Get a complete view of your digital footprint—including shadow IT and hidden vulnerabilities. Uncover gaps and secure your perimeter before attackers can find them.
Enabling More Precise Evaluation of Email Security with DMARC

Email is a well-known and widely used attack vector for malware distribution, phishing, and many other types of threats. For this reason, we evaluate certain email security practices as part of the Diligence category of risk vectors used to calculate Bitsight Security Ratings.
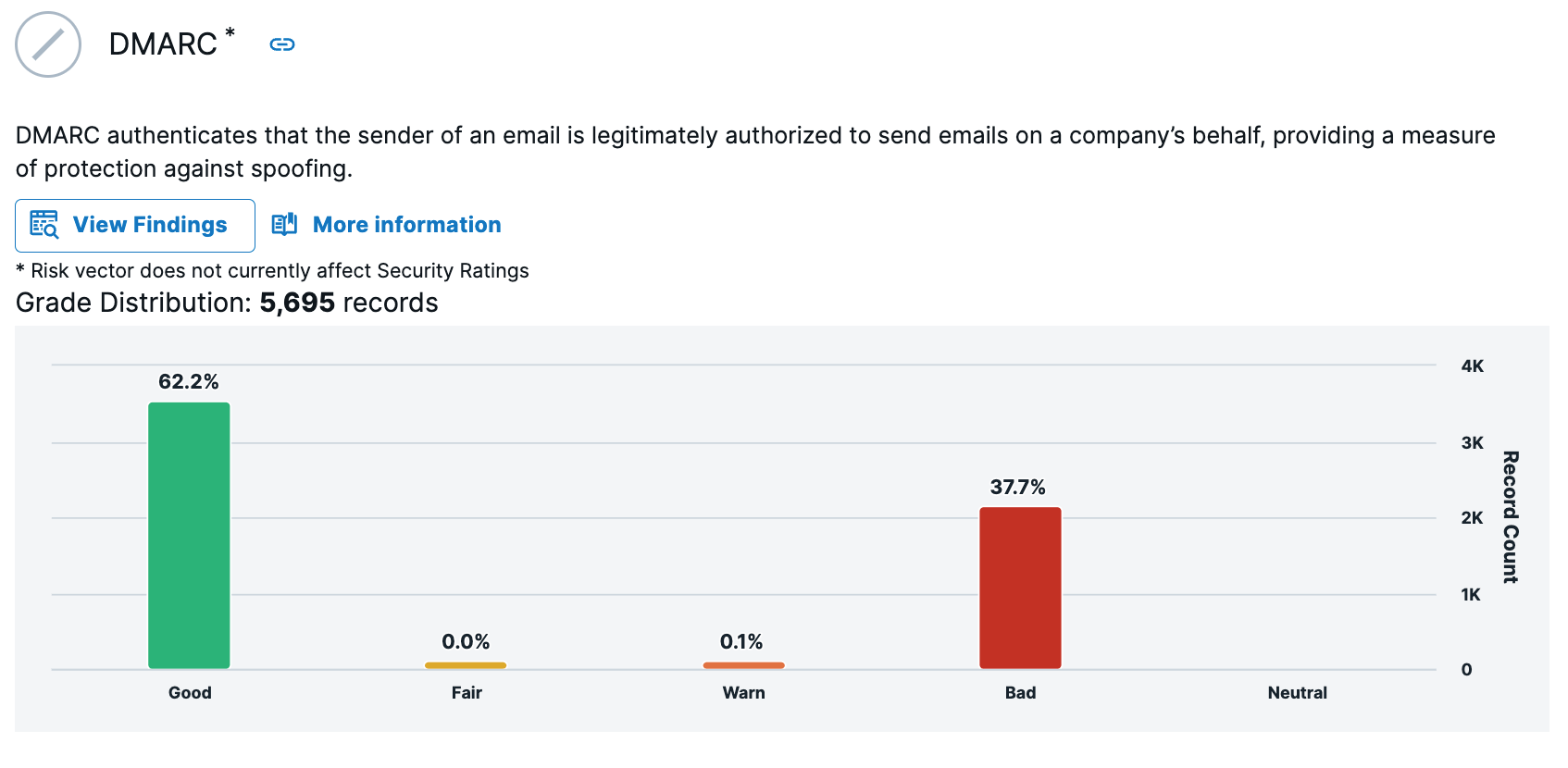
On April 30, 2024, we added a new email security evaluation focused on the use of Domain-based Message Authentication, Reporting, and Conformance (DMARC) records. DMARC evaluation is initially included as a non-graded risk vector and will not impact Bitsight Security Ratings at this time.
Here are some further details about this enhancement, why we made it, and what it means to your organization.
How has Bitsight evaluated email security previously?
Historically, Bitsight has evaluated the email security practices for specific domains by reviewing the usage of two commonly used DNS record types:
Sender Policy Framework (SPF) Records
SPF records identify mail servers permitted to send email on behalf of a domain. Bitsight looks for properly configured SPF records for all an organization’s domains, even if they aren’t used to send email. This is a best practice, since threat actors may attempt to spoof email from a domain even if the organization does use it for email themselves.
DomainKeys Identified Mail (DKIM) Records
DKIM records provide an additional level of protection against email spoofing by using public key cryptography to verify the authenticity of email messages. Bitsight looks for properly configured DKIM records that ensure that email messages have not been altered in transit and originate from the claimed source domain.
These evaluations are performed through automated scanning, and findings for both have a lifetime of 60 days.
What is DMARC, and how does it work?
DMARC is an email authentication protocol that builds on SPF and DKIM by giving domain owners greater control over email authentication, including:
- Requiring either SPF or DKIM to pass in order for email to be considered authenticated
- Allowing domain owners to specify the action mail servers should take when authentication fails, such as rejecting or quarantining the message
- Providing the ability to request authentication statistics from receiving mail servers to review the effectiveness of their implementation
This additional level of control, when configured effectively, provides enhanced protection against phishing and other email-based threats.
For a more detailed explanation and real-world examples of how proper DMARC usage reduces email risk, check out “Domain (in)security: the state of DMARC” for a deeper dive into this topic by the Bitsight Research Team.
What is driving DMARC adoption?
Major email providers like Google, Yahoo, and Apple are taking steps that will accelerate the transition of DMARC from best practice to a must-have email configuration. For example, Google implemented a new set of requirements on February 1, 2024, that requires all organizations that send more than 5,000 messages per day to Gmail users to have a DMARC policy in place. They also noted that they will be using a DMARC quarantine policy moving forward for messages sent from Gmail addresses.
Yahoo and Apple have introduced similar policies. While these changes are initially focused on bulk email senders, they apply to many email marketing platforms used in the business setting. These actions by top email providers also likely represent a major step towards broad-scale adoption of DMARC for all types of email delivery.
How does Bitsight evaluate DMARC usage and diligence?
Bitsight now scans DNS records for the presence of DMARC records in addition to SPF and DKIM records. As part of this process, we confirm that, in addition to SPF and DKIM, DMARC is functioning to better protect against spoofing attacks, including verification that:
- An incoming email passes SPF (which authorizes mail servers to send an email on behalf of a domain) and/or DKIM (which checks the email for tampering during transit).
- The Envelope From domain matches either (a) the Header From domain or (b) the DKIM domain.
Will this change affect my organization’s Bitsight Security Rating and related workflows?
As noted above, DMARC has been introduced as a non-graded risk vector that will not yet affect Bitsight Security Ratings. Details about the DMARC can now be found in the Bitsight portal and API under the Diligence Category.
DMARC will not be included in planning tools like Risk Remediation Plans or comparison tools like Peer Analytics as part of this initial release.
We are evaluating future options to make DMARC, or a set of email security assessments that include DMARC, a ratings-impacting Risk Vector in a future ratings algorithm update. We will communicate any future plans in the area to Bitsight customers well in advance, so they can understand any rating impact and plan accordingly.
Learn more about the Bitsight Security Rating
If you would like to learn more about how the Bitsight Security Rating works and view examples of its correlation with real-world cybersecurity outcomes, be sure to visit our security ratings overview page or with Bitsight account log in to view the Rating Details page.

