Explore why Forrester recognized Bitsight as a Leader in its 2026 evaluation and how Bitsight delivers the intelligence needed to support stronger cyber risk decisions.
How to Use the MITRE ATT&CK Framework as a Shared Language for SOC, CTI, GRC, and Leadership
Tags:


Picture the first meeting after a serious security event.
The Security Operations team is talking about alerts, detections, and lateral movement. Threat Intelligence is talking about adversary tradecraft and known campaigns. Governance and Risk is talking about control gaps, exposure, and business risk. And leadership? They only care about how bad this event is, and what the team is doing about it.
Security teams often agree on the mission: deter and stop threat actors at all costs. But sometimes, language itself becomes a barrier.
While every organization is different, the following tenets usually apply in some shape or another: SOC focuses on detection and response, CTI tracks adversary behavior and emerging threats, and GRC aligns controls, risk, and compliance requirements with business priorities. Each function sees a different part of the security picture, and each tends to describe that picture in its own terms. Together, they form a powerful security alliance, but it’s easy for teams to get stuck in their own priorities and their own “language.”
The result? Friction. It becomes harder to connect threat intelligence to monitoring priorities, harder to translate operational findings into risk language, and harder to give leadership a clear view of what matters most, which ultimately undermines decision-making.
This is where the MITRE ATT&CK Framework comes in. It gives SOC, CTI, and GRC teams a universally understood language for describing adversary behavior, defensive coverage, and security gaps. Just as importantly, it’s a framework leadership increasingly recognizes and trusts. That makes MITRE more than a technical reference. It becomes common ground across the organization, where TTPs can be discussed, mapped, and understood in a consistent way.
Why MITRE resonates across functions
MITRE is widely used because it’s practical. It does not force every team into the same workflow, but it gives them a consistent vocabulary.
SOC
For the SOC, MITRE helps map detections and investigations to known adversary techniques. Whether analysts are seeing timestomping, brute-force attempts, credential access activity, or lateral movement, MITRE adds structure to what they are observing. It makes it easier to understand what those behaviors represent, measure coverage against known techniques, and identify where visibility is strong and where it is weak.
CTI
For CTI, MITRE provides a way to translate threat reporting into concrete behaviors. Instead of speaking only in terms of actor names or campaign narratives, intelligence teams can describe the techniques that matter operationally. That gives CTI a clearer way to inform the SOC about what to watch for, while also helping analysts connect observed TTPs to broader threat activity when the intelligence supports it.
GRC
For GRC, MITRE offers a way to connect technical activity to risk discussions. It helps frame control effectiveness around real-world attacker behavior, which is often more meaningful than abstract control statements alone. If phishing is a recurring tactic in campaigns targeting your industry, or if account takeover techniques are being used against key vendors and third parties, MITRE helps translate those patterns into risk-informed conversations about control gaps, resilience, and business exposure.
The value is not that every team uses MITRE in the same way. The value is that they can all use it to speak a common language.
A translation layer between technical and business conversations
One of the biggest challenges in security is translation.
Technical teams often communicate in terms of alerts, telemetry, tools, and incidents. Leadership, on the other hand, wants to understand exposure, resilience, business impact, and whether the organization’s security posture is improving over time.
MITRE helps bridge that gap.
When security teams use MITRE to describe coverage, validate controls, or explain adversary behavior, they are grounding their message in a framework that is structured, repeatable, and broadly understood. That makes conversations easier at every level of the organization.
A SOC leader can explain that detection engineering is not just producing more alerts, but expanding coverage against specific adversary techniques known to target the organization’s industry. A CTI leader can show how intelligence is shaping priorities by highlighting the techniques most relevant to the organization’s threat landscape. A GRC leader can frame gaps not simply as control deficiencies, but as areas where known attacker behaviors are less effectively mitigated.
For executives, that creates a much clearer story. MITRE makes it easier to answer familiar leadership questions:
- Where are we most exposed?
- What are we prioritizing and why?
- How does today’s threat landscape connect to our security investments?
- Are we improving in measurable ways?
Why leadership responds to MITRE
Leadership does not need every technical detail. What they need is a credible, understandable model that connects security activity to business risk.
MITRE helps because it is recognizable, structured, and grounded in adversary behavior. It gives leaders confidence that teams are not speaking in isolated, tool-specific language or making purely subjective judgments. Instead, they are aligning around a model that is widely adopted and easy to communicate.
That matters in board updates, risk reviews, investment discussions, and cross-functional planning. A framework like MITRE creates consistency. It helps leadership compare priorities across teams and understand why one gap matters more than another.
In other words, MITRE is popular with leadership for the same reason it is useful to practitioners: it turns complexity into something more navigable.
What common ground actually looks like
Here’s a flow that MITRE alignment could enable:
- CTI identifies the techniques most associated with relevant adversaries
- The SOC then measures detection and response coverage against those techniques
- GRC assesses whether controls and assurance activities address the same areas
- And leadership sees a unified picture of threat-informed priorities and gaps
With MITRE, teams stop operating as parallel functions and start reinforcing one another.
Threat intelligence becomes more actionable. Security operations become easier to prioritize. GRC becomes more connected to real attacker behavior. Leadership gets a more coherent understanding of security posture.
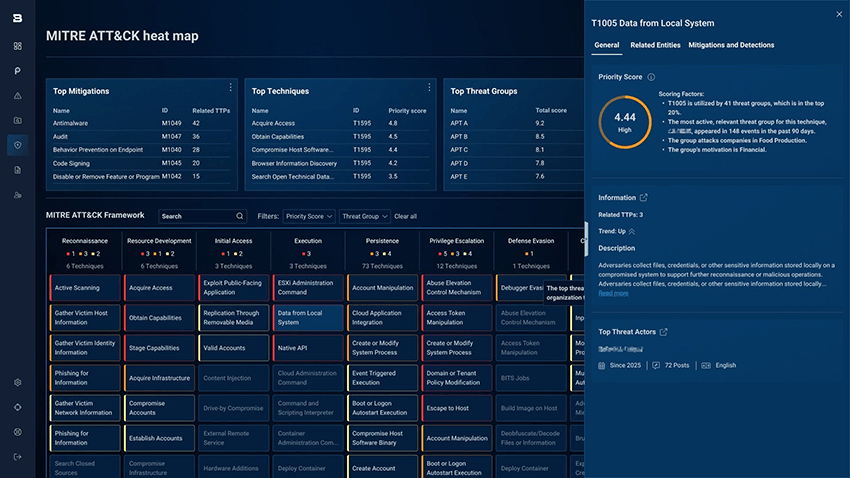
Why current threat actor TTPs make the heat map more valuable
On its own, a heat map can show where visibility and detection coverage are strong and where gaps remain. But MITRE becomes even more valuable when organizations apply that framework in a way that reflects their own threat landscape.
From a CTI perspective, the value is not just in knowing who the threat actors are: it’s in understanding the TTPs they are currently using, how those behaviors are evolving, and which techniques are most relevant to the organization’s industry, region, or third-party ecosystem.
That context can feed directly into the SOC. If intelligence shows that a financially motivated group is leaning more heavily on phishing for initial access, valid accounts for persistence, or remote services for lateral movement, then the SOC can use that information to validate whether those techniques are covered, tune detections where needed, and prioritize gaps that matter most. Instead of treating the ATT&CK heat map as a static coverage exercise, teams can use it as a living view of defensive readiness against current adversary behavior.
This is where the relationship between CTI and SOC becomes especially valuable, and where GRC and leadership gain clearer visibility as well. CTI helps identify which techniques deserve immediate attention based on the current threat landscape, while the SOC operationalizes that intelligence through detections, monitoring, and response. GRC can use the same intelligence to assess whether controls and risk management efforts are aligned to the attacker behaviors most relevant to the business.
In that way, the heat map becomes more than a visualization of ATT&CK coverage. It becomes a practical way to align intelligence, operations, and risk so defenders can focus not just on what is possible, but on what is most likely.
How Bitsight can help
MITRE is most valuable when it moves beyond theory and into practice. Bitsight helps organizations operationalize that shared language by connecting threat intelligence, adversary intelligence, and external risk into a more actionable view.
MITRE ATT&CK heat map
A MITRE heat map gives teams a clear visual representation of adversary techniques and defensive coverage. Instead of looking at threats and controls in isolation, security teams can see where visibility is strong, where gaps exist, and where attention should be focused next. That helps SOC, CTI, and GRC teams align around the same picture of risk.
Threat actor and adversary tracking with prioritization
Not every threat actor matters equally to every organization. Bitsight helps teams track relevant threat actors and adversary activity with prioritization built in, so analysts can focus on the actors most likely to impact their business, industry, or third-party ecosystem. That gives CTI teams a stronger way to guide SOC priorities and helps leadership understand why certain threats deserve more attention than others.
On-demand threat actor profiles
Security teams need fast access to context. On-demand threat actor profiles make it easier to understand who an adversary is, how they operate, which TTPs they are associated with, and what that activity may mean for your organization. This helps CTI teams quickly translate intelligence into something operational teams and stakeholders can act on.
IOC tracking
Indicators of compromise remain an important part of day-to-day defensive operations. Bitsight helps teams track relevant IOCs so they can connect intelligence to monitoring, investigations, and response activities more efficiently. That gives the SOC another way to operationalize current threat intelligence and strengthen day-to-day readiness.
Dark web intelligence for third-party risk
Third-party risk does not stop at questionnaires and compliance reviews. Bitsight helps organizations monitor dark web intelligence related to vendors and partners, providing additional visibility into where third parties may be introducing exposure. That helps security and risk teams understand where vendor-related threats may be emerging and where external dependencies could increase organizational risk.
To learn more about how your organization can start using the MITRE ATT&CK Framework as a common language between SOC, CTI, GRC, and leadership, talk to our team.