Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Insights blog.
Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Slicing through CISA’s KEV Catalog

Slicing through CISA’s KEV Catalog
Dive into the critical insights of CISA's Known Exploited Vulnerabilities (KEV) Catalog with Bitsight’s latest blog! Discover how KEVs, which signal urgent cybersecurity risks, are being tracked and mitigated across industries. Learn why addressing these vulnerabilities quickly is vital and how it impacts organizational security.
Within the Bitsight Security Ratings platform, we prioritize features that help organizations both identify and manage risks across their own networks and the networks of their third parties. Bitsight now enables users to identify organizations who are potentially vulnerable to VPNFilter malware or Oracle’s WebLogic server problems.

If you’ve done your homework as a cybersecurity professional, then you know that third-party vendors with substandard security controls and processes could be putting your organization at risk.

In a world where business is increasingly conducted on mobile devices, it is imperative that organizations offer mobile applications to serve their customer base. In fact, for many businesses, mobile applications are one of the primary channels used to interact with customers and to sell products and services.

As advances in cloud computing and managed services have made IT operations more streamlined, the focus of IT leaders has shifted to improving efficiency, agility, and risk management. Managing risk, in particular, has become an even more central concern.

Mitigating risk is an essential business function that should cover obvious domains — like financial risk — but also include reputational, strategic, and operational risks.

With outsourcing continuing to rise, third party cyber risk management has become a pressing issue for organizations worldwide. Yet, many firms across the globe are approaching this challenge differently.
At a recent Bitsight Roadshow, a customer with an advanced third party risk management program declared “assessments are not risk reduction.” The statement was not meant to convey that assessments are useless for third party risk; rather, that assessments themselves don’t inherently drive risk down.

You’re responsible for information security at your organization. You dedicate yourself every day to identifying weaknesses and patching vulnerabilities in your network. You’ve developed policies to protect employees from cyber threats. You’ve designed procedures for responding in the event of a data breach, and you’ve practiced those procedures with company stakeholders.

In March 2017, the New York Department of Financial Services (NYDFS) cybersecurity regulations—known as 23 NYCRR Part 500—went into effect. According to the regulation, “any Person operating under or required to operate under a license, registration, charter, certificate, permit, accreditation or similar authorization under the Banking Law, the Insurance Law or the Financial Services Law” is considered a covered entity and must comply.

Compliance, at its core, is a legal responsibility. It is defined as “act or process of doing what you have been asked or ordered to do.” Creating a successful vendor compliance program isn’t as simple as asking third parties to comply with your security requests or pestering them to answer your security risk assessment questions.

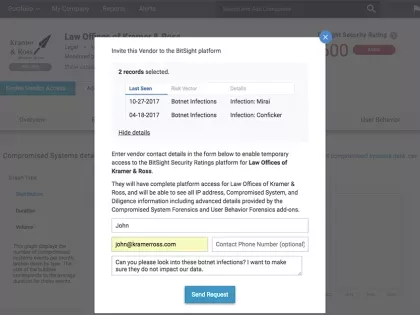
In today’s business landscape, it’s critical to manage the risk that your vendors, or third parties, can pose to your business — and it’s not always the easiest task. It requires that organizations not only have the ability to continuously monitor and identify new risk, but also the ability to work with their vendors to fix security issues quickly. Getting to risk reduction rapidly means that both organizations are communicating effectively, using data and evidence rather than conjecture to make progress.

You can’t go more than a few weeks (or sometimes a few days) without hearing about yet another company whose data was compromised after hackers gained access through a third-party vendor. These attacks show that it’s no longer enough to secure only your own network from cyber attacks—you have to ensure your vendor networks are secured as well.

In today’s expanding business ecosystem, managing vendor risk is becoming increasingly critical to protecting companies’ sensitive data. With new threats emerging daily and companies continuing to outsource, vendor risk management is an issue that will only grow in affecting organizations and their business partners. According to a recent Navex Global study, the ability to promptly resolve newly identified risks is a top challenge for organizations’ third party risk management programs.

In today’s security climate, talk of proper cybersecurity procedures must include discussion of a continuous monitoring plan that applies both internally and externally (with the company’s third-party vendors). And while continuous monitoring is critical to the health and well-being of your company, it’s also incredibly challenging to do.

As a U.S.-based company, you may be asking yourself, “Does my company need to prepare for the EU’s General Data Protection Regulation (GDPR)?” Simply put, if you process personal data for anyone in the European Union, the answer is very likely yes.