Request your free custom report and see how you can start reducing your cyber risk exposure across your digital ecosystem: cloud assets across all geos & subsidiaries; discover shadow IT; security risk findings; and more!
The Latest Cybersecurity Trends in State Government Entities
Tags:

It should come as no surprise that the cybersecurity landscape has been changing dramatically throughout the year 2020. According to Bitsight research, up to 85% of the workforce in some industries has shifted to remote work in response to the COVID-19 pandemic — introducing corporate devices to a variety of new and evolving cyber threats. While malicious actors are taking advantage of this opportunity to advance their nefarious objectives, security teams are racing to adapt to our “new normal” operating environment so that they can continue to effectively mitigate risk across their growing attack surfaces.
This new cybersecurity climate offers a variety of challenges for private enterprises, but perhaps even more so for government entities — which may lag behind their private sector counterparts in certain areas that optimize remote work, such as cloud adoption. At the same time, these agencies are facing new regulations, such as the California Consumer Privacy Act (CCPA) and the New York State Department of Financial Services (NYDFS) Cybersecurity Regulation, which place new requirements on state CIOs and CISOs to manage their own security performance and develop an effective third-party risk management program. To make matters more complex, public security incidents continue to be on the rise. In fact, over 70 state and local governments across the United States suffered from ransomware attacks last year.
Now, more than ever, state CIOs and CISOs are facing increased pressure to demonstrate that they have the right risk management program in place. In an effort to understand the latest state government cybersecurity trends, we dove into our Bitsight Security Ratings data — analyzing the largest areas of improvement, the top risk vectors of concern, and more.
Breaking down the average state security ratings
Bitsight Security Ratings are calculated using externally observable data on compromised systems, security diligence, user behavior, and public disclosures. These four data categories are comprised of various risk vectors, including everything from botnet infections and exposed credentials to open ports and patching cadence.
In the Bitsight platform, each of the 50 United States has its own rating that provides an independent and objective measurement of its security posture. As of August 2020, the average Bitsight Security Rating for the 50 states as a whole was 530. And if you imagine, for a moment, that the 50 states represent an entire industry, this rating is considerably lower than that of its private sector peers.
Here’s a breakdown of the average Bitsight Security Ratings for a sample of private industries during this same time period:
- Finance: 720
- Legal: 710
- Healthcare/Wellness: 700
- Technology: 690
Of course, not all states are created equal when it comes to their security posture. While some states have Bitsight Security Ratings in the 700 range, others have ratings in the low 400s. That being said, looking at the average rating for the 50 states portfolio as a whole empowers us to identify some key trends and challenges in the local government space.
Where have the 50 states seen the largest security posture improvement?
Let’s start with the good news: When looking at this data set for the period of February to July 2020, we found that this group improved their overall security performance in a variety of risk vectors. In the chart below, increasing a grade in a particular risk vector indicates that the states in question reduced their risk exposure in that area.
|
Risk Vector |
Percentage of States That Increased Their Grade |
Percentage of States That Decreased Their Grade |
|
Server software: This risk vector analyzes versions of commonly installed IT infrastructure software. |
46% (23 states) |
2% (1 state) |
|
Botnet infections: This risk vector observes a unified network of machines that perform actions instructed by malware creators. |
46% (23 states) |
2% (1 state) |
|
Desktop software: This risk vector analyzes any potential vulnerabilities in versions of commonly installed operating systems. |
42% (21 states) |
12% (6 states) |
|
Unsolicited communications: This risk vector looks at any host that is observed trying to contact a server on another host that is not expected or supported. |
20% (10 states) |
0% (0 states) |
What were the top risk vectors of concern?
Now that we have a basic understanding of the areas in which the 50 states have improved their security posture, let’s take a deep dive into the other end of the spectrum. When looking at this data set for the same 6-month period, we found that there were two main areas of concern: patching cadence and SSL configurations.
Both of these risk vectors fall into the diligence category — which analyzes the steps a company has taken to prevent cyber attacks. While patching cadence speaks to the speed at which a company resolves publicly disclosed vulnerabilities, the SSL configurations risk vector looks at records indicating that servers support strong encryption standards and have properly configured security protocol libraries.
Here’s a closer look at our findings (with “companies” representing states):
While installing regular updates and patches is an easy process, it’s one that can pose significant cyber risk if left undone. In fact, according to Bitsight data, failing to patch makes an organization at least 2x more likely to suffer a breach.
Without the proper encryption standards and protocols in place here, states open themselves up to a potentially damaging cyber attack.
In the end, the fact that two diligence risk vectors are the top areas of concern shouldn’t be all that surprising. With the widespread shift to remote work, it’s increasingly difficult for states to ensure they have the right systems and processes in place to prevent attacks across their extended digital ecosystems.
For instance, even when employees were previously connected to their work networks, it’s likely that many were not particularly diligent about installing updates and patches — or restarting their machines. And some agencies may have relied on employees to be connected to the government VPN in order for customized patches to be installed. Now, as a large number of employees are remote and connected to their Work From Home-Remote Office (WFH-RO) networks, it can be even more challenging for security leaders to ensure their teams are connecting to the VPN regularly and following the correct patching protocol.
How can states effectively mitigate risk in our "new normal" operating environment?
Given the current landscape, it’s never been more important for security leaders to take a risk-based, outcome-driven approach to cybersecurity.
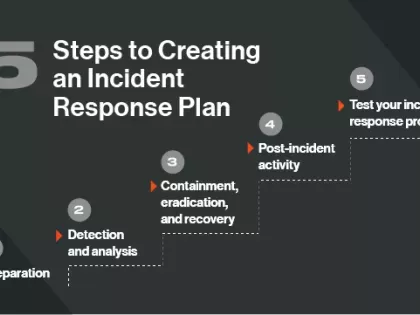
Here are five best practices states can put into place to develop a strong risk mitigation program:
1. Update your employee security training program
As this new environment opens your network up to a variety of unique risks, you should reassess and update your security training resources accordingly. Your team should be continuously reminded of the malicious methods that may use them as a vector of attack — and how to prevent themselves from falling victim to these initiatives. For instance, as identified above, ensuring that employees are following the desired patching protocol is a major pain point right now. New vulnerabilities will continue to be weaponized over the coming months, and it’s critical that you train all employees to update their software and install patches regularly.
2. Ensure all digital assets are identified and managed properly
Without clear and continuous visibility into all the assets that comprise your expanding digital ecosystem, it’s difficult to identify hidden areas of risk lurking in the shadows. With Bitsight Attack Surface Analytics, you can validate and manage your digital footprint across a complex environment involving cloud service providers, subsidiaries, and remote office environments. And, using our Work From Home-Remote Office solution, you can import WFH-RO IP addresses and monitor them for open ports, malware traffic, out-of-date OS and browser software, and more — making it easier than ever to evaluate and prioritize material findings that could pose significant risk.
3. Understand and meet rapidly changing standards of care
It’s never been more important for security and risk leaders to know the latest state government security performance standards. With Bitsight Peer Analytics, you can gain unprecedented visibility into the cyber security benchmarks that exist in your industry, sector, and peer group — based on the security performance data of hundreds of thousands of global organizations. This solution empowers you to uncover gaps in your cybersecurity program based on a comparison of risk vectors within your local government peer group — and prioritize investments for the areas that can have the greatest security performance impact.
4. Gain visibility into your security performance across subsidiaries
Each government agency has a unique structure, function, and ecosystem of digital touchpoints — and this level of complexity often makes it difficult to pinpoint where the greatest cyber risk exists across your distributed ecosystem. With Bitsight Enterprise Analytics, you can leverage real-time, meaningful, and objective data and metrics to uncover the factors within each group that most significantly impact overall security performance — such as unpatched systems, insecure access points, and existing malware infections. Armed with these insights, you can develop informed remediation plans that drive accountability throughout your state.5. Mitigate risk throughout your vendor network
In an effort to be as efficient, agile, and flexible as possible in our “new normal” operating environment, your agency is likely partnering with a variety of third parties. While these partnerships offer exciting opportunities for growth, they can also introduce unwanted vulnerabilities into your network. With Bitsight for Third-Party Risk Management, you can optimize your processes for evaluating third-party risk effectively, onboarding new vendors securely, and facilitating remediation initiatives throughout your partner network.
Interested in learning more about navigating the new security challenges? Check out our solution brief for tips on how to rethink your policies, processes, and plans to mitigate cyber risk in an increasingly remote workforce.