How to Measure Your Vendors’ Security Posture – Faster and at Scale
Data breaches that originate in an organization’s supply chain are more prevalent than ever. According to the 2022 Verizon Data Breach Investigations Report, 62% of network intrusions came through an organization’s partner.
For this reason, it’s critical that you conduct a rigorous and extensive analysis of a vendor’s security posture – before they are onboarded. However, for most organizations this is a costly and lengthy process. Gartner reports that it takes most companies an average of 90 days to complete vendor due diligence. This can undermine your business’ efforts to accelerate growth and remain competitive.
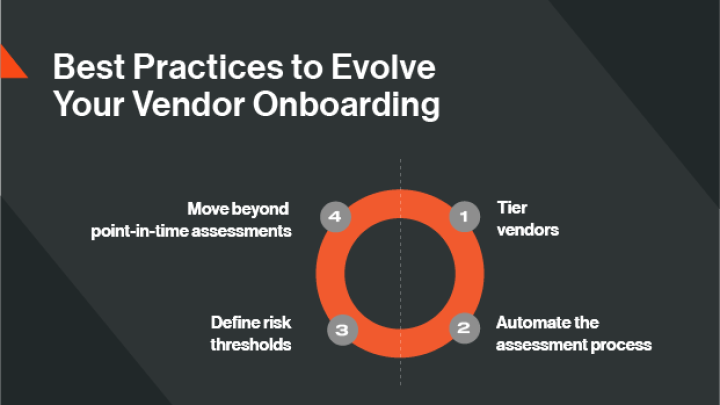
But it doesn’t have to be that way. Let’s look at a few best practices you can adopt today to onboard new vendors securely and at the speed of business.
1. Don’t treat every vendor the same
One way to save time during vendor onboarding due diligence is by grouping or tiering your vendors based on how critical they are to your organization.
Not all vendors will have the same risk threshold. For example, a company that provides an important service or has access to your sensitive data (like a payroll provider) would be a higher priority than a company that does not have immediate access to proprietary information or performs a mission-critical function (such as a food service business).
By moving beyond a “one-size-fits-all” approach during the due diligence process and tiering your vendors in this way, you can determine if a vendor needs a more in-depth evaluation and focus your resources where they’re needed most.
2. Automate the assessment process
Once you’ve tiered your vendors, it’s time to evaluate their security postures.
Instead of relying on traditional, resource-intensive vendor evaluations, you can expedite this process using a continuous monitoring tool like Bitsight Security Ratings. These ratings, which range from 250 to 900, automatically compare vendors’ security profiles side-by-side and allow you to prioritize them according to risk – with a higher score suggesting a lower risk profile. Ratings are updated daily to provide unprecedented visibility into a vendor’s security posture.
With this insight, you can go beyond your initial tiering and further prioritize which vendors need the most attention. You may decide, for example, that the assessment process for vendors with high security ratings may not need to be as rigorous, while the process for vendors with lower ratings could be more thorough.
3. Define thresholds for acceptable levels of risk
You also can use Bitsight Security Ratings to establish acceptable risk thresholds and develop language to ensure that your entire third-party network meets these requirements.
To make this work, establish a culture of cross-collaboration across various departments. Involve everyone from the CEO, the CIO, and the CFO to the head of legal in determining your organization’s risk appetite — what is acceptable and what is not. Then, set parameters around risk. For example, you might collectively decide to put extra contractual controls in place based on the rating of a particular vendor. Those with lower ratings may require more stringent controls to ensure that they meet your acceptable risk threshold.
You should also work with your legal department to create contract language that guarantees that vendors will not fall below a certain threshold or security grade.
4. Move beyond point-in-time assessments
Security questionnaires and assessments have their place. However, they only provide a point-in-time view of a vendor’s security posture. They are also time-consuming and hard to scale across the expanding supply chain.
Continuously monitoring third-party vendors is a much more complete and accurate way to gauge a vendor’s true security posture. For instance, Bitsight provides an immediate, near real-time snapshot of third-party security. A higher rating denotes better security, while a lower rating means improvement is needed.
Depending on how they score, using Bitsight, you can prioritize which vendors may need more rigorous due diligence for a deeper dive into their security processes and policies.
A key benefit of Bitsight’s automated data analysis technology is that it speeds up the vendor onboarding process. Even after the contract is signed, you can keep tabs on your vendors’ security postures for the duration of the contract. If a vendor’s security rating drops, you’ll get automated alerts so you can quickly work with your vendor to mitigate the issue.
5. Consider historical security performance
An important, and often overlooked area of cyber risk due diligence is what a vendor’s historical performance looks like. A vendor might have had no cybersecurity incidents over the past year, but what if they had suffered multiple kinds of major breaches each of the three years prior?
Bitsight Security Ratings consider a vendor’s historical security performance so you get a more complete view of how a potential third-party has managed and responded to cybersecurity risk over time.
Optimize your onboarding process today
Through the strategies we have outlined here, you can accelerate your onboarding process and cut down on the time it takes to onboard partners from months to weeks or even days. And you can move forward knowing that all of your vendors – even if they number in the hundreds or thousands – present acceptable levels of risk to your organization.
For a deeper dive into this topic, read our white paper: Faster, Less Costly, and More Scalable – Here's how your vendor onboarding program can have all three.



