Why IT Vendor Risk Management Is So Difficult
While your organization works to mitigate many types of risk, the risks posed by IT vendors may be among the most difficult to manage. Cybersecurity threats have the potential to be incredibly damaging, affecting your company’s reputation, operations, financial performance, and competitiveness. While your own security programs may be highly effective, your vendors may not exercise the same diligence, creating a weak link in your security armor. In fact, studies suggest that nearly 75% of companies that were breached reported the attacker accessed their network through a vendor, partner, or another third-party.
The challenge of IT vendor risk management is complicated by continual growth in third-party ecosystems and in the nature of monitoring vendor risk. New, more sophisticated cyber threats seem to emerge weekly or even daily. In this environment, manual tools for managing vendor risk like annual self-assessments can’t provide daily insight into whether a vendor’s security controls are working effectively.
Bitsight can help. As the leader in the security ratings industry, Bitsight provides solutions for continuously monitoring the security posture of third-party organizations and tracking security performance of vendors in real-time.
Automating IT Vendor Risk Management
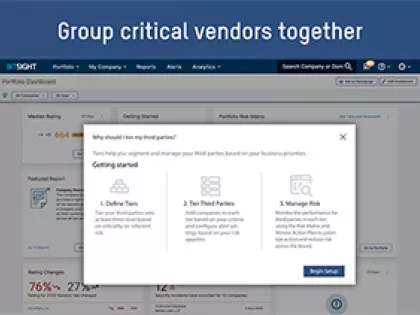
As you consider the best way to mitigate risk in your portfolio of IT vendors, leveraging technology-enabled automation is the best way to keep up with your ever-growing vendor base and the speed at which cyber threats emerge.
Automated technologies provide three critical benefits for risk reduction
1. Greater velocity
Traditional vendor risk management assessments have long turnaround times, prohibiting companies from gaining a quick and comprehensive view of a vendor’s security posture. Automated IT vendor risk management solutions enable quicker assessments and greater productivity when managing hundreds or thousands of vendors, and when deciding between multiple vendors in the procurement process. When new threats and vulnerabilities emerge, automated solutions can instantly determine the impact on security posture of third and fourth parties, and notify security teams before the vendor’s themselves have addressed it.
2. Simple scalability
With constant innovation in new technologies and the rise of cloud services, the number of vendors in the average third-party ecosystem continues to grow. Most organizations lack the people, time, and resources to adequately conduct due diligence on all third-party vendors. Automated security diligence technology enables risk management teams to streamline cybersecurity assessments and processes with the headcount and resources they already have.
3. Easier collaboration
Working with third parties to address cybersecurity risk is one of the most difficult aspects of IT vendor risk management. Automated risk management solutions provide a common platform where companies and their vendors can review the same data in one shared view to provide clarity around security issues and cyber threat intelligence decisions.
Related Blog: What is Vendor Risk Management (VRM)?