security and risk leaders can see not only what could happen, but also what is actively occurring and how to prioritize response.
Threat intelligence for the risks you don’t control.
Breach Intelligence
Breach Intelligence
Stay ahead of third-party incidents with real-time breach alerts and context, so your team can detect and respond to vendor compromises before the damage spreads.
- Monitor breach activity across your supply chain with a unified, real-time intelligence stream.
- Get enriched insights from breach data, credential leaks, public disclosures, and dark web signals.
- Understand the who, what, and where of each breach to accelerate triage and response.
- Spot lagging and emerging breach patterns to proactively assess vendor risk.
Dynamic Vulnerability Exploitability
Dynamic Vulnerability Exploit (DVE) Scores
Go beyond CVSS with real-world exploitability data that predicts which vulnerabilities are most likely to be used in attacks—so you can focus on what matters now.
- DVE scores assess the likelihood of exploitation within the next 90 days—so you act before attackers do.
- Filter 18,000+ CVEs down to the risks most relevant to your vendor ecosystem.
- Drill into exposures by ransomware association, threat actor TTPs, or other CTI attributes.
- Equip GRC, TPRM, and SOC teams with a common view of risk grounded in real-world attacker behavior.
Threat Insights
Threat Insights
Understand which vulnerabilities matter most by combining attacker behavior, exposure context, and threat severity—so you can prioritize action based on real-world risk, not just theoretical CVEs.
- Focus on exposures actively targeted by adversaries using MITRE ATT&CK–mapped TTPs.
- View findings in the context of known threat actor behavior, not just scores.
- Combine threat intel with attack surface and supply chain data for unmatched context.
- Identify which adversaries are most likely to target your organization or vendors.
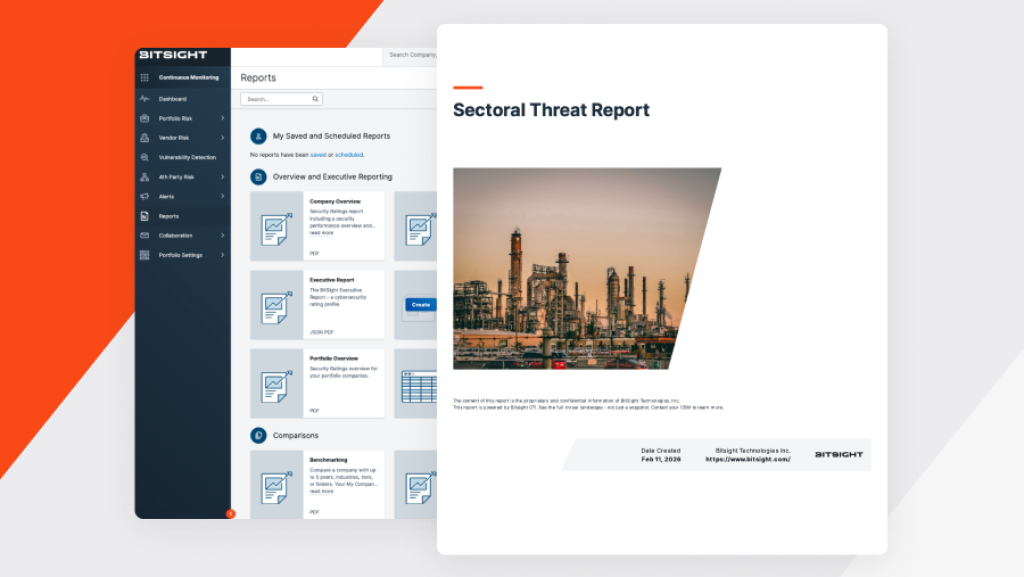
Sectoral Reports
Sectoral Reports deliver curated threat intelligence tailored to the industries in your supply chain. Get summaries of emerging risks, attack trends, and adversary tactics targeting specific sectors.
These insights help you identify patterns across your vendor ecosystem—without requiring deep threat intel expertise. Stay informed and ready to act with industry-relevant intelligence that supports faster, more focused risk decisions.
Deep and dark web intelligence has changed how we manage third-party risk. It gives us clear and early visibility into threats emerging across our supply chain, sometimes even before vendors themselves are aware, allowing us to assess impact and respond with confidence instead of reacting after the fact.”