The Symbiosis of Residential Proxy Services and Malware Ecosystems
Tags:


Residential proxy services, also called RESIP, present a persistent operational hurdle for tracking and attributing malicious network activity, as they allow threat actors to mask their true origins behind seemingly benign, geographically diverse IP addresses. While often marketed for legitimate use cases, these networks are aggressively leveraged for fraud, credential abuse, and perimeter evasion. This investigation empirically shows the residential proxy economy is heavily subsidized by the malware ecosystem. With a baseline of 20% of proxy exit nodes actively communicating with our sinkholes, defenders must now treat anonymized residential traffic not just as a potential evasion tactic, but as a direct extension of botnet infrastructure. This necessitates a strategic defense shift, as relying purely on static IP reputation is no longer viable.
Key takeaways
- Massive scale: The research, conducted over a 55 day period (January 19, 2026 to March 15, 2026), yielded unprecedented visibility into the economy of residential proxies, observing 53M global unique proxy exit nodes. Top-tier services, including Netnut and 711Proxy, demonstrated massive capacity, with daily peaks ranging from over 1 million to more than 2.3 million exit nodes.
- High rate of compromise: Residential proxy infrastructure is built through systemic, unauthorized device compromise, not merely voluntary proxyware installation. Over the observation period, 15% of all distinct egress IPs (8.2M) were simultaneously flagged for active malware infections, and 13% (6.8M) exhibited riskware activity.
- Malware symbiosis: The infected subset of proxy nodes showed persistent co-infections with well-known malware and riskware, including Vo1d, Badbox, RootSTV/Pandoraspear, OpenCandy, Gamarue, and m0vy.
- True infection rate: While the global residential proxy ecosystem exhibits a 14–21% baseline infection overlap, specific clusters like IPIDEA run at a highly concentrated 15–26% overlap with payloads like Vo1d, Badbox, and RootSTV/Pandoraspear. Because our telemetry only captures actively beaconing devices, these figures are strictly lower bounds. We assess the true infection rate powering these specific networks realistically approaches 50%.
- Critical defense shift: Despite coordinated industry takedowns like the IPIDEA disruption in January 2026, demand is quickly absorbed by new services, proving that the market is resilient. Defenders must treat anonymized residential traffic as a direct extension of botnet infrastructure.
Unmasking the proxy supply chain
In the ongoing effort to track and attribute malicious network activity, residential proxy services present a persistent operational hurdle. By routing traffic through consumer broadband and mobile devices, these services allow threat actors to mask their true origins behind seemingly benign, geographically diverse IP addresses.
To build these massive IP pools, proxy providers acquire their exit nodes through a spectrum of methods, ranging from voluntary enrollment to deceptive practices and outright compromise. On the voluntary or gray area side, users may willingly install "proxyware" applications to sell their unused network bandwidth for passive income. Others are unknowingly drafted into these networks when they accept the terms and conditions of free mobile apps, VPN services, or media players that have proxy Software Development Kits (SDKs) bundled inside them. More legit ways to source for exit nodes include bulk renting residential IP address space with ISP partners to acquire clean and localized IPs.
However, a massive, hidden segment of this supply chain relies entirely on systemic device hijacking. This research builds on our previous tracking of the Socks5SystemZ malware, a backconnect proxy malware that has been active since at least 2016. We previously correlated this malware with the ProxyAM residential proxy service (now ProxyBox). While proxy networks are frequently marketed for legitimate use cases, they are aggressively leveraged for fraud, credential abuse, and perimeter evasion.
To better understand the mechanics and scale of this infrastructure, our threat research team conducted a sustained enumeration of global proxy exit nodes. By enriching this proxy telemetry with our broader compromised systems observation datasets, we set out to answer a critical empirical question: *How many of these "residential" proxy nodes are actually compromised devices operating within active botnets?*
Residential proxies and risks for organizations
To understand the severity of this threat, one must understand the concept of "rotating proxies.” This is a foundational concept in modern cybercrime operational security, describing the rapid, continuous cycling of compromised residential IP addresses by proxy networks to bypass enterprise security controls.
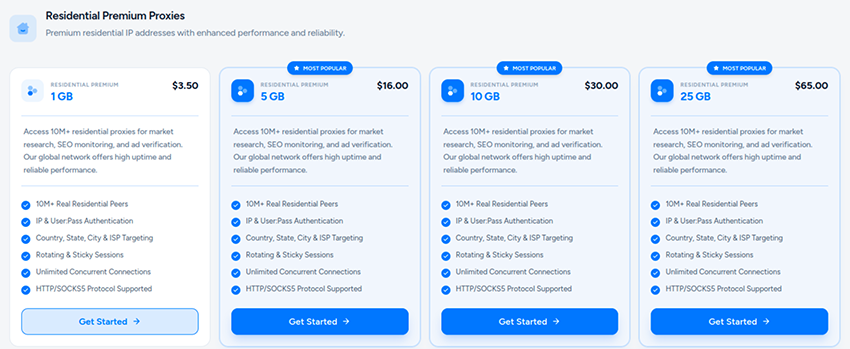
In this model, threat actors do not rely on static, easily identifiable datacenter infrastructure; instead, they route automated attacks through millions of transient home internet connections. Because these proxy nodes are often single touch, used for just one or two sessions before vanishing and being replaced by a different device, they structurally break traditional IP reputation systems. The malicious IP rotates away long before it can be flagged or blocked. For cybercriminals and fraudsters, this economy is highly lucrative, enabling massive scale credential stuffing, account farming, coupon abuse, and inventory scalping to masquerade perfectly as organic, independent human users. Renting these proxy exit nodes is often very inexpensive, typically costing around $3 USD per gigabyte. Furthermore, many services offer fully anonymous access, requiring no customer information and accepting payment in untraceable cryptocurrency.
Before diving into the telemetry, it is vital to understand that residential proxies pose a multifaceted, dual-sided threat to organizations.
Risks to targeted organizations (inbound threats)
When attackers route their traffic through residential proxies, they look like everyday users, which neutralizes traditional security controls:
- Evasion of IP and geo controls: Residential proxies easily bypass region restrictions, per IP rate limits, and reputation lists tuned to block known IP ranges.
- Account takeovers (ATO) and credential stuffing: Threat actors combine credential stuffing tools with rotating residential IPs to test stolen passwords at scale, avoiding per IP lockouts.
- Financial and banking fraud: Attackers specifically seek out residential proxy services to access compromised banking and cryptocurrency accounts. By routing their connections through residential IPs that match the victim's geographic location, attackers can bypass strict anti-fraud systems and anomaly detection engines used by financial institutions to flag suspicious logins.
- Perimeter reconnaissance: Attackers use residential proxies to map enterprise perimeters, such as VPN login pages or authentication gateways, deliberately evading reputation based blocking while they inventory corporate access points.
- Malspam campaigns: Proxy networks are heavily abused to distribute spam and malspam emails, for example, botnets like Tofsee and SystemBC are known to act as proxies for large scale spam campaigns.
Risks to hosting organizations (internal/outbound threats)
When a device inside a corporate network acts as a proxy exit node, the organization effectively becomes the launchpad for malicious traffic. This happens through malware infections, but also via employees installing "passive income" proxyware or software SDKs in corporate devices that quietly sell network bandwidth:
- Reputation damage and blacklisting: If corporate IP space is inadvertently used to host proxy traffic, those addresses may become associated with fraudulent activity, leading to blacklisting by third-party partners and security detection systems.
- Increased attack surface: Hosting proxy traffic inside the perimeter introduces severe risks, enabling potential data exfiltration, credential abuse, and malicious relay operations from the inside out.
- Bypassing the perimeter: Work from home endpoints are particularly vulnerable. If an employee's device is co-opted as a proxy node while running legitimate enterprise VPN software, it provides threat actors with a direct, authenticated path past the corporate perimeter.
Quantifying the threat: 55 days of proxy telemetry
To map the residential proxy landscape, out of a list of +150 services, we intentionally scoped our research to target 30 proxy services known for their weak Know Your Customer (KYC) verification.1 Tracking this specifically selected infrastructure between 2026-01-19 and 2026-03-15 yielded unprecedented visibility into the residential proxy economy.
The sheer scale of the residential proxy ecosystem observed over that 55 day period is substantial:
- Total enumeration events: 989,686,388
- Global unique IPs : 53,346,368
- Last 30 days unique IPs: 36,842,328
- Peak 72-hour unique IPs: 13,747,519
- Peak 48-hour unique IPs: 11,390,896
- Peak 24-hour unique IPs: 8,443,091
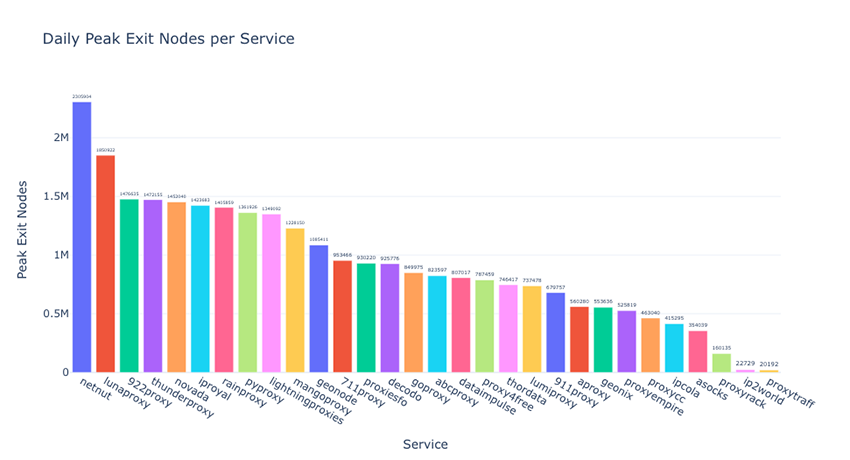
When analyzing the telemetry by service, we observed massive daily fluctuations as nodes rotated in and out of the active pools. At their daily peaks during our monitoring window, several top tier services demonstrated massive capacity, including Netnut (2.3M exit nodes), LunaProxy (1.85M exit nodes), 711Proxy (1.65M exit nodes), 922Proxy (1.64M exit nodes), ThunderProxy (1.47M exit nodes), and many others with more than 1M exit nodes. In this research we focus only on IPv4 nodes, extending it to IPv6 will increase the counter in millions.
Despite the common practice among proxy services to boost exit node pools exceeding 50 million for competitive advantage, the reality is that the number of simultaneously available nodes is substantially smaller. This actual count typically fluctuates between 10,000 and 2.5 million, varying by the specific service provider. The following chart illustrates the peak enumeration observed for each service within the scope of our study:
The overlap between proxies and malware
The most revealing outcome of our research lies in the behavioral context of these IPs. Residential proxy networks do not materialize out of thin air, they require a constant supply of host devices. While there are multiple tactics for a proxy service to source for exit nodes (users voluntarily install proxyware to sell their bandwidth, IP space renting, etc.) our data indicates that a vast portion of this infrastructure is built through systemic, unauthorized device compromise.
By correlating the identified proxy egress IP addresses against our proprietary compromised systems datasets, we identified a highly symbiotic relationship between commercial proxy networks and malicious botnets.
Over the 55 day observation period:
- Active Malware Infections: 15.49% of all distinct egress IPs (8,222,677) were simultaneously flagged for active malware infections.
- Riskware Presence: 12.78% of the egress IPs (6,785,708) exhibited activity flagged in with riskware.
It is critical to contextualize these metrics as strict lower bounds. We only record an overlap when a compromised device actively attempts to communicate with one of our sinkholed command and control (C2) domains in the same 24h period. Because we cannot observe compromised devices that are dormant, blocked by local firewalls, or successfully communicating with surviving upstream threat actor infrastructure, our telemetry only captures a fraction of the true infection base powering these networks.
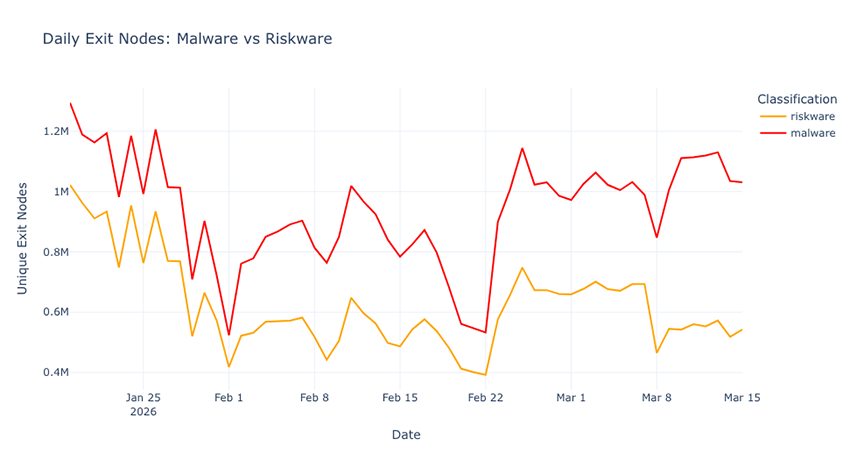
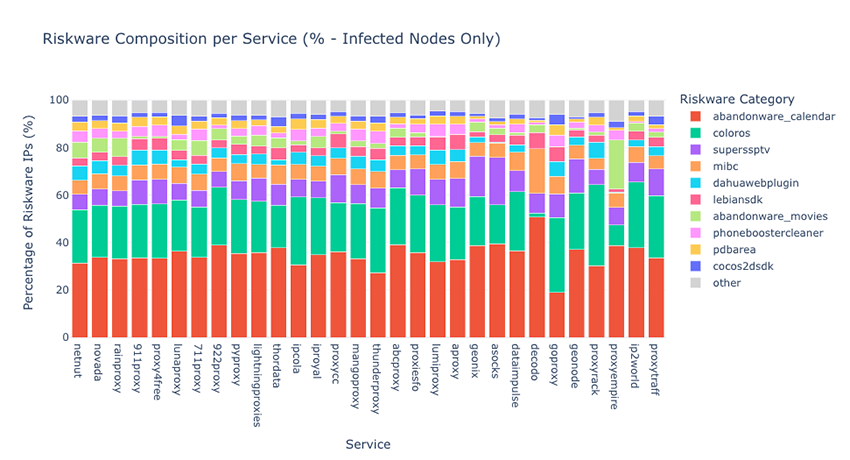
Analysis of the infected residential proxy nodes revealed persistent co-infections involving known malware and riskware. Specifically, devices acting as proxy exit nodes were found to harbor families such as Vo1d, Badbox, RootSTV (also known as Pandoraspear), OpenCandy, Gamarue, and M0vy. A significant overlap was also observed between systems infected with malware and those containing riskware.
This overlap between exit nodes that are also compromised by malware and riskware represents a lower bound; the actual infection rate is likely much higher. Our results are limited to the correlations between our proxy enumeration and the malware and riskware observations collected in our sinkholes. Consequently, these findings do not reflect any proxy malware for which we lack telemetry. Furthermore, an observed malware may not be actively running as a proxy bot itself, but could indicate the presence of other malware operating as a proxy bot on the system.
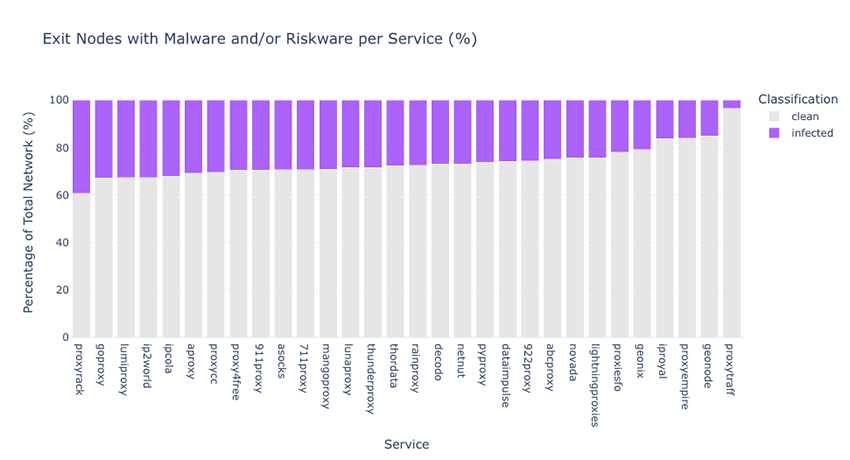
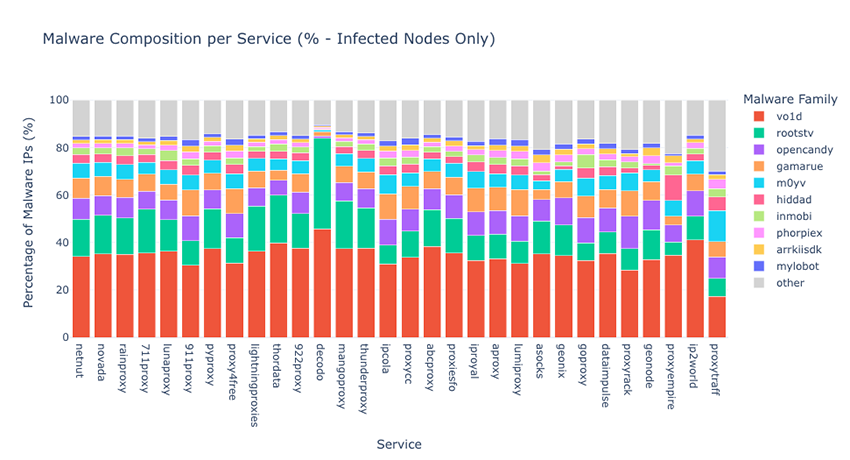
Observations of riskware serve as a significant indicator that a device is at an elevated risk of compromise. When correlating these observations with our proxy enumeration, we found that two categories, Abandonware_Calendar and ColorOS, accounted for the highest counts.
The escalating war on proxy networks
The correlation between proxies and malware is not a new phenomenon, and recent years have seen an escalation in coordinated takedowns targeting this type of infrastructure from both public and private cooperations. Key operational disruptions include:
- October 2023: Human security disrupts BADBOX/PEACHPIT
- Disruption of PEACHPIT ad fraud network related to BADBOX and Triada malware
- Firmware backdoor on low-cost, off-brand Android devices (streaming boxes, tablets, smartphones) during manufacturing or distribution, making them arrive "primed for fraud."
- The scheme compromised over 74k devices (and millions more in later iterations like BADBOX 2.0), turning them into proxy nodes and tools for fake social media accounts.
- December 2023: Socks5systemz disruption
- Bitsight led a disruption of a Socks5systemz botnet with more than 250k compromised systems that was used by ProxyAM residential proxy service.
- Taking over C2 domains and releasing IoCs degraded the botnet’s ability to supply “clean” residential IP addresses to criminals.
- In 2024, the service underwent a rebranding initiative and started to source for bots with other proxy providers because its customer base was moving to competing suppliers.
- May 2024: 911 S5 botnet disruption
- The FBI successfully dismantled the botnet infrastructure, halting an operation that had generated approximately $99 million in revenue.
- November 2024: NSOCKS takedown
- Industry led disruption targeted the Ngioweb botnet, the backbone of NSOCKS, VN5Socks, and Shopsocks5 proxy services
- Blocking C2 nodes and releasing IoCs degraded the botnet’s ability to supply “clean” residential IP addresses to criminals.
- July 2025: BadBox 2.0 disruption
- A coordinated effort by Google, Human Security and others (2023-2025) significantly reduced BadBox's scale, increased detectability, and forced operator change through threat exposure, platform enforcement, supply chain intervention, and monetisation pressure.
- Late 2023: BadBox, an Android supply chain malware pre-installed on TV boxes for residential proxy monetisation, was publicly exposed.
- 2024: Google's platform actions (Play Protect, certification limits) reduced its stealth and monetisation within Android.
- March/June 2025: Supply chain disruptions removed affected devices; network operators blocked/sinkholed C2.
- Mid-2025: Monetisation pressure on proxy services using BadBox nodes (e.g., IPidea) further degraded profitability.
- January 2026: IPIDEA disruption
- Google intensified its pressure on this ecosystem after the Badbox and Badbox 2.0 disruptions by taking down IPIDEA. This extensive proxy network utilized Badbox, Vo1d, and other malware, ultimately assisting over 550 threat groups in conducting cybercrime.
- March 2026: Dopellganger disruption
- Lumen Black Lotus team as discovered and taken actions to disrupt a new malware called KadNap that was used to support the proxy service Dopellganger
- March 2026: Disruption of AVRecon/SocksEscort
- A joint international law enforcement operation recently dismantled the SocksEscort service, a residential proxy service that used AVrecon malware to create a botnet of 369k routers and IoT devices globally and monetize traffic of infected systems since 2020.
Despite ongoing actions in recent years that aim to disrupt criminal activity, the demand in this massive market is inevitably absorbed by a new service when an existing one is shut down.
Case study: The IPIDEA cluster
To truly understand the collection potential and fidelity of our dataset, we closely analyzed the IPIDEA proxy ecosystem. Recently targeted in a major disruption effort by Google and industry partners, IPIDEA operated as one of the world's largest residential proxy networks. By routing traffic through millions of compromised consumer devices worldwide, the network allowed various threat actors to mask their operations behind everyday residential IP addresses.
Significantly, the IPIDEA service extends beyond a typical proxy broker. Our analysis suggests that rather than independently acquiring these nodes, the threat actors running the IPIDEA conglomerate of proxy services maintain deep affiliations with the specific threat groups operating the underlying botnet infrastructure. Through strategic partnerships with the operators of the Vo1d, Badbox, and RootSTV/Pandoraspear malware families, IPIDEA secures a massive, continuous pipeline of infected devices to reliably fuel their commercial exit node network.
The IPIDEA network encompasses several distinct proxy service brands marketed to typical customers. These brands include: 360 Proxy, 922 Proxy, ABC Proxy, Cherry Proxy, Door VPN, Galleon VPN, IP2World, Ipidea, Luna Proxy, PIA S5 Proxy, PY Proxy, Radish VPN, and Tab Proxy. For the purpose of this study, we selected the following brands from this group: 922proxy, ABCproxy, IP2World, Lunaproxy, and pyproxy.
When querying the malware correlation across this conglomerate's footprint, our sinkhole telemetry revealed a consistent 15–26% baseline overlap with the Vo1d, Badbox, and RootSTV/Pandoraspear payloads. When expanding our view to the entire global residential proxy ecosystem over the same 55-day window, our sinkholes revealed a consistent 14–21% baseline overlap across all proxy services and all tracked malware families.
While our direct observations establish a firm baseline, accounting for the previously noted constraints of sinkhole telemetry leads us to assess with high confidence that the true infection rate powering this specific proxy conglomerate realistically approaches 50%. This assessment is heavily supported by the scale of the underlying botnets: our internal sinkhole telemetry registers over 3 million unique infections daily for malware related to this cluster. Even when accounting for overlapping infections, this provides the threat operators with a massive, globally distributed pool of compromised devices. This rotating supply is more than capable of easily sustaining a 50% infection footprint across the 2.8 million daily active nodes we observed peaking in the IPIDEA downstream cluster.
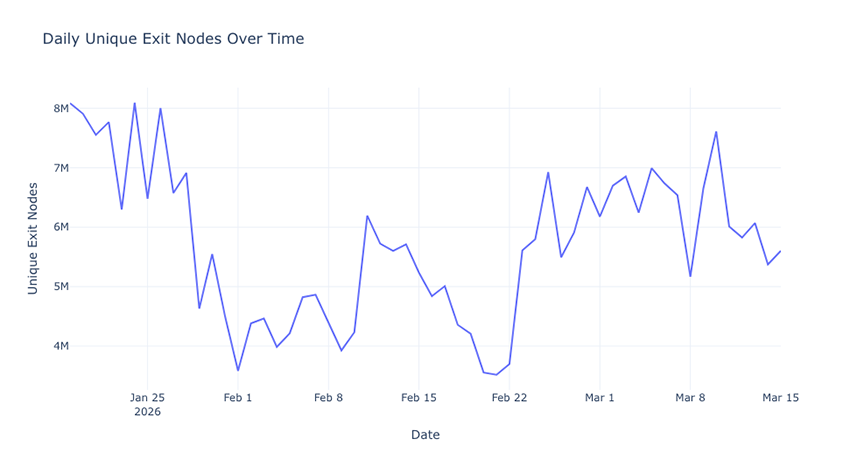
The sheer scale of the IPIDEA conglomerate's market dominance, was empirically validated during the Google Threat Intelligence Group takedown of IPIDEA in late January 2026.
Our telemetry captured the exact moment the threat actor's frontend infrastructure fractured.
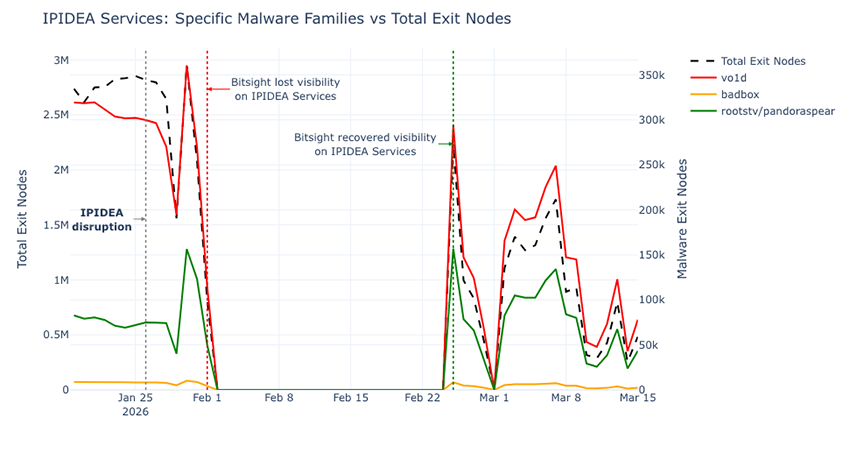
Prior to the disruption, our data revealed just how heavily the global proxy market relied on this single, vertically integrated provider. On January 25, just one day before the takedown, we observed 302,238 Vo1d infections serving as exit nodes through IPIDEA operated infrastructure. When compared against our global telemetry for that same day, 55% of the entire global Vo1d botnet was actively monetized through IPIDEA’s visible network. RootSTV showed a similarly massive footprint, with IPIDEA routing 33% of its global nodes.
Infrastructure resilience
When Google executed the disruption against IPIDEA on January 26, it left a massive crater in the visible proxy ecosystem. By February 1, our direct visibility into their services dropped entirely, marking the beginning of a 24 day telemetry blackout for this specific cluster.
However, it is critical to contextualize the exact nature of this blackout. Our assessment is that the Google disruption primarily impacted the proxy provider's frontend infrastructure and retail storefronts, rather than destroying the threat actor's backend botnet operations. Our visibility into the service dropped to zero not because the exit nodes vanished, but because our threat intelligence collection accounts exhausted their bandwidth allocations. Because Google successfully took the IPIDEA’s websites offline, customers were unable to log in, top-up balances or renew subscription packages. While we were locked out of the collection accounts, our global sinkhole telemetry combined with our visibility into other, non-IPIDEA proxy services told a completely different story about the threat actor's resilience.
Because we assess that the IPIDEA operators are also affiliates with Vo1d, Badbox, and RootSTV/Pandoraspear botnets, they operate as a wholesale provider. When the websites and related frontend infrastructure went down, the operators simply shifted the routing of their infected victims to their other third party wholesale proxy clients.
During our 24 day IPIDEA blackout, the malware remained highly active across the rest of the proxy ecosystem. On February 15, smack in the middle of the IPIDEA disruption, we observed over 5.2 million total exit nodes operating across other proxy services. Within that non-IPIDEA traffic, the threat actors were actively monetizing at least 429,687 Vo1d infections and 253,775 RootSTV infections.
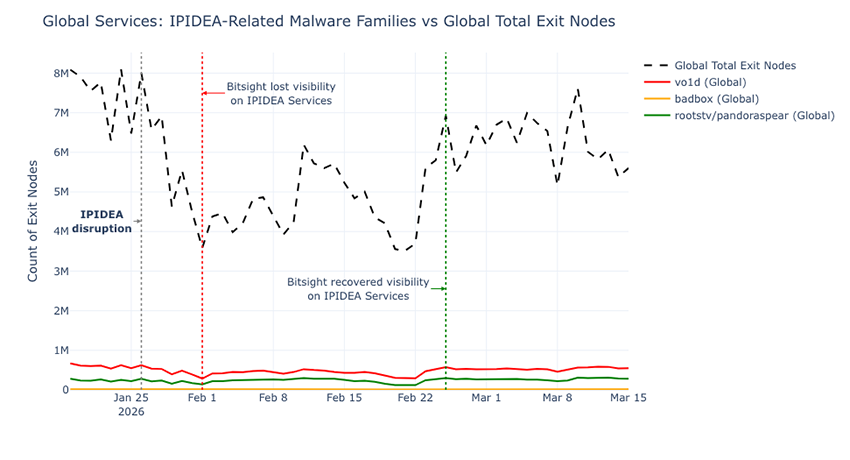
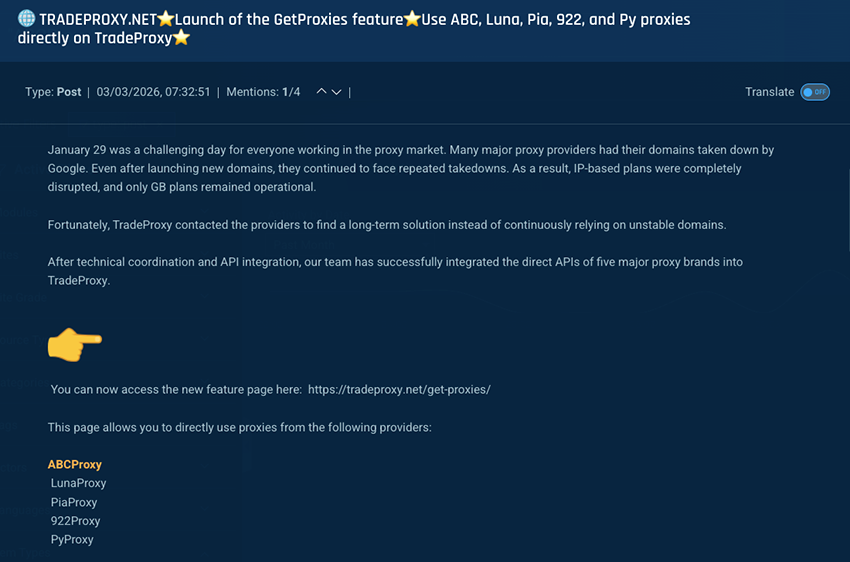
A week after the takedown in early February, proxy resellers were spotted across several underground forums actively advertising access to IPIDEA related services, indicating that the broader market was desperate for the conglomerate's infrastructure to return:
This shows that while the takedown successfully severed the *routing layer* that turned these devices into commercial exit nodes for IPIDEA's retail brands and B2B clients, the threat actor retained control of the compromised devices, keeping them dormant or routing them through alternative, surviving channels while they rebuilt their backend.
On or about February 25, Bitsight recovered visibility over IPIDEA’s operated services. The data did not show a slow, organic rebuild of a destroyed botnet. Instead, the numbers spiked instantaneously back to pre-disruption levels, registering 2.24 million total exit nodes and nearly 300,000 Vo1d infections on the very first day of recovery.
Conclusion
Our dataset proves that the residential proxy economy is heavily subsidized by the malware ecosystem. With a baseline of 20% of proxy exit nodes actively communicating with sinkholes, and realistic infection rates likely much higher, defenders must treat anonymized residential traffic not just as a potential evasion tactic, but as a direct extension of botnet infrastructure. Relying purely on static IP reputation is no longer viable when the attack nodes are dynamically generated from millions of infected hosts worldwide.
For defenders, this paradigm shift demands a modernized approach to network security and threat modeling. When threat actors can seamlessly blend into organic consumer traffic using continuous proxy rotation, organizations must adapt by moving beyond legacy, threshold-based blocking.
To effectively mitigate this dual sided threat, security teams should focus on the following strategies:
- Shift to behavioral correlation: Since individual IPs rotate too quickly for static lists to catch them, defenders must detect the rotation pattern itself. Alert on sequential, single touch interactions where multiple distinct residential IPs perform identical, low volume actions against authentication, API, or checkout endpoints.
- Layer adaptive controls: Establish risk tiers for your critical assets. When traffic originating from anonymizing infrastructure targets sensitive endpoints, introduce adaptive friction, such as step-up authentication, CAPTCHAs, or MFA, rather than relying on outright blocking, which can inadvertently impact legitimate customers.
- Audit internal outbound traffic: To prevent your own corporate endpoints from being weaponized as proxy nodes, enforce strict egress filtering. Ensure IoT devices cannot initiate unauthorized outbound traffic to stop botnet propagation chains, and monitor for unexpected VPN client signatures that may expose compromised work from home devices.
- Leverage Continuous Proxy Observability: The proxy economy moves too fast for traditional, periodic threat intelligence updates. Security operations must enrich session data with high-fidelity, real-time intelligence capable of tracking dynamic proxy pools, identifying transient nodes, and correlating them to active malware families as they emerge.
Ultimately, neutralizing the threat of residential proxies requires illuminating the infrastructure that powers them. By integrating continuous proxy enumeration and malware correlation into defense-in-depth strategies, organizations can strip threat actors of their most valuable asset: anonymity.
For other researchers and law enforcement, cooperation is key to tackle this ongoing threat and to keep up with the escalating war on proxy networks. Reach out!
1Most IaaS providers have KYC policies to ensure that their services are not used for malicious purposes.



