5 Tips for Crafting a Cybersecurity Risk Remediation Plan
What was the last time you re-evaluated your cybersecurity controls? Now is the time to review and consider updating your cybersecurity risk remediation strategy.
Do you have a plan for cybersecurity risk remediation? Has this plan outlined who needs to be involved? How are you being notified of risks? Is there a process in place to identify and prioritize the riskiest threats for rapid remediation? Now more than ever, it's important to plan ahead for evolving cybersecurity threats and follow these five tips for crafting a risk remediation plan.
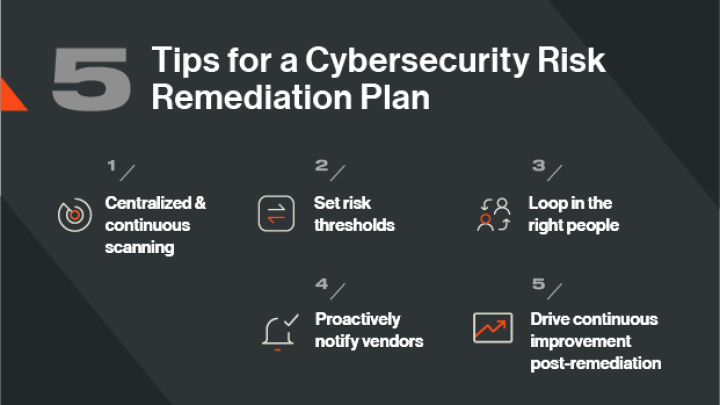
5 tips for an effective cybersecurity risk remediation plan:
- Utilize centralized and continuous scanning technology to identify risk
- Set acceptable risk thresholds
- Determine who needs to be looped in
- Proactively notify vendors
- Drive continuous improvement post-remediation
1. Utilize centralized and continuous scanning technology to identify risk
To effectively remediate cybersecurity risk, you need to first identify it. As more and more business operations move to the cloud, and across multiple locations and countries, the need for network security monitoring tools increases. These tools can help to keep your digital environment secure, but the sheer amount used can be overwhelming. Indeed, studies suggest that the average IT and security team uses between 10 and 30 monitoring tools.
Yet these siloed tools can create more exposure. Your security teams are buried in a sea of alerts, and may miss something.
A better way to scan your IT infrastructure for cyber risk is to leverage continuous monitoring technology that automatically discovers where risk lies hidden across your growing attack surface and threat landscape. Using dashboards that provide a near-instantaneous overview of the security of your digital resources, you can identify potential vulnerabilities and suspicious user conduct, and find where your network may have been infiltrated, without becoming overwhelmed by too many tools.
To aid your cybersecurity risk remediation plan, you can also visualize where cyber risk is concentrated and prioritize those assets for further investigation.
2. Set acceptable risk thresholds
It’s unrealistic for the SOC team or any other team to respond to every security alert in the same manner. Accommodations must be made, and that’s okay. Good cybersecurity requires a shift from a reactive defense strategy to a highly focused and proactive approach.
One way to do this is to set acceptable risk thresholds. That’s where Bitsight Security Ratings come in.
Similar to a credit score, Bitsight Security Ratings range in value from 250 to 900, with a higher rating equaling better cybersecurity performance. Ratings vary by industry. For instance, the average rating for the legal sector is relatively high at 710. Use this handy tool to help establish an acceptable cyber risk threshold for your organization then receive alerts if your security performance dips below that grade for speedy remediation.
3. Determine who needs to be looped in
Not all cyber risk is created equal and different risk scenarios require different responses and different teams. Determining which teams need to be looped in depends on whether the incident requires attention now and which assets are impacted. Bitsight can help with this task by continuously and automatically identifying areas of disproportionate risk across your digital environment.
For example, a misconfigured web firewall that protects sensitive data in the cloud would be considered a high priority risk that requires immediate attention from the Security Operations Center (SOC). Similarly, the discovery of malware on a web server would require rapid attention.
With these insights, investigation and analysis teams can prioritize these assets for remediation. They can also use Bitsight’s integrations with SIEM tools, like Splunk, to refer to all cyber threat intelligence in one place. Depending on the nature and severity of the risk, remediation can be conducted solely by the security team or other teams may need to be looped in. For instance, a severe incident will require engagement from the C-suite and board of directors, legal counsel, and communications teams.
4. Proactively notify vendors
According to Gartner, 60% of organizations work with more than 1,000 third parties. Because of the interconnected nature of these vendor relationships, a cyber incident on your network may have a cascading impact across your digital supply chain, as the 2020 SolarWinds hack did.
To stay on good business terms with your vendors, it's important that your cybersecurity risk remediation plan includes a process for notifying third parties of a serious cyber incident on your network so that they can assess their own risk exposure.
Bitsight helps makes this process easy. Using the Enable Vendor Access (EVA) feature in the Bitsight product, you can share your security findings with your third parties. With EVA, they can assess their networks for risk, investigate forensic data on any vulnerabilities or cybersecurity incidents, and gain a better understanding of their overall security postures.
5. Drive continuous improvement post-remediation
Use the data insights that Bitsight provides to learn from your remediation activities and identify trends and patterns. For instance, if you receive alerts about vulnerabilities like unpatched systems or misconfigured network devices on a regular basis, you may need to revisit your device policies.
You can also use Bitsight’s suite of continuous monitoring tools to plan and measure improvement over time. With Bitsight, you can align investments and actions where they will have the highest measurable impact for your organization’s cybersecurity program, as well as facilitate data-driven conversations around cybersecurity among key stakeholders.
How to Make Your Cybersecurity Remediation Process More Efficient
Now that you have your cybersecurity risk remediation plan in place, it's time to rethink the traditional processes you have in place throughout your risk management program — from the initial discovery and assessment phases to ongoing performance monitoring. By finding new operational efficiencies in each stage, you can maximize your cybersecurity ROI and ultimately do more with less.
Gone are the days when you can (or should!) respond to every security alert in the same manner. As your team continues to adjust to the “new normal” operating environment, it’s more important than ever that you have the necessary context and visibility to be more strategic in where you focus your mitigation efforts. Here are 3 ways to drive efficiency in your cybersecurity remediation process:
1. Prioritize efforts based on areas of disproportionate risk
In many ways, prioritization is the key to optimizing your security remediation process. After all, your team may be inundated with alerts — some of which may prove to be false positives — and you don’t have the bandwidth or resources to tackle every potential issue that comes your way. In order to prioritize effectively, you need to have a system in place that empowers you to gain visibility into your expanding attack surface and regularly assess all of your critical assets for disproportionate risk.
That’s where Bitsight Security Ratings come in. Derived from objective, verifiable data, security ratings provide a dynamic measurement of your organization’s cybersecurity posture — making it easier than ever for you to rate your performance and identify vulnerabilities across your digital ecosystem. Bitsight Security Ratings are calculated using externally observable data on compromised systems, security diligence, user behavior, and public disclosures. And these four data categories are comprised of various risk vectors, including everything from botnet infections and exposed credentials to open ports and patching cadence.
By looking at your ratings for different risk vectors, you can identify areas of disproportionate risk and prioritize your efforts accordingly. For instance, the Bitsight platform assesses open ports to evaluate whether any unnecessary access points exist. And recent research by Bitsight found that organizations with an F as their Bitsight Open Port grade are more than twice as likely to experience a breach than companies with an A. This is the type of finding that you would want your team to address immediately so that you could prevent a potentially damaging security incident.
By having these data-driven insights at your fingertips, you can make informed decisions on how to prioritize limited resources and focus remediation efforts on the areas that can have the biggest impact on your cybersecurity posture.
2. Streamline the process of collecting and using data for remediation
It’s clear that data plays a major role in your ability to make strategic cybersecurity decisions. But in order for you to be able to use your data effectively, it needs to be easy to access. After all, you don’t have the time to reference multiple different dashboards or go through a slow, manual process of compiling insights from various tools.
Through Bitsight’s integrations with SIEM tools like Splunk, it’s easier than ever to pull your Bitsight findings into existing security workflows and dashboards — so you can refer to all of your threat intelligence insights in one place.
By combining your Bitsight observations with other security findings you may already be collecting, you can extract more value from this data than ever before — and streamline the process of compiling and using cybersecurity insights to make more informed, comparative remediation decisions.
3. Report on improvement using a common language
Another huge factor in your ability to make your remediation process as efficient as possible is whether you have a means through which to clearly track and communicate your team’s progress on addressing the cybersecurity gaps that you discover.
With Bitsight Security Ratings — which are based on independent, objective, and broadly accepted data — you can unite your entire organization around a standardized KPI and common language for quantifying security performance. And as these ratings are updated on a daily basis, you can always have real-time insight into your program effectiveness, and how your investments in remediation resources are impacting your cybersecurity posture over time.
And now, with our recently released Issue Tracking for Remediation feature, it’s easier than ever to monitor your progress on remediation activities. With this exciting new capability, you can set the status of specific Bitsight findings and assign ownership for remediation activities directly from your MyCompany or MySubsidiary Findings Table in the portal. Now, you can ditch your manual remediation status tracking sheets and monitor your progress directly in the Bitsight platform.
Effective cybersecurity risk remediation depends on data-driven insights
A common theme among each of these cyber risk remediation planning tips is the need for reliable, easily accessible, and understandable data. Each tool and practice described here works together to ensure your organization’s remediation efforts are informed by data-driven insights, visibility, and context.
In today’s ever-evolving cybersecurity landscape, it’s more important than ever to be able to quickly identify which potential threats and existing risks you need to mitigate first for the greatest performance impact. With Bitsight Security Ratings, you can ensure you always have the necessary context and visibility to optimize your cyber risk remediation plan.
Interested in learning more about how to do more with less? Check out our new ebook, 3 Ways to Get the Most Out of Your Security Investments.



