Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Insights blog.
Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Bitsight and Google collaborate to reveal global cybersecurity performance

Bitsight and Google collaborate to reveal global cybersecurity performance
This joint study between Bitsight and Google arms organizations with actionable insights, providing the current status of global cybersecurity performance by analyzing nearly 100,000 global organizations across 16 cybersecurity controls and nine industries amid heightened stakeholder demands on cybersecurity strategy.

Highlight cyber exposure management's role in risk control and urge collaboration between security experts and business leaders for improved cyber risk management.

Whaling attacks are a form of spear phishing that target senior executives. Learn how to defend against these attacks.

These are the basic steps you should take to develop an effective cyber risk management strategy.

Does your organization have a cybersecurity risk remediation plan? Follow these 5 tips for crafting one.

Network security monitoring tools are a critical component of any IT security toolkit.

Our strategic direction is bolstered by an expanded partnership with Moody’s Corporation, enhanced Third-Party Vulnerability Detection & Response capabilities, and an improvement to our proprietary ratings algorithm.

New outsourcing opportunities may present as you build next year’s strategy, making Vendor Risk Management (VRM) critical for three main reasons.

Cyber risk quantification methods can help you talk about risk in terms of business and financial impacts. Here’s how to find the right method for your organization.

Wondering how to leverage your remaining funds? As you decide how to use your end of year budget, ask yourself these questions.
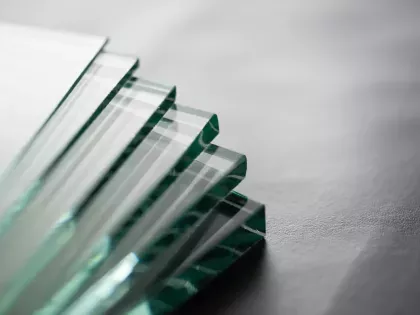
Improve visibility into third-party risk with a single pane of glass approach to vendor risk management – from onboarding through the life of the relationship.

Executive performance and cyber risk management are now inextricably linked. Learn how CISOs can help executives be more accountable for cyber risk.

Compliance vs. Risk management. How your organization can unify its efforts to ensure cyber resilience.

The UK Cyber Resilience 2022 strategy is a remarkable blueprint for any organization looking to improve cyber resilience. What lessons can be learned?

What is information risk management? Learn more about how the classic equation of threat x vulnerability x consequence helps inform your cybersecurity risk management strategy.

Cyber risk mitigation and remediation are often talked about in the same terms. But they are different. Learn how you can optimize both.