Gartner predicts disaster recovery will become part of the CISO’s job. This isn’t just an IT problem anymore—it’s an enterprise imperative.
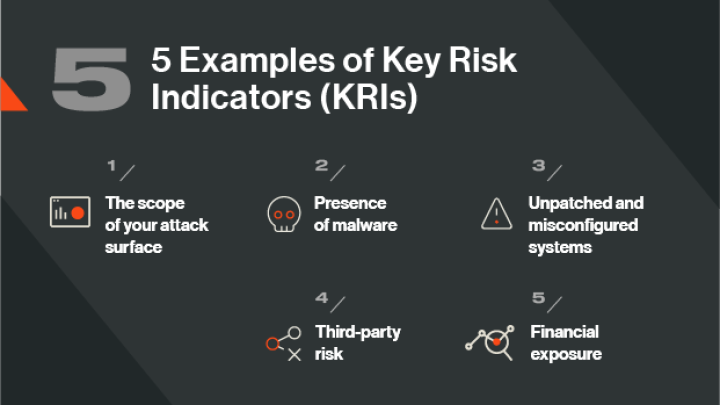
5 Examples of Key Risk Indicators (KRIs) in Cybersecurity
Tags:
What is a key risk indicator in cybersecurity?
Key risk indicators (KRIs) are critical metrics used by security leaders and risk management teams to monitor and measure cyber risk exposure.
KRIs can be used to monitor changes in your organization’s risk profile, provide insights into vulnerabilities in your security apparatus or digital environment, and support ongoing risk monitoring between security audits.
KRIs are often confused with key performance indicators (KPIs), but there is a difference. KRIs enable you to monitor and quantify cyber risk so that you can initiate quick remedial action. A KPI, on the other hand, measures security performance, progress against goals, and trends over time.
Let’s look at five KRIs that you should monitor to understand the potential risks your organization faces.
KRI #1: The scope of your attack surface
An important KPI is knowing where risk lies hidden in your digital environment. But as your business expands to the cloud, across business units, geographies, and remote locations, it can be hard to discover and validate your digital footprint, identify potential risk, and prioritize remediation.
One way to gain this insight is to use a discovery and reporting tool like attack surface scanning. This technology automatically and continuously takes inventory of your digital assets, far beyond your traditional network perimeter. Findings are presented in dashboard views, assets are pinpointed by location, and areas of concentrated risk are highlighted so you can quickly move to address these.
KRIs to monitor include:
- Previously unknown instances of cloud services or shadow IT and the risk posture of these assets.
- Business units, subsidiaries, or remote offices that fail to adhere to corporate security policies.
- The risk profile of critical digital assets, such as a cloud instance that stores sensitive data.
- Areas of highest risk exposure.
KRI #2: Presence of malware
The presence of malware on your network is a strong indicator of the probability of breach and gaining visibility into malware activity is essential to reducing your organization’s cyber risk exposure. But malware developers are skilled at designing malicious software that can go undetected by traditional anti-virus and scanning tools.
While no organization is immune from malware, you can use Bitsight’s powerful data-driven insights to discover machines that may already be compromised. You can also identify user behavior that could introduce malware onto your network – and classify the level of risk posed to your business.
Malware KRIs to monitor include:
- The exposure of employee credentials on the dark web (hackers use this information to infiltrate your network and install malware).
- Instances of compromised files downloaded by employees.
- The number of machines impacted by malware or botnets.
KRI #3: Unpatched and misconfigured systems
Poor security hygiene, in the form of unpatched and misconfigured systems, is a significant indicator of risk. When Bitsight analyzed hundreds of ransomware events to estimate the relative probability that an organization will be a ransomware target, we discovered that:
- Enterprises with a patching cadence earning D or F grades were more than 7x more likely to be a victim than organizations with an A grade.
- Companies with a C grade or lower in TLS/SSL configurations are nearly 4x more likely to be ransomware victims.
- Only 10% of organizations achieved an A grade for security performance excellence.
To improve these statistics, use Bitsight to continuously and automatically monitor your digital infrastructure for vulnerabilities and security gaps.
Security hygiene KRIs to monitor include:
- TLS/SSL certificate effectiveness: Bitsight analyzes certificates to determine if they are signed using a secure algorithm.
- TLS/SSL configurations: Identify servers with misconfigured security protocol libraries and weak encryption standards.
- Patching cadence: Discover which systems are affected by critical vulnerabilities and how quickly your organization patches them.
- And more.
KRI #4: Third-party risk
Third-party risk is one of the leading causes of data breaches. But it can be hard to know if you're doing business with a high-risk vendor. That’s because traditional methods of assessing and measuring your vendors’ security postures only capture a point-in-time view of risk. They are also costly, time-consuming, and require you to take your vendors at their word.
A better way to expose risk in your supply chain is to monitor the security performance of your vendor pool continuously and automatically – from onboarding through the life of the relationship.
Third-party risk KRIs to monitor include:
- The presence and severity of security vulnerabilities in your vendors’ IT infrastructures.
- Your vendors’ historical security performance (a past breach can provide a good indication of their current security postures).
- Any changes in your vendors’ security postures during the life of their contracts.
KRI #5: Financial exposure
With the average cost of a data breach now at $44.35 million, the board and C-suite need to understand your organization’s financial exposure. Only then can they make more informed decisions around cyber risk management and prioritize new technology investments to protect your organization.
However, significant resources and expertise are needed to collect the necessary data and model various scenarios – such as the financial impact of a ransomware attack or data breach. And this process isn’t easily repeatable.
But with Bitsight Financial Quantification, you can simulate your organization’s financial exposure across hundreds of thousands of cyber events.
KRIs you can model include the financial impact of:
- Denial of service, data theft, extortion, privacy breaches, and other types of attacks.
- Cyber incidents in your digital supply chain.
- A failure to meet cybersecurity standards and regulations and likely penalties and fees.
KRIs are a critical part of any cybersecurity risk management program and should be closely tied to a KPI. For instance, if you discover persistent KRIs across your organization, such as unpatched systems, a related KPI could be a measurable improvement in your patching cadence over a certain period of time.
KRIs and KPIs will vary by organization, but whatever your chosen metrics, be sure to leverage technology and automation so you can easily collect and analyze data, monitor trends, and quickly remediate issues.