Request your free custom report and see how you can start reducing your cyber risk exposure across your digital ecosystem: cloud assets across all geos & subsidiaries; discover shadow IT; security risk findings; and more!
As Holiday Shopping Season Nears, Retailers May Be At Risk Of Ransomware

Recent Bitsight research shows that 75% of retail businesses may be at increased risk of ransomware attacks as indicated by poor TLS/SSL configuration management. With the holiday shopping season upon us, it's more important than ever for retailers to evaluate their security posture.
Large retail businesses may have hundreds or even thousands of TLS/SSL certificates identifying specific Internet-connected devices. Plus, many lack an organization-wide framework for discovering, cataloging, and managing TLS/SSL configurations. Instead, management is conducted on an ad hoc basis, usually at a departmental level.
While poor TLS/SSL management does not directly result in successful ransomware attacks, Bitsight has found that it is a good indicator of overall security hygiene.
“Bitsight believes that the use of deprecated, insecure TLS protocols often indicates that an organization is unable or unwilling to upgrade to newer, supported technology,” said Ethan Geil, Senior Director, Data and Research at Bitsight. “If they are unable to fix SSL, it is likely that they are unable to patch other, more critical vulnerabilities, as well. Continuing to support insecure protocols is a symptom of poor security hygiene in general.”
What we learned
To rate TLS/SSL configuration management performance, we examined whether security protocol libraries support strong encryption standards when making connections to other machines. Incorrect or weak TLS/SSL configurations result in infrastructure becoming more vulnerable to potential attack.
To calculate the grades (A-F) associated with the TLS/SSL Certificate and Configuration Management risk vector, Bitsight examines a variety of parameters. These include, but are not limited to, the presence of insecure or obsolete protocols, the strength of encryption keys and hashing algorithms, and the presence of self-signed and/or expired certificates. Click here to learn more about how Bitsight Security Ratings are calculated.
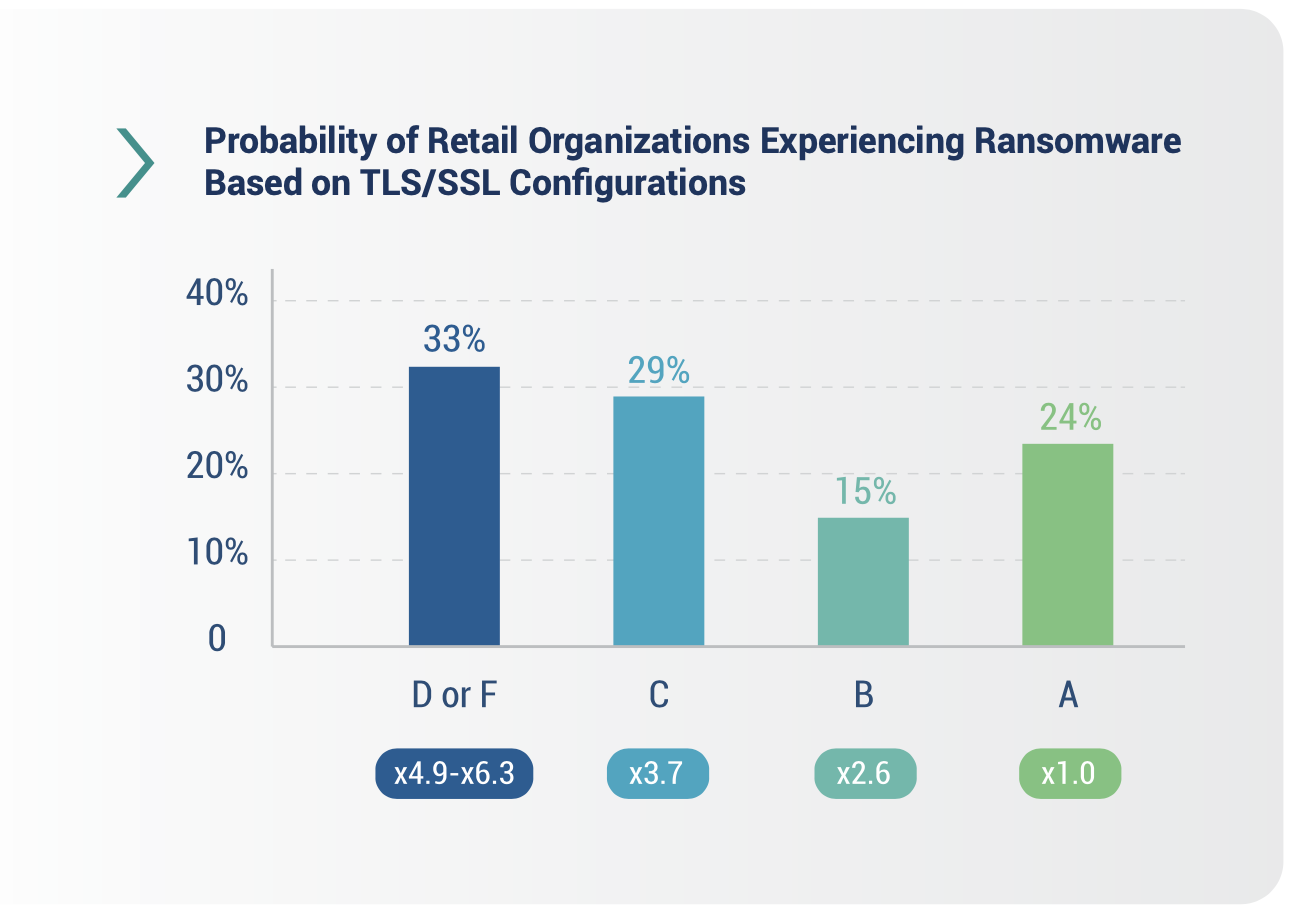
As noted above, 75% of the retail sector is at heightened risk of ransomware due to poor TLS/SSL configuration management. Only 24% of retail sector organizations scored an “A” in TLS/SSL Configurations, making them less likely to experience a ransomware attack. 15% scored “B”, 29% scored “C”, and 33% were in the “D” or “F” range.
Companies with a C grade or lower in TLS/SSL Configuration are nearly four times more likely to be a ransomware victim—concerning for over 60% of organizations in the retail sector.

Addressing TLS/SSL certificate management issues
Last year, The National Institute of Standards and Technology (NIST) released a highly detailed report on TLS certificate management. According to the report:
To effectively address the risks and organizational challenges related to TLS server certificates and to ensure that they are a security asset instead of a liability, organizations should establish a formal TLS certificate management program with executive leadership, guidance, and support. The formal TLS certificate management program should include clearly defined policies, processes, and roles and responsibilities for the certificate owners and the Certificate Services team, as well as a central Certificate Service.
Additionally, the report offers actionable steps to address security risks associated with TLS/SSL certificate management, such as:
- Create a TLS inventory: Establish and maintain a single inventory of all TLS server certificates.
- Establish a certificate service: Support certificate owners in effectively managing their certificates.
- Establish a management interface portal: Provide an effective user interface to view and manage certificates.
- Automate discovery and import: Provide multiple options for automated certificate discovery import.
- Automated enrollment and installation: Eliminate errors associated with manually requesting, installing, and managing large numbers of certificates.
- Automate certificate lifecycle: Automate certificate lifecycle management whenever possible to decrease security and operational risks.
- Monitor certificate status: Continuously monitor TLS certificate status to prevent outages and security vulnerabilities.
- Develop reporting and analytics: Establish visibility across inventory to quickly identify TLS server certificate issues or vulnerabilities.
To learn more about protecting your business, download our “Ransomware in the Retail Sector” eBook. For more insight into the potential risks living on our network request a Bitsight demo.

