Get the report and see why Bitsight was named a Visionary.
The End of the Exploit Window: How Frontier AI Is Changing CVE Prioritization
Tags:


When a new vulnerability is announced, the race begins.
Security teams jump into action, checking exposure, triaging events, identifying affected systems, and figuring out how quickly they can patch. The clock is ticking and they know it.
At the same moment, threat actors are doing their own version of that work. They’re reading the same advisories, watching the same feeds, and asking a much simpler question: Who is still vulnerable?
That’s what makes Common Vulnerabilities and Exposures (CVEs) tricky. They’re designed to help defenders track and respond to known vulnerabilities, but they also act as a signal. Once a CVE becomes public, it’s no longer just a defensive tool. It’s shared knowledge, and attackers are often very good at turning that knowledge into action.
It’s easy to assume attackers have some hidden advantage, but in many cases, they don’t. They’re using many of the same sources, tools, and techniques available to everyone else. The difference is how quickly and systematically they act on what they find. While threat actors do discuss and study CVEs on the deep and dark web, many attackers learn about vulnerabilities through the same public disclosures defenders rely on. More advanced groups may identify or study vulnerabilities before they are even publicly disclosed.
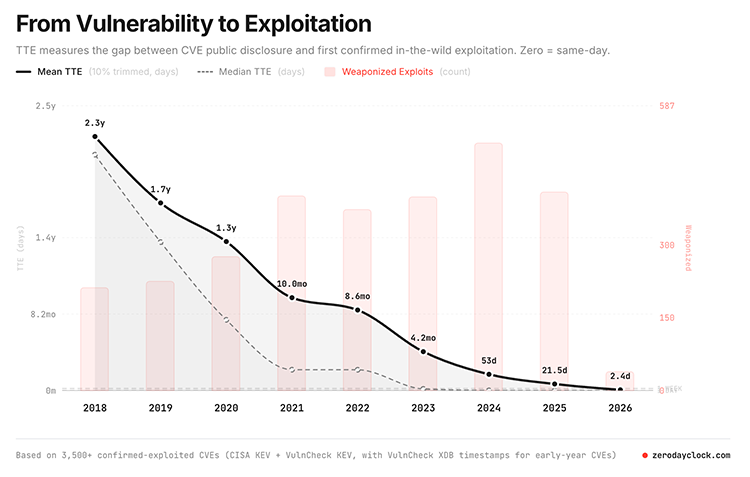
In a world still adjusting to the “Mythos Effect,” this race is no longer measured in days or weeks. Frontier AI models point to a future where vulnerability discovery, exploit development, and target identification happen faster, at greater scale, and with far less manual effort. That changes the challenge for defenders. Instead of just knowing a CVE exists, now it’s about deciding what matters first before attackers do.
Frontier AI and the shrinking time to exploit
Claude Mythos and other Frontier AI models represent a broader change in the threat landscape, which is that AI is lowering the barrier to exploitation. For defenders, the concern is three-fold: attackers can find vulnerabilities faster, test them faster, and turn them into working exploits faster. That compresses the window between exposure and breach even further.
It also raises the risk of vulnerability chaining. In many real-world attacks, a single vulnerability is not the whole story. Attackers often combine multiple weaknesses to move from initial access to deeper compromise.
For example, an attacker might start with an exposed application vulnerability, then chain it with weak authentication, excessive permissions, or a misconfigured cloud service to reach sensitive data. Individually, each issue may not look catastrophic. Together, they can create a serious attack path.
This is what makes prioritization harder in the Mythos era. Defenders are dealing with more vulnerabilities plus the additional ways those vulnerabilities can be combined, operationalized, and exploited against critical systems and third-party relationships.
This moves beyond hypothetical risk. Attackers are already experimenting with AI-enabled tactics with other tactics, techniques, and procedures (TTPs). Advanced Persistent Threat (APT) groups have reportedly used AI platforms in campaigns such as “Hexagonal Rodent” to create more targeted phishing content and support attempted intrusions. In another case, an attacker reportedly used AI-generated audio in a vishing scheme that resulted in a victim transferring $25 million. Whether AI is used for phishing, social engineering, or exploit development, the trend is the same: lower effort, higher speed, and greater scale for attackers.
This is where models like Mythos become especially important. AI-driven tools may make it easier to identify not just isolated vulnerabilities, but combinations of weaknesses that can be exploited together. That means defenders need to think beyond individual CVEs and look at exposure, asset importance, business context, and third-party dependencies.
If vulnerability volume increases dramatically, security teams will not be able to fix everything. The real challenge becomes knowing what matters most right now.
Attackers don’t wait for perfect timing
We tend to think about vulnerabilities in clean stages: discovery, disclosure, patch, resolution.
Attackers don’t think that way. They’re looking to make the most impact and get the most return on their investment, regardless of how new or shiny a CVE may be.
They step in wherever there’s an opportunity, even if that opportunity is a two decade old CVE. Sometimes that’s before a vulnerability is publicly known, but more often, it’s right after a patch is released or a CVE is published. The moment there’s enough information to understand a flaw, even partially, someone may already be looking at how to exploit it.
That’s why the gap between disclosure and exploitation can feel so short. As opposed to just getting lucky, attackers are always watching and they are motivated to exploit quickly.
How attackers prioritize CVEs from public signals
One of the most effective ways attackers identify useful vulnerabilities is also one of the simplest: they monitor public sources. That includes vendor advisories, vulnerability databases, GitHub security notices, mailing lists, and researcher blogs. None of this is hidden. It’s often the same information security teams rely on every day.
The difference is the automation.
Attackers can use systems that constantly ingest new CVEs as they’re published, tag them, and prioritize them based on potential return. If a vulnerability affects widely used software, appears easy to exploit, or applies to internet-facing systems, it can move up the list quickly, much like we saw with the 2023 MoveIt breach perpetrated by Cl0p that impacted 2,700 organizations and 91 million individuals. This breach continued for months beginning, during which new victims were continuously added to Cl0p’s Data Leak Site (DLS) on the dark web, even after the breach was widely reported. In this case, researchers believe Cl0p may have identified or studied the vulnerability well before its public disclosure, giving the group a significant head start before widespread exploitation began.
Patches reveal more than you think
When a vendor releases a patch, it fixes the problem but it can also reveal clues about the vulnerability. By comparing the patched version of software with the previous version, attackers can see what changed. This process, often called patch diffing, helps them narrow in on the part of the code that was vulnerable. From there, they may be able to reconstruct what the issue was and how it could be triggered.
This is one reason exploitation can happen quickly after a patch is released. The fix protects customers who apply it, but it can also give attackers a roadmap for understanding the flaw. For organizations that delay patching, that creates a risky window where the vulnerability is both known and still exploitable.
In a compressed exploit cycle, even a short delay can matter.
Finding targets is a matter of scale
Once attackers understand a vulnerability, the next step is finding where it exists by scanning the internet. Using tools that can probe large portions of the internet quickly, attackers look for exposed systems, open ports, and identifiable software versions. If a vulnerability affects a specific product or version, they may be able to find potential targets in a short amount of time.
At that point, it’s about finding the easiest opportunities. A forgotten server, an unpatched appliance, or an exposed service can become an entry point simply because it is visible.
And in a modern enterprise, those entry points may exist well beyond your own environment, including across subsidiaries, cloud infrastructure, and third-party vendors.
Some actors go looking for vulnerabilities themselves
While many attackers rely on public disclosures, more advanced groups take a different approach: they actively search for vulnerabilities before they are announced. This can involve reverse engineering software, analyzing how applications behave under unusual conditions, or digging through code to find subtle flaws. It’s slower and more technical work, but it can lead to valuable discoveries, especially vulnerabilities that no one else knows about yet.
Fuzzing is a common technique leveraged by threat actors. By feeding software large amounts of unexpected or malformed input, researchers and attackers can trigger crashes or strange behavior. Those crashes can point to deeper issues, some of which may be exploitable.
Signals are everywhere
Not all vulnerability clues come from official CVEs. In many cases, attackers just need a starting point as opposed to the full details.
Threat actors watch what’s happening around them via open-source projects, developer conversations, and the broader security community. Something as trivial as a small change in a GitHub commit, a vague note about “improving input validation,” or even a conference talk hinting at new research can provide enough of a lead to start investigating.
There’s also a market for vulnerabilities.
Some vulnerabilities are acquired as opposed to discovered. There are markets where exploits are bought and sold, shared within closed groups, or brokered privately through Initial Access Brokers (IAB). This is especially true for high-impact vulnerabilities affecting widely used systems.
While not every attacker participates in this ecosystem, it plays a role in how quickly certain exploits appear and spread.
Why it feels like attackers are always ahead
From the outside, it can feel like attackers are moving impossibly fast. In reality, they benefit from a few simple advantages:
- They automate aggressively,
- They focus on what is exploitable,
- And they don’t have to worry about testing patches, avoiding downtime, or coordinating across business units.
Defenders, on the other hand, have to do all of those things. That difference creates a gap, and attackers are very good at operating inside of it. Frontier AI threatens to widen that gap even further by making exploit discovery and development more scalable, more repeatable, and more accessible.
What CVE prioritization means for defenders
Not every CVE represents the same level of risk. Some vulnerabilities may be difficult to exploit, affect systems that are not exposed, and require very specific conditions. On the flip side, some are easy to exploit, widely exposed, and actively discussed or targeted by attackers.
Those are the ones that matter most. The challenge is figuring out which is which. It’s no longer enough to track CVEs based on severity alone. Security teams need context, asking questions like:
- Is the system exposed to the internet?
- Is there exploit code available?
- Are attackers actively discussing or using this vulnerability?
- Does it affect critical assets or key vendors?
Without that context, it’s easy to waste time on theoretical risks while missing the ones that are most likely to become real incidents.
In other words, the challenge goes beyond vulnerability management. Now it’s about cyber risk prioritization under compressed timelines.
Where Bitsight helps
This is where Bitsight helps shift the focus from simply tracking vulnerabilities to understanding real-world risk.
- Bitsight Vulnerability Intelligence, including Dynamic Vulnerability Exploit (DVE) Scores, helps prioritize CVEs based on their likelihood of exploitation. By combining vulnerability intelligence with real-world threat signals, teams can focus on the exposures most likely to become active threats.
- Bitsight Security Posture Management (SPM) helps organizations connect exposure and threat context to a broader understanding of cyber resilience. That means not only identifying what is most urgent to fix, but also measuring whether remediation and security investments are actually reducing risk over time.
- Bitsight Third-Party Risk Management (TPRM) extends that visibility across vendors and partners, helping organizations understand where newly disclosed or actively targeted vulnerabilities may introduce external risk. Bitsight’s Dark Web Intelligence for Supply Chains adds another layer by surfacing threat activity, breach signals, and emerging risk across the third-party ecosystem.
While attackers are watching for exposed vulnerabilities, Bitsight helps defenders understand where those risks are most likely to become real-world threats.
The bottom line
Threat actors don’t rely on a single technique to find vulnerabilities. They monitor disclosures, analyze patches, scan the internet, follow researchers, and automate as much of the process as possible. Most of what they use is already public. The difference comes down to speed, focus, and prioritization.
For defenders, the goal goes beyond just knowing that a CVE exists to instead understanding whether it matters: whether it is likely to be exploited, whether it is exposed, and whether it is relevant to your organization or your third parties.
In the Mythos era, defenders cannot manage exploit risk with severity scores alone. The organizations that adapt fastest will be the ones that combine threat intelligence, exposure context, and business impact to decide what matters before attackers do.