OPC UA Exposure Snapshot: A Year in Review of Internet-Facing Devices


Over the past year, Bitsight TRACE has identified 14,220 unique internet-exposed Open Platform Communications Unified Architecture (OPC UA) servers globally. Given OPC UA's critical role as a communication backbone for modern industrial control systems (ICS) across numerous sectors, this level of exposure warrants a closer look. Our analysis reveals that over half (51.74%) of these devices allow unauthenticated access, while 80.26% transmit data in plaintext without encryption or integrity protection. Additionally, nearly 90% support at least one deprecated security policy with known cryptographic vulnerabilities - configurations that violate OPC UA security best practices. This is part of a larger and concerning trend of increasing exposures of all kinds of ICS/OT devices, as detailed in our previous post: The Growing Exposure of ICS/OT Devices. This exposure, often coupled with insecure configurations, represents a substantial and frequently underestimated risk to operational technology (OT) environments, potentially impacting industrial processes, critical infrastructure, and data security.
Introduction: Understanding the Landscape
OPC UA (Open Platform Communications Unified Architecture) is a machine-to-machine communication standard crucial for industrial automation, enabling secure and reliable data exchange across diverse equipment and systems. In practice, OPC UA enables real-time data collection from production equipment - such as Programmable Logic Controllers (PLCs) - to supervisory systems like SCADA and Manufacturing Execution Systems (MES), allowing operators to monitor production lines, track equipment performance, and optimize manufacturing processes. An evolution from its predecessor, OPC Classic, it addresses earlier limitations by offering platform independence and a robust security model, making it a cornerstone for Industry 4.0 and the Industrial Internet of Things (IIoT).
Unlike legacy industrial protocols such as Modbus, which was developed in 1979 and transmits data in plaintext with no built-in authentication or encryption, OPC UA was designed from the ground up with a comprehensive security model that includes mutual authentication, encrypted communication, and certificate-based trust.
OPC UA's applications span numerous sectors, including manufacturing, energy, building automation, and pharmaceuticals, facilitating seamless communication between PLCs, SCADA systems, HMIs, and enterprise-level platforms. However, OPC UA servers are designed for use within trusted industrial networks and should not be directly exposed to the internet, as this may expose critical operational data and control systems to potential attackers.
Bitsight continuously scans the internet for exposed systems. Our specific monitoring for OPC UA began in June 2024, and this analysis covers data collected through June 2025 from 85,505 exposures, corresponding to 14,220 unique devices found across 99 countries.
It's important to note that the retrieval of certain information presented in this post (such as manufacturer names, software versions and build dates) was possible because these specific servers allow reading such fields using the Anonymous Identity Token. This configuration represents a significant security risk, as it allows anyone to access server information and potentially read operational data without authentication. Of the 14,220 total exposed devices, a significant 7,358 (51.74%) allowed this form of anonymous interaction - a finding that highlights the extent of insecure configurations in internet-exposed OPC UA deployments.
A Note on Vendor-Specific Information
Among the data our probe retrieves from devices that allow anonymous access are manufacturer names and product versions. We deliberately do not include this vendor-specific information in this report. Exposing an OPC UA server to the internet and allowing anonymous access is a deployment and configuration choice; securing these systems is the responsibility of the end user or asset owner, and our goal is to raise awareness about exposure and configuration risks, not to single out any manufacturer.
In fact, major OT vendors consistently advise against direct internet exposure of OPC UA and other OT devices. For example, Schneider Electric has published guidance emphasizing the importance of removing OT connections to the internet and implementing robust cybersecurity measures. Similarly, Siemens has issued Security Bulletin SSB-104599 explicitly recommending that devices be disconnected or removed from networks with inadequate security levels, such as the internet. Rockwell Automation has likewise advised users to never configure their assets to be directly connected to the public-facing internet. WAGO has also recommended that industrial control systems (ICS) should not be directly accessible from the Internet and should be protected using a defense-in-depth strategy. Despite this widespread industry guidance, our analysis reveals that thousands of devices remain accessible from the internet.
Research: Developing our OPC UA Probe
To accurately identify and analyze the exposed OPC UA devices presented in this report, our team undertook a dedicated research and development effort to build a custom probe that operates within the current scanning policies at Bitsight. This process was a significant team effort, beginning with a deep dive into the OPC UA specification to thoroughly understand the protocol's complex syntax and communication patterns.
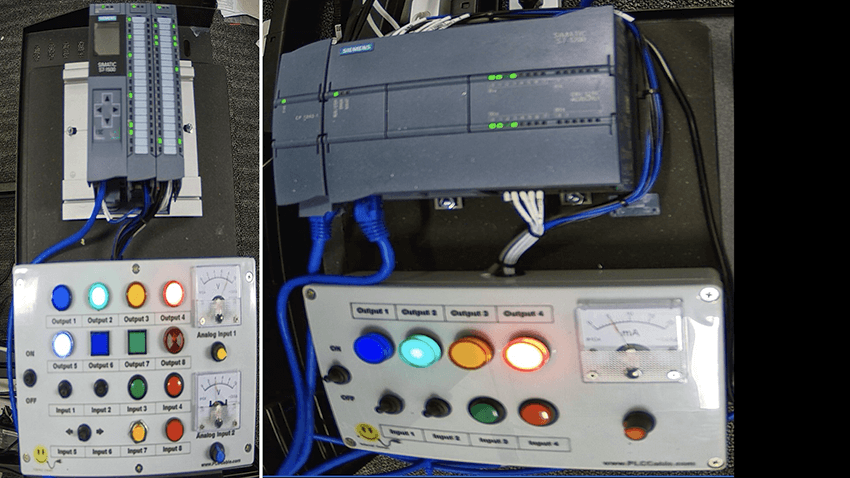
A core principle of this project was safety and non-disruption, in particular we took great care to ensure any interaction with devices would cause no change in their current operation Our approach to the sensitive nature of industrial control systems (ICS), involved utilizing our existing ICS Lab to build and test our probe, augmenting it with a variety of devices that support OPC UA to create a safe testing environment. The probe was rigorously tested to be as passive and safe as possible.
Our ongoing partnership with Schneider Electric allowed us to further enhance the probe's accuracy, reliability and safety during the research process. They provided access to some of their own OPC-UA enabled devices that allowed us to validate our probe. This collaboration has been invaluable to ensure our probe is safe and effective.
Following this comprehensive research, development, and testing process, the finalized probe was integrated into Bitsight's global internet scanning infrastructure, enabling the large-scale data collection and analysis that form the basis of the findings in this report.
Key Findings: A Data-Driven Look at Exposed OPC UA
Our analysis reveals several key characteristics of the internet-exposed OPC UA landscape.
Where are these 14,220 Devices Located?
The 14,220 exposed OPC UA devices are globally distributed across 99 countries, though concentrations are notable in several key industrial regions. This distribution may reflect varying adoption rates of OPC UA, density of industrial activity, or regional deployment practices.

Table 1: Top 10 Countries by Exposed OPC UA Devices (June 2024 - June 2025)
| Country | Unique Device Count | Percentage of Total (14,220) |
|---|---|---|
| Germany | 3,194 | 22.46% |
| United States | 1,334 | 9.38% |
| Korea, Republic of | 1,289 | 9.06% |
| China | 1,105 | 7.77% |
| Australia | 828 | 5.82% |
| Norway | 596 | 4.19% |
| Spain | 582 | 4.09% |
| Greece | 534 | 3.76% |
| Italy | 474 | 3.33% |
| Taiwan | 373 | 2.62% |
Which Ports Are Used by the 14,220 Devices?
The vast majority of the 14,220 exposed OPC UA devices (13,766 devices or 96.81%) were found using the standard OPC UA port, 4840/TCP. This commonality simplifies discovery for broad internet scans. A small fraction utilizes alternative ports, which may represent varied configurations or, in some cases, perhaps an ineffective attempt at security through obscurity.
Table 2: Common Ports Used by Exposed OPC UA Devices
| Port | Device Count | Percentage of Total (14,220) |
|---|---|---|
| 4840 | 13,766 | 96.81% |
| 4852 | 43 | 0.30% |
| 55101 | 35 | 0.25% |
| 4862 | 30 | 0.21% |
Age Profile of Devices
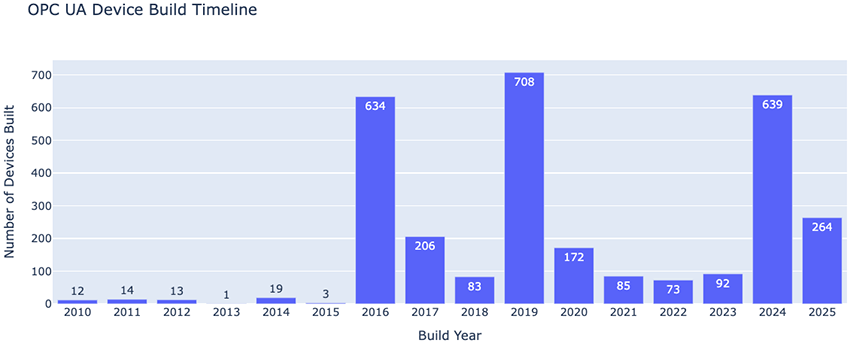
To understand the operational age of these exposed systems, we analyzed the reported BuildDate provided by servers that responded to unauthenticated probes. Valid build dates allowing for age calculation (relative to a fixed reference date of June 30, 2025) were found for 3,018 devices. This group represents 41.02% of the 7,358 anonymously accessible servers and 21.22% of all 14,220 exposed OPC UA devices found. The data suggests a mix of older, potentially less maintained systems and very new deployments among these devices. These very new deployments seem to be mostly from the products FreeOpcUa (Python Library) and open62541 (C Library), which are open-source projects and may relate to DIY projects, development, research activities, or even intentionally exposed honeypots.
1. Overall Age Distribution A majority (56.86%) of these 3,018 devices were built 5-10 years ago, with a median age of 5.57 years. However, a notable 25.38% are less than 1 year old. The average age for these devices is 4.85 years.
Table 3: Age Category Breakdown for 3,018 Dated OPC UA Devices
| Age Category | Device Count | Percentage |
|---|---|---|
| < 1 year | 766 | 25.38% |
| 1-2 years | 183 | 6.06% |
| 2-5 years | 291 | 9.64% |
| 5-10 years | 1716 | 56.86% |
| 10+ years | 62 | 2.05% |
2. Device Build Timeline The build years for these 3,018 devices show distinct manufacturing periods, with prominent clusters in 2019 (708 devices), 2024 (reflecting 639 devices <1 year old), and 2016 (634 devices).
Potential Honeypots and Research Deployments
While our analysis focuses on identifying genuine OPC UA deployments, recent research suggests that some internet-facing industrial control systems may be honeypots or research installations rather than operational devices. This is particularly relevant for two categories we identified in our data.
Among the 703 devices attributed to FreeOpcUa (Python Library) and 101 devices running open62541 (C Library), a large portion of these may represent honeypots, development environments, or research deployments rather than production industrial systems. These open-source implementations are commonly used by security researchers and honeypot operators to emulate OPC UA services for threat analysis and security research purposes. Additionally, our age analysis revealed that devices associated with these open-source libraries tend to be significantly newer (median age of 0.78 years and 0.34 years for FreeOpcUa instances and open62541 instances, respectively), which aligns with patterns observed in research deployments and honeypot infrastructure.
However, distinguishing between legitimate industrial deployments and research/honeypot installations requires deeper analysis beyond the scope of this study.
Security Posture: Observed Communication Configurations
The way these devices are configured to communicate reveals further insights into their security posture.
1. Anonymous Access Impact The fact that 51.74% (7,358) of all 14,220 exposed devices allowed unauthenticated access is a foundational security observation, as it means server nodes can be read without credentials.
2. Prevalence of Insecure Security Modes SecurityMode=None effectively disables OPC UA's transport security features, transmitting data in plaintext and leaving it vulnerable to eavesdropping and modification. Our analysis of the 11,206 devices that provided a list of supported security modes reveals that a striking 8,994 (80.26%) support SecurityMode=None. Furthermore, 3,229 of these devices (28.81% of those providing security modes, or 22.71% of all 14,220 exposed devices) only support this insecure 'None' mode.
3. Prevalence of Weak/Deprecated Security Policies Security Policies like Basic128Rsa15 or Basic256 (which often rely on SHA-1) are considered cryptographically weak and do not meet current security standards, making communication vulnerable. The None policy URI similarly offers no protection. Of the 11,206 devices providing security policy information, an alarming 9,971 devices (88.98%) support at least one weak or deprecated policy such as
http://opcfoundation.org/UA/SecurityPolicy#Basic128Rsa15,
http://opcfoundation.org/UA/SecurityPolicy#Basic256, or
http://opcfoundation.org/UA/SecurityPolicy#None.
Critically, 8,297 devices (74.04% of those providing policies, or 58.35% of all 14,220 exposed devices) only offer these outdated or insecure policies.
4. Auditing Status The OPC UA specification includes provisions for generating audit trails for security-related events such as session attempts, user authentications, and configuration changes, which are crucial for monitoring and incident response. Regarding this feature, of the 7,358 devices that don't require authentication, a large majority (4,513 devices or 61.33%) reported their OPC UA auditing feature as 'Disabled'. Only 375 devices (5.10%) reported it as 'Enabled'. For 2,470 devices (33.57%), this status was 'Not Provided' (field was NULL/empty).
Table 4: Auditing Status of 7,358 Anonymously Accessible OPC UA Servers
| Auditing Status | Device Count | Percentage of Anonymously Accessible (7,358) |
|---|---|---|
| Disabled | 4,513 | 61.33% |
| Not Provided | 2,470 | 33.57% |
| Enabled | 375 | 5.10% |
Conclusion: The Visible OPC UA Landscape
Our year-long analysis identified 14,220 internet-exposed OPC UA devices. A significant majority, 51.74% (7,358 devices), allowed anonymous interaction. Many of the systems with parseable build dates (3,018 devices from this group) have a median operational age of 5.57 years, indicating a mix of both legacy and newer systems accessible online.
The security posture of many exposed devices raises concerns. Of the 11,206 devices that reported supported security configurations, 80.26% (8,994 devices) support SecurityMode=None, with 22.71% of all 14,220 exposed devices (3,229 instances) only supporting this insecure mode. Similarly, 88.98% of those 11,206 devices (9,971 instances) support at least one weak or deprecated security policy, with 58.35% of all exposed devices (8,297 instances) only offering such policies.
This data provides a quantitative snapshot of the internet-facing OPC UA landscape, highlighting the scale of exposure, the types of operational details publicly revealed without authentication, the age profile of these systems, and the prevalence of insecure configurations. These observations underscore the visible characteristics of critical industrial components on the public internet.



