Stealer malware is thriving—especially Lumma and Risepro. These logs fuel ransomware, MFA bypass, and persistent access. It's $10 to compromise an account. Explore this and other insights the data reveals.
How to Prevent Cyber Data Leaks
It’s every security manager's worst nightmare. A member of the IT department reaches to alert that malicious software has been detected on an internal network, and the hacker potentially has access to layers of sensitive data. In the following days and weeks of remediation, locating an access point, and reinforcing cybersecurity measures, security managers often ask themselves, “could this data leak have been prevented?”
Sensitive information can leak out through any number of channels, for many different purposes, and it can then find its way into the hands of various threat actors worldwide. And just like data leakage can occur in various formats, it can affect nearly any type of company.
The good news? If your data is leaked in a way that could put your company at risk, there’s a good chance that the threat actors behind that risk will communicate in somewhat predictable ways. And, because the dark web is the go-to channel for threat actors worldwide to communicate online, monitoring its underground forums can seriously boost your ability to detect any data leakage that should concern you. As this post will explain, taking full advantage of threat intelligence from the dark web can help companies to detect data leaks promptly.
But first, let’s take a look at what data leakage is and the various forms it can take.
What is Data Leakage?
As open-ended as the term data leakage is, there are some particularly common ways it occurs:
- Phishing attacks: in which a threat actor deliberately uses impersonation to trick a victim into revealing sensitive information.
- Physical exfiltration of data: in which information is released via USB drives, printed pages, or other media (digital or otherwise).
- Insider attacks: an employee, contractor, or another individual with privileged access to a company’s sensitive information is enticed to reveal sensitive information – whether driven by greed, ideology, or simply resentment toward the company.
- Accident: in which an individual fails to take proper precautions and unwittingly leaves sensitive information exposed.
Of course, many data leaks can fit into more than one of these categories – such as in the case of an insider who deliberately exfiltrates sensitive data physically. And even within these categories, data can leak out in various ways. For example, an accident could be quite complex or as simple as leaving a printed page with sensitive information in a publicly visible location.
Still, as varied as data leaks can be, there are certain characteristics they generally have in common – most importantly, the risk they pose to the affected companies and organizations (as well as their customers).
Why is Data Leakage so Dangerous?
Some ways that a data leak could hurt a company are obvious and relatively consistent over time. Any company’s proprietary and sensitive information that is revealed – anything from company credit card numbers to trade secrets and future business plans – could hurt the company’s ability to function and profit.
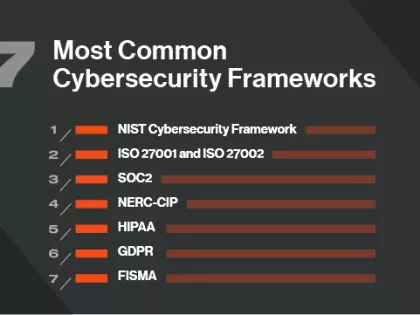
But where the last several years have really upped the ante is in terms of protecting customers’ personally identifiable information (PII). With privacy regulations like the GDPR and the CCPA dramatically increasing the penalties companies could face for failing to protect their customers’ data adequately, businesses now have a new and major financial incentive to invest in data leakage prevention and detection. Meanwhile, companies that fall victim to high-profile data leaks risk losing their customers’ confidence and business due to the bad press generated by these incidents.
Notable Data Leaks Since 2020
2020 welcomed a lot of chaos in the cybersecurity industry. With the COVID-19 pandemic disrupting the way of normal life, millions of people across the world were moved to remote work environments. Shifting company networks to allow for the remote connection by their entire workforce left organizations scrambling to protect their expanding attack surface.
Bad actors saw 2020 as full of opportunity not just because of remote workforces, but also because of the high-stakes nature of the COVID-19 pandemic. Healthcare organizations and those linked to vaccine creation were hit hard by malicious actors trying to take advantage of their thinned resources and limited time to spend on cybersecurity. And to top it off, 2020 ended with one of the most expansive, organized, and impactful data leaks in third party risk management history with the discovery of SolarWinds. Since then, there have been several prominent data breaches that demonstrate the importance of a having a mature TPRM program.
How to Protect Yourself from Data Leaks
There are important steps businesses can take to decrease the chances of suffering from data leakage. Technological solutions can make it harder for threat actors to access a company’s sensitive information, but even a single employee’s failure to follow best practices can create a significant cybersecurity risk. Proactively mitigating risk across your network is key to preventing data leaks, with a focus on four areas:
- Managing your organization’s internal security hygiene and measurement.
- Monitoring your vendors to avoid letting risks go undetected.
- Establishing solid employee cybersecurity policies.
- Find any company data that mind be on the dark web.
Maturing your cybersecurity program won’t happen overnight, but focusing on more manageable steps both internally and with external partners sets security managers on the right path towards cybersecurity management.
1) Assess your cybersecurity hygiene
Don’t overthink where to start when working to prevent data leaks in your network. First and foremost, ensuring your internal cybersecurity hygiene is well maintained will establish a solid base for decision-making and prioritizing resources. Getting full-visibility into where your business is behind the mark is possible with the right tools.
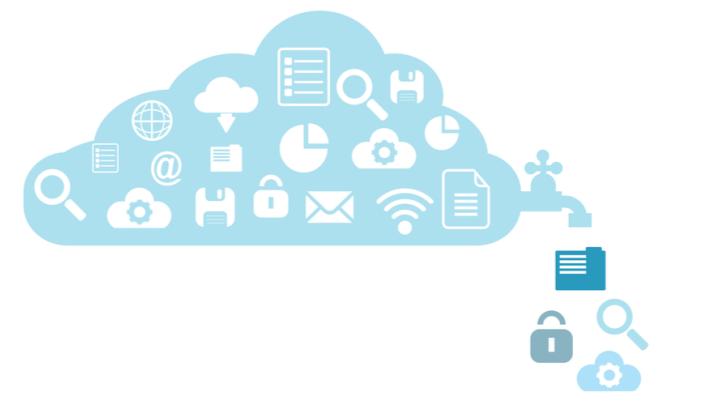
Bitsight offers Attack Surface Analytics to help security program managers get a complete picture of the risks hiding on their network and help reduce overall program risk quickly and efficiently. Attack Surface Analytics comprehensively scans your network to detect threats or vulnerable points across all lines of business and cloud service providers.
It’s also important to consider where your organization’s security hygiene falls among your competitors to give your team, and company executives investing money in your program, some context to how you’re preventing data leaks. With benchmarking technology, security leaders can compare their cybersecurity posture to others in their industry, giving context to what’s “average” or “normal” for their industry. Bitsight offers Benchmarking to Security Performance Management customers looking to gain a better understanding of what a solid cybersecurity program should look like, and to gain a more complete view of their program.
2) Monitor your third-party vendors
Some of the most impactful breaches in cybersecurity history have occurred through third-party access to a company’s network. Organizations are relying more and more on vendors to complete business operations better than they could do internally, increasing business efficiency but also adding to the access points bad actors can use to start a data leak in your network.
Continuous monitoring of your pool of vendors is a great starting point to prevent data leaks originating from your vendors. With consistent visibility into the security of third parties, vendor security managers don’t have to manually assess their vendors in a designated lifecycle, and instead only need to worry about a vendor’s cybersecurity if their monitoring software detects a data leak.
There are further steps to take to efficiently manage your vendor cybersecurity program, but starting with continuous monitoring technology is an effective first step.
3) Establishing solid employee cybersecurity policies
A final precaution you can take to actively prevent data leaks from impacting your network is to require your employees to follow best practices for protecting their own network access. Most companies now require phishing training to educate their entire workforce on detecting common phishing email techniques. Other organizations require employees to use work-provided devices that block the use of non work-related IP addresses or activity. And finally, organizations following employee cybersecurity best-practices require two-factor authentication or remote access login technology when employees log into their business’s network.
Education is an essential tool for preventing insiders from inadvertently leaking sensitive data. For instance, employees need to know how to spot a phishing email and what to do if they suspect they have received one. Ensuring your own employees are securing their network access and devices will only help to prevent data leaks to your organization’s network.
Still, we all know that even well-trained employees and other insiders sometimes make mistakes – and all the training in the world won’t help if an insider is deliberately trying to leak a company’s information. That reality makes data leakage detection especially important. The idea is to find out that some of your data have leaked as quickly as possible after the leak – especially if the initial leak could result in additional cyber threats in the future, as in the case of stolen credit card numbers that can then be used to commit theft.
4) Know what's on dark web
To really disrupt the ability of hackers and other threat actors to profit off data leakage at your company’s expense, it is important to keep in mind the role that the dark web plays in the cybercrime economy. Because many hackers and cybercriminals are motivated by their own financial interests, they often turn to the dark web not only to communicate with other threat actors but also to buy and sell leaked data and other assets.
The upshot for cybersecurity professionals? More than just a scary place where bad actors hang out online, the dark web can be a rich source of cyber threat intelligence. And being able to automatically scour threat intel with dark web monitoring tools seriously boosts a company’s ability to detect data leakage quickly.
While that kind of visibility cannot guarantee that your company will never suffer from data leakage, it can dramatically increase your chances of being alerted promptly in case a data leak does occur. And it can help you steer clear of the penalties associated with the major customer privacy laws of recent years.
Perhaps most importantly, having that kind of visibility regarding the dark web helps you zero in on the data leaks that should most concern you – those leaks that threat actors on the dark web deem worthy of their attention.
Summary
Data leaks can be detrimental to organizations, but when security leaders can break down protection into more manageable steps, it’s easier to prevent dangerous data leaks from making it to your organization.
As the attack surface expands, connecting the dots of what is putting your organization in harms’ way is not easy. With Bitsight, you can get a complete view of your exposure across on-premise, in the cloud, and throughout the supply chain to find—and remediate—your weakest links.
Bitsight combines external attack surface management with continuous monitoring, threat intelligence, and cybersecurity analytics to go beyond the traditional first vs. third party divide. This approach enables security leaders to confidently discover, prioritize, and communicate risk across their entire digital infrastructure.