Stealer malware is thriving—especially Lumma and Risepro. These logs fuel ransomware, MFA bypass, and persistent access. It's $10 to compromise an account. Explore this and other insights the data reveals.
Why Infostealers Are Central to Third-Party Breaches: A Look at the Top Malware Targeting Your Vendors


How Infostealer malware turns vendor access into supply chain breaches
When threat actors compromise your vendors, they are rarely aiming for a single, isolated win. They are looking for leverage. Every third party represents a potential force multiplier: a trusted connection, a shared platform, a pathway into multiple downstream environments. We recently looked at the vulnerabilities that are most commonly being used against vendors, but vulnerabilities alone don’t tell the full story. To understand how attackers turn third-party exposure into real-world impact, you need to follow the malware.
Drawing on data from the Bitsight Cyber Threat Intelligence portal—including monitoring across the clear, deep, and dark web, as well as stealer log analysis and infection telemetry—we analyzed activity targeting vendors commonly managed in third-party risk management (TPRM) programs. This includes MSPs, software vendors, healthcare suppliers, financial services firms, and the many non-tech companies that connect directly into customer systems.
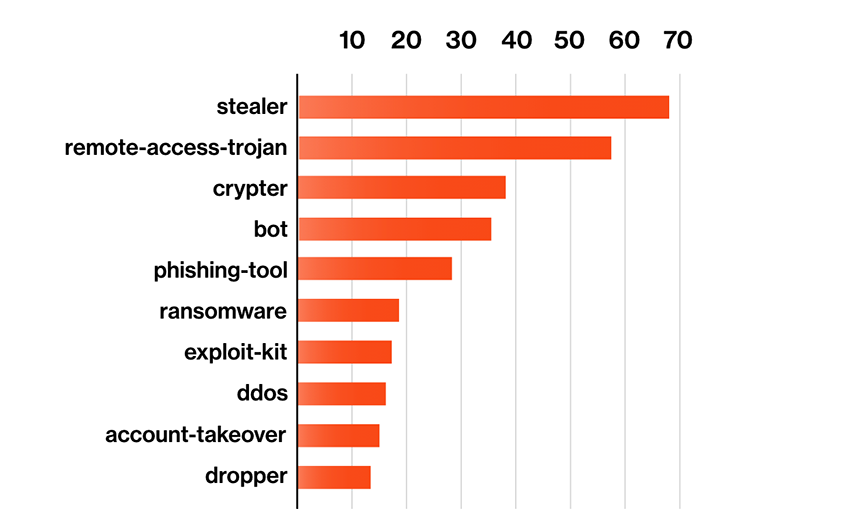
Our research reveals a consistent pattern. Threat actors are thinking beyond opportunistic disruption and prioritizing credential harvesting above all else. Infostealer malware dominates the top strains impacting vendors, systematically collecting passwords, session tokens, and authentication artifacts that can be reused to access customer environments as trusted users. These infections serve as gateways into broader third-party breach attack chains.
For attackers, a single infected vendor endpoint can unlock access to dozens, sometimes hundreds, of downstream organizations. That is why vendor infections command a premium in underground markets and why credential theft has become the foundation of modern supply chain attack activity.
In order to help TPRM leaders focus on the controls that manage the risks they’re most likely to face, let’s dig into five of the most common infostealers targeting supply chains and examine how these are fueling the wider cybercriminal economy.
Top Infostealer malware strains targeting third-party vendors
The malware families most commonly targeting vendors share a singular purpose: industrializing credential theft at scale. Each of these infostealers operates as a malware-as-a-service (MaaS) offering. With these MaaS schemes, criminal operators maintain the malware, provide customer support, and sell subscriptions to affiliates who use the tools to harvest credentials. Some operators also monetize credential streams directly, selling stolen logs on dark web markets or providing panel access to buyers looking for ready-to-use access.
They include:
- Lumma/LummaC2: A MaaS infostealer that systematically harvests browser-stored credentials, cookies, VPN profiles, and crypto wallets. Before May 2025 takedown efforts, Lumma accounted for nearly 92% of credential log alerts on Russian marketplaces in late 2024. The global disruption effort was spurred on when Microsoft observed ransomware groups using Lumma-harvested credentials to breach downstream targets. Lumma’s operators ran both a subscription service for affiliates and a credential marketplace where stolen logs were sold.
- Vidar: This MaaS stealer has scooped up tens of millions of stolen passwords over the past several years. Most recently, Vidar 2.0 late last year added techniques to bypass Chrome’s latest credential protection and expanded its reach to cloud credentials, messaging apps, and crypto currency wallets. What makes Vidar especially dangerous in vendor environments is it doubles as a loader. This means attackers can use a single infection to both harvest credentials for customer systems and establish persistent access in the vendor's network for later use.
- Acreed: This infostealer surged to dominance after Lumma’s May 2025 takedown. Like its predecessor, it targets browser credentials, session tokens, and cryptocurrency wallets. TPRM leaders should note that this one is particularly dangerous because it has a feature to hijack active session tokens to bypass MFA. This opens the door to lateral movement into customer systems even when strong authentication is in play. Security researchers describe Acreed as a full-fledged access broker, providing ransomware affiliates with ready-to-use pathways into enterprise networks. We see this model as the future of attackers taking advantage of supply chain connectivity.
- Rhadamanthys: A premium MaaS stealer known for sophisticated evasion and persistence capabilities. Its ability to steal document files alongside credentials sets it apart, along with AI-powered image recognition that can extract details like cryptocurrency seed phrases from screenshots. Attackers distribute it through SEO poisoning of legitimate software downloads. So, a vendor employee searching for tools like Zoom or Notepad++ can end up infected instead. For TPRM leaders, the document theft angle is particularly concerning. A single infection can exfiltrate not just passwords, but also contracts, customer lists, and other sensitive files that can be used for more sophisticated future attacks.
- StealC: Going strong since it emerged in 2023, this MaaS tool was built using a combination of different techniques pioneered for credential harvesting over the last several years. It targets over 20 browsers and 70 browser plug-ins, including password managers and SSO extensions that vendor employees commonly rely on. The plugin breadth makes it a particularly potent tool for sweeping up every credential they might have stored across different customer portals, admin consoles, and remote support tools.
Why MaaS operators home in on third-party vendors
Like any savvy business leader, the criminal operators behind these infostealer-as-a-service platforms are looking for every opportunity to optimize their ROI. Vendor infections deliver those opportunities on a platter.
Whether it is an MSP engineer’s laptop or a healthcare administrator’s computer, when an infostealer lands on the right vendor endpoint, the criminals stand to yield high-value credentials for dozens, hundreds, or even thousands of organizations at once.
According to Bitsight Threat Intelligence, credential compromise has surged dramatically, with a 160% increase in compromised credentials in 2025 compared to the prior year. Stolen credentials remain the most effective path to intrusion, enabling successful compromise in 98% of cases by allowing attackers to bypass traditional defenses altogether. Adversaries acquire these credentials through phishing campaigns, credential-stuffing attacks, and third-party breaches, blending seamlessly into legitimate user activity. As a result, compromised credentials now account for 47% of security incidents, with a single exposed password often cascading into data theft, resource abuse, or ransomware deployment, reinforcing why vendors have become such powerful force multipliers in the modern criminal supply chain.
Third-Party Risk Management strategies against Infostealer attacks
Infostealers have become the gateway to third-party breaches. This means that TPRM programs need to get serious about educating their vendors and working with them to minimize their exposure to wholesale credential harvest. One effective starting point is to reposition dark web monitoring as an internal risk signal. Expanding coverage beyond first-party domains to include critical vendors’ domains in stealer logs and credential dumps enables earlier detection and when those credentials surface, they should trigger a shared incident response.
Organizations that handle third-party credential exposure as a coordinated incident response exercise with clear notification timelines and joint credential rotation can contain damage faster and shrink the window for attackers to exploit stolen access. In regulated industries like financial services and healthcare, these arrangements are increasingly required by contract and regulation. For everyone else, it’s an approach worth building toward.
Want to see how your program looks to an attacker? Bitsight’s free Threat Assessment gives you a personalized look at the signals that attackers see when targeting your organization. Using intelligence gathered from the clear, deep, and dark web, this report surfaces risks that are often missed by traditional tools.



