Beyond Indicators: Gaining Context with Adversary Intelligence


Actions have consequences.
In cybersecurity, we often only see actions at the surface level: a suspicious IP, a new domain, or a single mention on a dark web forum.
For threat hunters, the consequences of treating these actions as isolated incidents are significant. These signals are rarely "one-offs." They are the visible tips of coordinated campaigns built on months of planning, spanning multiple tactics, techniques, and procedures (TTPs).
Today’s adversaries are organized. They don’t just attack randomly; they strategize and execute. The problem is that most security teams see individual threats, but miss the adversary context behind them. They lack the information to answer the questions that actually drive risk decisions:
- Who is behind this activity?
- How do they typically operate?
- Does it matter to our specific business, sector, or geography?
Without those answers, prioritization is just guesswork, and the consequences can be severe.
From industry news to actionable context
Consider how context changes the stakes in a real-world scenario:
Your team notices a major competitor listed on a ransomware leak site. There is no direct reference to your company, and no alerts have triggered in your environment.
Without context: It’s just industry news. You might flag it for a weekly report and move on.
With adversary context: The story changes instantly. You see that this specific ransomware group has targeted five organizations in your sector over the last 90 days. More importantly, you see the pattern: every attack used the same initial access vector of an exposed VPN appliance tied to a specific CVE.
You run a quick query and realize that the same vulnerable version exists in your own environment. Now, it’s not news. It’s a warning. And you finally have the intelligence to act before you become the next victim.
The "whack-an-adversary" trap
Without a centralized map of actor behavior, most organizations are left flying blind, relying on manual ad-hoc research to bridge the gap. When an alert is triggered, analysts jump between vendor portals, blogs, internal PDFs, and dark web forums to manually stitch together a narrative.
This approach creates blind spots, slows investigations, and wastes time on repetitive research. High-risk activity gets under-prioritized, low-value noise gets escalated, and MTTR rises. By the time teams understand the “who” and the “why,” the damage is often already done.
Stop chasing indicators. Start countering adversaries
Bitsight Threat Intelligence’s Adversary Intelligence module removes the guesswork by providing a centralized, "encyclopedic" view of global threat entities. It transforms fragmented data into a living model of actor behavior, giving teams context and perspective so they can defend the threats that matter with insights that position them for success.
Adversary Intelligence allows teams to:
- Pivot with context: Instantly move from a single indicator to see its global usage, related campaigns, and associated threat actors.
- Leverage AI-driven insights: Use Bitsight AI to turn raw, fragmented data into clear, source-backed summaries and actionable next steps.
- Map behavior to frameworks: Anchor investigations to the MITRE ATT&CK framework and view Malpedia-backed context to understand specific adversary techniques and patterns.
- Assess ransomware exposure: Access victim incident details, attack timelines, and leak site screenshots to understand a group's targeting patterns before they hit your network.
Diving into Adversary Intelligence
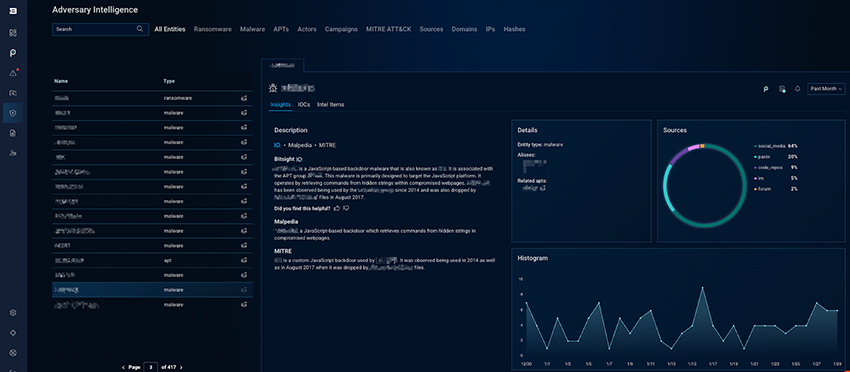
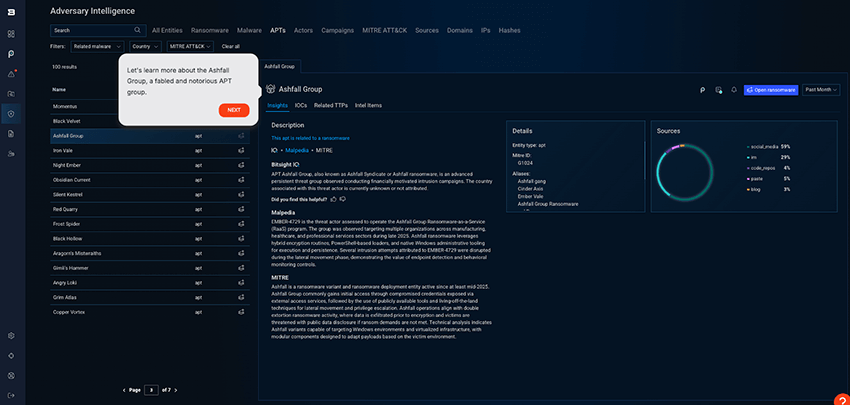
Adversary Intelligence allows threat hunters and analysts to deep-dive into a comprehensive range of adversary entities, including Ransomware, Malware, APTs, Actors, Campaigns, MITRE ATT&CK (TTPs), Sources, Domains, IPs, and Hashes.
Designed as a comprehensive investigation module within the Bitsight Cyber Threat Intelligence solution, Adversary Intelligence compiles threat information and links it to relevant actors, malware, campaigns, and infrastructure. Analysts can filter by time, sector, and geography to quickly understand targeting trends, see activity histograms, review supporting sources, and extract IOCs and aliases for detection and response.
Each threat entity is bolstered with a GenAI summary via Bitsight AI and also pulls data from Malpedia and MITRE. It also shows key details, such as aliases, sources, sectors and locations of threat actor activity, and histograms.
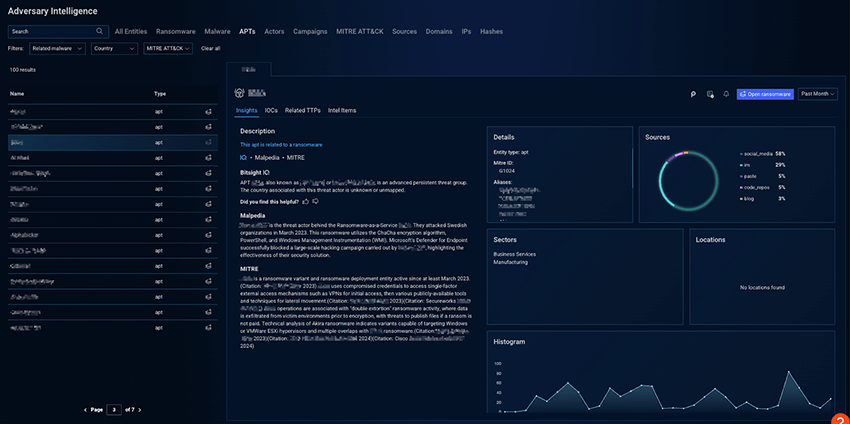
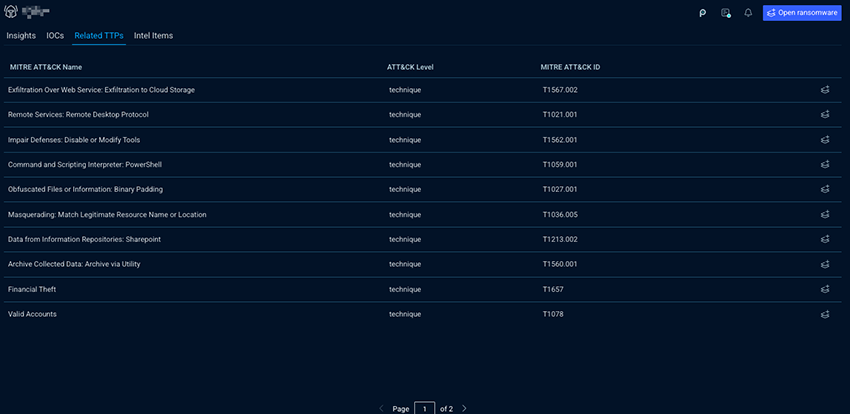
For deeper technical analysis, the module reveals specific MITRE ATT&CK techniques and sub-techniques observed for a given adversary. This allows teams to quickly understand how an adversary operates, enabling them to better anticipate future threats.
Why context matters
Fragmented data is a liability. It leads to wild goose chases, increased dwell time, and misaligned defenses. Adversary Intelligence doesn't just give you more data; it gives you a complete story. It turns isolated signals into a clear picture of intent, capability, and risk.
Actions have consequences. When your security team’s actions are driven by guesswork, the consequence is increased risk and exposure. But when those actions are grounded in adversary context, the consequence is a faster, smarter, and more resilient defense posture.
Want to see the full picture behind adversaries?
Adversary Intelligence gives your security team the centralized, source-backed context to move beyond surface-level indicators and reveal the adversaries’ objectives, patterns, and likely next steps. By transforming fragmented data into a living model of actor behavior, you can shift from reactive guesswork to an informed, proactive defense, ensuring your team can prioritize with confidence and make faster, smarter decisions before a threat escalates.