The 2025 State of Cyber Risk and Exposure report reveals why security leaders are under pressure: AI-driven threats, expanding attack surfaces, and misalignment with business priorities. Based on global survey data, it surfaces the root causes behind today’s risk fatigue—and what mature organizations are doing differently.
How to Build a Security Compliance Audit Process that Works All Year Round
Tags:


Security compliance audits can feel intimidating, especially if your team has never been through one before. For many organizations, an audit feels like a high-pressure project with a hard deadline, a long list of evidence requests, and a lot of manual work spread across security, IT, legal, and compliance teams. For vendors and companies in highly regulated industries, audits and risk assessments may already be a routine part of doing business.
But audits should not be treated as isolated events. A strong audit process is not just about passing a review once a year. It is about understanding your security posture, spotting weaknesses before they turn into incidents, and showing that your organization can manage risk in a consistent, defensible way all year long. The same year-round mindset should also apply to third-party risk.
When handled well, security audits do more than support compliance. They help uncover vulnerabilities, reveal process gaps, strengthen accountability, and improve the way your organization protects sensitive data.
Why security audits matter
Security audits are essential because they help organizations identify vulnerabilities before attackers can exploit them. They offer a structured way to evaluate whether security controls are working as intended and whether policies, procedures, and systems line up with internal expectations and external requirements.
A good audit process also shows how well teams work together. It can reveal whether security operations, GRC, IT, and risk teams are sharing information effectively, whether issues are being escalated when they should be, and whether threat, control, and compliance activities are actually aligned.
A thorough cybersecurity audit usually looks across multiple parts of the security program, including data protection practices, access controls, hardware and software management, incident readiness, third-party risk, and regulatory compliance. Auditors often review policies, logs, network diagrams, tickets, change records, and other documentation to determine whether security measures are not just documented, but truly operating in practice.
That is one reason regular audits are so valuable. They can surface weak procedures, inconsistent control execution, and gaps that might otherwise go unnoticed. They also encourage employees and control owners to follow security practices more consistently, which helps organizations identify issues earlier.
At the end of the day, security audits are a core part of risk management. They help organizations understand where their cyber risks are, how those risks are being managed, and whether existing controls are strong enough to support the business.
Why audit readiness should not be a once-a-year fire drill
If this is your first audit, it is easy to think of it as a one-time milestone. The audit gets scheduled, everyone scrambles to gather evidence, and the organization pushes through the process as quickly as possible.
That is common, but it is not sustainable.
When audit preparation happens at the last minute, evidence is often incomplete, inconsistent, or outdated. Control owners have to dig through multiple systems to prove that a review, approval, or remediation activity actually happened. Security and GRC teams end up spending their time chasing screenshots and spreadsheets instead of focusing on the most critical risk issues.
This kind of reactive process also makes it easier to miss something important. A control may exist, but if ownership is unclear or the evidence is hard to retrieve, then the audit becomes much harder than it needs to be.
A better approach is year-round audit readiness. That means building a process where controls, evidence, and risk context stay current throughout the year. Now, instead of treating the audit like an emergency, you treat readiness as part of normal operations.
Four fundamentals of year-round audit readiness
Year-round audit readiness does not mean your team is constantly preparing for an auditor. It means your security and compliance program is organized well enough that you are not starting from scratch every time someone asks for proof.
In practice, that usually comes down to four fundamentals:
- First, you need a current view of your assets, risks, and controls. You should know what systems matter, what data is sensitive, what threats are relevant, and which controls are supposed to reduce risk.
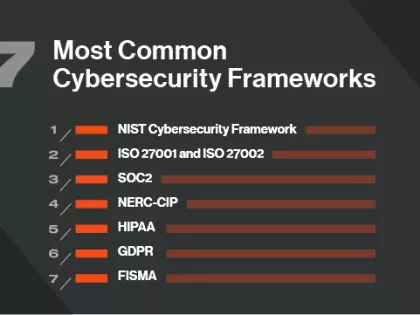
- Second, you need to connect those controls to the frameworks and requirements that matter to your business. That might include NIST, ISO 27001, SOC 2, PCI DSS, or internal security standards. That kind of mapping helps teams avoid duplicative work and makes it easier to explain how one control can support multiple requirements.
- Third, your evidence needs to be current and useful. Strong audit readiness depends on more than static files saved the week before the audit. It depends on records that reflect how security work actually happens, including logs, approvals, review histories, system exports, change records, vendor documentation, and remediation activity.
- Finally, there needs to be enough consistency that an auditor can easily follow the story. They should be able to see what the control is, who owns it, how often it operates, what evidence supports it, and how exceptions are handled.
When those pieces are in place, the audit becomes much more manageable.
If this is your first audit, start with controls and evidence
If your organization has never gone through a security audit before, the best place to start is not with perfection. It is with clarity.
First, identify the controls that matter most to your audit scope. For many organizations, that includes access management, vulnerability management, logging and monitoring, incident response, vendor oversight, change management, backup practices, and policy governance.
From there, document the basics for each control:
- What is the control supposed to do?
- Who owns it?
- How often does it happen?
- What evidence shows that it happened?
- Where is that evidence stored?
These questions may sound simple, but they are the foundation of an effective audit process.
It also helps to think practically about what auditors want to see. Auditors assess an organization’s security posture by reviewing things like policies, logs, network diagrams, and technical documentation. They are looking for evidence that security measures are appropriate, implemented, and functioning consistently. In some cases, this also helps teams prepare for more in-depth assessments such as penetration tests or control validation exercises.
Next, figure out what actually counts as good evidence.
Good evidence is accurate, current, and tied to the real operation of a control. A policy by itself is usually not enough. Auditors want to know whether the policy is being followed and how you know it is being followed.
That is why operational records are often much more valuable than one-time screenshots. Useful evidence might include access review records, ticket histories, configuration exports, approval logs, vendor assessment results, training completion reports, backup reports, incident records, and monitoring data that shows control activity over time.
The stronger your evidence is, the easier it becomes to explain your environment and defend your control posture.
How to make the process sustainable
A continuous process only works if it fits into the way the organization already operates.
The most sustainable audit programs build compliance into normal workflows instead of layering it on afterward. If access reviews already happen quarterly, then evidence collection should be part of that process. If vendor assessments are part of procurement or third-party risk management, then the supporting documentation should be retained in a way that makes future review easier. If incidents, vulnerabilities, or exceptions are tracked in a system of record, that system should also support your audit trail.
Depending on your environment, sustainability may also mean using the right technologies to improve visibility into cloud usage, access controls, asset exposure, and third-party risk. The point is not any single tool category. The point is making sure your controls are visible enough to support both day-to-day security operations and audit requirements.
How Bitsight can help
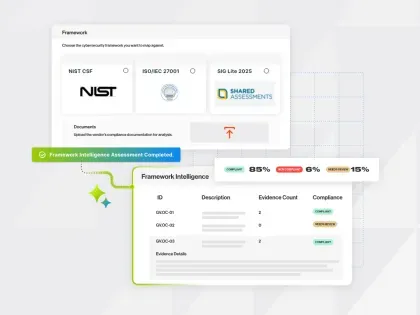
Building a year-round audit readiness process is much easier when security and GRC teams have continuous visibility into external exposure, asset risk, and third-party security performance.
That is where Bitsight can help.
Bitsight helps organizations move beyond point-in-time evidence gathering by providing ongoing insight into security posture, internet-facing asset exposure, and vendor risk. Instead of relying only on static snapshots or manually assembled updates, teams can use more current data to support audit preparation, control discussions, and reporting.
Stronger third-party oversight
Third-party risk is receiving more attention in audits, and for good reason. Bitsight helps organizations monitor vendor security posture continuously, making it easier to demonstrate that oversight is active and ongoing rather than limited to a one-time assessment.
Through Continuous Monitoring, organizations can also use Dark Web Intelligence for Supply Chains to gain ongoing visibility into threat activity across vendors, suppliers, and partners. That helps security, GRC, and third-party risk teams identify potential targeting earlier and prioritize response based on real-world signals.
More current evidence for audit narratives
Audit readiness improves when teams can show that their security program reflects current conditions rather than outdated snapshots. Bitsight can help support a more measurable, real-time view of risk that strengthens audit conversations and reporting.
Bitsight also helps teams understand exposed assets, changes in attack surface, and signs of emerging risk over time, including issues like open ports. In practice, this supports stronger asset management, vulnerability management, and external exposure monitoring.
Support for risk-informed compliance
Frameworks may differ, but many controls point back to the same security outcomes. Bitsight helps security and GRC teams connect external risk insight to broader governance and compliance efforts, which can make audit preparation more efficient and more meaningful.
Bitsight does not replace the audit process itself, but it can help make that process more informed, more continuous, and easier to sustain over time.
The broader value of staying audit-ready
One of the biggest misconceptions about audits is that they are only about compliance. In reality, a strong audit process improves much more than your ability to pass a review.
It reduces disruption because teams are not constantly scrambling for documentation. It builds trust with customers, regulators, and leadership because the organization can explain its security posture more clearly. And it strengthens governance by connecting risks, controls, and evidence in a more consistent way.
Most importantly, it helps organizations become more resilient. That is why the best audit programs are not built around panic. They are built around visibility, repeatability, and ownership.