Request a free cyber risk report for your company to find the gaps in your security program and how you compare to others in your industry.
Security Analytics
Manage risk effectively with security analytics
For enterprises today, the digital ecosystem is constantly increasing in size and complexity. Workforces are becoming more mobile, with employees increasingly using their own devices to access corporate networks and assets. Enterprises are embracing cloud services that deliver greater agility and productivity, but that comes with greater risk as well. In the face of all this change, IT teams need superior security analytics that can provide greater visibility into the organization’s digital footprint and into the effectiveness of security programs.
Bitsight is transforming cyber risk strategy and cybersecurity performance management with detailed, objective security analytics. Our industry-leading security ratings deliver insight into security performance and risk concentrations.
Essential metrics for security analytics
Understanding risk within your IT environment – and how effective your security programs are at mitigating it – is essential to strengthening your cybersecurity posture and mitigating risk in your supply chain. The following metrics are an essential part of effective security analytics.
- Security ratings. Bitsight Security Ratings evaluate a company’s overall cybersecurity performance based on externally observable key risk indicators from more than 120 sources. Ratings are based on information about a company’s compromised systems, security diligence, user behavior, and data breaches.
- Botnet infections. Understanding the frequency, severity, and duration of botnet infections within a network gives security leaders insight into how likely their company is to fall victim to a data breach.
- Open ports. Hackers can exploit open to gain access to sensitive systems and data. Organizations with more open ports are more likely to experience a breach than companies with fewer.
- Intrusion attempts. Understanding how many intrusion attempts were detected and blocked can help identify the risk that systems and data face daily.
- Patching cadence. The rate at which critical security patches are applied is an essential metric for security analytics. Slow patching cadence indicates either a lack of diligence or lack of resources, and organizations that fail to apply critical security patches in a timely manner may be exposing themselves to potentially dangerous cyber risks. In fact, Bitsight research shows that slow patching cadence is strongly correlated with ransomware attacks.
- Phishing test success rate. Organizations that conduct phishing tests can get a better read on how likely their employees are to fall for phishing attempts.
- Average password strength. This metric is a simple indicator of risk, and one that can be easily mitigated.
- Unidentified devices on the network. Security teams have less control over unidentified devices than over company devices. The number of unidentified devices is directly related to an increase in cyber risk.
Security analytics from Bitsight
As the most trusted, transparent, and transformative cyber risk analytics company, Bitsight provides organizations with security analytics solutions for managing security performance and mitigating third-party risk. With Bitsight analytics, security teams gain visibility into the entire digital ecosystem to continuously monitor risk as well as the effectiveness of security programs.
Bitsight’s security analytics solution offers a centralized dashboard where you can view all digital endpoints organized by cloud provider, business unit, and geography. By tracking security metrics daily, your teams can quickly identify the areas of greatest risk and make plans for immediate remediation. Bitsight’s data analytics & cybersecurity reporting features enable security and risk leaders to confidently share security analytics with business executives and the board, using language and metrics that are easily understood by technical and non-technical personnel alike.
Bitsight for Security Performance Management (SPM) enables organizations to continuously monitor the effectiveness of security controls over time. Security analytics within the SPM platform include:
- Attack surface analytics. This security analytics solution continuously discovers and segments the assets, applications, and devices within your digital footprint. With Bitsight, you can visualize areas of disproportionate risk and gain visibility into all digital assets that need to be secured. You can also discover hidden assets and shadow IT instances, assessing them for risk and bringing them in line with corporate security policies.
- Enterprise analytics. Bitsight delivers visibility into security performance across units, subsidiaries, and other organizational groups, taking the guesswork out of identifying risk concentration and enhancing security performance throughout the organization.
- Peer analytics. Gain visibility into your security’s relative performance strength as compared to peers and competitors. Benchmark your programs against other organizations in your industry or against companies of similar size to make more informed decisions about where to focus cybersecurity efforts.
Security analytics for third-party risk
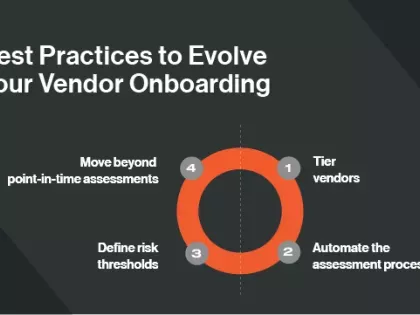
Bitsight for Third-Party Risk Management (TPRM) enables risk leaders to measure and continuously monitor third-party security controls, taking action to mitigate risk for third and fourth parties. This Bitsight solution enables teams to quickly and confidently ensure that new vendors are within the organization’s risk tolerance, and it manages constantly changing risk levels throughout the vendor lifecycle. Continuous monitoring complements traditional vendor risk assessments, enabling third-party risk management teams to track changes, prioritize responses, and drive remediation through proactive, evidence-based collaboration. Additionally, Bitsight security analytics for IT vendor risk management make it easier to measure the performance of cyber controls across the vendor portfolio.
Why choose Bitsight?
An industry-leading solution
Bitsight is the world’s leading provider of cyber risk intelligence, transforming how security leaders manage and mitigate risk. Leveraging the most comprehensive external data and analytics, Bitsight empowers organizations to make confident, data-backed decisions and equips security and compliance teams from over 3,300 organizations across 70+ countries with the tools to proactively detect exposures and take immediate action to protect their enterprises and supply chains. Bitsight customers include 38% of Fortune 500 companies, 4 of the top 5 investment banks, and 180+ government agencies and quasi-governmental authorities, including U.S. and global financial regulators.
Extensive visibility
Bitsight operates one of the largest risk datasets in the world. Leveraging over 10 years of experience collecting, attributing, and assessing risk across millions of entities, we combine the power of AI with the curation of technical researchers to unlock an unparalleled view of your organization. Bitsight offers more complete visibility into important risk areas such as botnets, mobile apps, IoT systems, and more. Our cyber data collection and scanning capabilities include:
- 40 million+ monitored entities
- 540 billion+ cyber events in our data lake
- 4 billion+ routable IP addresses
- 500 million+ domains monitored
- 400 billion+ events ingested daily
- 12+ months of historical data
Superior analytics
Bitsight offers a full analytics suite that addresses the challenges of peer comparison, digital risk exposure, and future performance.
Ratings validation
Bitsight is the only rating solution with third-party validation of correlation to breach from AIR Worldwide and IHS Markit.
Quantifiable outcomes
Bitsight drives proven ROI with significant operational efficiency and risk reduction outcomes.
Prioritization of risk vectors
Bitsight incorporates the criticality of risk vectors in to calculation of Security Ratings, highlighting risk in a more diversified way to ensure the most critical assets and vulnerabilities are ranked higher.