Making Vendor Risk Collaborative, Not Combative

Reducing cyber risk that stems from third and fourth party vendors is no easy task. It requires that organizations not only have the ability to continuously monitor and identify new risk, but also the ability to work with their vendors to fix security issues quickly. Getting to risk reduction quickly means that both organizations are communicating effectively, using data and evidence rather than conjecture to make progress.
Security Ratings are used to support these data-driven conversations, allowing organizations to inquire why their vendor’s security performance has recently changed or why a particular issue has emerged on their network. However, organizations with large supply chains may have hundreds of conversations with vendors occurring simultaneously. They cannot afford to wait several days to get a response from each vendor: the more quickly they receive responses, the more likely it is that they can make a decision in time to avoid any risk transferring over to their own organization.
Bitsight customers are increasingly enabling vendors with access to the portal — allowing them to investigate their rating and details behind it, free of charge. To date, nearly half of companies invited to the platform have increased their rating by an average of 37 points, allowing customers to get to risk reduction more quickly and drive security improvements in their business ecosystem.
This functionality has been strengthened, allowing customers customers to quickly gain insight into the vendors they’ve invited and receive greater clarity around issues they are investigating. The Vendor Access Dashboard page allows customers to see who they have invited to the Bitsight platform to answer questions such as:
- What is the status of my invitation? Has the vendor I sent access to logged into the Bitsight platform?
- What actions has my vendor taken to improve their Bitsight Security Rating and their cybersecurity posture?
- Have their rating and/or risk vector grades improved since I enabled their access to the Bitsight portal?
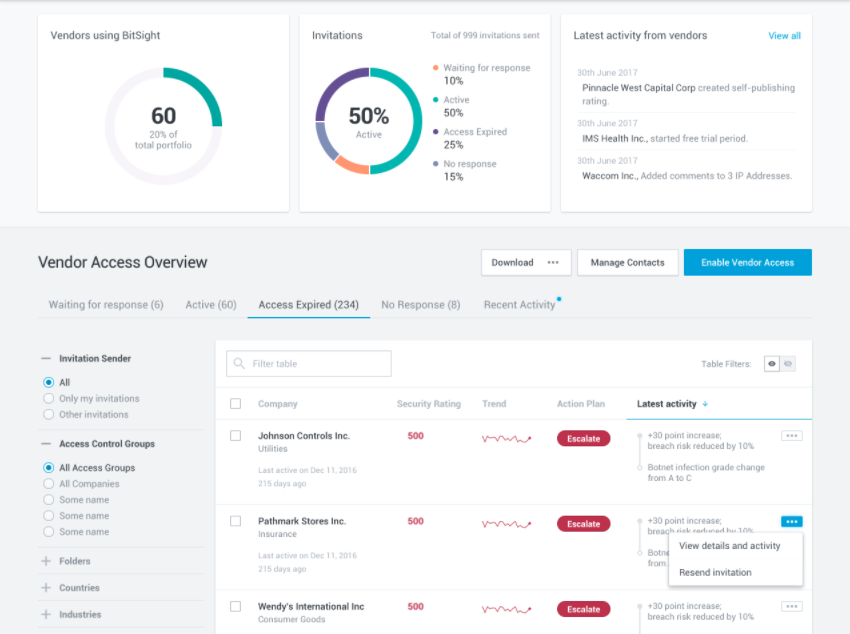
Customers can filter based on folders within their portfolio to track the status for a group of particular vendors, or even track the status of vendors they’ve invited that exhibit a particular type of infection or vulnerability. For instance, a company can filter to identify vendors who have not responded across specific levels of criticality.
Security and risk professionals should no longer have to keep tabs on each vendor they work with individually. Not only is this a cumbersome process — it also prevents organizations from scaling their vendor risk management programs. Bitsight is making it possible to reach out to vendors en masse and instantly identify which companies have responded to potential issues and which have not. Vendor Risk Management needs to be more of a collaborative discussion, not a combative one. Whether or not you are a Bitsight customer, this enhancement of the Bitsight Security Rating platform will help risk and security professionals work together.