Organizations need a way to assess the ongoing state of their security posture in order to identify and detect unknown risk hiding throughout their digital ecosystems.
How to Conduct a Cloud Security Audit: A 5-Step Checklist
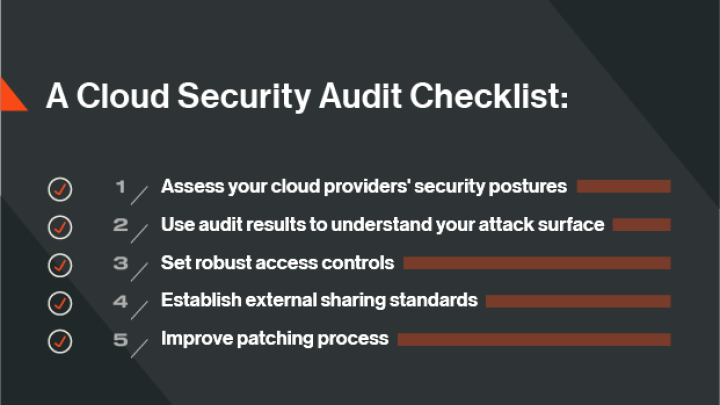
A checklist for your cloud security audit
For the first time, cloud security breaches and incidents are more commonplace than on-premises attacks. According to the 2021 Verizon Data Breach Investigations Report (DBIR), in 2020, 73% of cyberattacks involved cloud assets, compared to only 27% in the previous year. That statistic is punctuated in a separate study by Oracle and KPMG, which found that three-quarters of organizations have experienced data loss from a cloud service more than once.
As your business increases its dependency on digital infrastructures and introduces more cloud providers to its network, you must assess its cloud security posture – on a continuous basis. While you should customize any assessment to your industry or size of your organization, here are some standard best practices we recommend you include in your cloud security audit.
1. Assess your cloud providers' security postures
No one wants to enter a relationship with a partner whose security posture isn’t what it should be. The same holds true of your cloud vendors. In addition to reviewing their security policies and protocols, you need a way to independently ascertain risk based on data-driven insights – from onboarding through the life of the relationship.
This practice may sound overwhelming, but you can easily automate this process using a tool like security ratings.
Ratings work by continuously monitoring a vendor’s security posture based on factors such as vulnerabilities, compromised systems, adherence to industry best practices, and compliance with cybersecurity frameworks. Findings are presented as an easy-to-understand numerical score with a higher rating equating to better overall security performance. If a rating is low, you may choose not to enter into a cloud services agreement with a vendor. Alternatively, if you consider them business-critical, you can work with them to improve their rating.
You can also use security ratings to keep an eye on any changes that may impact a vendor’s security posture over time. This will stop risk creeping into the relationship.
2. Understand your extended attack surface
Cloud consumption can create visibility blind spots. In fact, the Oracle/KPMG study found the biggest cloud security challenges organizations must overcome are a lack of visibility into software vulnerabilities and misconfigured cloud services that expose servers to cyber risk. Unfortunately, traditional cyber security audits and cyber security assessments don’t always scale into the cloud (particularly multi-cloud environments), making it hard to discover how secure your cloud-hosted assets are.
Bad actors know this and frequently exploit weaknesses that can arise when cloud assets aren’t monitored continuously and effectively. Compromised systems, open ports, unpatched software, and other vulnerabilities present open doors for industrious hackers.
Instead, consider adding attack surface monitoring technology to your cyber security audit checklist. By continuously analyzing your cloud environment, you can quickly identify your organization’s cloud assets and any gaps in your security controls. You can also identify areas of concentrated risk, such as a misconfigured web application firewall, and prioritize that asset for remediation. The technology even reveals hidden security issues that may be lurking in shadow IT.
With visibility into the risk profile of all your cloud assets, your organization will also solve the challenge of the shared responsibility model. After all, you can’t secure what you can’t see.
This form of monitoring also solves the challenge of the shared responsibility model by giving visibility into the risk profile of the cloud assets you are responsible for on a continuous basis.
3. Set robust access controls
Access management violations are among the most common cloud security risks (just see how much damage was caused to Colonial Pipeline, who didn’t have multi-factoring authentication requirements for employees). While your cloud provider will designate administrator-level access to trusted account managers, if those credentials fall into the wrong hands, your data may be at risk. It’s a big problem. The Verizon DBIR found that 61% of data breaches involved credentials theft.
Take the following steps to reduce risk on your side of the cloud:
- Set strong password policies and standards
- Make multi-factor authentication mandatory
- Regularly audit permissions
- Monitor users’ activities as they interact with cloud assets
Use your cyber security audit checklist to periodically review your organization’s access control policies and multi-factor authentication requirements. Then, over time, ensure that security teams are regularly auditing permission rights and monitoring user activity in the cloud.
4. Establish external sharing standards
One of the major benefits of the cloud is convenience. It has made accessing and sharing information across the enterprise a breeze. But convenience brings risk. Employees may download a file containing sensitive information to their home network or share it with someone outside the organization.
Your cloud security audit should include a review of your data loss prevention policies. For instance, you can establish rules that limit sharing of sensitive documents, automatically warning the user against sharing the file with an external email domain or quarantining the file before it is accessed or shared.
5. Audit your patching cadence
Maintaining a regular patching cadence is key to ensuring your cloud environment is secure. But getting a handle on patch management can be an unending challenge for IT and security teams. The Verizon DBIR found that patching performance is still lacking. Research suggests that it takes the average organization 38 days to patch a vulnerability – and that’s a problem. A Bitsight study found that organizations who are slow to patch systems and software are seven times more likely to be a victim of ransomware than those that maintain a regular patching cadence.
Finding gaps in both your cloud and on-premises patching program isn’t easy. A sea of alerts and a lack of resources can hamper efforts. Fortunately, you can use Bitsight Security Ratings to continuously identify unpatched systems(wherever they’re located), prioritize which patches are most critical, and allocate resources where they are needed most.
Threats are evolving. So must your cloud security audit.
The Verizon DBIR underscores the security challenges facing businesses as they move to the cloud. Surveys and reports continue to underscore the security challenges of moving to the cloud. Yet, cybersecurity teams are still playing catch-up, resulting in a cloud security readiness gap. To mitigate the risk created by this situation and accurately assess and manage enterprise risk, your cyber security audit checklist must include measures that provide broad and continuous visibility into the security posture of your cloud assets and that of your cloud service providers. Only then is focused and effective risk mitigation possible.
Smart security policies that address common areas exploited by hackers are critical. But your audit must also provide broad and continuous visibility into the security posture of your cloud assets and that of your cloud vendors. Only then is focused and effective risk mitigation possible.



