Understanding the Effects of DoublePulsar & WannaCry Across Industries


The Shadow Brokers, a hacking group known for releasing exploits and vulnerabilities allegedly used by the National Security Agency (NSA), published a cache of tools over a month ago on April 14th. This release had initially caused panic within the security industry as it was believed at the time that some of the exploits were using zero day vulnerabilities, or vulnerabilities for which the vendor had not yet made a fix available. It was later learned that Microsoft had released a patch for these vulnerabilities in a March update, MS17-010. Since these vulnerabilities were first revealed, a set of malicious actors have deployed the DOUBLEPULSAR backdoor onto affected machines to permit easier access, and another set have written a worm, known as WannaCry, to take advantage of unpatched systems and spread internally within a network. Bitsight customers have the ability to filter their portfolio of continuously monitored companies to determine those companies that are at risk because they have the DOUBLEPULSAR implant on a host.
The WannaCry ransomware worm also caused panic beyond the security community. Britain’s National Health Service (NHS) said 16 organizations had been affected. Hospitals across England were forced to turn away patients after experiencing service outages that affected an array of devices from desktops, X-ray machines, phone systems, and more. It is not the first time an event like this has happened: in March of 2016, MedStar Health patients in Maryland were also turned away as a result of a ransomware infection. However, the scale of disruption that occurred at the NHS may be unprecedented.
Background and Affected Industries
This release by the Shadow Brokers contained some of the more significant revelations compared to their prior releases: remote code execution vulnerabilities affecting almost every version of Microsoft’s Windows platform. Most vulnerabilities affected the Server Message Block (SMB) service often used for file sharing, while one vulnerability was discovered for Remote Desktop Protocol (RDP). Other exploits in the cache were for known vulnerabilities that had been patched several years prior. The more recent vulnerabilities that dropped in the cache make the following systems particularly vulnerable to system administrators who have not yet applied MS17-010:
- Windows Server 2003, 2008, 2012 & Windows XP, Vista, 7, and 8 are affected by SMB vulnerabilities through the NSA exploits ETERNALCHAMPION, ETERNALROMANCE, ETERNALBLUE, and ETERNALSYNERGY.
- Windows Server 2003 and Windows XP are also vulnerable to an RDP vulnerability through the NSA exploit ESTEEMAUDIT.
Any aforementioned system with these services exposed to the Internet that has not been patched is vulnerable to remote attack. Since Bitsight aggregates externally observable network and security data to companies across a breadth of industries, we are able to observe the distribution of companies who have SMB exposed on the Internet that might be affected by these vulnerabilities. The following bar chart represents the ratio of companies within that industry that have at least one system with SMB exposed.
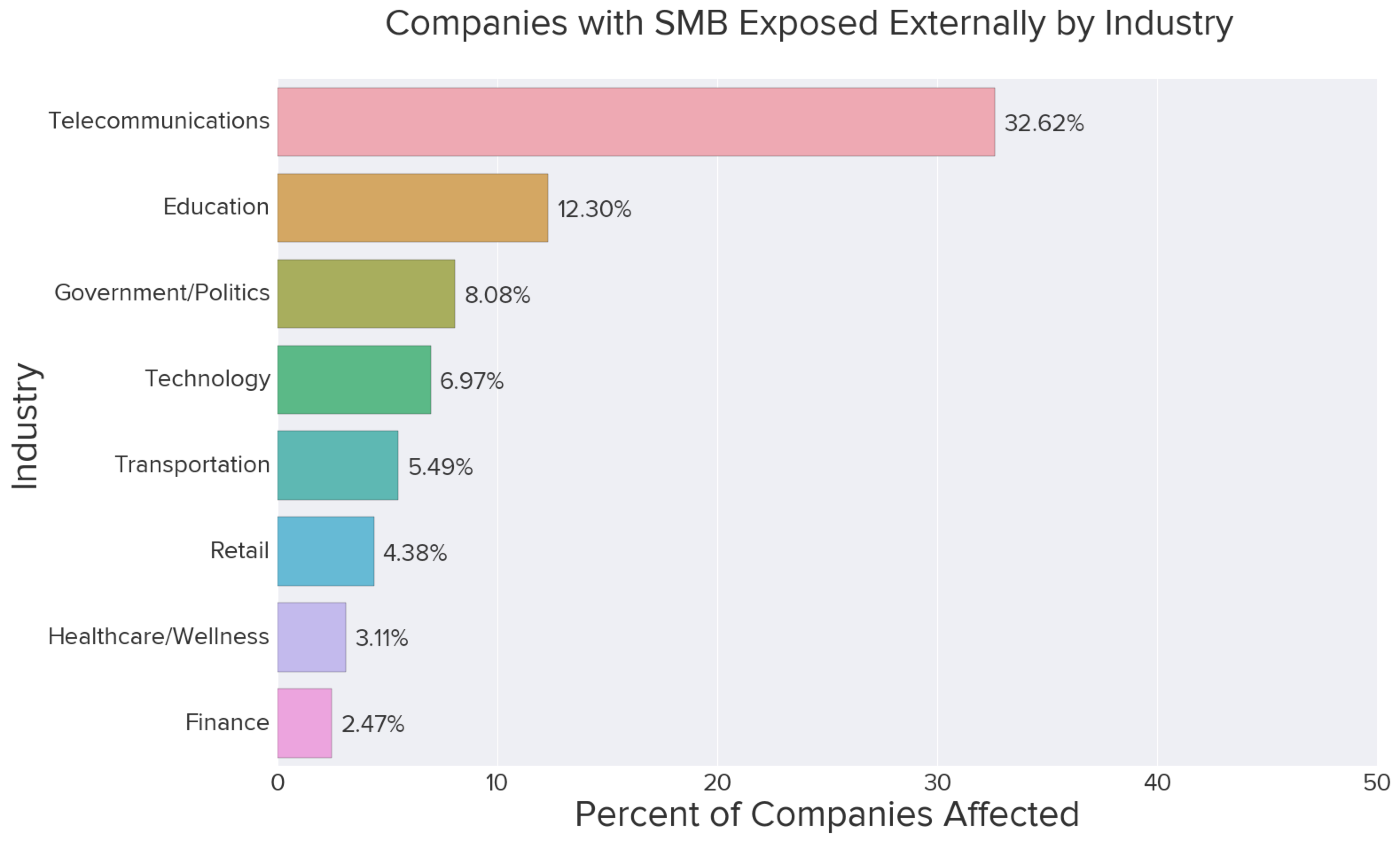
The top two industry sectors are Telecommunications and Education, which often include consumer and residential networks and thus often have less restrictive network and security policies. On the other end, Healthcare and Finance rank last with the fewest percent of companies affected.
Starting shortly after the release of NSA exploits, malicious actors took advantage of an included implant, known as DOUBLEPULSAR, to inject a backdoor into the affected hosts for easier access. As DOUBLESPULAR is an ephemeral backdoor, it will be removed when a system is rebooted, thus requiring another injection of the implant to occur. Likewise, as system administrators patch systems, they will be resistant to another attempt. If an organization's external-facing systems have been patched but not their internal workstations or servers, they are still at risk to suffer a network-wide compromise, which would include companies not present in the industry distribution.
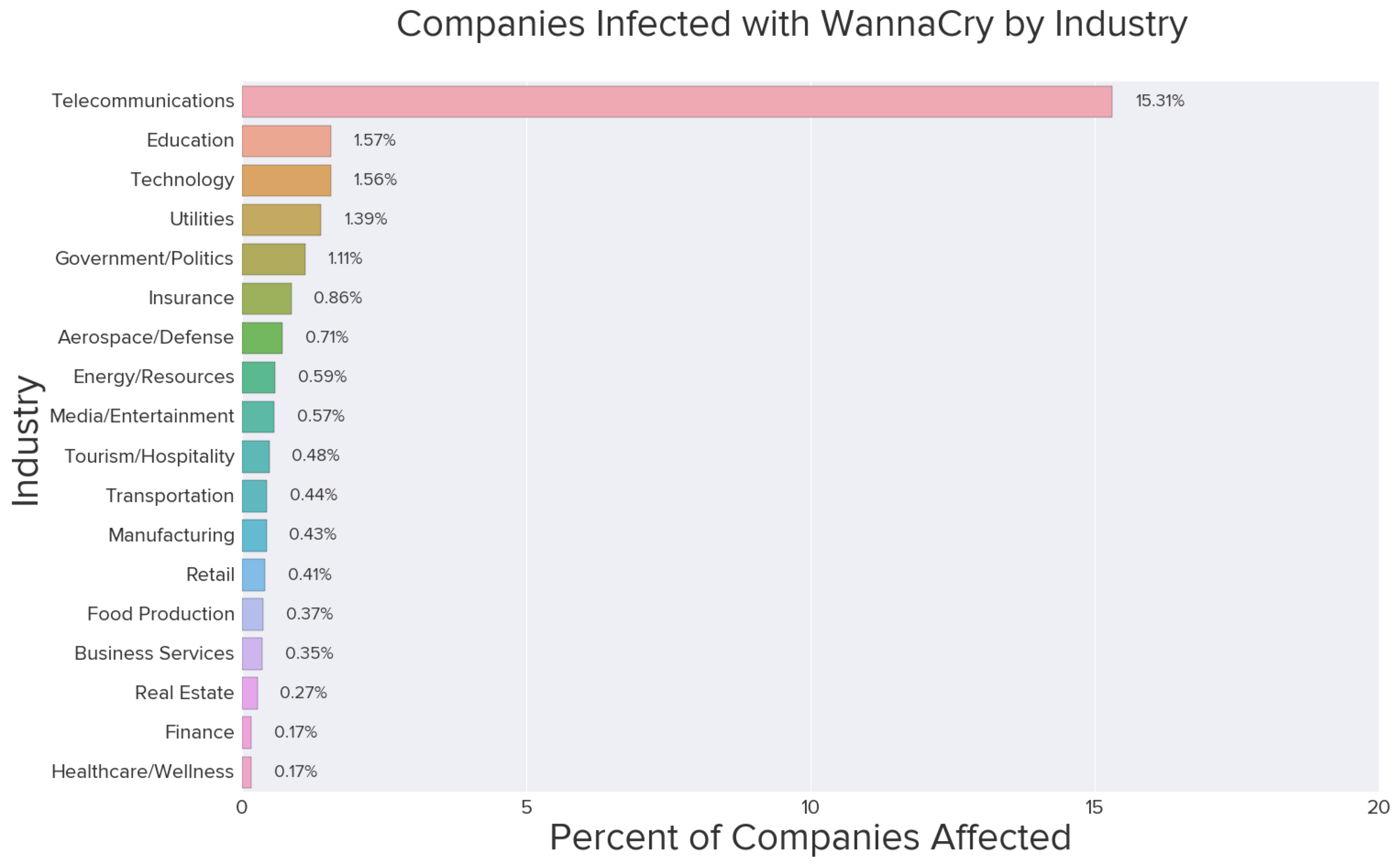
Ransomware can be one of the more damaging forms of malware since it targets user data, which is often of significant value to the user or company, but not third-parties. The first version of WannaCry included an accidental kill-switch that caused the worm to slow down propagation once it was activated by security researchers. However, it is widely expected that new iterations of the worm will not include the same mechanism to stop propagation, and this emphasizes the necessity to ensure proper patch and vulnerability management processes. The chart below captures the ratio of companies who had been infected over the weekend by WannaCry by industry.
The severity of these vulnerabilities brings to light the difficulty of supporting and maintaining complex systems that often rely upon out-of-date and unsupported platforms like Windows XP. In light of this, Microsoft released a patch in the past couple days on their unsupported platforms in an effort to protect these systems, but for many of them it may have come too late. Mission critical and life support systems could continue to become victims to efficient network worms that halt business operations and may ultimately have life or death consequences.
Discovering and Engaging With Your Affected Third Parties
We allow Bitsight customers to instantly filter their third parties and other companies who exhibit WannaCry infections. We also allow filtering within a portfolio by many attributes, allowing users to discover which of their third parties have the SMB service exposed externally on any one of those company assets. Below are the three filter options that might be of interest to users who wish to understand the risk to their ecosystem. Communications can then be targeted toward only the affected third parties.
WannaCry Infection
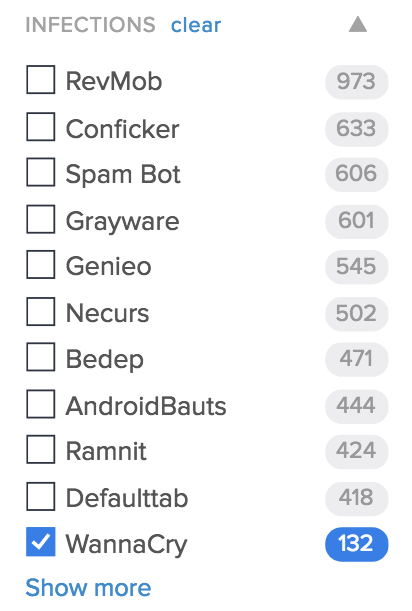
To see a list of third parties in a portfolio that have had a machine infected over the weekend by the recent WannaCry worm, a user can use the “Infections” filter on the Portfolio page and choose “WannaCry.”
SMB and RDP Exposed
For the Server Message Block (SMB) service and Remote Desktop Protocol (RDP), a user can do this by choosing the “Open Ports” filter on the portfolio page and selecting “SMB” or “RDP.” The results will contain third parties that have this service exposed, whether it remains unpatched or is currently patched.
DOUBLEPULSAR Backdoor
The DOUBLEPULSAR backdoor is categorized under “Vulnerabilities” and thus on the Portfolio page; the user may expand that category and choose “DOUBLEPULSAR.” The results will contain third parties who currently have a system with the DOUBLEPULSAR implant active on a host.
Additional Tips for Avoiding WannaCry Infections
- Install MS17-010 on all systems inside a network. Microsoft has also released out-of-band patches for unsupported systems, including Windows XP.
- Disable SMBv1 across the Windows Domain or on all systems in the network.
- Do not block the killswitch domain on the perimeter; the malware is expecting a valid HTTP response from this domain to not spread via the SMB worm. (Since it’s already sinkholed by researchers, it’s OK to let the traffic between the infected systems and domain pass.)
- If the above is not an option, set up an internal sinkhole that points that domain to an internal webserver. If your network has a non transparent proxy, you need to setup an internal sinkhole, since the malware is not proxy aware.



