Dark web monitoring, threat actor tracking, and ransomware intelligence — unified. Expose adversary relationships, infrastructure, and TTPs to focus investigations and prioritize response.
Transform scattered threat data into a complete adversary story.
Security teams aren’t defending against random alerts—they’re defending against organized adversaries. Today’s threat actors plan campaigns, reuse infrastructure, and refine tactics over time. Yet most teams encounter them only as fragments: isolated IOCs, suspicious domains, or a single mention buried in a feed. Without adversary context, teams can’t tell who’s behind the activity, how serious it is, or whether it actually poses risk to the business. Prioritization breaks down, and response stays reactive.
Bitsight Adversary Intelligence connects 64M+ threat actor entities, campaigns, infrastructure, and TTPs into a single navigable view, turning scattered data into a complete adversary story. Security teams can instantly see who is behind an activity, how they operate, and how it connects to known campaigns, breaches, and ransomware operations — enabling faster prioritization and confident response.
Complete adversary context at your fingertips.
Stop chasing indicators. Start countering adversaries.
Deep adversary context
Deep adversary context
Tap into the industry's most comprehensive threat repository — 64M+ threat entities, 700+ APT groups (nation-state, financially-motivated, hacktivist), and 4,000+ malware families.
- Centralized view of global threat actors, campaigns, and infrastructure — instantly understand the who and how behind every attack
- Extract, enrich, and connect scattered data into clear summaries and actionable next steps with source-backed context.
- Utilize MITRE ATT&CK and Malpedia-aligned catalogs to gain a shared framework for understanding malware and ransomware behavior.
- Track named groups including LockBit, BlackCat, Cl0p, Akira, APT28, APT29, Lazarus, and 700+ others
Streamline investigations
Streamline investigations
Consolidate analysis into a single module — pivot between related entities, validate intelligence instantly, and push enriched intel directly into your SIEM, SOAR, and TIP workflows.
- Filter intelligence by time, sector, and geography to reveal targeting trends and activity patterns
- Enrich IOCs (IPs, domains, hashes) with deep historical context to determine if an alert is part of a larger campaign
- Integrate with Splunk, Microsoft Sentinel, Cortex XSOAR, ThreatConnect, and 15+ other security platforms
Respond with confidence
Respond with confidence
Move beyond reactive IOC lists to proactive, adversary-aware prioritization — supporting strategic, operational, tactical, and technical intelligence needs.
- Reduce Mean Time to Respond (MTTR) by replacing manual research with actionable adversary guidance for analysts
- Generate AI-driven reports for both executives (strategic intelligence) and IR teams (tactical/technical context)
- Enable threat hunting based on TTPs, infrastructure, and adversary behavioral patterns"
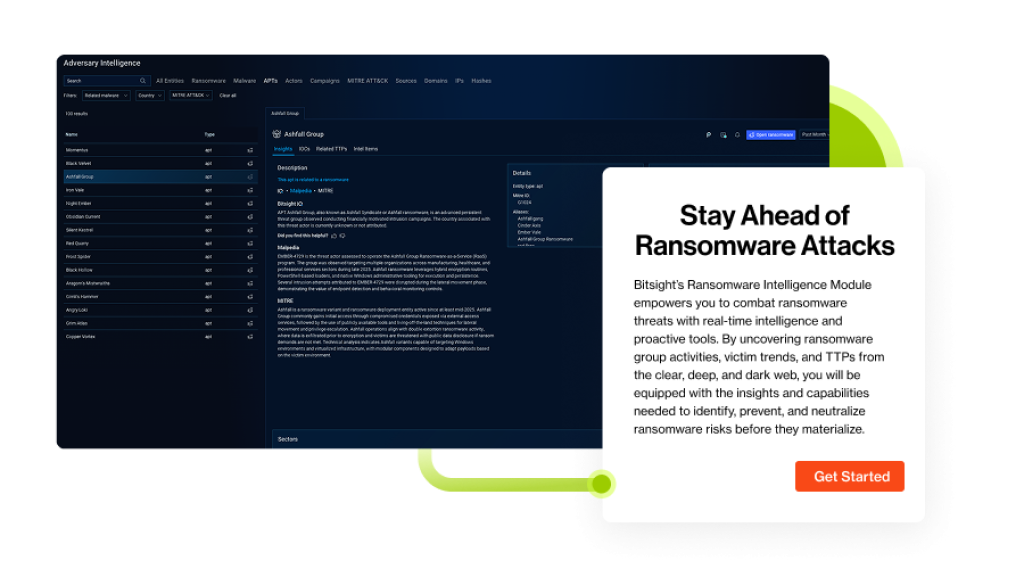
Outsmart ransomware with real-time intelligence
Ransomware attacks rose 25% year-over-year with average payouts up 89%. As ransomware groups fragment, reform, and refine tactics, reactive security can't keep pace.
Bitsight Ransomware Intelligence, a core segment of the Adversary Intelligence module, combines OSINT, deep, and dark web data with AI-driven enrichment to deliver real-time remediation guidance. By correlating global adversary chatter with your specific digital footprint, Bitsight surfaces pre-ransomware indicators, leak-site mentions, and active TTPs before encryption hits.
Threat intelligence services
We are ready to help. Learn more about our cyber threat intelligence services.