Bitsight analyzed over 27,000 companies over two years and compared their security ratings to a comprehensive set of disclosed data breaches.
Good Harbor Salon: The Future of Supply Chain Cyber Risk Management After SolarWinds


The right cyber security information can dramatically simplify the task of improving security performance and mitigating risk. To defend against a rapidly evolving threat landscape, security teams need actionable data that can help identify risks, highlight security gaps, and support plans to remediate vulnerabilities.
Most security teams don’t suffer from a lack of data. Many teams are overwhelmed by huge volumes of raw information that make it hard to sort out the essential intelligence from the background noise. To improve monitoring and remediation of risk within their digital ecosystem, security teams need high-value cyber security information that can shine a spotlight on critical assets, prioritize risks and vulnerabilities, and evaluate the performance of security controls.
That’s where Bitsight can help. Bitsight is the world’s leading Security Ratings service, providing organizations with unprecedented visibility into their digital footprints and attack surfaces. By delivering objective, verifiable cyber security information on a continuous basis, Bitsight helps organizations make faster, more strategic decisions about cybersecurity policy and third-party risk management.
Bitsight pioneered the security ratings industry by developing a platform that provides an outside-in approach to cyber security information. Much like credit ratings, Bitsight Security Ratings range from 250 to 900, with the current achievable range being 300-820 – higher numbers correlate to a better overall security posture.
Rather than relying on traditional and often manual techniques like penetration testing, questionnaires, or on-site visits, Bitsight’s Security Ratings are derived from externally observable data gathered from 120+ sources around the world. This cyber security information provides critical insight into the performance of organizations in relation to 23 key risk vectors, which fall into four data categories: compromised systems, security diligence, user behavior, and public disclosures. By analyzing and weighting this data with a proprietary algorithm, Bitsight produces daily Security Ratings that accurately communicate an organization’s security posture and performance.
Features of Bitsight Security Ratings
Bitsight Security Ratings deliver the essential cyber security information that organizations need to improve security performance and mitigate risk.
The external cyber security information view provided by Bitsight Security Ratings allow security teams to identify the greatest areas of risk and prioritize resources and staff to remediate them fast. As a result, organizations can strengthen their security posture more quickly and reduce the risk of a breach.
Through security benchmarking, Bitsight helps organizations quantify cyber risk, measure the impact of mitigation efforts, and contextualize their performance over time and against industry peers.
Bitsight helps third-party risk managers identify issues within their supply chain, prioritizing remediation efforts and streamlining further assessments to improve security controls.
Cyber security information from Bitsight delivers actionable insights into gaps in security controls – such as misconfiguration, unpatched systems, and vulnerabilities – across all parts of the digital ecosystem. From on-premises cyber assessments to cloud security audits, Bitsight delivers the visibility and insight security leaders need to mitigate risk and improve security posture.
Bitsight enables large enterprises to gain visibility into concentrated areas of risk across organizational groups such as business units, subsidiaries, acquisitions, and disparate geolocations.
Bitsight Security Ratings provide a common language that make cyber security information and information security presentations easier to understand. With Bitsight, security leaders can easily communicate essential findings to executives, Board members, and stakeholders with non-technical backgrounds. Users can quickly pull metrics into cybersecurity KPI dashboards and reports, using built-in templates and cybersecurity executive summary examples to streamline reporting efforts.
Bitsight analyzed over 27,000 companies over two years and compared their security ratings to a comprehensive set of disclosed data breaches.
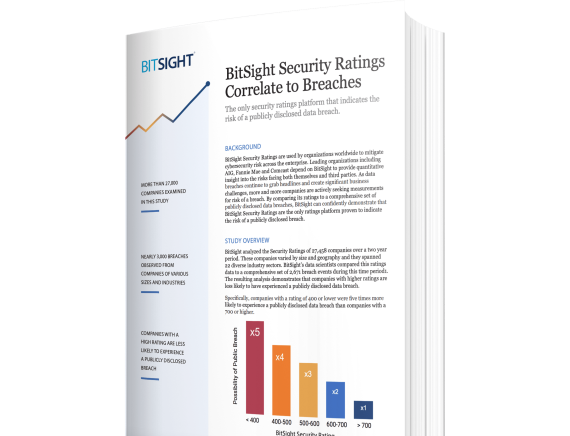
Through an analysis of 27,000+ companies over a two-year period, Bitsight’s data scientists, working alongside AIR Worldwide’s research and analysis team, determined that Bitsight Security Ratings are the only ratings platform proven to indicate the risk of a publicly disclosed breach.
The study confirmed that companies with a Bitsight Rating of 400 or lower were 5x more likely to experience a publicly disclosed data breach than companies with a rating of 700 or higher.
Bitsight is the world’s leading provider of cyber risk intelligence, transforming how security leaders manage and mitigate risk. Leveraging the most comprehensive external data and analytics, Bitsight empowers organizations to make confident, data-backed decisions and equips security and compliance teams from over 3,300 organizations across 70+ countries with the tools to proactively detect exposures and take immediate action to protect their enterprises and supply chains.
Bitsight customers include 38% of Fortune 500 companies, 4 of the top 5 investment banks, and 180+ government agencies and quasi-governmental authorities, including U.S. and global financial regulators.
Bitsight operates one of the largest risk datasets in the world. Leveraging over 10 years of experience collecting, attributing, and assessing risk across millions of entities, we combine the power of AI with the curation of technical researchers to unlock an unparalleled view of your organization. Bitsight offers more complete visibility into important risk areas such as botnets, mobile apps, IoT systems, and more. Our cyber data collection and scanning capabilities include:
Bitsight offers a full analytics suite that addresses the challenges of peer comparison, digital risk exposure, and future performance.
Bitsight is the only rating solution with third-party validation of correlation to breach from AIR Worldwide and IHS Markit.
Bitsight drives proven ROI with significant operational efficiency and risk reduction outcomes.
Bitsight incorporates the criticality of risk vectors in to calculation of Security Ratings, highlighting risk in a more diversified way to ensure the most critical assets and vulnerabilities are ranked higher.
A cyber security policy details the practices, standards for behavior, and measurable goals that an organization requires to prevent and recover from cyberattacks.
Cyber security policies cover a broad range of potential security concerns, and can be specific to a given industry or global region. Policies may outline the acceptable use of the corporate network and systems, define ideal cyber hygiene, or determine how responses to a data breach should be handled. Access control policies define the standards for who can access the network and what controls are in place to limit and authenticate users. Security policies should also outline a disaster recovery plan that will manage response teams after an incident, and a business continuity plan can ensure operations continue while hardware, software and data are being restored.
Establishing cyber security policy is an essential part of protecting organizations against cyber risk. As the landscape of cyber threats rapidly evolves, cyber security policies must adapt at an equal pace to help organizations avoid security incidents and major breaches.
Security and risk teams don’t need to draft cyber security policy from scratch. There are plenty of security frameworks and guidelines that provide excellent cyber security policy examples. However, security policy must be created in coordination with the Board and C-suite – and that task can be more complicated.
Many executives and Board members lack the technical background to develop or approve cyber security policy based on highly technical reports and presentations. To get the buy-in of organizational leadership, security and risk managers must communicate risks, security performance gaps, and recommendations for remediation in business terms that everyone can understand.
Bitsight can help. Bitsight Executive Reporting provides tools that make security performance understandable and accessible to senior leadership, driving more productive conversations about cyber risk as well as cyber security policies.
When looking for recommendations and examples of cyber security policy, these common frameworks make it easier to define the processes and procedures organizations can take to assess, monitor, and remediate cyber security risk.
Setting cybersecurity policy is a critical step in protecting your organization against cyber threats. As cyberattacks grow more sophisticated and frequent, your organization’s policies must also evolve to incorporate more powerful defenses and more intelligent cyber risk mitigation.
As your board and C-suite work to set effective cybersecurity policy, their decision-making must be informed with a clear understanding of security posture and the risk posed by third-party vendors. However, preparing reports for executives is challenging and time-consuming. Security and risk managers often lack the proper cyber risk metrics to facilitate data-driven conversations on risk, security gaps, and resource allocation.
Bitsight Security Ratings for Executive Reporting helps security teams communicate effectively with the board and C-suite so decision-making can happen quicker. Bitsight’s metrics make security performance understandable and accessible for all stakeholders. Customizable reports make it easy to set goals and requirements for effective cybersecurity policy.
Security ratings are a data-driven, objective measurement of the security performance of an organization. Security ratings can help to manage cyber risk and establish cybersecurity policy, providing continuous measurement of third-party risk and internal security efforts.
Bitsight has pioneered the security ratings market since 2011. Today, Bitsight is the most widely adopted Security Ratings platform in the world. Derived from objective, verifiable information, Bitsight Security Ratings evaluate data from 120+ sources to provide insight into 23 risk factors across compromised systems, security diligence, user behavior, and data breaches. Security Ratings are calculated daily using a proprietary algorithm that weights each data point and generates a score from 250 to 900, with the current achievable range being 300-820. With Bitsight, organizations get the data and metrics they need to more effectively set cybersecurity policy.
Bitsight Security Ratings are a data-driven, objective measurement of the security posture of an organization and its third-party vendors. Security Ratings provide continuous measurement of the organization’s security performance and the risk within its supply chain. With insight gleaned from Bitsight’s cybersecurity ratings, organizations can make faster and more strategic decisions about cyber security policy.
Bitsight Security Ratings are informed by data drawn from 120+ sources that provides insight into 23 risk vectors in four categories of security: compromised systems, user behavior, security diligence, and data breaches. Security ratings are calculated daily and range from 250 to 900, with the current achievable range being 300-820 – higher numbers indicate a stronger security posture and correlate to financial performance.
Bitsight Security Ratings play multiple roles in managing cyber security policy. For example, organizations can use Bitsight ratings to measure the effectiveness of a policy over time. Because Bitsight provides detailed cyber security assessment information about vulnerabilities such as botnet infections, malware servers, spam propagation, open ports, patching cadence, filesharing, and exposed credentials, security and risk team can also use Bitsight ratings to create and revise policy based on comprehensive visibility into the adapting risks within its digital ecosystem.
Bitsight Executive Reporting provides tools that help security and risk managers quickly and easily compile metrics for reports to executives and the Board. By making security performance reports accessible and contextual, Bitsight helps organizations review the effectiveness of cyber security policies with summaries of where the program successfully mitigated risk as well as where threats and vulnerabilities need remediation.
Executive Reports can provide information at a high level or with granular detail about compromised systems, vulnerabilities, security diligence, user behavior risks, network infrastructure, and domain infrastructure. Reporting in the Bitsight platform is intuitive, and users do not need specific technical knowledge to create reports. Reports can be customized by your security team looking to communicate specific points, or can generated from more than a dozen readily available reports, making it easy to communicate with leadership about the security performance of the organization and its vendor portfolio.
Bitsight is the world’s leading provider of cyber risk intelligence, transforming how security leaders manage and mitigate risk. Leveraging the most comprehensive external data and analytics, Bitsight empowers organizations to make confident, data-backed decisions and equips security and compliance teams from over 3,300 organizations across 70+ countries with the tools to proactively detect exposures and take immediate action to protect their enterprises and supply chains.
Bitsight customers include 38% of Fortune 500 companies, 4 of the top 5 investment banks, and 180+ government agencies and quasi-governmental authorities, including U.S. and global financial regulators.
Bitsight operates one of the largest risk datasets in the world. Leveraging over 10 years of experience collecting, attributing, and assessing risk across millions of entities, we combine the power of AI with the curation of technical researchers to unlock an unparalleled view of your organization. Bitsight offers more complete visibility into important risk areas such as botnets, mobile apps, IoT systems, and more. Our cyber data collection and scanning capabilities include:
Bitsight offers a full analytics suite that addresses the challenges of peer comparison, digital risk exposure, and future performance.
Bitsight is the only rating solution with third-party validation of correlation to breach from AIR Worldwide and IHS Markit.
Bitsight drives proven ROI with significant operational efficiency and risk reduction outcomes.
Bitsight incorporates the criticality of risk vectors in to calculation of Security Ratings, highlighting risk in a more diversified way to ensure the most critical assets and vulnerabilities are ranked higher.

CTI doesn’t need to be noisy.
Get clear on what you really need from your threat intel. This guide helps CISOs prioritize, assess vendors, and build a CTI program that fuels proactive security and compliance.
A cybersecurity maturity model is a framework of security practices, guidelines, and controls that provide an organization with a roadmap for creating effective, and at times compliant, cybersecurity programs.
The NIST Cybersecurity Framework, ISO 27000, and CIS 20 are among the most widely adopted cybersecurity maturity models. Other frameworks include the European Union’s General Data Protection Regulation (GDPR), the Payment Card Industry Data Security Standard (PCI DSS), and the Health Insurance Portability and Accountability Act (HIPAA).
There are three primary frameworks that are considered the gold standard when it comes to cybersecurity maturity models.
The National Institute of Standards and Technology (NIST) is a cybersecurity maturity model that’s often used by U.S. organizations. In this model, establishing and communicating tolerance for risk are the keys to increasing security. The NIST framework accommodates a rapidly evolving threat landscape and advises security teams that adopt this model to adjust monitoring techniques and remediation strategies to match the ongoing threat environment.
ISO 27000 is an international standard created by the Internal Standardization Organization (ISO) to outline best practices for information security management systems. This cybersecurity maturity model has more popularity in the European Union and focuses on people, processes, and technology as the three main areas of focus to mature your cybersecurity management program.
This cybersecurity maturity model, developed by the Center for Internet Security (CIS), is a series of 20 critical controls for protecting organizations’ network from cyberattacks. The CIS 20 model is designed to be all-encompassing and requires extreme attention to an organization’s cybersecurity management processes.
When followed, each of these frameworks can help to mature security programs, improve cyber hygiene, and mitigate risk throughout a digital ecosystem. Organizations can choose to follow a chosen cybersecurity maturity model based on common practices in their industry or among peers, or may be required to comply with a specific framework (like HIPAA or DORA). Each offers cyber security policy examples that can accelerate the work of security and risk teams as they work to build effective programs.
In the realm of security frameworks, distinguishing between cybersecurity and information security maturity models is crucial. While intertwined, these models present distinct strategies for bolstering an organization's defenses and safeguarding its assets.
Within this model, a comprehensive strategy is employed to combat cyber threats, encompassing technology, processes, and personnel both within and beyond the organizational boundaries.
This model primarily focuses on preserving the integrity, confidentiality, and availability of sensitive information. It aligns meticulously with specific standards and regulatory compliance measures.
Understanding these nuanced differences is pivotal for organizations seeking alignment with requisite frameworks and standards essential for meeting operational and compliance needs. While both share common goals of enhancing security and mitigating risks, the cybersecurity maturity model typically has a broader scope (cited in the examples above), addressing various aspects of cyber defense, whereas the information security maturity model is more specific in managing information-related risks and compliance.
For security and risk managers, a cybersecurity maturity model can provide invaluable guidelines for mitigating risk throughout the organization and vendor ecosystem. Basing security practices on proven, well-known models, some tailored to specific industries or world regions, can help to mature programs more quickly, improve security posture, and mitigate third-party risk.
In an ideal cybersecurity maturity model, a variety of processes, tools, and people are all aligned and working together to successfully mitigate risk. Mature security programs have buy-in from the C-suite and the Board, and goals are understood by departments throughout the organization.
Every maturity model requires comprehensive cybersecurity visibility into the organization’s digital ecosystem and vendor network. As the world’s leading Security Ratings platform, Bitsight provides the visibility that can help organizations refine their security and risk programs to bring practices in line with their preferred cybersecurity maturity model.
Bitsight transforms how companies manage security and risk. The Bitsight Security Ratings platform provides a suite of solutions that help organizations understand the risk landscape, close security performance gaps, and bring programs in line with the cybersecurity maturity models they have adopted.
Security Ratings are at the heart of the Bitsight platform. Bitsight’s cybersecurity ratings provide a comprehensive, outside-in view of the company’s overall cybersecurity posture, as well as a granular view of security performance relating to key risk vectors. Bitsight Security Ratings range from 250 to 900, with higher ratings equating to a better overall security posture. Ratings are based on externally verifiable information drawn from 120+ sources concerning 25 key risk vectors. These fall into four major categories – evidence of compromised systems, diligence to security practices, risky user behavior, and public disclosure of breaches. By analyzing and weighing this data with a proprietary algorithm, Bitsight issues daily Security Ratings for over 540,000 organizations.
Bitsight ratings can help security maturity in multiple ways:
Bitsight serves as a continuous monitoring solution, providing near-real-time insight into risk within an organization’s digital ecosystem and third-party network. This information can help security teams to identify and remediate the most critical risks and vulnerabilities more quickly.
By identifying the most severe areas of risk and highest concentrations of risk within an organization, Bitsight helps security teams to focus limited resources on remediating the greatest threats.
Bitsight Security Ratings provide a common language for organizations to discuss security performance and risk management. Bitsight’s easy-to-understand reports enable those without a technical or cybersecurity background to understand the risk an organization faces, enabling more productive conversation and decision-making around risk and security programs.
Bitsight Security Ratings provide the intelligence for a suite of solutions that can help to improve security performance and mitigate third-party risk. Working with Bitsight solutions, security and risk teams can more effectively bring programs in line with a given cybersecurity maturity model.
Bitsight exposes cyber risk within the supply chain by continuously measuring and monitoring the security performance of vendors. By helping to focus resources and providing insight that can be shared with vendors to work cohesively, Bitsight helps third-party risk managers achieve significant and measurable cyber risk reduction.
Bitsight helps manage the performance of cybersecurity programs through broad measurement, continuous monitoring, financial quantification of risk, and detailed planning and forecasting.
By delivering comprehensive visibility into the organization’s attack surface, Bitsight Attack Surface Analytics helps security teams get a handle on the risk hidden in digital assets in the cloud, geographies, subsidiaries, and the remote workforce.
With Bitsight, organizations can perform a cyber security assessment to monitor their security posture, benchmark performance against industry peers, measure the impact of risk mitigation efforts, and report on security progress and results.
Bitsight is the world’s leading provider of cyber risk intelligence, transforming how security leaders manage and mitigate risk. Leveraging the most comprehensive external data and analytics, Bitsight empowers organizations to make confident, data-backed decisions and equips security and compliance teams from over 3,300 organizations across 70+ countries with the tools to proactively detect exposures and take immediate action to protect their enterprises and supply chains. Bitsight customers include 38% of Fortune 500 companies, 4 of the top 5 investment banks, and 180+ government agencies and quasi-governmental authorities, including U.S. and global financial regulators.
Bitsight operates one of the largest risk datasets in the world. Leveraging over 10 years of experience collecting, attributing, and assessing risk across millions of entities, we combine the power of AI with the curation of technical researchers to unlock an unparalleled view of your organization. Bitsight offers more complete visibility into important risk areas such as botnets, mobile apps, IoT systems, and more. Our cyber data collection and scanning capabilities include:
Bitsight offers a full analytics suite that addresses the challenges of peer comparison, digital risk exposure, and future performance.
Bitsight is the only rating solution with third-party validation of correlation to breach from AIR Worldwide and IHS Markit.
Bitsight drives proven ROI with significant operational efficiency and risk reduction outcomes.
Bitsight incorporates the criticality of risk vectors in to calculation of Security Ratings, highlighting risk in a more diversified way to ensure the most critical assets and vulnerabilities are ranked higher.
For security professionals, visibility into an organization’s digital ecosystem is critical to identifying, quantifying, and remediating risk. After all, it’s impossible to protect assets that can’t be seen. Yet, as IT environments continue to expand and become more complex, maintaining complete cybersecurity visibility is harder than ever. Cloud services, remote offices, diverse geographies, and multiple subsidiaries all present serious obstacles to visibility, making it hard to conduct cybersecurity risk assessments or to monitor security performance within an IT environment.
Bitsight can help. As the world’s leading cybersecurity ratings solution, Bitsight provides a suite of solutions that delivers superior cybersecurity visibility by enabling continuous monitoring, complete measurement across all endpoints, and detailed security planning and forecasting.
There are multiple challenges when seeking to maintain cybersecurity visibility in a complex and ever-expanding digital ecosystem.
As businesses are relying more and more on cloud services, just keeping track of endpoints within the cloud is a challenge, let alone maintaining complete visibility. Yet, each cloud instance must be properly configured, managed, and monitored according to the shared responsibility model.
Digital footprints are typically larger than security teams realize, thanks to old URLs, rogue IP addresses, and forgotten domains.
Residential IPs are now almost expected of organizations globally since the Covid-19 pandemic, yet they account for more than 90% of all observed malware infections and compromised systems. Maintaining cybersecurity visibility into these networks has presented challenges for organizations looking to balance their workforce’s needs with their business’s risk threshold.
Various divisions of an organization may be harboring digital assets that aren’t part of a parent company’s inventory, making it hard for security teams to know what’s out there and to ensure that it’s protected.
Employees can easily spin up new cloud instances and web services without the knowledge or approval of IT – whether intentional or not- creating security concerns and presenting new visibility challenges.
A firewall is a primary defense that should in theory serves as a line of defense for a network. In today’s network environment, considerable traffic occurs outside the firewall, making it difficult to see everything entering or leaving the network.
Assets that sit behind the firewall can be easily overlooked when it comes to patching, updates, and configuration – potentially opening them up to known vulnerabilities.
Desktops, laptops, mobile devices, and IoT devices are all vulnerable to exploits. The rise of BYOD has only made this problem worse – and made cybersecurity visibility more difficult.
As part of the Bitsight Security Ratings platform, Bitsight for Security Performance Management offers solutions that can deliver greater cybersecurity visibility. Using externally observable information, this Bitsight solution provides vital context for making informed decisions, and shines a light on the gaps in security performance. With Bitsight, you can understand the true size of your digital footprint, get visibility into your attack surface, and identify and remediate risk throughout your digital ecosystem.
Bitsight for Security Performance Management improves cybersecurity visibility through the use of its industry-leading Security Ratings. Bitsight ratings provide a data-driven measurement of an organization’s overall security performance as well as grades and granular detail on performance as it relates to individual risk vectors. Bitsight’s ratings are derived from over 120+ sources concerning 25 key risk vectors, many of which are unique to the Bitsight platform. This information examines externally verifiable evidence in four major categories: diligence in security practices, risky user behavior, compromised systems, and publicly disclosed data breaches. Bitsight issues daily ratings that provide an accurate and comparable assessment of an organization’s security posture – as well as a likelihood for breach.
Bitsight delivers the cybersecurity visibility organizations need to continuously monitor their digital ecosystem, expose risk related to critical assets, and prioritize remediation to maximize the impact of available resources. Bitsight’s solutions can also enhance cyber hygiene, improve cloud security posture management, and bring security programs in line with cybersecurity maturity models.
Bitsight Attack Surface Analytics delivers even greater visibility into an expanding digital ecosystem, helping security teams get a handle on the risk hidden in digital assets in the cloud, geographies, subsidiaries, and the remote workforce. This Bitsight solution makes it possible for IT and security teams to quickly validate their digital footprint, assess their security posture, reduce risk exposure, and drive higher security ratings.
Bitsight delivers unprecedented insight into digital assets across the organization’s entire attack surface. Rather than manually tracking assets with a spreadsheet, security teams can automatically discover all assets and identify specifically where they’re located in your network for quick remediation. A centralized dashboard provides the location of assets broken down by cloud provider, geography, and business unit. Bitsight also highlights the cyber risk associated with individual assets.
Bitsight can shine a light on shadow IT – those technology solutions procured or spun up by teams and individuals without the knowledge or approval of IT.
To improve visibility into cloud services, Bitsight shines a spotlight on the security of assets hosted in the cloud. Bitsight lists the precise location of each asset and reveals hidden vulnerabilities, infections, and misconfigurations that could expose the organization to the risk of a breach.
Bitsight provides ecosystem-wide views of digital assets, enabling teams to visualize areas of critical risk, determine areas of highest exposure, and prioritize remediation.
Bitsight is the world’s leading provider of cyber risk intelligence, transforming how security leaders manage and mitigate risk. Leveraging the most comprehensive external data and analytics, Bitsight empowers organizations to make confident, data-backed decisions and equips security and compliance teams from over 3,300 organizations across 70+ countries with the tools to proactively detect exposures and take immediate action to protect their enterprises and supply chains.
Bitsight customers include 38% of Fortune 500 companies, 4 of the top 5 investment banks, and 180+ government agencies and quasi-governmental authorities, including U.S. and global financial regulators.
Bitsight operates one of the largest risk datasets in the world. Leveraging over 10 years of experience collecting, attributing, and assessing risk across millions of entities, we combine the power of AI with the curation of technical researchers to unlock an unparalleled view of your organization. Bitsight offers more complete visibility into important risk areas such as botnets, mobile apps, IoT systems, and more. Our cyber data collection and scanning capabilities include:
Bitsight offers a full analytics suite that addresses the challenges of peer comparison, digital risk exposure, and future performance.
Bitsight is the only rating solution with third-party validation of correlation to breach from AIR Worldwide and IHS Markit.
Bitsight drives proven ROI with significant operational efficiency and risk reduction outcomes.
Bitsight incorporates the criticality of risk vectors in to calculation of Security Ratings, highlighting risk in a more diversified way to ensure the most critical assets and vulnerabilities are ranked higher.

Request your free custom report and see how you can start reducing your cyber risk exposure across your digital ecosystem: cloud assets across all geos & subsidiaries; discover shadow IT; security risk findings; and more!
Get a complete view of your organization’s attack surface — both on-premise and in the cloud and discover where your organization's cyber risk is.
