New high-severity vulnerability (CVE-2023-29552) discovered in the Service Location Protocol (SLP)

Editor's Note: On November 8, 2023, CISA added CVE-2023-29552 to the Known Exploited Vulnerabilities list.
Researchers from Bitsight and Curesec have jointly discovered a high-severity vulnerability — tracked as CVE-2023-29552 — in the Service Location Protocol (SLP), a legacy Internet protocol. Attackers exploiting this vulnerability could leverage vulnerable instances to launch massive Denial-of-Service (DoS) amplification attacks with a factor as high as 2200 times, potentially making it one of the largest amplification attacks ever reported. In February 2023, we identified over 2,000 global organizations and over 54,000 SLP instances — including VMware ESXi Hypervisor, Konica Minolta printers, Planex Routers, IBM Integrated Management Module (IMM), SMC IPMI, and others — that attackers could potentially leverage to launch DoS attacks on unsuspecting organizations around the world.
Given the criticality of the vulnerability and the potential consequences resulting from exploitation, Bitsight coordinated public disclosure efforts with the U.S. Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA) and impacted organizations. Bitsight also engaged with denial of service teams at major IT service management companies to help with remediation. CISA conducted extensive outreach to potentially impacted vendors.
- Technical details regarding CVE-2023-29552 are available here.
- The CISA Current Activity Alert is available here.

What is the Service Location Protocol (SLP)?
SLP is a protocol that was created in 1997 through RFC 2165 to provide a dynamic configuration mechanism for applications in local area networks. SLP allows systems on a network to find each other and communicate with each other. It does this by using a directory of available services, which can include things like printers, file servers, and other network resources. SLP works by having a system register itself with a directory agent, which then makes that system's services available to other systems on the network. Daemons providing SLP are bound to the default port 427, both UDP and TCP.
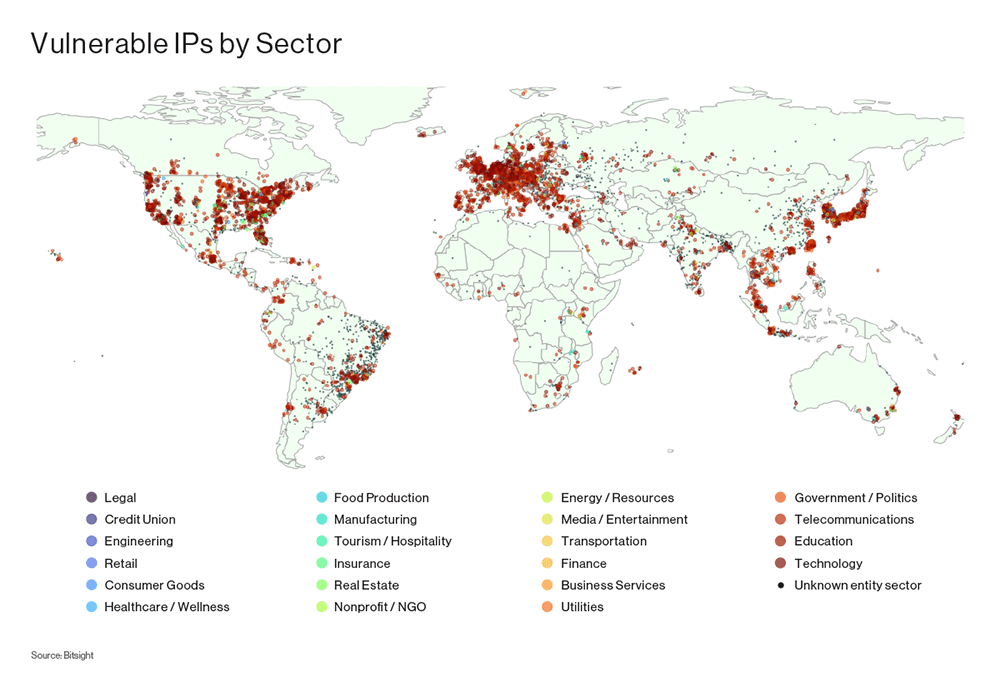
SLP was not intended to be made available to the public Internet. According to RFC 2165, "Service Location provides a dynamic configuration mechanism for applications in local area networks. It is not a global resolution system for the entire Internet; rather, it is intended to serve enterprise networks with shared services." However, the protocol has been found in a variety of instances connected to the Internet. A recent internet-wide scan revealed more than 54,000 SLP-speaking instances online, belonging to organizations across many sectors and geographies.
Researchers have identified security vulnerabilities affecting implementations of SLP for many years. VMware has issued multiple advisories warning users about vulnerabilities affecting SLP in their ESXi products and disabled SLP by default in ESXi software releases since 2021. In recent months, ransomware gangs have leveraged an issue in SLP implementations in campaigns targeting vulnerable organizations. In February 2023, VMware warned customers to install the latest security updates and disable OpenSLP service because it was being targeted in a large-scale campaign of ransomware attacks against internet-exposed and vulnerable ESXi servers.
What vulnerability was discovered?
Researchers from Bitsight and Curesec jointly discovered CVE-2023-29552 (CVSS 7.5). If exploited, CVE-2023-29552 allows an attacker to leverage vulnerable instances to launch a DoS attack — sending massive amounts of traffic to a victim — via a reflection amplification attack.
DoS attacks have made headlines in recent years, causing significant financial, reputational, and operational harm. With attacks predicted to double from 2018 to the end of 2023, organizations continue to fall victim to service disruptions. In fact, small to medium-sized businesses (SMBs) spend an average of $120,000 as a result of a DoS attack, while larger organizations may face larger financial losses due to relatively higher costs of disruption. Large, multinational enterprises are not immune to these attacks – Amazon Web Services (AWS), GitHub, and even nation states have fallen victim to DoS attacks.
How does a typical reflection DoS amplification attack work?
In a typical reflection DoS amplification attack, the attacker usually sends small requests to a server with a spoofed source IP address that corresponds to the victim's IP address. The server then replies to the victim's IP address, sending much larger responses than the requests, generating large amounts of traffic to the victim’s system. The attacker is simply tricking systems on the Internet — not necessarily owned by the target — to send mass amounts of traffic to the target.
What does a reflection DoS amplification attack leveraging CVE-2023-29552 look like?
Reflection coupled with service registration significantly amplifies the amount of traffic sent to the victim. The typical reply packet size from an SLP server is between 48 and 350 bytes. Assuming a 29 byte request, the amplification factor — or the ratio of reply to request magnitudes — is roughly between 1.6X and 12X in this situation. However, SLP allows an unauthenticated user to register arbitrary new services, meaning an attacker can manipulate both the content and the size of the server reply, resulting in a maximum amplification factor of over 2200X due to the roughly 65,000 byte response given a 29 byte request. This extremely high amplification factor allows for an under-resourced threat actor to have a significant impact on a targeted network and/or server via a reflection DoS amplification attack.
Typical reflection DoS amplification attack:
- Step 1: The attacker finds an SLP server on UDP port 427.
- Step 2: The attacker spoofs a request to that service with the victim's IP as the origin.
- Step 3: The attacker repeats step two as long as the attack is ongoing.
Client request:
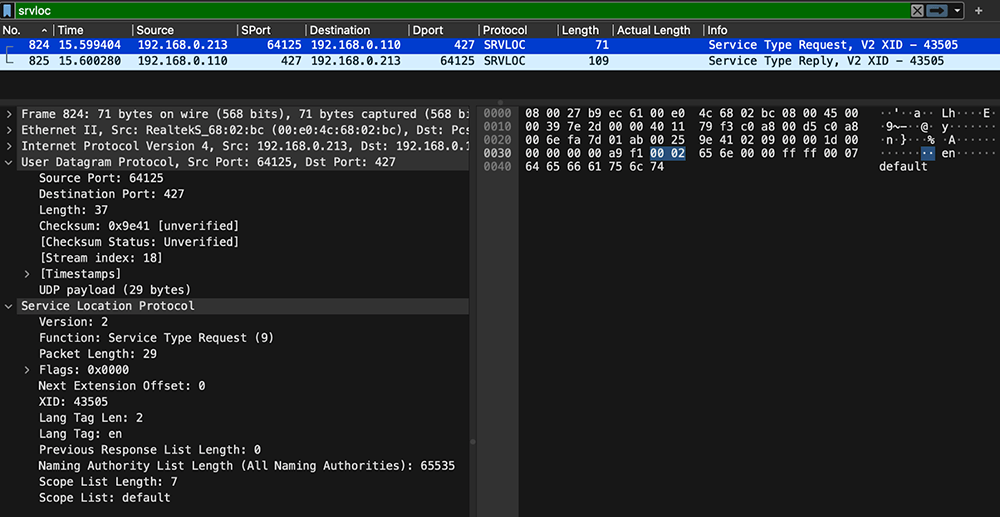
Server reply:
During this attack, the requests made and the response differ in size. The bigger the response in relation to the request, the higher the amplification factor. With SLP, it is possible to forge Service Type Request messages, requesting all naming authorities and the default scope. This makes the server reply with all service type lists it provides.
Amplification factor: between 1.6X and 12X.
Reflection DoS amplification attack leveraging CVE-2023-29552:
- Step 1: The attacker finds an SLP server on UDP port 427.
- Step 2: The attacker registers services until SLP denies more entries..
- Step 3: The attacker spoofs a request to that service with the victim's IP as the origin.
- Step 4: The attacker repeats step three as long as the attack is ongoing.
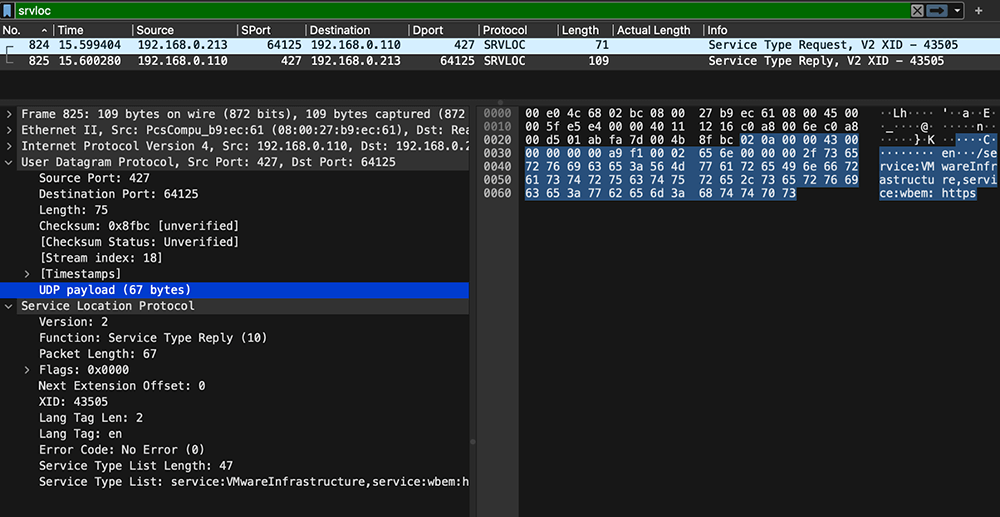
The setup phase of the attack only needs to happen once to fill the server response buffer. The attacker can manipulate both the content and size of the server reply by registering arbitrary new services. During the attack, the interaction between the attacker and the server would look like a service registration loop until the server buffer is full, followed by arbitrary spoofed requests.
Below is the Wireshark log capturing the complete communication between an attacker and a server, where the attacker is attempting to fill the response buffer. The registration requests are highlighted in green, and the server replies are highlighted in red. As each request is made, it is important to observe that the reassembled UDP packets are increasing in size. Depending on the software and/or system being used, the size of the reply can potentially reach the practical limit of a single UDP packet, which is typically 65,536 bytes.
Amplification factor: maximum of approximately 2200X. By comparison, the 2020 DoS attack on AWS was executed with a similar reflection amplification attack using CLDAP, relying on a maximum amplification factor of 55X.
To see the amplification in action, see the video below:
What products are affected?
CVE-2023-29552 affects all SLP implementations tested by Bitsight and Curesec. We detected more than 54,000 SLP-speaking instances and more than 670 different product types, including VMware ESXi Hypervisor, Konica Minolta printers, Planex Routers, IBM Integrated Management Module (IMM), SMC IPMI, and many others.
There are many SLP speaking instances which makes it a challenge to exhaustively fingerprint all instances affected by the issue. There are some SLP implementations that do not allow for registration of new services, leaving the amplification factor to a smaller fixed value. However, most of the implementations that we have seen and tested do allow and are vulnerable to registration of spoofed services, thus enabling the massive 2200X amplification factor.
Organizational impact is broad
Over 2,000 organizations were identified as having vulnerable instances. Attackers could potentially leverage these vulnerable instances to launch a DoS attack targeting the system owners and/or other organizations.
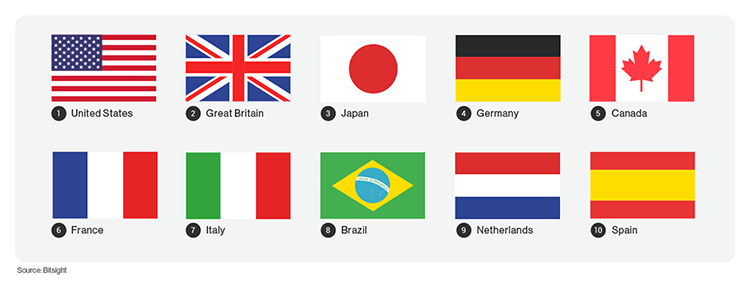
The top 10 countries with the most organizations having vulnerable instances are:
Fortune 1000 organizations with vulnerable instances
Many Fortune 1000 organizations were identified as having vulnerable instances. Fortune 1000 impact spans many sectors, including finance, insurance, technology, telecommunications, manufacturing, healthcare, hospitality, and transportation.
How to protect against CVE-2023-29552
To protect against CVE-2023-29552, SLP should be disabled on all systems running on untrusted networks, like those directly connected to the Internet. If that is not possible, then firewalls should be configured to filter traffic on UDP and TCP port 427. This will prevent external attackers from accessing the SLP service.
Take action now
CVE-2023-29552 is a threat that can potentially impact business continuity and result in financial loss, even if an attacker has limited resources. Organizations must implement appropriate security measures to safeguard their networks and servers from being used in such attacks. One effective way to protect against SLP vulnerabilities is by implementing robust network security controls such as firewalls.
It is equally important to enforce strong authentication and access controls, allowing only authorized users to access the correct network resources, with access being closely monitored and audited. Organizations should also have an incident response plan in place that clearly outlines procedures for mitigating SLP vulnerabilities, as well as procedures for communicating with users and stakeholders in case of an incident.
Implementing strong security measures and access controls can reduce the risk of falling victim or unwillingly participating in these types of attacks, while incident response plans can mitigate the effects of such an attack.




