Get the report and see why Bitsight was named a Visionary.
The Mythos Effect and the End of “Business as Usual” for Security Operations and Risk Management
Tags:


Something fundamentally shifted in cybersecurity.
Claude Mythos, Anthropic’s frontier AI model, signaled the arrival of what the Cloud Security Alliance called an “AI vulnerability storm,” a world where vulnerabilities are discovered and exploited at machine speed.
This is a compression event, collapsing timelines, expanding attack surfaces, and forcing a rewrite of how organizations think about security operations, software development, risk, and ultimately, business survival.
“The Mythos Effect” is a new Bitsight blog series exploring the impact of agentic models like Anthropic’s Mythos on enterprise security and risk programs. We’ll examine a variety of topics such as the collapsed time between vulnerability identification and exploitation, what happens when the volume of exposure overwhelms your system to prioritize them, and the expanding attack surface that is growing beyond the limits of your network perimeter.
We will also explore the other side of the equation, unpacking the dynamic world of threat actors and the opportunities these new tools present for their operations. Finally, we will step back to understand the strategic implications: exposure, risk, resilience, and a new mandate for those charged with managing it all. In the end, our goal is to provide both insight and best practices to leaders searching for answers to difficult questions.
What is Mythos?
Mythos is Anthropic’s upcoming Frontier AI model. In addition to other advances in capability, it has been found to be incredible at discovering software vulnerabilities and, critically, developing exploits for them.
That pairing matters.
Historically, vulnerability discovery and exploitation were separated by time, expertise, and effort. Mythos collapses that gap. In many cases, discovery and exploitation now occur almost simultaneously, eliminating the traditional “window of safety” defenders relied on. It democratizes cyber crime, making the sophistication needed to find and exploit a vulnerability very low.
A junior attacker with little technical background no longer needs to understand exploit chains, reverse engineer patches, or write custom malware. With AI, a “script kiddie” can simply ask a model to identify vulnerable internet-facing systems, generate working exploit code, tailor phishing lures to a target organization, and automate lateral movement once access is gained. An attacker who once relied on copying fragments from forums can now orchestrate sophisticated campaigns through natural language prompts and autonomous agents.
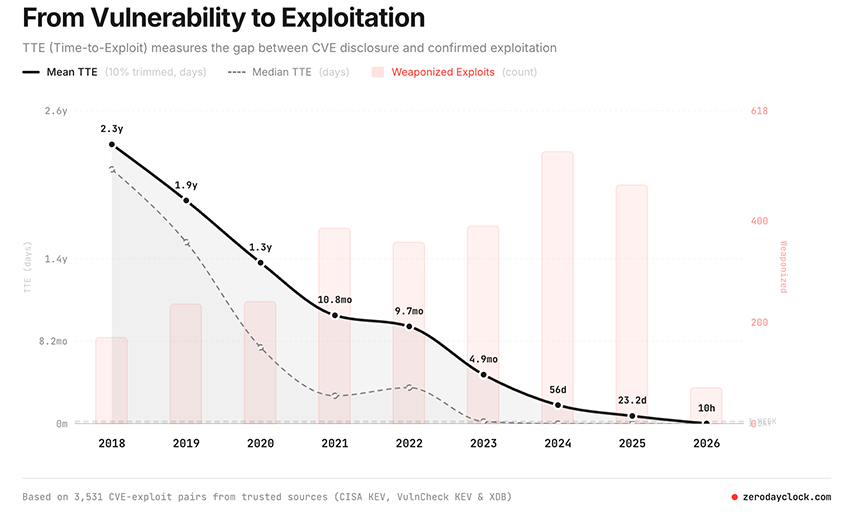
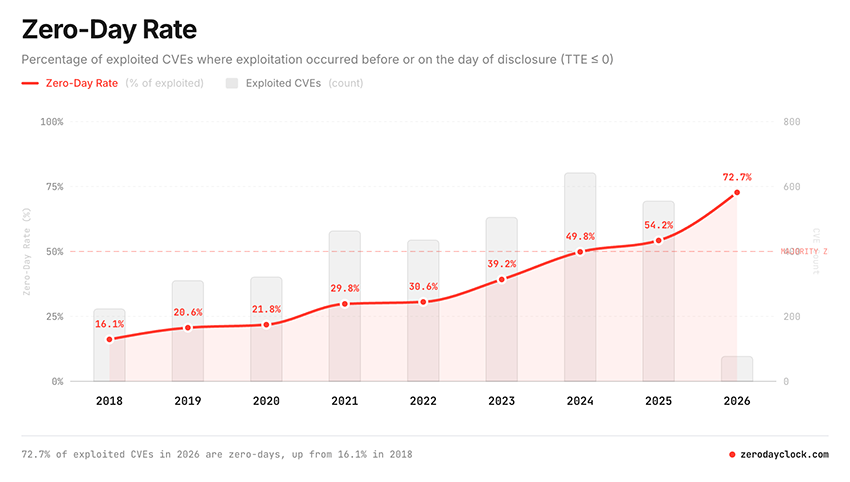
The result is a step-change in velocity and frequency of attacks. What once took months can now happen in hours or minutes. What once was manageable by teams of people leveraging tools becomes orders of magnitude larger, forcing a ‘machine vs machine’ arms race. Resources like the Zero-day Clock are already showing the troubling trends for time to exploit and zero-day rate as AI takes root, and this is before models like Mythos are even available.
The CSA frames Mythos not as a tool, but as a forcing function: AI-driven vulnerability discovery is accelerating faster than defenders can operationalize their response.
Implications and impact: The collapse of security timelines
The most immediate impact of the Mythos Effect is the destruction of time as a defensive buffer.
- Vulnerabilities will be discovered at scale
- Exploits will follow immediately
- Attack campaigns will overlap and multiply
The traditional vulnerability management lifecycle breaks under this pressure. Patch cycles, prioritization queues, and remediation SLAs were all designed for a slower world.
That world is gone.
Security teams are now being asked to move at “machine speed,” a pace current operating models were never built to support. And it is not just their environment that they need to be concerned about, it’s the ever-expanding network of vendors and partners they rely on to operate the business.
The vulnerability tidal wave
A second visible symptom of the Mythos Effect is the vulnerability tidal wave. A looming influx of alerts across software, infrastructure, and third-party vendors unlike anything security teams have faced before. Backlogs swell into inventories as new exposures arrive faster than existing ones can be investigated. The idea of a manageable “prioritized queue” begins to collapse under its own weight. When everything is labeled critical, critical loses meaning.
The downstream effects ripple across the entire security stack. SIEM platforms flood analysts with escalating volumes of detections, correlations, and threat indicators, many tied to emerging exploits and overlapping attack campaigns. Alert fatigue intensifies as teams struggle to separate signal from noise. Over time, organizations stop reducing risk and begin quietly stockpiling it, creating a dangerous erosion of operational confidence and trust in the systems designed to protect them.
The infinite attack surface
Mythos and other models accelerate a trend that was already underway: the effective disappearance of boundaries. Modern enterprises operate across:
- Cloud environments
- Third-party ecosystems
- Open-source dependencies
- Hybrid infrastructure
AI helps to chain this interconnected landscape effortlessly, identifying vulnerabilities across the supply chain. Third, fourth, and nth party risk *IS* the new perimeter. Operators become charged with not only securing the house, but securing the neighborhood.
The result is an effectively unbounded attack surface, forcing security leaders to not only gain visibility, but to enforce control on environments that live outside of their authority. Moving toward comprehensive, continuous visibility across that extended digital ecosystem, including suppliers and partners, is now just table stakes. The new question is not whether you can see it, but what are you doing about it?
The shift left
‘Shifting left’ will become an essential part of adapting to the Mythos Effect. Mature software organizations will increasingly use AI throughout the software development lifecycle to identify vulnerabilities earlier, improve code before release, and produce more resilient products over time. But that protection will be unevenly distributed. Not every company will modernize at the same pace, and vast amounts of legacy software, unsupported infrastructure, and open-source dependencies will remain exposed for years to come.
But even as some organizations improve their internal development practices, attackers will continue to find opportunities across unmanaged external dependencies, poorly secured vendors, and aging software that still underpin the modern enterprise.
The change we seek: Business context is critical
Not all risk is created equal. In a world flooded with vulnerabilities, collapsing exploit timeliness, and an infinite attack service, context is king.
- Which systems support critical business functions?
- Which exposures create real operational risk?
- Which vulnerabilities are actively being exploited?
Without this context, organizations drown in noise. They generate findings but lack the ability to connect those findings to business impact. The Mythos Effect amplifies this problem. When vulnerability discovery scales exponentially, prioritization becomes the central challenge. It’s unsolvable unless there is some context for what those vulnerabilities mean to business operations.
From protection to resilience
What then emerges is a shift from focusing on protecting the organization to a higher calling. When vulnerabilities are discovered and exploited at machine speed, then breaches are no longer edge cases, they are inevitable.
The focus must shift from protection to resilience:
- How proactive is your approach to discovering vulnerabilities across an interconnected attack surface?
- How effective are you at prioritizing exposure in systems that would disrupt business operations?
- How impactful are your investments and controls in reducing risk?
This will require a new standard of readiness being dubbed “minimum viable resilience,” measured by factors like cost of exploitation and containment effectiveness. Success to be defined by withstanding a barrage of threats and sustaining business operations.
The overnight operationalization of risk management
The role of the company ‘Risk’ manager just got much more interesting. Mythos signals the end of the stodgy, slow, and antiquated risk management process. Future risk management will be real-time with active and dynamic governance that is informed by the evolving threat.
This means operationalizing risk management across the organization:
- Integrating threat intelligence into risk management
- Bringing third-party risk signals into the SOC
- Correlating external exposure data with internal telemetry
- Continuously validating risk assumptions
The fundamentals of risk management, segmentation, identity controls, defense-in-depth still matter, but they must be applied continuously and at scale.
The end of the beginning?
If Mythos marks the end of business as usual, it also marks the beginning of something far more consequential. In the next parts of this series, we’ll move beyond the initial shockwave and into the second-order effects: what happens when prioritization collapses under “everything is critical,” how defenders navigate a world where automation is not an advantage but a requirement, and how threat actors evolve when the same tools are placed in their hands.
We’ll explore the emerging architectures, operating models, and leadership decisions that will define who wins and who loses. Buckle in, it’s going to be a wild ride!