With KEVs being fixed 3.5 times faster than other vulnerabilities, how does your organization measure up? See where you stand and what you can do to improve.
Race to KEV Remediation: Who Tops the Charts in Europe?
Tags:



In our global study of the CISA KEV Catalog, we uncovered widespread vulnerabilities and the swift pace at which threats evolve. As we dissect the layers of data from the report, it becomes evident that each country's unique approach to cybersecurity regulation, vulnerability management, and remediation presents distinct challenges and opportunities.
Our research highlights a variation in KEV prevalence across Europe, with Germany and France experiencing higher incidences than the global average, while the UK shows a notably lower prevalence. Let's explore what these regional nuances mean for cybersecurity leaders looking to bolster their defenses against increasingly sophisticated threats.
Analyzing KEV Prevalence in France, Germany, and the UK
In reviewing the security posture of more than 1 million global organizations, Bitsight found that 35.3% had a KEV in 2023. That means at one time or another more than a third of organizations had an externally facing CVE that was known to be exploited in the wild.
When we zoom into Europe, we observe that prevalence and remediation rates vary dramatically by company, organizational size, and country. Let’s break down the most revealing findings.
1. The UK has lower KEV prevalence than the rest of Europe
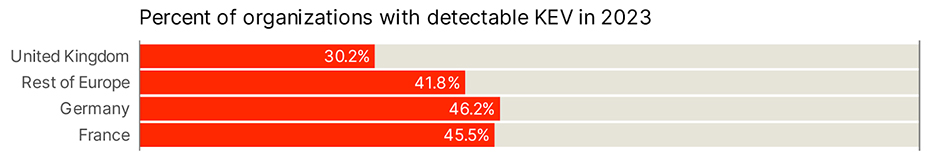
The UK shows lower prevalence, with 30.2% of organizations exposed to detectable KEVs in 2023. Germany, France, and the rest of Europe generally are higher than the global average of 35.3%. One primary consideration is the varying levels of organizational maturity across different European nations. In countries like Germany and France, where there are dense concentrations of industrial and technological infrastructures, organizations may use a broader array of complex systems and technologies. This diversity can increase the exposure to various KEVs, particularly if these systems are not uniformly updated or secured.
Moreover, the regulatory environment in Europe, notably stringent due to frameworks like GDPR, DORA, and NIS2, encourages higher transparency in reporting vulnerabilities. This could mean that what appears as a higher prevalence might also be a reflection of better detection and reporting.
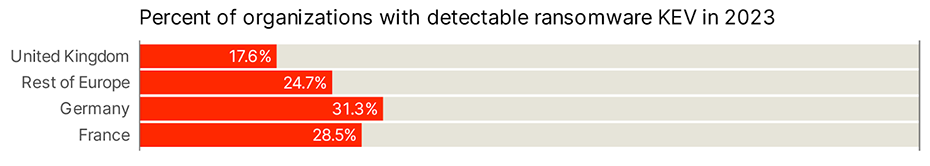
The same trend applies to ransomware-related KEV vulnerabilities, with lower prevalence for the UK than in rest of Europe, France, and Germany. However, it’s worth noting that Germany and France are well above the global average of 20%:
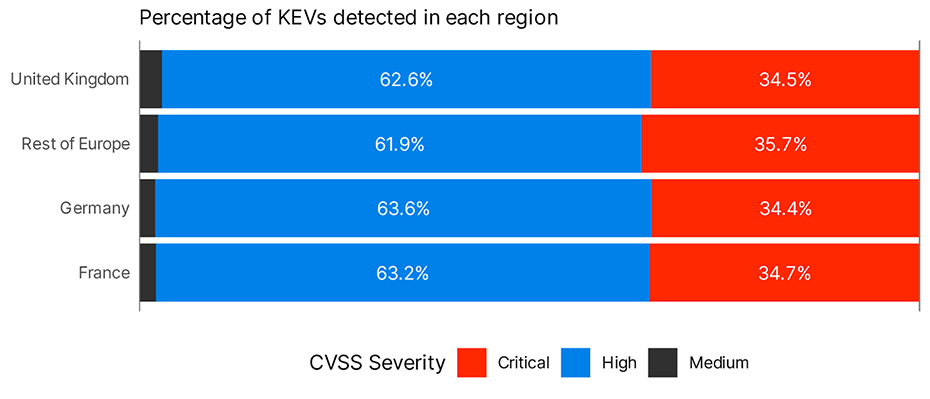
When we look at severity, we don’t see real differences across countries, with an overall predominance of High and Critical vulnerabilities detected:
2. Germany and France show higher exposure to particularly prevalent CVEs
Thousands of CVEs are created each month, but only a handful of them make headlines—think WannaCry or BlueKeep. So what role do these (in)famous vulnerabilities play here?
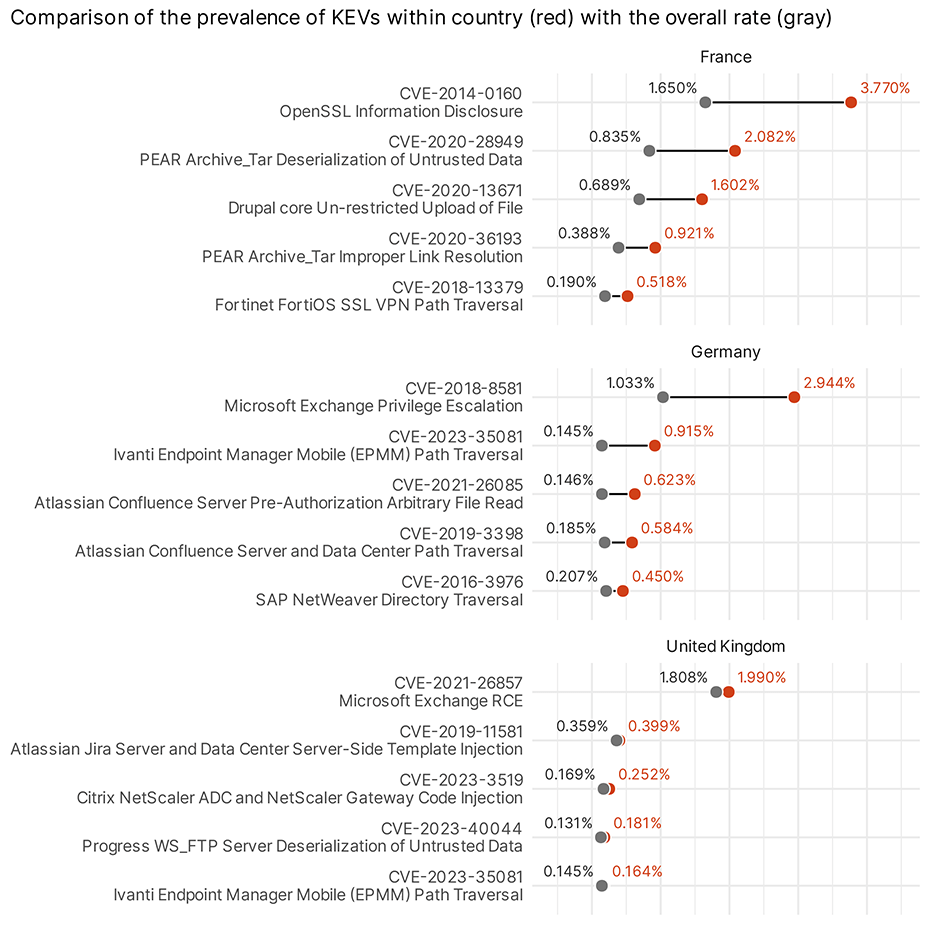
In France, the persistence of vulnerabilities like Heartbleed (CVE-2014-0160, disclosed in 2014) raises questions about legacy systems still in operation. Shockingly, 2.3x as many organizations maintain web servers with Heartbleed versus the global average. And the Drupal and PEAR Archive vulnerabilities may indicate a wider than usual prevalence of vulnerable Drupal instances in this country.
Some organizations may be facing lingering challenges in updating and securing older systems and critical infrastructure, which is a significant risk factor. The cybersecurity strategy here may need to prioritize faster phase-outs of outdated technologies.
Meanwhile, the notable prevalence of specific vulnerabilities like the one affecting Ivanti in Germany suggests we have yet to see comprehensive remediation across affected systems. This, coupled with their efficient remediation times, suggests a robust but possibly overstretched cybersecurity framework. While efficiency is commendable, it also underscores the need for continuous investment in cyber defenses to prevent future exploitations.
As for the UK, despite lower overall prevalence, the swift remediation times are not always in line with broader European trends. This could reflect differing levels of cybersecurity maturity across sectors, suggesting a need for more unified standards and training.
3. Germany is fastest at the fix
The KEV catalog provides a useful bit of guidance by giving U.S. federal agencies a specific deadline for which they’ll need to remediate KEV vulnerabilities. Our research showed that organizations globally remediate KEV vulnerabilities faster than vulnerabilities not in the KEV catalog.
The UK, France, and the rest of Europe show similar remediation times for KEV vulnerabilities, while Germany is significantly faster. Interestingly, they all fall behind the rest of Europe for non-KEV vulnerabilities, with France and the UK being significantly slower.
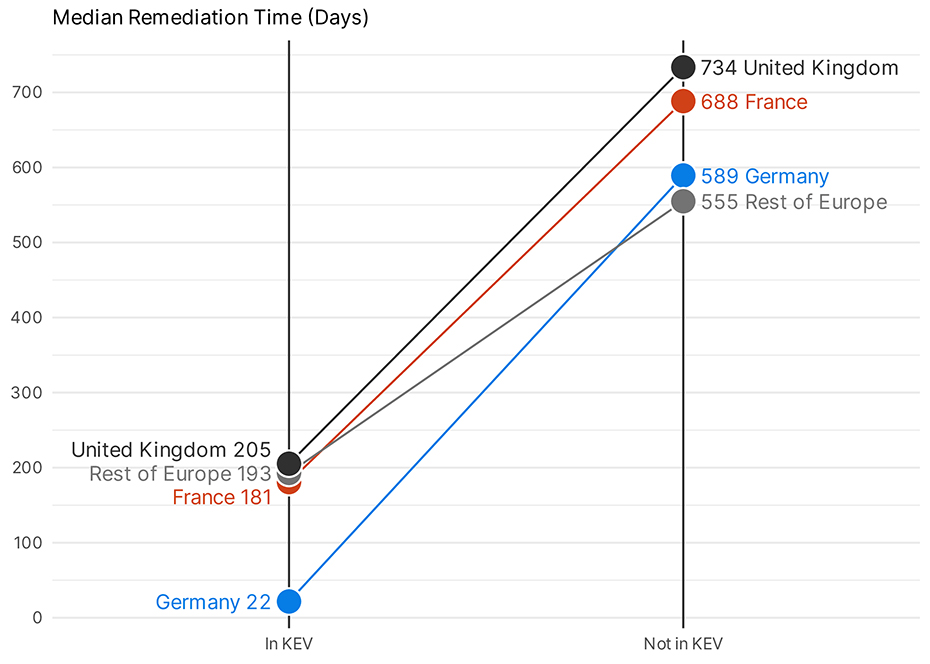
Germany, with its relatively high exposure, ends up the fastest in Europe in getting things cleaned up. The UK, in contrast, is relatively slow on remediation, even with its relatively low exposure. It’s also worth noting that bigger organizations have faster remediation rates in every country, as their maturity probably allows for increased visibility of assets and a clear plan of action for fixing vulnerabilities.
Implications for Cybersecurity Strategies
These findings underscore the necessity for tailored cybersecurity approaches that consider both the local regulatory environment and specific threat landscapes. Financial institutions, for instance, must align their cybersecurity measures with both global standards and regional directives.
As KEVs continue to pose significant risks, understanding regional differences and commonalities in how these threats are managed can empower cybersecurity leaders to develop more effective strategies. For France, Germany, and the UK, the path forward involves not only rapid response but also a deepened focus on preventive measures and regulatory compliance—especially with standards like NIS2 and DORA demanding organizations to strengthen resilience.
The nuances of the European cybersecurity landscape remind us that while global trends provide a broad picture, local details sharpen our focus and strategy. This deeper understanding is essential for cybersecurity leaders aiming to safeguard their operations in an increasingly interconnected world.
Explore the full scope of our KEV research and gain more insights into how your organization can enhance its cybersecurity posture by downloading our detailed report.