How to Make Your Third-Party Risk Management Program More Efficient

With as much as 75% of the workforce shifting to remote work in some industries, organizations around the world are seeking to rapidly acquire new software and technology to properly enable the business, facilitate the new needs of workers, and prevent employees from turning to unauthorized shadow IT.
While these conditions may put added pressure on security leaders to make vendor onboarding decisions quickly, rushing through assessments often leads to errors — which can open organizations up to unwanted cyber risk. This is particularly true now, as more businesses are moving to mandated work-from-home models — because residential IPs account for more than 90% of all observed malware infections and compromised systems.
Though organizations are facing new challenges when it comes to collecting and evaluating cybersecurity data about their vendors in a scalable way, the fundamentals of a good third-party risk management (TPRM) program haven’t changed. In fact, given the risk climate during the current pandemic, the need for companies to look for operational efficiencies in their programs has never been more critical.
Reassess your current procedures and contracts
The current global environment has made it increasingly difficult for many organizations to choose and assess potential vendors effectively. In order to promote efficient vendor evaluation and onboarding processes with a largely remote workforce, security leaders must automate whenever possible — and determine whether they need to establish new procedures to immediately identify areas of risk that require attention.
Ask yourself the following types of questions to ensure you have the right tools and processes in place to streamline your vendor risk assessment and risk remediation efforts during the pandemic:
- Do you typically rely on outside consultants to conduct vendor evaluations? If so, how can you bring these processes in-house?
- Do you regularly conduct on-site assessments? If so, how can you leverage online tools to complete these assessments remotely?
- Who are your current critical vendors? Do they have pandemic and recovery plans in place?
- How will your vendors (and their vendors) remediate any security issues that arise over the coming months if everyone is working remotely? What contingencies do you need to establish in writing to align on new processes and expectations?
- Do you have the necessary communication plans and escalation procedures in place to ensure you are immediately notified of any breaches within your vendor network?
By being proactive in reevaluating your current processes through the lens of the new and evolving state of the global workforce, you can work quickly to make the necessary shifts with limited to no impact on your business.
Streamline your vendor evaluation process
Once you’ve reassessed your existing third-party risk management procedures and aligned on new roles and responsibilities, it’s time to consider how you can make your vendor onboarding process faster and more scalable to meet the growing need to acquire new SaaS tools quickly.
A good place to start is with your pre-screening process:
- How do you currently determine whether a vendor is worth considering? Can this process be optimized?
- What security criteria do you have in place?
- What does your team consider to be an acceptable risk threshold?
In order to get the most out of the time and money your team is investing in its third-party risk management program, it’s critical that you have a common, standard set of cybersecurity KPIs to use to measure and communicate the effectiveness of a potential vendor’s security program over time. As security ratings are a data-driven, objective, and dynamic measure of security performance, thousands of organizations around the world use this KPI to manage cyber risk where transparency may have historically been lacking.
Using security ratings findings, you can set clearly defined acceptable risk threshold policies and pre-screen proposed vendors accordingly. If, for example, a particular third-party doesn’t meet your security guidelines from that start, you may choose to eliminate them from the procurement process — allowing you to focus your limited resources on evaluating those vendors that have more desirable cybersecurity postures.
When it comes to streamlining your third-party risk management program, another crucial factor to consider is how you should adapt your assessments based on the partnership your organization will have with the vendor in question. After all, no two vendors are the same. Each third-party presents different risk levels, and therefore merits different treatment.
Instead of wasting time doing long, full-blown assessments on every vendor, allocate your resources to those that require greater due diligence. With security ratings data, you can shorten onboarding cyber security risk assessment questionnaires by making sure they focus on the areas of known risk. And, using the Bitsight Benchmarking tool, you can even see how a particular vendor compares against others in a similar industry — empowering you to make faster, data-driven assessment decisions.
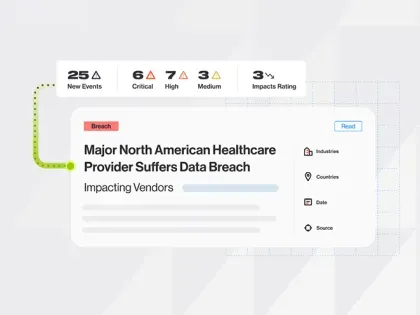
Assess risk and report on security outcomes regularly
Now, more than ever, it’s critical that you continuously monitor any shifts or changes in your vendors’ cybersecurity postures — and perform reassessments when necessary. As security ratings are updated on a daily basis, you can quickly determine if and when a drop below your previously agreed-upon risk threshold occurs. This data empowers you to get the most out of your team’s limited resources and focus your remediation efforts on the areas that can have the biggest impact. During these uncertain times, be sure to pay close attention to your most critical vendors to understand any new or evolving risks in their networks.
Of course, ongoing communication and reporting of security performance are also vital parts of an effective third-party risk management program. As a best practice, you should schedule a regular vendor summary report so that you can stay updated on any security posture shifts — and gain the insights you need to provide a consistent and timely update to the board and other relevant stakeholders.
The TPRM fundamentals haven’t changed
While we’re all operating in a new and evolving threat environment as a result of the coronavirus outbreak, the basics of developing a strong third-party risk management program remain the same. In fact, with the increased push to acquire new technology quickly, finding operational efficiencies in your process is more important than ever. In order to promote efficient and effective vendor assessment and onboarding processes with a largely remote workforce, security leaders must automate and streamline wherever possible.