The SEC’s cybersecurity disclosure rules are a game-changer. Compliance isn’t just about avoiding penalties—it’s about strengthening trust with investors and the board. This guide helps you navigate the regulatory landscape with confidence.
What is Cybersecurity Compliance? List of Compliance Regulations by Industry

Cybersecurity Compliance: Definition
Cybersecurity compliance refers to the practice of adhering to laws, standards, and regulatory requirements established by governments and industry authorities. These compliance regulations are designed to protect a business’ digital information and information systems from cyber threats, including unauthorized access, use, disclosure, disruption, modification, or destruction.
Cybersecurity compliance is typically achieved by establishing risk-based controls that protect the confidentiality, integrity and availability of information that an organization stores, processes, integrates or transfers.
Key Elements of Cybersecurity Compliance
By complying with cybersecurity regulations, organizations can be sure that they have the ability to enforce the validity of their security controls, and therefore better prevent data breaches, protect customer information, maintain reputation and improve security posture. Compliance also ensures that organizations understand and are in control of their risk to those security controls which can help to avoid regulatory fines and litigation related to noncompliance. Key elements of compliance are as follows:
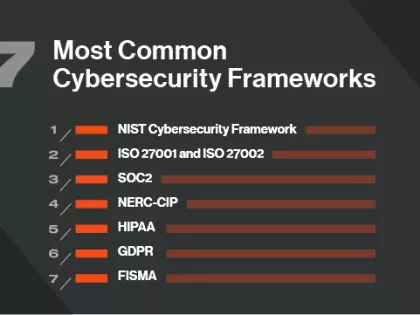
- Regulatory Requirements: Compliance with laws and regulations specific to the industry or region (e.g., GDPR, HIPAA, CCPA).
- Industry Standards: Adherence to standards and frameworks such as ISO/IEC 27001, NIST Cybersecurity Framework, PCI-DSS, etc.
- Policies and Procedures: Development and implementation of internal policies and procedures that align with regulatory and industry requirements.
- Risk Management: Conducting risk assessments to identify vulnerabilities and threats, and implementing measures to mitigate risks.
- Access Control: Ensuring that only authorized individuals have access to sensitive information and systems.
- Data Protection: Implementing measures to protect data from unauthorized access, breaches, and other security incidents.
- Incident Response: Establishing an incident response plan to effectively handle security breaches and minimize their impact.
- Training and Awareness: Providing regular training and awareness programs for employees to understand and comply with cybersecurity policies and procedures.
- Auditing and Monitoring: Regularly auditing and monitoring systems, vendors, and processes to ensure ongoing compliance and identify areas for improvement.
- Reporting and Documentation: Maintaining detailed records and documentation to demonstrate compliance and facilitate audits by regulatory bodies.
Cybersecurity Regulations & Compliance by Industry
If you operate in specific sectors, cybersecurity maturity is more than a best practice, it’s a regulatory requirement. These regulations are complex and constantly changing. To help you better understand your organization's regulatory environment and the cybersecurity standards and controls they stipulate, let's break down key cyber compliance regulations by industry.
1. Healthcare
The Health Insurance Portability and Accountability Act (HIPAA) is perhaps the most well-known healthcare cybersecurity compliance regulation because it impacts all of us.
HIPAA requires healthcare organizations, insurers, and third-party service providers to implement controls for securing and protecting patient data and conduct risk assessments to identify and mitigate emerging risks. Although HIPAA has been in place since 1996, the sector still struggles with compliance, as Bitsight research suggests.
2. Financial Services
As a lucrative target for bad actors, the financial services cybersecurity compliance landscape is abundant with regulation. The most common set of regulations are found in the Federal Financial Institution Examination Council handbook (FFIEC IT). As recently as 2020, there has been a renewed emphasis on continuous monitoring and business continuity management both internally and across the supply chain.
Another regulation is the Service Organization Control (SOC) Type 2 (SOC2). Developed by the American Institute of Certified Public Accountants (AICPA), SOC2 is a stringent trust-based cybersecurity compliance framework that helps firms verify that third parties are securely managing client data. In addition to protecting digital infrastructure, financial services companies must also comply with the Gramm-Leach-Bliley Act and notify customers of how their information is shared and when it may have been exposed.
As if all that weren’t enough, financial regulatory bodies also issue multiple guiding frameworks for cybersecurity compliance. For instance, the Office of the Comptroller of Currency (OCC) has published procedures for managing third-party risk. That guidance is issued to all organizations that fall under their oversight.
3. US Federal & Government Contracts
In the wake of the massive 2015 breach of the Office of Personnel Management (OPM) and the more recent SolarWinds supply chain attack, it’s no surprise that the government is doubling down on regulations that address today’s persistent and evolving threats.
Let’s talk about what’s changing.
In May 2021, the Biden administration issued an Executive Order (EO) to protect federal infrastructure. Among other things, the EO requires federal agencies to adopt new standards and tools to ensure the security of their software supply chains, including criteria to monitor and evaluate the security practices of third-party developers. Government contractors are also required to notify customers if a cyber-attack may have impacted their data.
Biden’s EO builds on a broad range of government cybersecurity regulations. The most comprehensive cybersecurity compliance framework established to date is the Federal Information Security Management Act (FISMA).
Aligned closely with FIPS and NIST 800 guidelines, the act sets standards for first- and third-party compliance. If you operate in the government sector, check out what FISMA means for you and how you can monitor FISMA compliance. In the defense sector, businesses must meet cyber requirements set up in the Defense Federal Acquisition Regulation Supplement (DFARS) and Procedures, Guidance, and Information (PGI). They must also comply with the new Cybersecurity Maturity Model Certification (CMMC), which requires defense contractors to undergo assessments of their security postures. Find out if your business is ready for the CMMC.
4. Energy
The Colonial Pipeline breach is the most recent in a long line of cyberattacks against the U.S. energy sector, but it won’t be the last. Bitsight research finds that 62% of oil and energy companies are at heightened risk of ransomware attacks due to their weak cybersecurity performance. And nearly 100 of these organizations are 4.5 times more likely to experience such an attack.
It’s critical that these companies immediately assess their security programs to discover any gaps, particularly around configuration management, patching, vulnerability management, and endpoint security. They must also ensure that they comply with the North American Electric Reliability Corporation – Critical Infrastructure Protection (NERC CIP) cybersecurity standards. Read about effective strategies for achieving NERC-CIP compliance.
Lastly, energy companies must comply with the Federal Energy Regulatory Commission's (FERC) Critical Infrastructure Protection (CIP) Standards.
5. Consumer Businesses
Businesses that have direct contact with consumers, such as restaurants, retailers, and consumer product companies, are increasingly using digital technologies and data initiatives to improve the customer experience. While customer data is necessary for these interactions, legislation requires that businesses protect and ensure consumer data privacy.
For instance, the General Data Protection Regulation (GDPR) instituted new requirements for how businesses – including U.S. businesses – collect and store the private data of European Union citizens. Fines for non-compliance are high; up to €20,000,000 or 4% of global revenue, and the EU is not shy about enforcing them. In 2018, the California Consumer Privacy Act (CCPA) enacted similar legislation. Other states are following suit. In May 2021, the Commonwealth of Virginia passed a Consumer Data Protection Act, which adds data protection assessment requirements.
6. Publicly Traded Companies
In 2023, The Securities and Exchange Commission (SEC) has implemented new rules regarding cybersecurity disclosure for publicly traded companies. These rules create new obligations for reporting material cybersecurity incidents and disclosing critical information related to cybersecurity risk management, expertise, and governance. Companies will be required to disclose risks in their annual reports beginning on December 15, 2023.
The SEC also encourages companies to have policies and procedures in place to prevent insider trading based on nonpublic information about cybersecurity risks and incidents. Failure to comply with these rules can result in regulatory action, investor lawsuits, and potential reputational damage.
7. Retail
The retail sector isn’t federally regulated, but it does follow regulations from the Payment Card Industry Security Council’s Data Security Standard (or PCI DSS).
Any organization that process, store or transmit payment cardholder information are required to follow regulations from PCI DSS which stipulates standards for securing cardholder data. Several provisions within PCI DSS requirements concern identification, monitoring and remediation of software vulnerabilities that, when exploited by threat actors, could jeopardize the security of payment cardholder information.
8. Defense
As a condition of providing a service to the U.S. Department of Defense (DOD), businesses must meet cyber requirements set up in the Defense Federal Acquisition Regulation Supplement (DFARS) and Procedures, Guidance, and Information (PGI). DFARS outlines cybersecurity standards a third party must meet and comply with prior to doing business with the DOD in order to protect sensitive defense information.
9. Insurance
While regulations for insurance departments and companies vary state by state, many have issued requirements to protect consumer information. Furthermore, we’ve seen increased interest in adding more regulations in this area. In October 2016, the New York State Department of Financial Services (DFS) proposed new regulation around cybersecurity for both financial organizations and insurance companies.
The Challenge of Cybersecurity Compliance
From Europe’s general data protection regulations and California’s Consumer Privacy Act to PCI DSS and HIPAA regulations, CISOs are under pressure to comply with a variety of mandates related to cybersecurity and the protection of sensitive data.
The stakes are high. Failure to achieve and maintain legal compliance can often result in fines and litigation that may cost millions of dollars. When compliance failure contributes to a cyberattack or data breach, the impact can be even more devastating. Breaches typically cause customers to lose confidence and stock to prices drop. The company’s reputation inevitably suffers, and profitability takes a hit.
Achieving compliance with the broad array of regulatory frameworks requires solutions that can accomplish several key objectives. Cybersecurity compliance technology must be able to:
- Identify and address data risk and system vulnerabilities, aligning them with business regulatory objectives.
- Provide visibility, enhance enforcement and demonstrate efficacy of the security controls needed to meet compliance.
- Deliver the ability to take a prioritized, risk-based approach to cybersecurity compliance.
- Automate and streamline data security and privacy programs.
- Eliminate compliance silos, reduce control clutter and empower executives to gather answers more quickly.
- Minimize security assessment control creep.
- Reduce the administrative burden of risk assessments and increase the efficiency of personnel dedicated to security risk management.
- Lower the cost of cyclical security and IT audits or assessments.
Compliance Summary
While cybersecurity compliance is an essential goal if your organization operates in these sectors, you can also mature your cybersecurity program by modeling it after common cybersecurity frameworks like NIST, ISO 27000, and CIS 20.
Use Bitsight Security Ratings to assess and score your cybersecurity performance and continuously monitor your third parties to ensure they don’t pose a hidden risk to your network. With cybersecurity compliance frameworks as your guidepost and the insight that Bitsight brings, you can better understand what regulators are looking for and continue to mature your cybersecurity performance.
Additionally, Bitsight Cyber Threat Intelligence helps organizations comply with PCI DSS by enhancing the vulnerability assessment and prioritization process. Bitsight CTI uses real-time vulnerability exploit intelligence from the cybercriminal underground to accurately predict which vulnerabilities are most likely to be exploited in the next 90 days. This intelligence enables security teams to more effectively prioritize these vulnerabilities to increase security and ensure cybersecurity compliance with PCI DSS requirements.