The 2025 State of Cyber Risk and Exposure report reveals why security leaders are under pressure: AI-driven threats, expanding attack surfaces, and misalignment with business priorities. Based on global survey data, it surfaces the root causes behind today’s risk fatigue—and what mature organizations are doing differently.
The Hidden Third-Party Risks Behind Domain Hijacking


Domains are foundational to digital trust. You visit your favorite online store or log in to your email without thinking twice about the web address in your browser. But what happens if that domain has been hijacked and you have just entered your personal information into an attacker’s trap?
The modern domain ecosystem is deeply intertwined with third parties, including DNS providers, registrars, SaaS platforms, CDNs, cloud hosts, and marketing tools. Many organizations rely on these external providers to manage and host critical domain infrastructure. Yet how do you know if your hosting provider is secure, or whether their systems have already been compromised? Domain hijacking is no longer just an internal security failure. It is increasingly a third-party risk management issue that extends beyond your own network and into your broader digital supply chain.
What is domain hijacking?
Domain hijacking is the unauthorized takeover or manipulation of a domain name or its associated services. This can occur in several ways, including compromise of a registrar account, unauthorized changes to DNS records, nameserver takeover, subdomain hijacking caused by misconfigured or abandoned services, and the re-registration of expired domains that were not properly renewed.
Because domains control where web and email traffic is directed, attackers who gain access can cause significant harm. Real world consequences often include website defacement, redirection of legitimate traffic to malicious destinations, phishing campaigns hosted on trusted domains, interception of email through unauthorized changes to MX records, and long-term brand damage that erodes customer trust.
How third parties expand the attack surface
Third parties significantly expand the domain attack surface by introducing additional points of failure outside an organization’s direct control. Registrar and DNS providers are frequent targets because compromise of credentials, weak multi-factor authentication policies, exposed API keys, or even insider threats at the service provider can allow attackers to alter domain settings at scale.
SaaS and cloud dependencies create further risk, particularly when dangling DNS records point to deprovisioned services, cloud storage or CDN endpoints are misconfigured, or forgotten staging environments remain publicly accessible. Marketing teams and external vendors can also introduce exposure when agencies manage DNS without proper security oversight, third-party tools require DNS verification changes, or shadow IT leads to decentralized domain ownership. As domain management extends beyond core IT teams, organizations often lose visibility and control, making it easier for attackers to exploit gaps in governance and monitoring.
Common attack scenarios involving third parties
Real world incidents highlight how third-party weaknesses can enable large scale domain abuse. For example, Guardio Labs uncovered a campaign known as “SubdoMailing,” in which attackers hijacked more than 8,000 subdomains belonging to well known brands and institutions, including MSN, McAfee, The Economist, Cornell University, CBS, Marvel, and eBay. By taking control of misconfigured or abandoned subdomains, the attackers leveraged the inherent trust of those brands to distribute massive volumes of spam and phishing emails. The campaign demonstrated how subdomain takeovers can scale when DNS records point to deprovisioned services and no one is actively monitoring them.
Subdomain takeovers and dangling DNS risks
One common scenario is phishing via subdomain takeover. In this attack flow, an organization creates a DNS record pointing to a third-party service such as a cloud application or marketing platform. When that service is later decommissioned but the DNS record remains, an attacker can claim the external resource and host malicious content on a trusted subdomain.
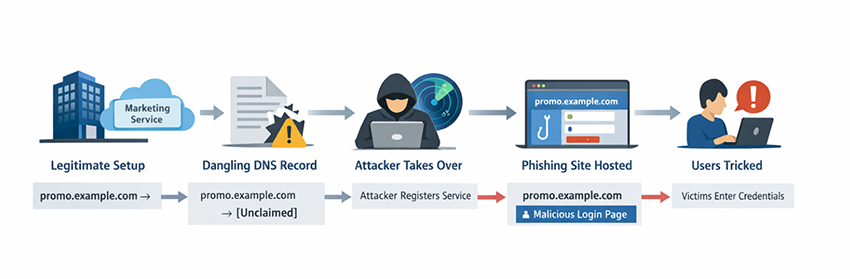
Detection is often delayed because the primary domain remains intact and security teams may not continuously monitor unused subdomains. Governance typically breaks down when ownership of DNS entries is unclear or when offboarding processes for vendors do not include DNS cleanup.
Registrar compromise and DNS hijacking
Another scenario involves DNS hijacking through a compromised registrar account. An attacker gains access through stolen credentials, weak authentication controls, or exposed API keys, then modifies nameservers or DNS records to redirect traffic or intercept email. The step-by-step process can take only minutes, and organizations without MFA, registry locks, or DNS change alerts may not detect it until traffic or email has already been redirected.
In 2018 attackers manipulated internet routing in MyEtherWallet to redirect users to a malicious server that mimicked the legitimate site. Although this attack involved a Border Gateway Protocol (BGP) hijack affecting DNS resolution rather than direct compromise of a registrar account, it illustrates the broader risk: when attackers gain control over DNS infrastructure, even briefly, they can reroute traffic, present seemingly valid TLS certificates, and harvest sensitive credentials within minutes.
Email interception and business email compromise
A third scenario arises when an expired or deprovisioned vendor service leaves behind an exploitable DNS record. Similar to subdomain takeover, attackers actively scan for dangling DNS records that reference cloud storage buckets, CDN endpoints, or SaaS platforms that are no longer claimed. If the underlying resource has been deleted but the CNAME or other DNS record remains in place, an attacker can re-register or claim the external service and gain control of content under legitimate corporate subdomains.
Research from Bitsight TRACE has also shown that abandoned domains can continue receiving traffic long after they are no longer in use. In one observed case, hundreds of expired calendar domains were still receiving synchronization requests from millions of devices, demonstrating how forgotten external dependencies can create persistent and exploitable trust relationships at scale. This allows them to host phishing pages, malware, or fraudulent content that inherits the trust of the parent domain.
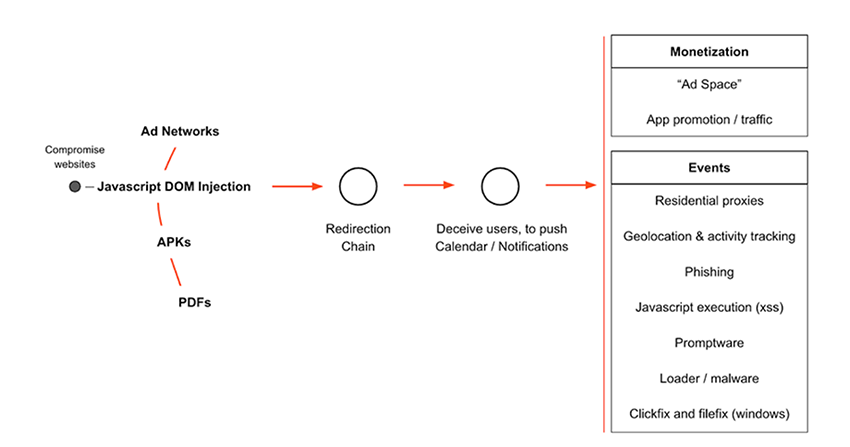
Security researchers have demonstrated this risk across platforms such as Shopify and GitHub Pages, where deleted hosted sites left behind CNAME records that enabled attackers to claim the unregistered resource and serve malicious content under trusted corporate subdomains. Because the exposure exists outside the organization’s core network and responsibility for DNS hygiene frequently falls between IT, security, and business units, timely detection can become difficult.
Finally, business email compromise can occur through unauthorized MX record changes or other manipulation of domain and DNS settings. If an attacker gains access to a registrar or DNS management console, they can modify mail exchange records to reroute email traffic to infrastructure they control. This enables interception of sensitive communications, credential harvesting, or impersonation of executives and finance teams to facilitate wire fraud.
Governance failures typically include insufficient monitoring of DNS changes, weak authentication controls at the registrar level, and limited integration between domain management and third party risk oversight. The FBI has repeatedly warned in its Internet Crime Complaint Center annual reports that attackers increasingly target email infrastructure, including DNS and domain configurations, to enable business email compromise and financial fraud, underscoring the growing importance of protecting domain level controls as part of enterprise security strategy.
Why traditional security programs miss domain risk
Traditional security programs and teams tend to focus primarily on endpoints, internal networks, and core infrastructure, often due to limited bandwidth, tooling constraints, or a mandate centered on assets inside the corporate perimeter. As a result, domain and DNS security can fall outside day-to-day monitoring priorities.
Many organizations have limited visibility into DNS record changes, especially when management is handled through third-party registrars or external providers. Maintaining a complete and accurate domain inventory is also a persistent challenge, particularly in large enterprises with regional offices, acquisitions, or decentralized purchasing authority. Organizational silos further complicate oversight, as security, IT, and marketing teams may each manage different aspects of domains without shared governance or centralized tracking. In addition, vendor risk assessments frequently evaluate data handling and access controls but overlook DNS posture and registrar security settings, leaving a critical layer of the attack surface insufficiently assessed.
Business impact: More than just website downtime
The impact of domain hijacking extends far beyond temporary website outages. When a domain is compromised, customer trust can erode quickly, especially if phishing, email interception, or data exposure occurs under a trusted brand name. The consequences often create a domino effect that reaches customers, vendors, and even third- and fourth-party partners, particularly if stolen credentials or malicious emails are used to pivot deeper into the supply chain. Regulatory implications may follow, including data protection investigations, breach notification requirements, and potential fines depending on the jurisdiction and the nature of the data involved. Publicly disclosed incidents can also contribute to reputational damage and, in some cases, short-term stock price volatility as markets react to perceived governance failures.
Beyond immediate financial loss, organizations may experience longer term supply chain amplification effects, where trust deteriorates across their ecosystem. Domain related incidents can also negatively influence digital risk assessments and external security ratings, shaping how customers, partners, insurers, and investors perceive an organization’s overall security posture.
How to reduce domain hijacking risk in a third-party ecosystem
Reducing domain hijacking risk requires a coordinated approach that extends beyond internal IT and into the extended attack surface. Organizations should begin by strengthening domain governance through a centralized and continuously updated domain inventory, with clearly defined ownership and lifecycle management processes for every domain and subdomain. Registrar lock and registry lock protections should be enabled wherever available, along with enforced multi factor authentication and role based access controls for all registrar and DNS accounts. Employee training is equally important, particularly for teams that interact with vendors or request DNS changes, so that domain security is treated as a shared responsibility across internal departments and external partners.
Continuous DNS monitoring is critical to detecting misuse early. Security teams should implement alerts for changes to nameserver, MX, and A records, actively scan for dangling DNS records that point to deprovisioned services, monitor certificate issuance for unauthorized TLS certificates, and track subdomain sprawl across the organization. Suspicious domains, phishing sites, and anomalous DNS changes should be promptly reported and investigated to limit downstream impact.
Domain risk should also be formally integrated into third-party risk management programs. Vendor security reviews should include evaluation of DNS controls and registrar security practices, with requirements for multi-factor authentication and strong account protections. Organizations should carefully assess vendors that require DNS modifications as part of onboarding and continuously monitor their external attack surface for emerging exposures. Regular audits of vendors and domain management providers can help validate that security controls remain effective over time and that contractual expectations are being met.
Finally, incident response preparedness is essential. Organizations should document registrar escalation procedures, validate 24/7 emergency contact information, and maintain predefined domain recovery playbooks that outline technical, legal, and communications steps. Practicing these procedures through tabletop exercises can significantly reduce recovery time and limit business disruption if a domain hijacking incident occurs.
The future: Domain risk as an external attack surface signal
As organizations mature their security programs, domain risk is increasingly emerging as a measurable external attack surface signal. Domain posture, including DNS configuration hygiene, subdomain management, certificate transparency monitoring, and registrar security controls, can provide observable indicators of overall security discipline.
Poor domain hygiene, such as dangling DNS records or inconsistent ownership controls, may correlate with broader governance gaps that increase breach likelihood. At the same time, domains offer external visibility into third party dependencies, revealing relationships with SaaS platforms, cloud providers, marketing tools, and other vendors that expand the attack surface. The future of domain security lies in shifting from reactive cleanup after incidents occur to proactive, continuous monitoring that identifies exposure before it is weaponized by attackers.
How Bitsight can help
Managing domain risk across a complex digital ecosystem requires external visibility and continuous intelligence. Bitsight helps organizations identify and reduce exposure by providing vendor insights and risk views that offer objective insight into the security posture of third parties, including indicators tied to domain hygiene and external attack surface management. By monitoring vendors continuously, organizations can detect emerging risks that traditional point in time assessments may miss.
Bitsight’s Threat Intelligence capabilities provide actionable insight into third-party exposures, including indicators of compromised infrastructure, phishing activity, and malicious campaigns that may involve trusted domains. Dark Web Intelligence for Supply Chains further strengthens this visibility by identifying leaked credentials, exposed data, and conversations related to compromised domains or vendor environments. In the event of active abuse, takedown services can assist organizations in removing fraudulent domains, phishing sites, and malicious infrastructure that exploit brand trust. Together, these capabilities enable organizations to move from reactive response to proactive risk reduction across their domain ecosystem and third party landscape.
To learn more about how Bitsight can help you stay ahead of domain-related threats, talk to our team.



