Learn your risk of becoming a ransomware victim. Download our datasheet to find out what Security Rating makes you 6.4 times more likely to be a victim, and 3 ways you can take action to prevent it.
How Policymakers Can Measure Critical Infrastructure Sector Cybersecurity Performance



Policymakers are increasingly interested in measuring cybersecurity performance in critical infrastructure organizations and sectors. Measuring performance is critical for policymakers to understand current levels of risk and exposure and the effectiveness of existing policies and approaches. Armed with performance data, policymakers can answer key questions (“is our approach working?”) and make better decisions about engagement, risk reduction, and other potential solutions.
According to its new strategic plan, the U.S. Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA) plans to use performance goals to set standards and recommendations to guide security decisions regarding critical infrastructure protection. During a recent meeting, CISA Director Jen Easterly stated that “We're really going to be working hard to align our goals and objectives with specific measurements that help us reduce risk.”
What performance areas should policymakers begin measuring? Why are these important? How should they collect the data?
Performance Measurements Tied to Ransomware
Bitsight recently studied how cybersecurity performance can impact the likelihood of an organization experiencing a ransomware incident. Bitsight non-intrusively collects unique telemetry into the cybersecurity performance of organizations around the globe, and uses it to create cybersecurity analytics that measure performance over time. The Bitsight Security Rating measures an organization’s overall cybersecurity performance. Bitsight risk vectors measure an organization’s performance in particular cybersecurity domains (e.g. patching cadence, software updating practices, etc.).
After comparing the security performance data of thousands of organizations that experienced ransomware incidents against those that did not, Bitsight found several analytics to be strongly correlated with ransomware incidents, including Patching Cadence, TLS/SSL Certificates, and TLS/SSL Configurations.
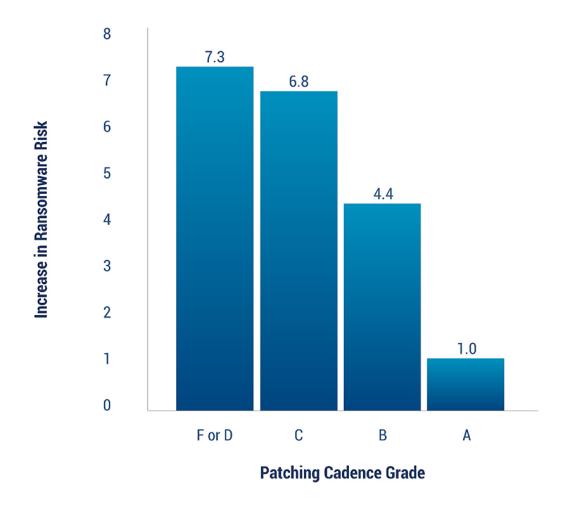
1. Patching Cadence
Bitsight’s Patching Cadence risk vector measures how many systems within an organization’s network are affected by important vulnerabilities, and how quickly the organization remediates them. Bitsight finds that organizations with an F or D grade on the Patching Cadence risk vector are more than 7 times more likely to experience a ransomware incident relative to A-grade organizations. Patching Cadence is so important that earning even a B means an organization is still over 4 times as likely to fall victim to ransomware.
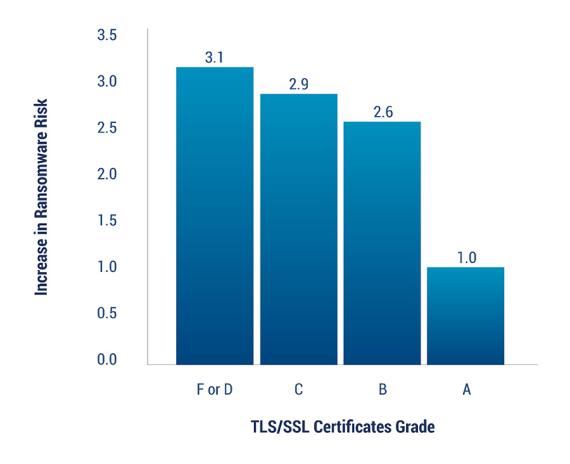
2. TLS/SSL Certificates
Bitsight’s TLS/SSL Certificates risk vector measures whether a company has properly obtained and deployed TLS/SSL encryption certificates that are used to secure communication over the Internet. Bitsight finds that organizations earning less than an A in this risk vector are approximately 3 times as likely to experience a ransomware incident.
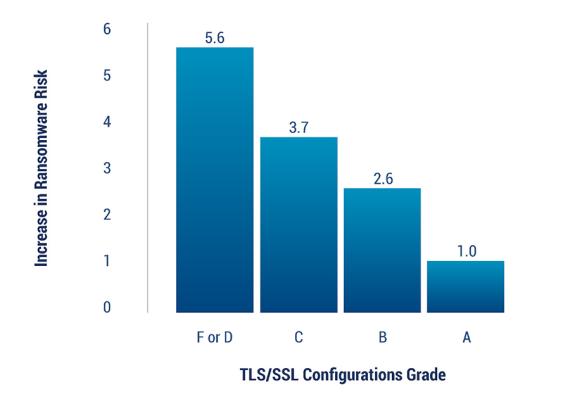
3. TLS/SSL Configurations
Bitsight’s TLS/SSL Configurations risk vector measures whether a company has correctly configured security encryption software, and whether that software utilizes strong encryption protocols when making encrypted connections to other machines. Bitsight finds that organizations earning an F or D grade on TLS/SSL Configurations leaves an organization nearly 6 times more likely to experience a ransomware incident relative to A-grade organizations.

Which sectors are at the highest risk of ransomware?
Leveraging the ransomware likelihood analysis, Bitsight examined whether certain sectors are at higher risk of experiencing ransomware incidents based on the security performance of organizations in these key risk vectors. Employing a statistical analysis, we found the following:

Sectors with “high” ransomware risk have a generally high proportion of organizations with grades B or lower across Bitsight’s Patching Cadence, TLS/SSL Configuration, and TLS/SSL Certificates risk vectors. Therefore, these sectors have a high proportion of organizations at a heightened risk of ransomware. In general, our low, mild, moderate, and high categories refer to the proportion of organizations within a sector at an increased ransomware risk.
Low-risk sectors aren’t necessarily low risk because they aren’t targeted. In fact, some of the lowest-risk sectors are those that are targeted the most – finance, legal, and business services, for example. Bitsight believes these sectors are at lower risk because they have implemented more effective, measurable defensive programs by investing significant resources in cybersecurity protection, acquiring and retaining top IT talent, and leveraging existing research and analytics to reduce ransomware risk in a targeted way. As a result, organizations in these sectors are able to counter attack tactics and techniques with sound defensive strategies.
You can read more about Bitsight’s analysis here.
Next steps for policymakers
Policymakers are taking an important step forward by leveraging data-driven performance metrics to understand critical infrastructure sector risk and make better decisions about strategy and tactics. By incorporating measurements that are scientifically related to security outcomes like Bitsight analytics, they can make significant progress in meaningfully reducing risk to critical infrastructure. Leveraging non-intrusive data can ensure that policymakers have a solid foundation of data that can be supplemented with additional data sets over time.
If policymakers are interested in reducing the likelihood of critical infrastructure organizations experiencing a ransomware incident, they should focus on 3 risk vectors that Bitsight finds to be strongly correlated to ransomware likelihood. Policymakers should also prioritize collaboration efforts with sectors that have a higher proportion of organizations that demonstrate weaker performance in these areas. Using a data-driven approach will help all stakeholders better understand gaps and resolve issues effectively.



