New! The Security Ratings report is now the Executive Report. Request your report to see enhanced analysis such as your rating, likelihood of ransomware incidents, and likelihood of data breach incidents.
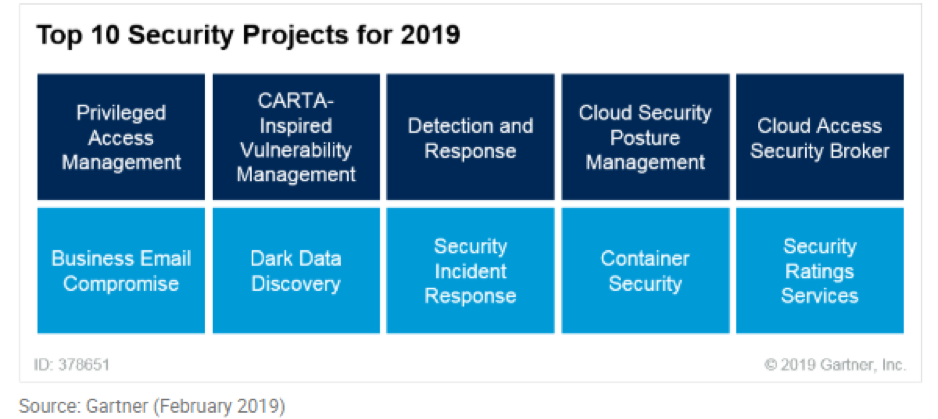
Gartner Names Security Ratings a Top 10 Security Project for 2019
Tags:

Just a few weeks ago, Gartner released their list of “Top 10 Security Projects for 2019”, and named security ratings services as a business imperative.
Gartner stated, “ As digital transformation matures, the risks associated with complex ecosystems become an integral part of the business. It is no longer just about the internal security and risk posture of an organization, but about the posture of suppliers, regulators, customers, business partners and platforms.”
They went on to say, “as a result, SRM [security and risk management] leaders should leverage security rating services as an additional data point to provide continuous, independent scoring for their overall digital ecosystem — public-facing assets and otherwise.”
In today’s expanding business ecosystem, managing third-party risk is increasingly critical to protecting companies’ sensitive data. With new threats emerging daily and companies continuing to outsource, third-party risk management is an issue that will only grow in affecting organizations and their business partners.
The third-party risk gap is growing, and while current approaches to the problem (like questionnaires, audits and penetration tests) are helpful, they typically only provide a moment-in-time snapshot of security risk. To proactively mitigate risk, organizations need automated tools that continuously measure and monitor the security performance of third parties. To make decisions in a timely manner, companies need to be able to access and aggregate data about their third parties quickly and efficiently. The speed at which organizations can comprehensively assess third parties is critical to the success of any third-party risk management (TPRM) program, and ultimately, the value delivered to the business.
When companies are able to make critical third-party risk management decisions rapidly, this enables them to drive business value and partner better with the business. Quicker third-party assessments and selection means less downtime. This allows them faster turnaround and more productivity when it comes to managing hundreds and sometimes thousands of third parties that affect their business’ bottom line.

Security ratings enable organizations to continuously monitor their entire third-party ecosystem and quickly understand the health of their third-party portfolio and potential third parties. Ratings also allow them to manage their organization’s cybersecurity performance — and security and risk leaders must take a risk-based, outcome-driven approach. They can do so through targeted measurement, continuous monitoring, and detailed planning and forecasting in an effort to measurably reduce cyber risk. Continuously monitoring an organization’s security posture is just the start in building a mature security performance management program. Businesses need to go beyond continuous monitoring to really be effective — there needs to be a process of continuous improvement.
Security ratings also allow users to set customizable alerts not only for their own security performance but also that match their company’s risk tolerance for different groups of third parties. If there are any changes that cross thresholds, the user can see the reason behind that change and then reach out to the third parties quickly and work with them to resolve the issue. Organizations can leverage alerts throughout the entire third party lifecycle — from pre-screening potential third parties to continuous monitoring, and contract review. If the performance of a particular third party does not improve over time, contracts and relationships can be re-evaluated accordingly.
When it comes to third-party risk management, the ability to have continuous insight into the risk associated with third parties and make decisions quickly and efficiently is critical to a successful and healthy program. With the ability to drill down into the security details used to generate an organization’s rating, companies can work more effectively by holding data-driven conversations with third parties about their security posture as well as continue to work towards keeping their network secure.


