The 2025 State of Cyber Risk and Exposure report reveals why security leaders are under pressure: AI-driven threats, expanding attack surfaces, and misalignment with business priorities. Based on global survey data, it surfaces the root causes behind today’s risk fatigue—and what mature organizations are doing differently.
How Early Signals Surfaced by Dark Web Intelligence Enhance Supply Chain Cyber Resilience

Organizations are facing a complicated and unwieldy cybersecurity perimeter due to the sprawling web of third-party dependencies that now account for 30% of all data breaches. This network of interconnected applications and infrastructure gives threat actors an opportunity through an extended attack surface to exploit organizations.
Attackers are also moving faster by leveraging AI to weaponize zero-day vulnerabilities in days rather than weeks, and most organizations remain dangerously behind the curve. According to an IBM study in 2025;
- The average organization takes 241 days to identify and contain breaches in the supply chain
- The average cost of a breach in the US has soared to $10.22 million
To stay resilient, third-party risk management (TPRM) teams need a tool that allows them maximum visibility across their specific supply chain so they can respond to breach-related incidents in as close to real time as possible. This is exactly why Bitsight is introducing Breach Intelligence for Continuous Monitoring customers.
Breach Intelligence: Milestone of Dark Web Intelligence for Supply Chains
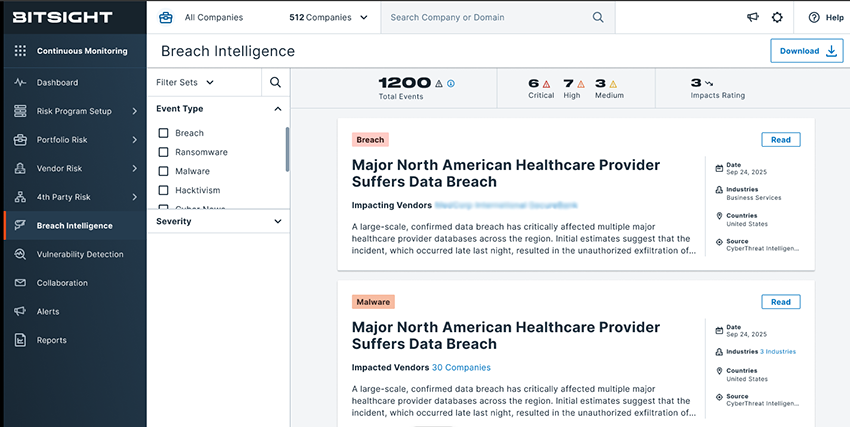
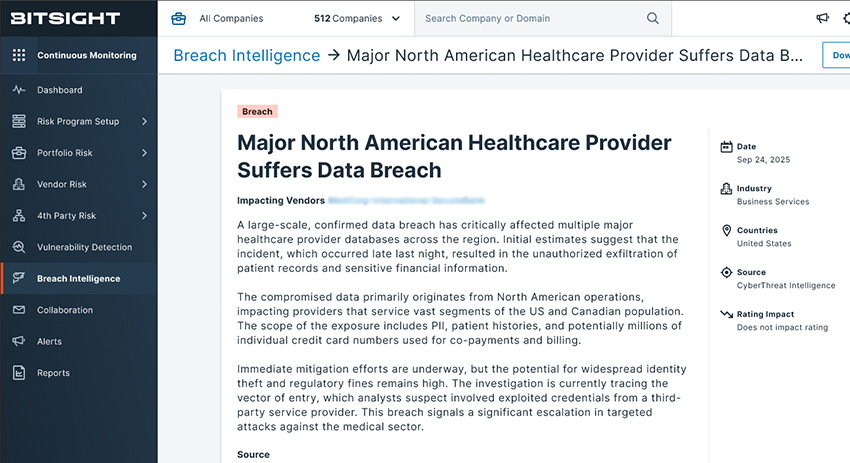
Following the announcement of Dark Web Intelligence for Supply Chains, a comprehensive capability that connects real-world threat intelligence with third-party exposure, we are excited to share that the next enhancement Breach Intelligence has become available. Breach Intelligence continues to evolve on Bitsight’s breach incident data, powered by Threat Intelligence and tailored for GRC and TPRM teams.
GRC teams and TPRM leaders increasingly recognize that threat actors are not static. Attack patterns evolve throughout the lifecycle of an incident, shifting targets, techniques, and timing in ways that render static reports and point-in-time assessments insufficient. A single data snapshot offers little insight into how a breach is unfolding or whether risk is accelerating across a vendor ecosystem. Continuous, real-time data intake is essential to understanding the true trajectory of adversary activity and maintaining an accurate view of exposure.
Breach Intelligence is built on an always-on collection at scale. Bitsight scans thousands of underground forums, dark web marketplaces, ransomware leak sites, Telegram channels, and public sources. This expansive coverage enables early detection of compromised data, exposed credentials, and vendor-related breach activity as it emerges, rather than days or weeks later through secondary reporting. This empowers security teams to move from reactive breach response to proactive, intelligence-led risk mitigation.
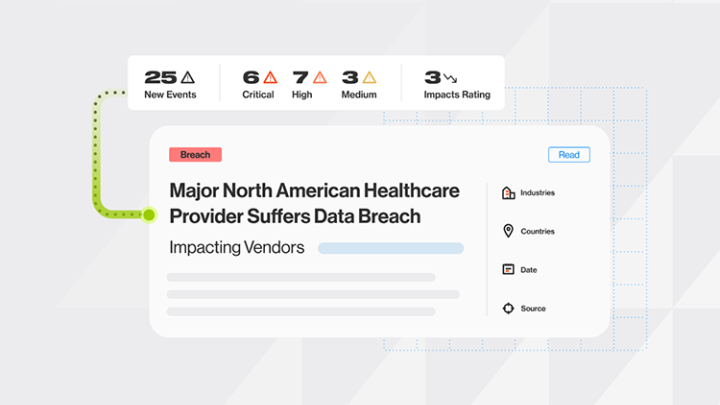
Key capabilities and benefits of Breach Intelligence:
- Delivers a unified feed of breach-related security incidents spanning a wide range of sources, including public news sites, telegram channels, breach forums, and ransomware leak sites.
- Surfaces events only relevant to your supply chain to eliminate noise frequently found in other breach feeds.
- Real time syncing from dark web sources accelerates response time and maximizes the effect of any mitigation steps deployed.
- Automatically classifies event severity and type so you don’t have to wonder what’s important.
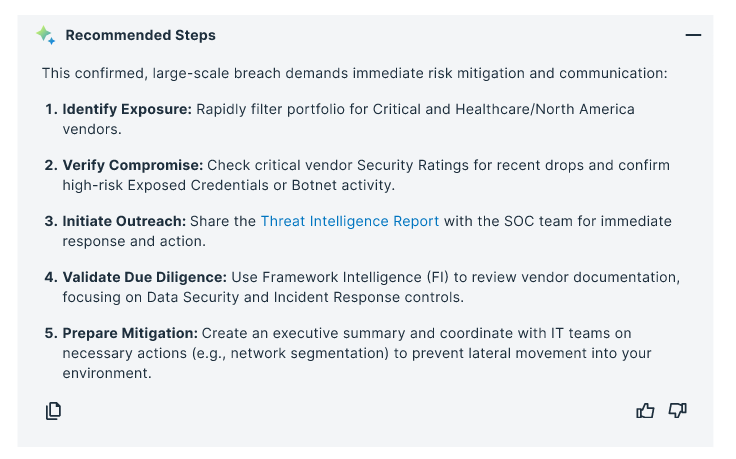
- Recommends actions based on event type and severity to simplify the breach response process.
Why it matters
- Delayed disclosure: Vendors often take weeks or months to investigate and legally vet a breach notification before informing their customers, which limits the ability to deploy internal mitigation strategies in conjunction with their security operations teams. Breach Intel solves this problem by monitoring what threat actors are discussing in real time.
- Threat landscape blind spots: Public news sites are only part of the equation, by actively and continuously monitoring dark web sources, TPRM teams can capture events from forums where threat actors engage.
- Datasource overload: There are literally hundreds of threat intel feeds and public news sites that disclose critical breach and other disruptive events, which presents a volume challenge for even the most experienced security teams. Breach Intelligence consolidates all of this information in one place that is tailored to your own supply-chain.
Supply chain resilience depends on early visibility. Breach Intelligence enhances Dark Web Intelligence for Supply Chains in Bitsight Continuous Monitoring with real-time, dark web-powered insights tailored to your vendor ecosystem, enabling TPRM and GRC teams to act faster and with greater precision.
By unifying underground signals, public disclosures, and AI-driven synthesis in one contextualized feed, organizations can reduce response time and proactively mitigate third-party risk before it escalates. This is just the beginning of unleashing the power of Threat Intelligence for Third-Party Risk Management. To learn more, request a Breach Intelligence demo.



