Stealer malware is thriving—especially Lumma and Risepro. These logs fuel ransomware, MFA bypass, and persistent access. It's $10 to compromise an account. Explore this and other insights the data reveals.
Connected Vehicles, Accelerating Risk: Inside the Cyber Threats Facing Automotive


The automotive industry is changing faster than ever, with smarter factories, connected vehicles, digital supply chains, and software-driven everything. But as the industry accelerates into this new era, something else is racing alongside it: cyber threats.
Over the past year, Bitsight Threat Intelligence data has shown a sharp rise in ransomware activity targeting companies across the auto ecosystem. And what’s striking is how often the same names keep appearing. Whether we’re looking at infected systems, code repositories, or intelligence feeds, five malware families show up again and again: Philadelphia, Conti, Rogue, BiBi, and Briar.
Most people outside of cybersecurity have never heard of these names and they shouldn’t need to. What matters is what they represent:
- Production lines that can grind to a halt without warning
- Supplier networks that ripple with disruption when a single link is compromised
- Connected vehicles that rely on constant software integrity to operate safely
- Brand reputation and customer trust on the line with every interruption
These ransomware families aren’t just technical threats. They are reminders of how vulnerable the modern automotive industry can be when everything depends on connectivity, speed, and software.
As auto manufacturers push toward smarter systems and more automated operations, cybercriminals and the malware they rely on are evolving just as quickly. Bitsight's intelligence shows that these threats are not slowing down. In fact, they’re becoming more frequent, more disruptive, and more capable of targeting the very technologies reshaping mobility.
This blog breaks down what’s happening, why it matters, and how organizations across the automotive supply chain can strengthen resilience in the face of a rapidly changing threat landscape.
Growing attack surface in a connected auto industry
From connected vehicles to telematics systems, EV charging networks, dealership platforms, and digital supply chains, the auto attack surface has expanded dramatically. Every new digital touchpoint introduces risk.
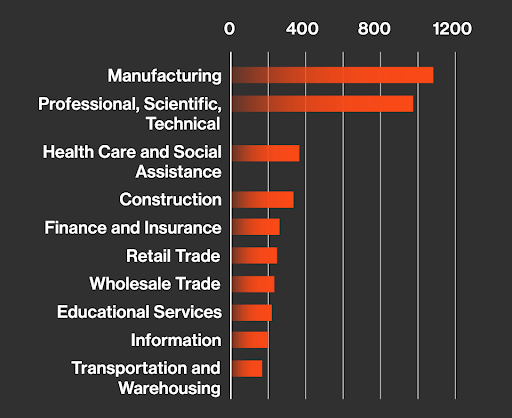
This exposure is very real. According to Bitsight threat intelligence, in 2024, 36% of all cyberattacks targeted the manufacturing sector, which includes automotive. Ransomware, data theft, business interruption, and lateral movement across interconnected operations remains a top concern.
Real-life scenarios: When minor issues become major disruptions
Let's discuss three scenarios in which cyber security incidents that may seem minor, have big costs:
Scenario 1. The dealership service department slowdown
A dealership group began noticing bizarre system behavior: slow terminals, frozen repair order software, delays in pulling OEM service bulletins.
The cause wasn’t a system outage, it was malware quietly running in the background, consuming resources and interfering with the tools technicians rely on daily.
Appointments backed up. Customers grew frustrated and complained about wait times.
No data was stolen. No ransom demand appeared.
But operations slowed to a crawl, costing the group thousands per day.
Lesson: Even low-grade malware can disrupt dealership operations and customer satisfaction.
Scenario 2. The connected vehicle that suddenly lost its connection
A major automaker pushed a routine software update to its connected vehicle fleet. Nothing unusual, just a security fix. But a small percentage of vehicles postponed the update.
Days later, security teams spotted indicators of malware scanning for vulnerable telematics modules across the Internet. It wasn’t targeting any single brand, but it didn’t have to. Any unpatched system was fair game.
Suddenly, that “routine update” felt urgent.
If malware slipped in, it could disrupt navigation services, remote start systems, or data flow back to the automaker’s cloud.
Lesson: In connected mobility, cybersecurity isn’t just an IT issue, it’s part of the customer experience and vehicle performance.
Scenario 3. The 2002 port shutdown that stopped assembly lines
In 2002, a labor dispute at several major West Coast ports led to a ten day shutdown. On paper, it was a contract negotiation issue. On the ground, it brought parts shipments for many industries to a standstill.
For automotive companies, the impact was immediate. Assembly lines that relied on just in time deliveries started running out of engines, transmissions, and electronics. Some plants cut shifts. Others paused production completely.
What happened hundreds of miles from any factory ended up halting vehicle output almost overnight.
Lesson: Even when the disruption has nothing to do with a cyber incident, the automotive ecosystem is so interconnected that a single chokepoint can stop production across an entire region.
Philadelphia malware targeting the auto industry
Philadelphia is a ransomware family known for fast encryption, credential theft, and widespread distribution. While not designed specifically for automotive systems, it frequently shows up in incidents affecting areas such as:
- Dealer back-office software
- Telematics servers
- Supplier IT environments
- Mobility applications
Philadelphia infections can interrupt services, disrupt daily operations, and expose sensitive information, even when the automotive system is not the intended target.
Delivery and infection methods
Philadelphia typically spreads through spear phishing emails, exploited public-facing applications, and abuse of common administrative tools such as Cobalt Strike, Mimikatz, Process Hacker, and LaZagne.
Bitsight intelligence tracked thousands of Philadelphia references across online platforms, indicating broad and ongoing activity.
Approximately 34% of examined incidents showed ties to this malware family, demonstrating its wide operational footprint across sectors.
Indicators of Compromise (IoCs)
The following IOCs have been associated with Philadelphia Malware:
Hashes
- 6b86b273ff34fce19d6b804eff5a3f5747ada4eaa22f1d49c01e52ddb7875b4b
- 356a192b7913b04c54574d18c28d46e6395428ab
- c4ca4238a0b923820dcc509a6f75849b
IP Addresses
- 66.155.40.24
- 50.16.218.27
- 69.16.230.165:80
Philadelphia is also known by the alias RussianRoulette, though both names refer to the same malware family.
Security measures gaining momentum
To counter rising threats, automakers are investing heavily in new cyber risk strategies and technologies:
Intrusion Detection & Prevention Systems (IDPS)
These systems have become critical layers of defense, detecting anomalies and mitigating threats before they disrupt operations or compromise sensitive data.
Vehicle Security Operations Centers (VSOC)
With connected cars generating massive data streams, VSOCs provide real-time monitoring, fleet-wide threat intelligence, and rapid incident response capabilities, strengthening cybersecurity across the entire vehicle lifecycle.
Over-the-Air (OTA) updates
OTA technology enables manufacturers to patch vulnerabilities, roll out new features, and improve safety without requiring a physical recall, an essential capability in the era of software-defined vehicles.
AI and automation across the value chain
AI-driven systems are transforming both cybersecurity and operational efficiency.
- AI-powered driver assistance enhances safety by identifying risks faster than human drivers.
- AI-based quality control reduces defects and improves reliability through real-time anomaly detection.
- AI-enhanced cybersecurity helps detect emerging threats, automate triage, and reduce response times.
Regulatory complexity and compliance pressures
As vehicles increasingly function as rolling data centers, regulatory and safety requirements continue to evolve. Automakers must address cybersecurity, privacy, and data protection standards across multiple global regions. Compliance now requires continuous monitoring and real-time visibility rather than periodic check-ins.
The need for collaboration and shared innovation
No single automaker can secure the ecosystem alone. Automotive companies, cybersecurity providers, suppliers, and public-sector stakeholders are developing shared standards, intelligence, and best practices. Collaboration is becoming an essential part of reducing systemic risk across connected mobility.
Future outlook: Building a secure digital backbone for mobility
As automotive companies adopt connected mobility, advanced analytics, tokenized assets, and digital infrastructure, a new foundation for the industry is taking shape. The future of vehicle ownership, mobility services, and automotive commerce will rely on how securely this foundation is built.
Adaptive security strategies, continuous visibility, and real-time analytics will be essential for long-term resilience.
How Bitsight can help secure the automotive ecosystem
As cyber risks expand, Bitsight provides the visibility, intelligence, and analytics needed to secure the digital and physical layers of modern automotive operations.
Malware trend and infrastructure monitoring
Bitsight identifies emerging malware trends and tracks infrastructure linked to evolving threats. This helps organizations understand where risks are growing and how they might affect connected systems.
Automotive and mobility alerts
Bitsight delivers sector-specific alerts when new vulnerabilities or relevant malware activity appears, helping organizations prioritize and respond quickly.
Indicators of compromise monitoring
Bitsight continuously tracks IOCs tied to active malware across an organization's digital footprint, enabling early detection, containment, and reduced lateral movement.
Third party risk management
Automotive organizations rely on extensive supplier networks. Bitsight provides visibility into supplier cybersecurity performance, helping teams identify risks, monitor changes, and support compliance requirements.
To learn more about securing your organization and getting insights tailored to your organization, reach out to our team.




