NERC CIP-013-1: Effective Date, Preparation Strategies, & Impact

The North American Electric Reliability Corporation (NERC) has developed a new set of cybersecurity standards designed to help power and utility (P&U) companies limit their exposure to third-party cyber risks and preserve the reliability of bulk electric systems (BES).
The Federal Energy Regulatory Commission approved the NERC standards in the fall of 2018.
NERC CIP-013-1 Effective Date
This critical infrastructure protection (CIP) standard will be enforceable starting on July 1, 2020. Affected companies will need to be able to prove that they’re compliant within 18 months of the NERC CIP-013-1 effective date in order to avoid penalties.
What’s included?
The new NERC CIP-013-1 standard proactively addresses specific supply chain cyber risks with the aim of improving BES reliability.
According to NERC, “The security objective [of these rules] is to ensure entities consider cyber security risks to the BES from vendor products or services.” CIP-013-1 includes regulations for vendor procurement, permissions, and monitoring.
The new standards will help utility companies protect bulk electric systems by limiting their exposure to malware, tampering, and other cyber risks that can originate with vendors.
Why now?
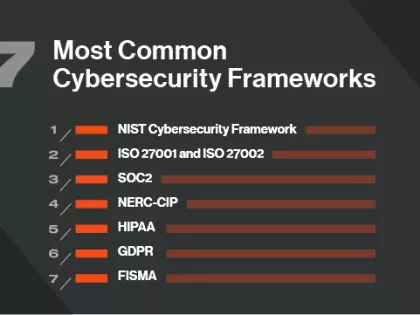
NERC CIP-013-1 comes at a time when many industry regulators are implementing regulations for third-party risk management. Other, broader regulations like GDPR also focus on third-party risk.
These regulations follow a long history of third-party data breaches across industries. Research has shown that breaches originating at third parties are among the costliest cyber attacks.
These attacks have caused downtime in major network infrastructure and derailed the physical operations of global companies like FedEx and Maersk. An attack of this nature that affects American power grids could potentially be catastrophic.
The Impact of NERC CIP-013-1
This new supply chain risk management standard could significantly impact operations at P&U companies (as well as their vendors).
In order to maintain compliance, impacted organizations will need to independently develop plans to identify and mitigate cyber risks in their supply chain.
For most entities, the push to meet the new standards starts immediately. Companies with incomplete programs or insufficient evidence of compliance face enforcement actions. For each outstanding violation, NERC is authorized to fine organizations up to $1 million per day.
Other organizations, like software vendors and consultants that support P&U companies, will also need to familiarize themselves with the new regulations. These organizations will potentially need to adjust their operations in order to preserve business relationships.
Planning for Compliance
The gradual rollout of these new guidelines is designed to allow companies time to properly assess and adjust their existing third-party risk management programs.
For many organizations, NERC CIP-013-1 will necessitate a shift in cybersecurity priorities. While internal controls like firewalls and incident detection and response are important, they don’t always protect the organization from attacks that begin in the systems of third parties. When vendors have access to a P&U companies’ systems, a successful attack on a vendor can quickly lead to a successful attack on the P&U company.
For this reason, a new focus on assessing, monitoring, and improving the cybersecurity of critical third parties is required.
Implementing Third-Party Risk Management
Thankfully, there are tools available to help utility companies assess and mitigate vendor risk.
Bitsight Security Ratings are the leading continuous monitoring solution for third-party risk management. These ratings supplement traditional vendor risk management processes like questionnaires, penetration tests, and on-site visits by providing a near-real-time look at vendor cybersecurity performance.
Importantly, security ratings can be used to prioritize third-party risk management activities and measurably reduce cyber risk.
Bitsight Security Ratings can help power and utility companies comply with NERC regulations for vendor procurement and third-party risk management.