Strengthen your third-party defenses—and when vulnerabilities hit, deploy AI-accelerated workflows to prioritize threats and drive rapid response.
What is Digital Supply Chain Management?

What is the digital supply chain? 2 Definitions
You may have heard the term “digital supply chain management” (SCM) being used to describe an emerging business function. But what exactly is a digital supply chain, and how is one supposed to manage it? Depending on the context in which it’s used, the term “digital supply chain” could have one of two different meanings. The term can either refer to:
- The digital aspects of a physical supply chain
- The chain of technology companies involved in the delivery of digital products
1. Supply chain + digital
In the first definition, “digital supply chain” refers to how the development and implementation of advanced digital technologies (IoT, blockchain, machine learning, artificial intelligence, predictive analytics, etc.) can drive improvements to traditional supply chains.
For example, in McKinsey’s concept of the “next-generation digital supply chain,” supply chain leaders ought to “place sensors in everything, create networks everywhere, automate anything, and analyze everything to significantly improve performance and customer satisfaction.”
Who’s responsible for managing the digital supply chain? Within this definition, the team responsible for digital supply chain management is the same as the team responsible for any supply chain functions (which could be sales, manufacturing, logistics, etc.).
These teams are tasked with finding new ways to accomplish the same goals they’ve always had: improving efficiency and increasing margins. In other words, “digital supply chain management” is really just supply chain management with an added layer of digital technologies. These technologies include:
- Predictive analytics to optimize inventory allocation and forecast demand
- Automated replenishment solutions
- Robotics to speed up assembly or picking
- IoT sensors to gather real-time feedback from manufacturing equipment and vehicles
2. Digital product ecosystem
The second definition — that the digital supply chain is the chain of technology companies involved in the delivery of digital products — originally referred to the supply chains of digital products that initially existed in physical form, such as ebooks and mp3s. This term was coined in a 2001 paper.
Now, the definition has expanded to include the supply chains that help deliver any digital product, such as a website or software platform.
Take an e-commerce website, for example. Its digital supply chain includes the website’s developers, its administrators, the cloud services company that hosts the website’s data, the CMS provider, and the devices that consumers use to access the website. In addition, every third-party technology provider whose code provides functionality to the website — e-commerce plugins, personalized recommendation engines, advanced analytics services, inventory tracking solutions, custom product builder, chatbots, etc. — should also be considered part of the digital supply chain.
Digital supply chain attacks examples
Looking closely at any digital product, whether it’s an e-commerce website, B2B software product, or something else, one can discover the long list of providers upon which the product relies. Viewing this list as a supply chain can help technology companies improve their own security, and can help customers decide whether or not a technology vendor is secure. Below are notable examples in recent years of supply chain attacks that underscore digital supply chain risk:
DDoS attack on Dyn
The 2016 DDoS attack on DNS provider Dyn that took down a large portion of the North American internet (including Spotify, Reddit, and the New York Times) for nearly a day. This is a typical example of a digital supply chain risk. The relationship between Spotify and Dyn is comparable to the relationship between a clothing retailer and a wool supplier — one relies on the other in order to deliver their product.
Ticketmaster breach
In 2018, card skimming malware was added to the Ticketmaster website via a vulnerability in the code of a customer support software company. In other words, a threat was introduced through Ticketmaster’s digital supply chain.
NotPetya
Although supply chain-based attacks have grown tremendously in the past year or two, one of the more notable ones happened in 2017. A Petya ransomware variant called NotPetya was used to target a Ukrainian accounting software package -- using a vulnerability previously exploited in the WannaCry supply chain attack as well as a credential-stealing technique for non-vulnerable machines -- before deploying ransomware.
The malware quickly spread beyond Ukrainian targets, affecting numerous multinational corporations, resulting in extensive financial losses, operational disruptions, and data destruction.
SolarWinds
In 2020, a Russian hacking group infiltrated SolarWinds' Orion platform, injecting malicious code into Orion software updates. That allowed the hackers to gain access to some 18,000 SolarWinds customers, compromising government agencies, technology firms, and other high-profile entities, resulting in unauthorized access and exfiltration of sensitive data.
MOVEit
File transfer solutions are frequent targets of cybercriminals, due to their role in facilitating the exchange of sensitive data across the supply chain. In June 2023, three critical SQL injection vulnerabilities were discovered in Progress Software’s MOVEit Transfer platform, a tool designed to securely transfer sensitive files used by close to 1,700 organizations. Zellis, a UK-based payroll and HR solutions provider, was affected by the MOVEit vulnerability and targeted by the Cl0p ransomware gang.
This attack resulted in unauthorized access to sensitive personal information of both Zellis and its clients. The MOVEit supply chain attack also affected dozens of other organizations, including British Airways, the BBC, and the Minnesota Department of Education, and posed a significant risk to millions of individuals globally.
What is digital supply chain management?
What exactly is digital supply chain management? Depends on who you ask. It can either refer to managing the digital aspects of a physical supply chain, or managing the supply chain of digital products.
In many ways, however, these definitions overlap. Almost every supply chain is now digital, and almost every digital product is now part of a supply chain. For IT security teams, understanding how the organization fits within various digital supply chains can help improve security. Once you’re able to map third-, fourth-, and fifth- party connections, you can gain a better understanding of your attack surface.
How to automate & scale digital supply chain security
1. Automate the vendor onboarding & assessment process
Automation is key in utilizing security program resources effectively. The traditional security questionnaire process, often mired in manual email, spreadsheet, and calendar management, is ripe for automation. This approach not only saves time but also reduces errors. Technologies like Bitsight Vendor Risk Management (VRM) can revolutionize this process, offering a secure, centralized platform for automating information gathering and assessment. This system ensures compliance with regulatory standards and frameworks and integrates independent validation to identify potential issues in vendor responses.
2. Continuously monitor your extended ecosystem
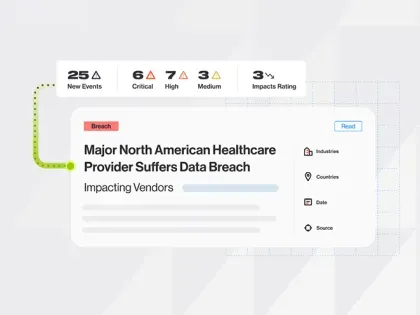
Traditional security assessments provide only a snapshot of vendor security postures. Bitsight's continuous monitoring technology allows for real-time awareness of emerging risks and cyber incidents across your digital supply chain, including fourth-party risks. This continuous oversight enables prompt action to mitigate breach risks and fosters collaborative remediation with vendors. Furthermore, this continuous monitoring facilitates effective reporting on supply chain cyber risk to leadership, enhancing dashboard reports that track risk trends and vendor performance.
3. Mature your digital supply chain security
For organizations with limited resources, maturing digital supply chain security is a challenge. A dedicated advisor can be a game-changer, especially when combined with a platform like Bitsight. This advisor can oversee VRM and remediation efforts, validate vendor security during RFIs and RFPs, ensure new vendors meet cybersecurity standards, manage the vendor assessment process, monitor alerts, assist in vulnerability remediation, and provide customized reports on risk posture and trends.
Incorporating these strategies into your digital supply chain management is not just a step towards efficiency; it's a leap towards enhanced security in a digitally dependent world. Automating and continuously monitoring the digital supply chain is crucial for safeguarding against evolving cyber threats and maintaining a resilient and effective supply chain network.
A growing attack surface
Digital supply chains are distributed and complex. Providers that appear to have little to do with the delivery of a digital product can still act as points of entry for cyber attacks, and must be considered part of the digital supply chain.
Take the 2020 SolarWinds breach, for example. Microsoft, which had used SolarWinds Orion software, revealed that the hackers behind the cyber attack were able to escalate access inside Microsoft’s internal network to view their source code repositories.
The SolarWinds incident shows us that monitoring the security of one’s own third-party network is insufficient. True digital supply chain security solutions demand knowing not just that your technology vendors are secure, but that their vendors are secure (and so on).
That problem isn’t as insurmountable as it seems. Tools are available that can help IT security teams create a map of the digital supply chain to identify vulnerabilities and single points of failure among third-, fourth-, and fifth-party providers.