Stealer malware is thriving—especially Lumma and Risepro. These logs fuel ransomware, MFA bypass, and persistent access. It's $10 to compromise an account. Explore this and other insights the data reveals.
Why Threat Actor Context Matters for Cyber Risk Prioritization


Cyber threat intelligence is often presented as a catalog of named threat actors, past incidents, and attribution labels that promise clarity. For defenders trying to understand risk, this structure feels reassuring. It suggests that threats can be identified, tracked, and anticipated based on observed behaviors.
In practice, that confidence is often overstated.
Threat actors are not static entities with fixed playbooks. They are individuals and groups that shift tactics in response to incentives, pressure, and the broader world around them. Assuming they’re predictable leads to outdated conclusions, poor prioritization, and decisions that can underestimate, or even amplify, current risk. To use adversary intelligence effectively, we must understand how and why attacker behavior changes.
The problem with treating threat actors as static
Many security tools and reports describe threat actors as stable, long-lived groups. Once an organization is linked to a named actor, that association often persists indefinitely, even if the underlying activity has stopped.
Real-world attacker behavior does not work that way.
Threat actors routinely change infrastructure, tooling, targets, and even identities. Groups fragment, merge, rebrand, or disappear entirely. Attribution reflects a moment in time, not a permanent state.
When attribution is treated as fixed, defenders end up managing yesterday’s behavior instead of today’s threat landscape.
How and why threat actors change over time
Threat actors do not operate in isolation. Their activity is shaped by forces outside the network, and changes in those forces often show up quickly in their tactics and targeting.
Financial incentives
Financially motivated actors are highly sensitive to profitability.
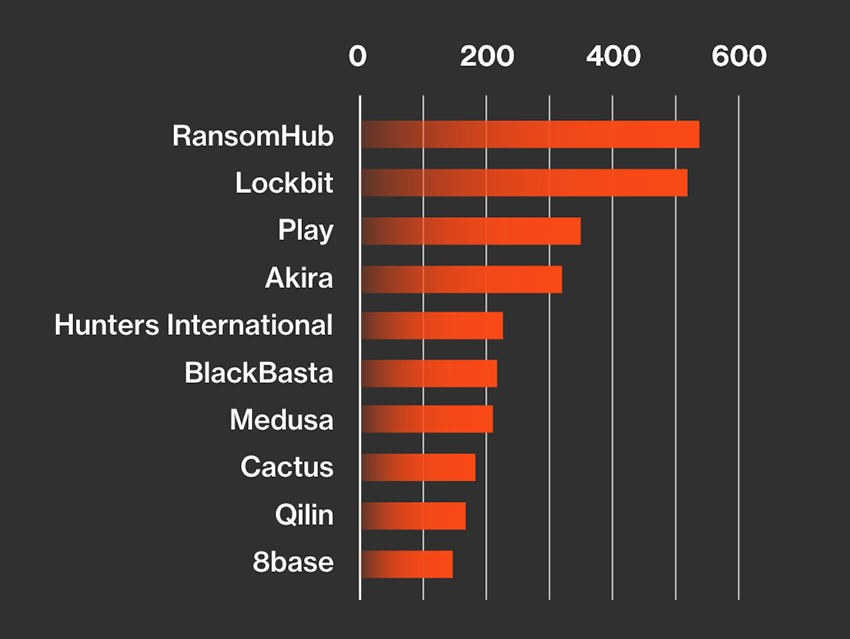
Ransomware groups provide a clear example. When ransomware payments are successful and enforcement pressure is low, activity tends to increase. When payments decline or risks rise, groups adapt.
After major ransomware disruptions and sanctions, several well-known ransomware operations have rebranded, splintered into smaller crews, or shifted toward quieter activities like initial access brokering. In some cases, the same operators resurface under new names using similar tooling, while previous group names fade from relevance.
Law enforcement and operational pressure
Law enforcement action can dramatically alter threat actor behavior.
The takedown of large criminal infrastructure, arrests of affiliates, or seizure of servers often leads to sudden drops in activity. In some cases, groups pause operations for months. In others, they reappear with new tooling, different malware families, or more cautious targeting.
This is why periods of apparent inactivity do not necessarily mean a threat is gone forever, but they do mean that historical behavior should not be treated as current risk without supporting evidence.
World events and geopolitics
Geopolitical events frequently influence threat activity.
Following Russia’s invasion of Ukraine in 2022, several cybercriminal and hacktivist groups changed their behavior almost overnight. Some ransomware groups publicly declared political alignment, while others shut down operations entirely after internal leaks exposed their members and infrastructure.
At the same time, hacktivist activity surged around specific geopolitical narratives, targeting government websites, media organizations, and critical infrastructure. Many of these campaigns were intense but short-lived, fading as global attention shifted.
These examples highlight how closely some threat activity is tied to external events rather than long-term strategic planning.
Access to tooling changes behavior
Threat actor tactics also evolve based on what tools are available.
The widespread exploitation of Log4Shell is a well-known example. Once the vulnerability became public, a wide range of actors began exploiting it, including ransomware groups, cryptominers, and state-aligned operators. Activity spiked rapidly, then declined as systems were patched and defenders adapted.
The actors involved did not fundamentally change, but their techniques and targeting priorities did. Treating exploitation behavior observed during that period as permanently representative would miss how quickly relevance faded.
Motivation often matters more than identity
When assessing risk, understanding why an actor operates is often more useful than knowing their name.
Financially motivated actors tend to follow opportunity. They target environments that are easier to compromise and more likely to pay. When conditions change, they pivot quickly.
Politically or strategically motivated actors operate on longer timelines. Their activity often aligns with national interests or geopolitical goals, and their targeting is more deliberate.
Ideological or activist actors are usually event-driven. Their activity spikes during moments of unrest or conflict and then drops just as quickly.
Two actors may use the same vulnerability or malware, but their intent, persistence, and risk profile can be very different depending on motivation and context.
The limits of static attribution
Static attribution models simplify threat intelligence, but that simplicity comes at a cost.
When past incidents are treated as indicators of ongoing risk, historical behavior can outweigh current evidence. Rapid changes in targeting or capability are missed. Security teams are left explaining why a labeled threat no longer aligns with what they are seeing today.
This often leads to confusion, alert fatigue, or misplaced urgency, especially when stakeholders expect threat intelligence to predict future attacks rather than explain past ones.
Thinking about threat actors as dynamic systems
A more accurate way to think about threat actors is as dynamic systems shaped by incentives, constraints, and opportunity.
Attribution becomes a snapshot rather than a verdict. Threat intelligence becomes a tool for interpretation rather than prediction.
Instead of asking whether a specific actor is associated with an organization, more useful questions include:
- When was this activity observed?
- What conditions enabled it?
- What pressures might cause it to change?
- What signals suggest it is still relevant?
These questions acknowledge uncertainty rather than hiding it.
Public-private partnerships have successfully disrupted major malware ecosystems, including infostealers like Lumma. In operations led by Bitsight and Microsoft in coordination with law enforcement agencies like the FBI, infrastructure has been seized and activity temporarily suppressed. Yet in several cases, operators resurfaced months later with new infrastructure, updated tooling, or revised distribution methods. Disruption altered the landscape, but it did not eliminate the financial incentives driving the activity.
This pattern reinforces that threat actors are and will remain dynamic.
Turning threat actor context into actionable cyber risk intelligence
By grounding threat actor context in real-time exposure and business impact, Bitsight’s Cyber Risk Intelligence solutions helps organizations move from static attribution to dynamic risk prioritization. In a landscape where attackers constantly adapt, risk intelligence must adapt faster.
Understanding that threat actors are dynamic rather than static changes how organizations should prioritize cyber risk. Attribution alone is not enough. What matters is whether the conditions that enabled past activity still exist, whether the motivation remains, and whether the signals suggest continued relevance.
This is where Bitsight Cyber Risk Intelligence (CRI) becomes essential. Rather than treating threat intelligence as a catalog of names and past incidents, CRI connects external threat context directly to observable risk signals across an organization and its third-party ecosystem. Through capabilities such as Cyber Threat Intelligence (CTI) and Dark Web Intelligence for Supply Chains, Bitsight translates shifting attacker behavior, active exploitation trends, credential exposure, and emerging campaign data into prioritized, measurable risk.
For security leaders and boards, this shift is critical. The question is no longer “Are we associated with a known threat actor?” but rather “Given how attacker incentives and capabilities are evolving, where are we materially exposed right now?”
By grounding threat actor context in real-time exposure and business impact, Bitsight’s Cyber Risk Intelligence solutions helps organizations move from static attribution to dynamic risk prioritization. In a landscape where attackers constantly adapt, risk intelligence must adapt faster.