New! The Security Ratings report is now the Executive Report. Request your report to see enhanced analysis such as your rating, likelihood of ransomware incidents, and likelihood of data breach incidents.
The Importance of Actionable Metrics in Managing Vendor Risk

In today’s market, an increasing number of security and risk management executives are being asked to present to the Board of Directors on the state of their — and their third parties’ — security and risk programs. Gartner estimates that by 2020, 75% of Fortune Global 500 companies will treat vendor risk management as a board-level initiative to mitigate brand and reputation risk. Bitsight understands that making an organization’s cybersecurity posture accessible to C-level executives and the Board of Directors is becoming more of a requirement within the business; we’ve added capabilities within Bitsight Security Ratings that arm security and risk management executives with actionable metrics that they can share with the Board of Directors.
Most Boards understand that cybersecurity — both for their own organization as well as their supply chain — is a critical issue and as a result, they frequently ask to receive regular briefings on the topic. If your organization has just begun this practice, it’s essential that you establish credibility when you present to your Board of Directors. Bitsight’s latest product enhancements allow organizations take actionable steps to identify, effectively communicate about, and actively manage the risk in their vendor portfolios.
Bitsight Security Ratings have helped hundreds of organizations develop their vendor risk management (VRM) strategies and programs. The foundation of this success has been objective, verifiable, and actionable data that empowers executives to make critical business decisions. To continue to do this, organizations need a set of prescriptive features when forming their VRM program. Bitsight now provides a prescriptive approach that allows companies using Bitsight Security Ratings to increase the actionability and effectiveness of their third party risk management programs. Using this prescriptive methodology enables Bitsight customers to operate their VRM programs at scale, drive faster decision making, and enhance collaboration between first parties and their critical vendors.
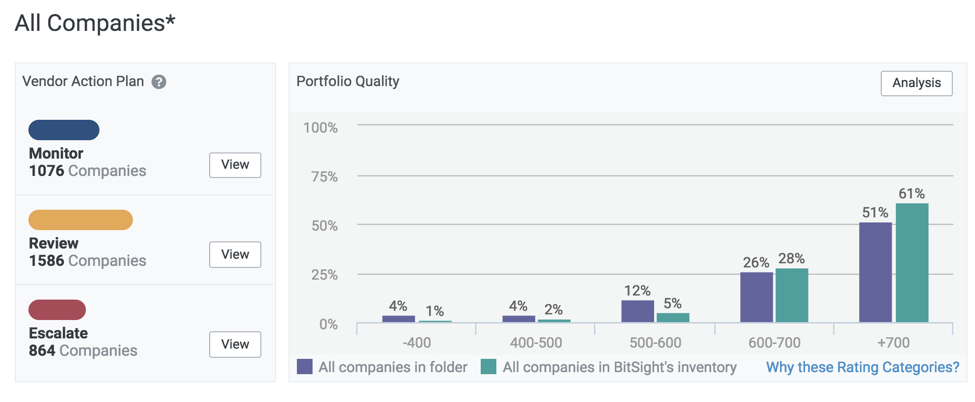
A portfolio overview in the Bitsight Security Ratings portal, with the vendor action plan and company breakdown indicated on the left.

A portfolio overview in the Bitsight Security Ratings portal, with the vendor action plan and company breakdown indicated on the left.
Additionally, Bitsight users can now create a vendor action plan based on their vendors’ tier, or prioritization, and their security rating. If a vendor has a security rating between 250-740 and is tiered as either High or Moderate priority, they are labeled as Escalate, meaning that immediate remediation steps should be taken. As the most serious vendor action plan label, “Escalate” marks that the company should issue an Enable Vendor Access (EVA) request to the vendor and ask them to remediate issues that Bitsight has identified.
Vendors tiered as Moderate or Low with a security rating of over 640 may be labeled as Review or Monitor. If labeled as “Monitor,” no action is needed and users can simply choose to receive a notification if the ratings change. “Review” signifies that the company should investigate the security posture of the third party further to gain a deeper understanding and determine if any remediation steps are necessary.
Actionable metrics should be at the heart of every organization’s VRM program, especially as organizations begin to communicate their security posture to their executives. By using Bitsight Security Ratings’ prescriptive approach to VRM, companies can convey easy-to-understand metrics to their Board of Directors or executives. This allows for easier collaboration moving forward as security teams continue to develop third party remediation plans and develop ways to proactively mitigate the risk vendors can pose to their organization.



