Get a report built on your actual external infrastructure—domains, IPs, certificates, cloud assets—and benchmarked against real-world breach data.
From Risk to Resilience: A New Standard for Security Posture Management
Tags:


For years, security leaders were asked a simple question: are we secure?
Today, that question is harder to answer. Boards, regulators, insurers, and customers want proof of resilience: assurance that organizations understand their exposure, are prioritizing the right work, and are reducing risk over time.
With attack surfaces rapidly expanding — accelerated by cloud migration, SaaS adoption, AI-driven innovation, third-party integrations, and global subsidiaries — organizations are operating far beyond their traditional perimeter. Threat actors are using automation and AI to turn these expanded digital footprints into new opportunities for attack. In response, boards are demanding greater accountability, and new regulations across regions and industries intensify the pressure.
Exposure management on its own is no longer enough. Security teams can easily get stuck playing “whack-a-mole” with individual issues as they surface. To make real progress, organizations need to strengthen the controls and practices that improve cybersecurity posture over time and proactively help avoid business disruptions.
Both SecOps and GRC teams play a role here. And yet, as expectations increase, many security leaders still lack a continuous, objective way to prioritize attacker-relevant exposure, validate control effectiveness, and demonstrate measurable progress to leadership.
This is where Bitsight’s Security Posture Management (SPM) becomes essential.
The visibility gap
Most organizations aren’t suffering from a lack of data. Rather, they lack the context and analysis needed to decipher their data and use it effectively at scale.
Security teams operate across dozens of stitched-together tools. They run scans, track CVEs, triage alerts, and produce dashboards. Governance teams manage frameworks, assessments, and reporting cycles. Much of this work relies on manual analysis and periodic reporting, which makes it difficult to keep pace with evolving threats or scale security efforts across their entire digital ecosystem.
Both security and governance teams are capable of generating valuable insights, but they often have difficulty bringing these insights together into a unified view of security posture. Without that unified view, leaders struggle to answer the questions that matter most: Are we actually improving? Is our security program reducing real risk? What areas do we need to focus on first, to meaningfully lower business impact?
Over time, this fragmentation leads to wasted budget, delayed response to real threats, and weakened executive confidence.
What is Security Posture Management?
Bitsight Security Posture Management enables security leaders to identify and prioritize enterprise exposure, measure the effectiveness of controls in mitigating risk, and communicate the impact of their cybersecurity program.
It connects critical elements of an organization's cybersecurity — exposure visibility, threat intelligence, business context, control effectiveness, and governance reporting — into one unified view. With automation and Bitsight AI, teams can focus on the risks that matter most, take action faster, and communicate clearly, while also connecting insights directly into the workflows used to assign, track, and validate remediation.
By integrating operational exposure data and threat insights directly into governance workflows, SPM bridges security operations and cyber risk management, ensuring that prioritization, investment, and reporting all align around measurable resilience.
Whereas traditional vulnerability management merely focuses on identifying weaknesses, SPM goes further by helping teams understand which exposures matter most based on threat activity and business impact. It also goes beyond static ratings and compliance checklists by connecting posture data to action, improvement, and reporting — and by feeding prioritized insights into the workflows teams already use to manage remediation.
In short, SPM turns fragmented security data into clear, prioritized insight that teams can act on and leaders can trust.
The four pillars of effective security posture management
Effective SPM is built on four core pillars.
1. Extended attack surface discovery
You cannot manage what you cannot see.
SPM starts with clear visibility into externally exposed assets across cloud environments, subsidiaries, third parties, and emerging AI-related exposure. It reflects the attacker’s perspective, revealing how your digital footprint appears in the real world.
That includes automatically mapping internet-facing assets, understanding exposure across complex corporate structures, continuously monitoring critical third parties, and layering in relevant threat and industry context. This comprehensive view of the extended attack surface enables teams to prioritize the exposures that present the most immediate threats and the greatest potential business impact.
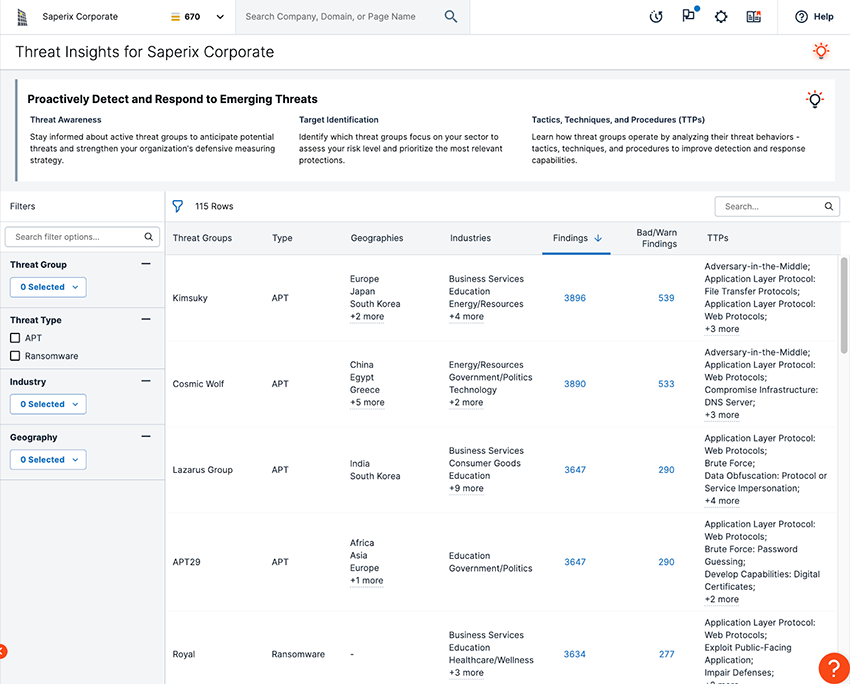
2. Threat-informed prioritization
Not all exposure carries equal risk. While still important, static scoring models and theoretical severity don’t reflect how attackers actually operate.
Threat-informed prioritization combines real-world exploit activity, ransomware campaigns, known threat groups, predictive intelligence, and AI-assisted analysis to help teams focus on the exposures attackers are most likely to exploit. This helps align remediation with asset criticality and business impact, reduce mean time to remediate (MTTR), and make better use of limited resources. By feeding those priorities into existing integrated workflows, teams can assign, track, and validate remediation without creating yet another disconnected process.
3. Measurable improvement over time
Resilience is not simply a pass-or-fail outcome. It can be measured — and improved — over time. SPM continuously tracks exposure trends and controls performance to determine whether security efforts are meaningfully strengthening resilience.
By establishing an objective baseline and benchmarking against peers, teams can validate that their remediation efforts are reducing risk. Leaders can also forecast the impact of planned investments and monitor improvement across business units and subsidiaries.
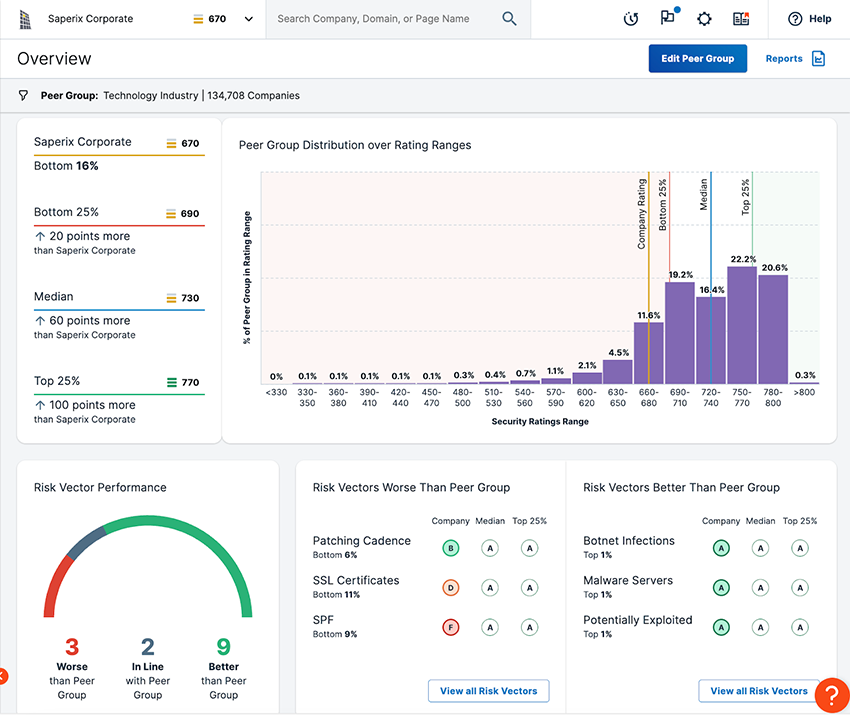
Rather than tracking activity alone, SPM shifts the focus to outcomes — providing clear evidence that the security program is working and highlighting where adjustments are needed.
4. Trusted communication
Translating cybersecurity posture into business terms is essential to building trust with stakeholders.
By grounding reporting in objective data and AI-driven insights, teams can move beyond manual reporting and quickly generate clear, audit-ready views of security posture. Leaders can easily communicate posture trends and align governance and security teams around a shared view of risk, while executives, boards, insurers, and regulators gain transparency into current security posture and measurable progress over time. They can further strengthen that conversation by leveraging familiar, externally validated signals like the Bitsight Security Rating, giving leaders another objective indicator of how posture is improving over time.
The bridge between SecOps and governance
One key driver for adopting SPM is its ability to connect day-to-day security operations with governance and reporting, ensuring both teams work from the same data and priorities.
Misalignment between these two teams is a major barrier to improving resilience. While they share the same objective, they approach the problem from different angles. Security operations teams focus on alerts, vulnerabilities, and MTTR, while GRC teams concentrate on reporting, frameworks, and board communication.
For posture management to be effective, it must fit into how these teams already operate. Rather than introducing another disconnected dashboard, it embeds prioritized, threat-informed insights into existing remediation and governance workflows, where actions can be assigned, tracked, and validated.
By unifying exposure data, threat context, and business impact into common metrics and workflows that both teams trust, SPM helps security operations and governance teams align more easily around priorities, remediation, and reporting.
What measurable resilience looks like
Measurable resilience means cybersecurity decisions are grounded in objective data and tied to real-world risk. Leaders can move from reacting to incidents to proactively and systematically reducing real-world risk. Remediation is prioritized based on active threat activity rather than only theoretical severity, so teams focus on the exposures most likely to be exploited. And security investments tie directly to measurable risk reduction, shifting the conversation from effort to outcomes.
With an objective baseline, organizations can track improvements across time, peers, business units, subsidiaries, and their entire digital supply chain. This gives leaders a clearer way to show progress, increase accountability, and keep board conversations focused on trends, impact, and sustained risk reduction.
From risk to resilience
Security posture only becomes valuable when teams can understand it, improve it, and explain it. By turning fragmented data into clear, actionable insights — and integrating those insights into the workflows teams already have in place — SPM helps connect threats, assets, controls, and outcomes in a single view. And as attack surfaces expand, threats evolve, and stakeholder expectations rise, that unified view is becoming the new standard for managing security posture and building resilience.
Bitsight Security Posture Management helps organizations measure, improve, and demonstrate cyber resilience with objective, threat-informed intelligence and defensible reporting.
See how Bitsight helps you operationalize resilience with confidence.



