Bitsight Study: Healthcare Sector is Far Too Vulnerable to Cyber Threats


Healthcare is under attack. Hospitals, doctors’ networks, insurance companies, and others are prime targets for hackers due to the valuable protected health information (PHI) they store and the vital role they play in our nation’s critical infrastructure.
Indeed, 89 percent of healthcare organizations have experienced a data breach in the past two years and the sector was the leading industry for cyberattacks and data breaches in 2018. In 2019, the trend looks to continue with six hospitals and healthcare systems reporting large scale attacks in the month of July alone.
But digital transformation in the healthcare sector is creating a perilous cybersecurity landscape. Cloud-based computing is on the rise and projected to triple in this sector as physicians, administrators, and patients demand secure access to information in a cost-efficient way. Furthermore, medical devices and telemedicine introduce unique IoT security concerns and further expand the cybersecurity threat landscape.
When a cyber attack does occur, the ramifications extend beyond financial and reputational losses. PHI is an extremely valuable commodity for hackers and, unlike other forms of data, is unique to each individual and cannot be replaced. There’s also an emerging and potentially catastrophic human impact. Malware attacks can hijack computer systems and restrict access to critical data, shut down healthcare systems and equipment, and even add tumors into CT and MRI scans.
There are also major regulatory consequences. PHI is leaking to the outside world at an alarming rate. And even with regulations like HIPAA in place, compliance and security are still lacking, as shown by the extensive list of companies on the Department of Health and Human Services’ data breach “wall of shame”.
A deeper dive into the cyber risk facing healthcare organizations
We decided to take a closer look and gauge the security performance of organizations within the healthcare sector. The idea was to better understand where greater risk management is required. Using data collected by Bitsight’s Data Science team as of June 1, 2019, we examined the overall security ratings of healthcare companies, as well as potential vulnerabilities such as legacy systems and software, insecure ports, and instances of already compromised systems.
The results are sobering.
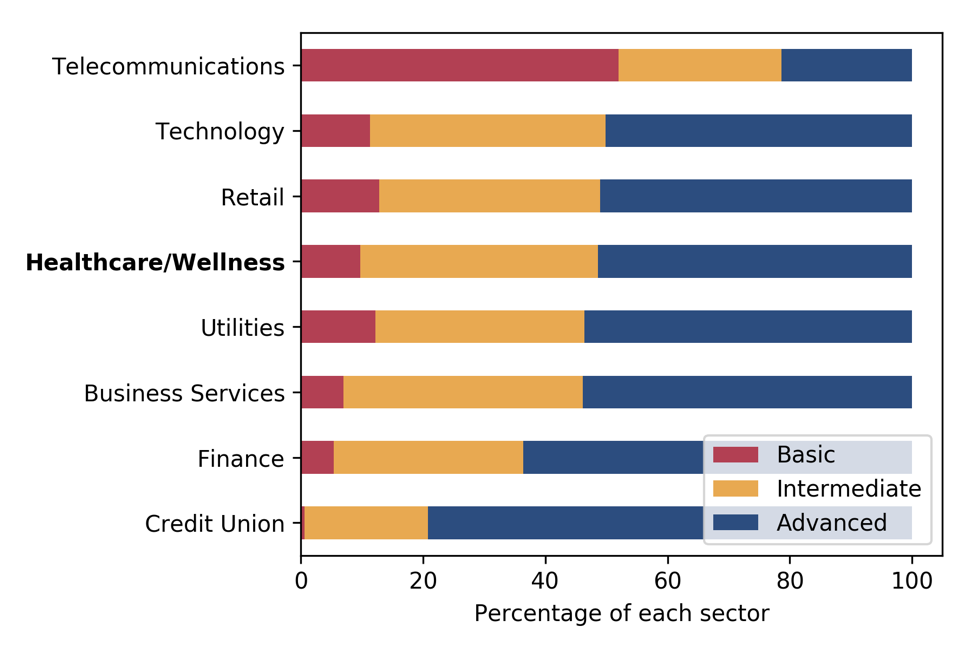
Our data suggests that the organizations in this sector have much to do to improve their security postures. As the chart below shows, only 50% of healthcare companies have Advanced Ratings—meaning they are at a much higher likelihood of breach. Bitsight Security Ratings range from 250 to 900, with a higher rating equating to a better security posture. Anything above 740 is considered “Advanced.” Companies with a security rating of 500 or lower are nearly five times more likely to experience a publicly disclosed data breach.
Breakdown of Security Ratings by Major Industry
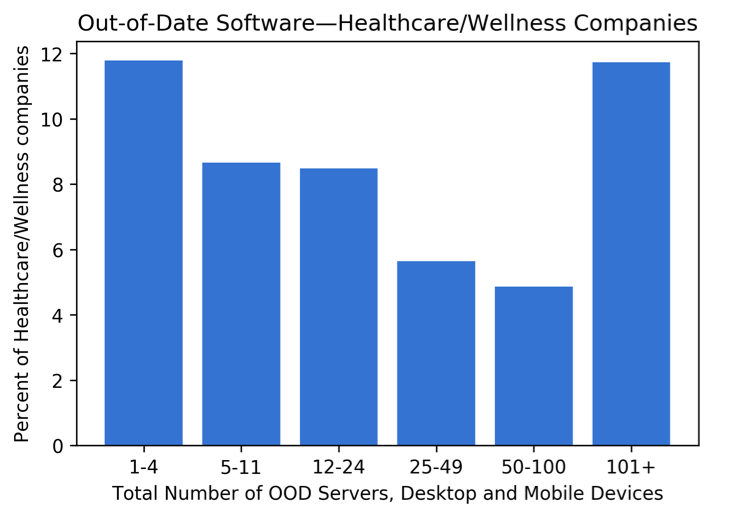
51% of healthcare organizations are also dealing with out-of-date systems or unsupported devices, which can be particularly vulnerable to failure or cyberattacks. In the healthcare industry, outdated medical devices are often exploited by bad actors to gain access to the entire network.
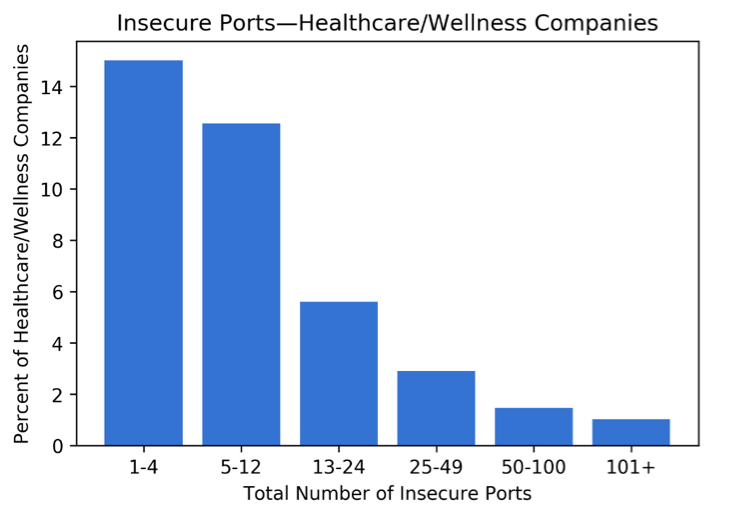
The news doesn’t get much better when one considers potential access points such as computers, laptops, mobile devices, tablets, etc. The following metrics show that the ports of 39% of healthcare companies are inherently insecure or vulnerable to cyberattack. That indicates that many of these organizations have several ways for hackers to exploit their systems, such as via medical devices with outdated software or vulnerabilities. Read more about the risks of open port vulnerabilities.
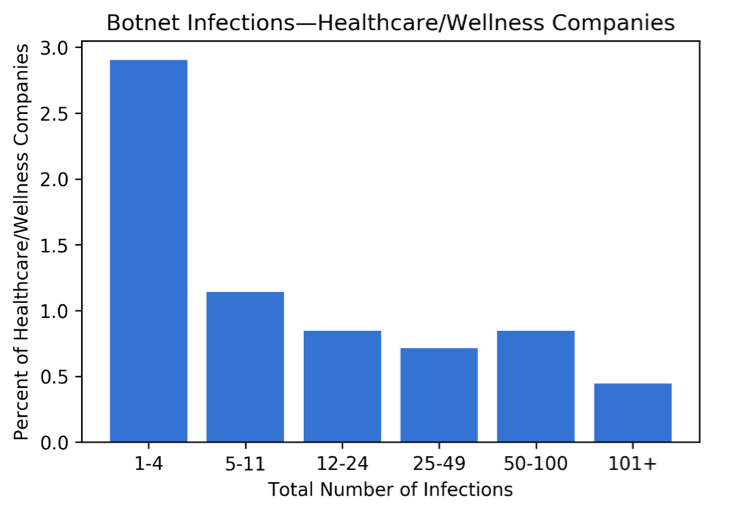
 Our findings show that 7% of healthcare companies had one or more botnet infections within the last three months. This number may seem relatively low, but the definition of “botnet” indicates that these infections extend beyond a single machine— whether on their network or not.
Our findings show that 7% of healthcare companies had one or more botnet infections within the last three months. This number may seem relatively low, but the definition of “botnet” indicates that these infections extend beyond a single machine— whether on their network or not.
Botnets are networks of computers that have been compromised or infected with malicious software and controlled as a group by an adversary without the owners’ knowledge. Bitsight research has identified a solid correlation between botnet infections and data breaches. More specifically, companies with a Bitsight botnet grade of B or lower were more than twice as likely to experience a publicly disclosed data breach.
There is some good news, however. The healthcare sector is doing a commendable job in protecting against SPAM and phishing emails, with nearly 70% of the sector utilizing DKIM or SPF—two authentications that validate email domains to verify that an email has not been forged.

Third-party supply chains remain fraught with risk
Third-parties remain a worrisome source of risk—especially given the increased dependency on cloud service providers and greater interaction with mobile and IoT technologies. A recent study showed that 59% of breaches originate with third parties. Case in point, the 2019 Quest Diagnostics breach, which exposed the private data of 11.9 million patients. This is just one example of the many third-party cybersecurity risks healthcare providers face.
Regulators are also starting to pay more attention to things like third and fourth-party cybersecurity. HITRUST certification, for example, is being used as a security measuring stick for managing third-party and supply chain risks in the healthcare sector.
Actions to be taken
As our data shows, the systems and networks of companies in the healthcare space are highly vulnerable to attack or already compromised. Yet, in far too many situations, these organizations wait until a breach or a cyber event has taken place to take action and respond to potential risk—in their own systems and in their supply chains. At that point, it’s too late to do anything more than clean up the mess that they’ve gotten into.
It’s critical that healthcare organizations find a way to more thoroughly, accurately, and continuously assess and monitor both their own internal security performance management and gain visibility into the security posture of their entire third-party ecosystem. They must also ensure that any cloud service provider that stores, transmits, or collects patient or other critical data aligns their security controls with the healthcare organization’s risk tolerance and adheres to regulatory obligations.
With a stronger, continuous, and more prepared approach to security, healthcare organizations can improve their security ratings, better mitigate risk, meet regulatory requirements, and protect their patients’ information.
Find out how Bitsight Security Ratings is helping healthcare companies mitigate cyber risk with this real-life customer story.
This content was produced by Evan Tegethoff in conjunction with John Burger and Shrinath Patel from the Bitsight Data Science Team.



