Analyzing Utilities Sector Cybersecurity Performance
Tags:

With economic sanctions being levied by the US against Iran and a trade war heating up with China, some security experts are cautioning that attacks targeting US critical infrastructure may be inevitable. Are electric utilities prepared to defend themselves and their facilities against these attacks?
According to a 2018 survey by KPMG, 48% of power and utilities CEOs said they believe a cyber attack is "inevitable.” Electric grid operability and reliability are the biggest challenges as cyberattacks on organizations and their third parties continue to increase — in fact, according to the Department of Homeland Security, Russian hackers obtained access to the U.S. electric grid in 2017.
Are Utilities Up to the Challenge?
Bitsight’s data science team took a closer look at the security performance of organizations in the utilities sector (all data as of June 1, 2019). Based on the terabytes of data collected by Bitsight about security performance, we observe that:
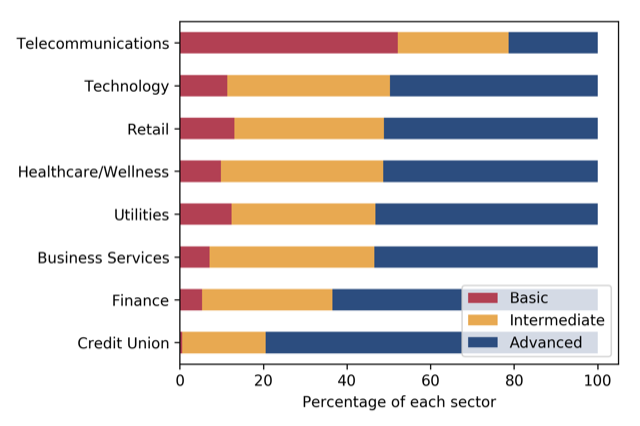
Over 53% of the companies in the Utilities industry have a Bitsight Security Rating in the advanced category (740 and above). This is in line with the Healthcare and the Business Services sectors, although Utilities has more companies with ratings in the Basic category (below 640). As a sector, Utilities falls below the strongest sector performers, including Finance and Credit Union.
.png)
- Diligence performance metrics show 51% of utility organizations with no vulnerable services (see Exhibit C) and 45% with no out-of-date systems (see Exhibit D). The presence of out-of-date or unsupported devices can lead to system failure, business disruption, or allow attackers to gain access to gain system access. As indicated here, the significant number of organizations that still have risky services and out-of-date systems presents a real concern.
- This sector has some of the highest adoption of email validation (see Exhibit E) among all of the sectors tracked by Bitsight, with almost 70% of companies using either SPF or DKIM across all of their email servers. SPF and DKIM, two authentications that validate email is not forged, allow mail readers can check if the mail was really sent from the “From” domain (Gmail does this), which helps to spot spam and phishing emails.
- Nearly 1 out of 10 utilities companies had one or more malware infections within the last three months (see Exhibit B). Bitsight research has shown that a higher rate of infection correlates with a higher likelihood of a breach. More specifically, companies with a Bitsight botnet grade of B or lower were more than twice as likely to experience a publicly disclosed data breach.
- Nearly 5% of utilities are still exposed to the recently announced — and potentially catastrophic — BlueKeep vulnerability. In May 2019, Microsoft issued a warning about BlueKeep (CVE-2019-0708), a vulnerability affecting Remote Desktop Services Protocol (RDP), a component common in most versions of Microsoft Windows that allows remote access to its graphical interface. This vulnerability, if exploited by an external attacker, will lead to full system compromise, without requiring any form of authentication or user interaction. According to Bitsight research, the electric utilities sector is the fourth worst performing sector when it comes to patching this critical vulnerability.
The Electric Utilities Supply Chain: A Weak Link?
While many electric utilities are working to address security risks within their own environment, they must not ignore the significant risk that comes from their third-party business ecosystem and supply chain partners. With new regulations in place for third-party supply chain risk management, and severe fines available for violations of CIP regulations or third party breaches, utilities need to ensure their suppliers and vendors are taking cybersecurity as seriously as they are.
For example, a 2018 breach on a smart regulator valve nearly destroyed a Saudi Arabian chemical plant — perfectly illustrating how significant threats can come from seemingly harmless third parties. Cyber risk to the third party supply chain has become such a serious concern that the Federal Energy Regulatory Commission (FERC) in 2018 passed new regulations requiring utilities to develop comprehensive cyber supply chain risk management programs. Regulators have been focused on third-party risk to the utilities industry for years — in 2018, a major utility was fined $2.7 million for a third party breach. With so much pressure from regulators on this issue, utilities must focus their efforts on building cost-effective, risk-reducing third-party cyber risk management programs.
Objective Security Ratings Contribute to Strong Cybersecurity Posture
Utilities need an effective means to gain visibility into the security posture of their own organization, as well as their third-party ecosystem partners and technology providers to reduce the risk and impact of a cyber incident. Security ratings deliver a continuous, data-driven measure of security performance, giving utilities companies the ability to compare performance with industry peers and report progress over time to executives and the Board. Security ratings also allow them to continuously monitor the cybersecurity performance of their third parties, allowing them to understand and address risks to critical suppliers.
Ultimately, security ratings allow the electric utilities industry — one that is essential to critical national infrastructure — to accurately assess risk across their business ecosystem.
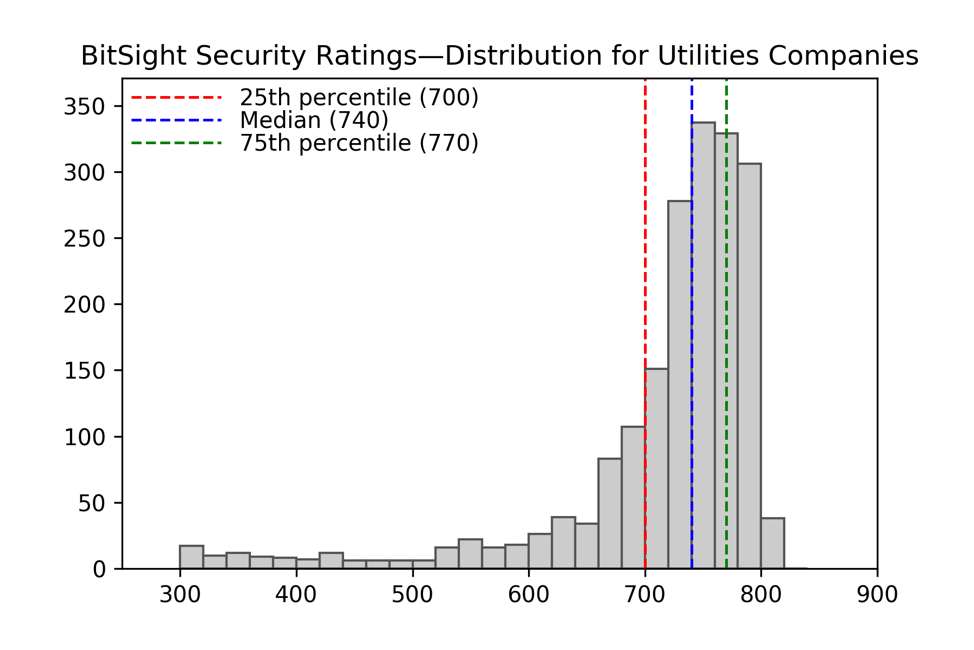
Exhibit A
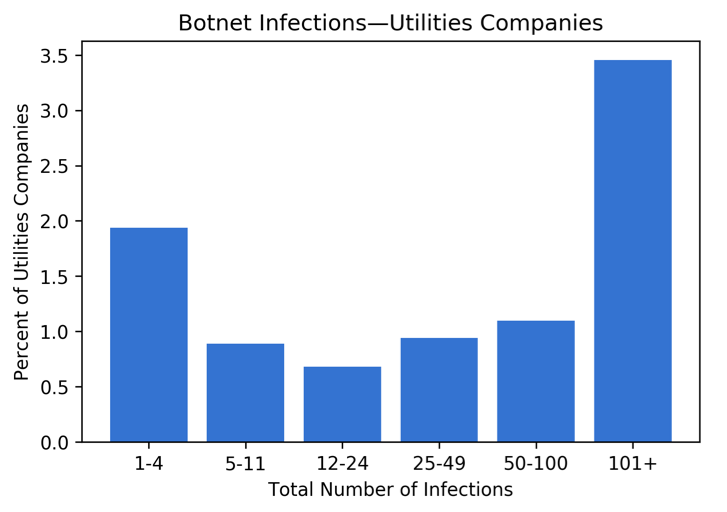
Exhibit B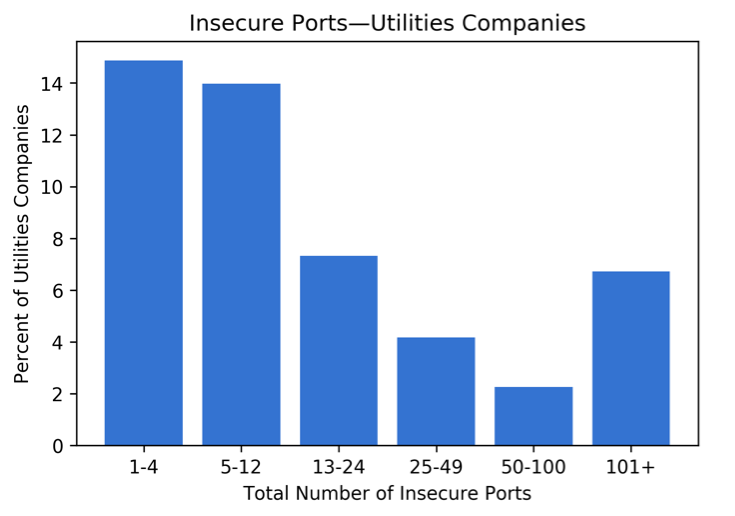
Exhibit C
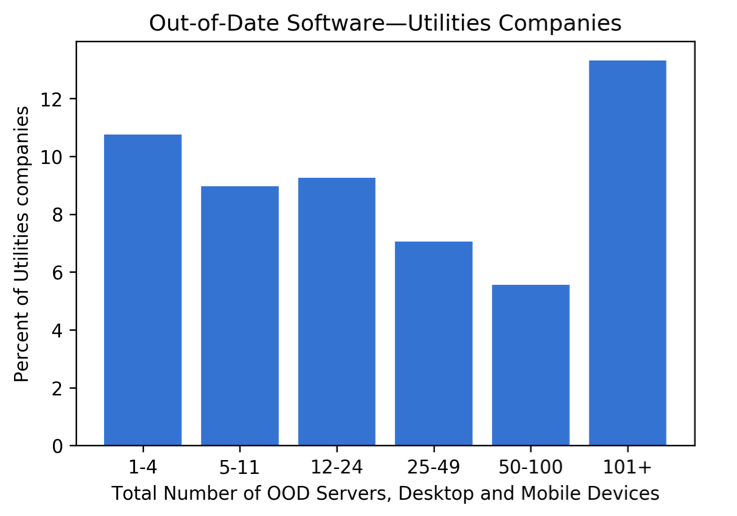
Exhibit D
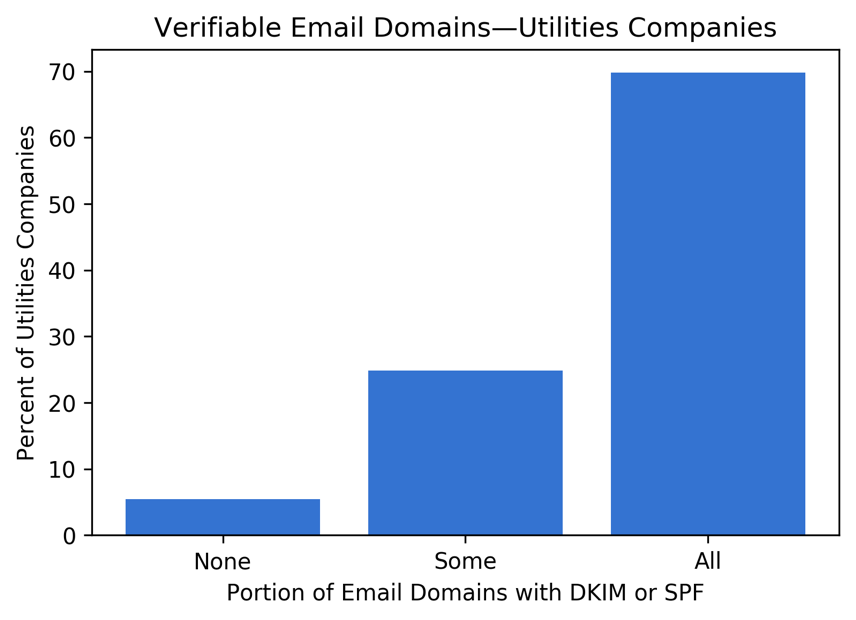
Exhibit E