Download our vendor portfolio risk report sample to get an exclusive look at the actionable reporting capabilities third party risk management teams can use to reduce critical portfolio risk.
Atlassian Confluence vulnerability (CVE-2022-26134) and what it means for your business

Written by Noah Stone; Research by Hala Mostafa & Paulo Pacheco
Confluence Vulnerability - Executive Summary
- Atlassian Confluence, a collaborative team workspace used by half of Fortune 500 companies, has been impacted by a critical-severity vulnerability (tracked as CVE-2022-26134) allowing for ransomware deployment, data theft, and more.
- Reports indicate that attackers are actively exploiting the vulnerability to deploy ransomware. Other exploitation attempts appear to be connected to a criminal cryptocurrency mining group based in China.
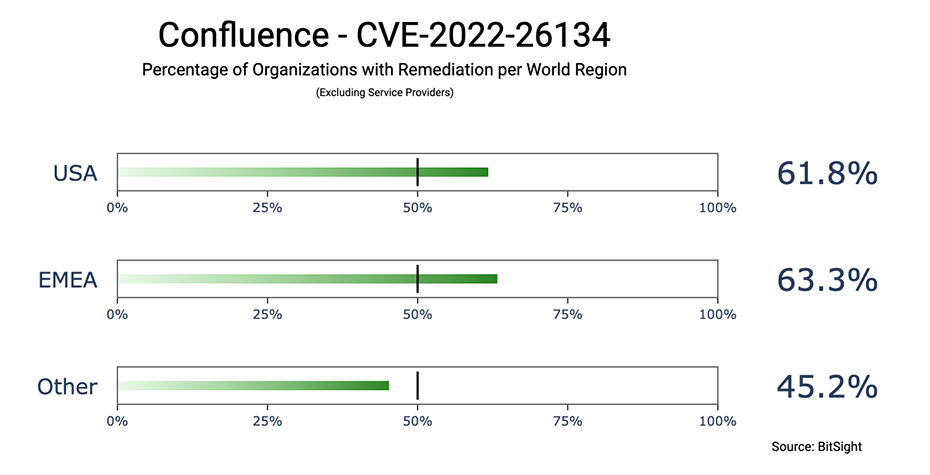
- Based on Bitsight’s observations, global vulnerability remediation is taking place but many organizations may still be vulnerable to CVE-2022-26134. Bitsight observes more than 60% of at-risk organizations in the United States and EMEA are no longer operating a vulnerable version of Confluence, while only 45% of at-risk organizations outside of these regions are no longer operating a vulnerable version.
- Because of the widespread usage of Confluence, this vulnerability represents a significant supply chain risk to many organizations; Bitsight observes that 199,000 companies are dependent on at least one potentially vulnerable organization. Organizations should evaluate their risk and exposure even if they do not directly use Confluence.
- To remediate the vulnerability, Atlassian urges users to upgrade to the latest version. If you cannot upgrade at this time, then Atlassian recommends a temporary mitigation involving updating specific files for the specific product version.
The Confluence vulnerability (CVE-2022-26134) is being actively exploited by cybercriminals, and you may be affected even if you do not use the software. Bitsight has uncovered that nearly 200,000 organizations are associated with at least one organization potentially vulnerable to CVE-2022-26134. If your organization shares data with a third party using Confluence, then your data may be at risk of disclosure and/or encryption. Now is a critical time to educate yourself on the topic, and prepare for future vulnerabilities.
What is Confluence?
Confluence is a collaborative team workspace developed by Australian software firm Atlassian. Firms may choose to store a wide variety of sensitive information on Confluence including trade secrets, patent filings, employee personal information, financial data, customer information, and planned business decisions.
What is the new Confluence vulnerability (tracked as CVE-2022-26134) and how could it affect my organization?
Atlassian’s Confluence Server and Confluence Data Center products have been impacted by a critical-severity remote code execution (RCE) zero-day vulnerability allowing an unauthenticated attacker to remotely take over servers hosting vulnerable Confluence versions. Attackers can achieve control of the server via creating new administrative accounts and executing arbitrary code.
Successful attacks can lead to ransomware deployment and data theft, and such attacks have already begun. Reports indicate that ransomware groups AvosLocker and Cerber2021 are actively exploiting the vulnerability, while some of the exploitation attempts appear to be connected to a Chinese cryptocurrency mining gang called the 8220 Mining Group. Given the use-case of Confluence as a company-wide information chest of sorts, the prospect of ransomware and data theft are serious. Adding to these concerns is the potential for business disruption and increased utility costs which could come into play if an attacker successfully exploits CVE-2022-26134 to implant cryptocurrency mining malware onto your machines.
Proof-of-concept (POC) exploits have already been made public, lowering the sophistication threshold required for threat actors to exploit CVE-2022-26134. This vulnerability is therefore surprisingly easy to exploit.
What are the supply chain implications of CVE-2022-26134?
Under these circumstances, third-party risk management (TPRM) should be top of mind for all organizations. Even if your organization does not use Confluence, you may still be affected via your supply chain. In fact, Bitsight observes that 199,000 organizations have an association with at least one potentially vulnerable organization.
The third-party supply chain implications are clear. Imagine you shared confidential intellectual property documentation with one of your third parties, like your company’s law firm. If the law firm used Confluence to store your sensitive information, then threat actors exploiting CVE-2022-26134 could gain access to your data via your legal firm and threaten to publicly share your confidential documents if you do not pay a ransom. Similarly, if you shared sensitive financial information or confidential business plans with another member of your supply chain then a threat actor could attack your vendor, encrypt your files, and demand a ransom for their decryption. Cybercriminals with a target in mind will often identify weak links within the target’s supply chain, opting to attack the target’s third parties as a way to obtain the target’s information for malicious purposes. CVE-2022-26134 serves as an example of a vulnerability that threat actors seek to exploit for these purposes.
Now is a good time to systematically reach out to your third parties to learn more about their use of Confluence and to obtain a better understanding of what data you have shared with them.
Why patching cadence is important for your organization.
The easiest way to protect yourself against CVE-2022-26134 is to patch or upgrade your Confluence instances and work with your third parties to ensure they have done the same. If not already completed, Atlassian urges users to upgrade to the latest version of Confluence. If you cannot upgrade at this time, then Atlassian recommends a temporary mitigation involving updating specific files for the specific product version.
CVE-2022-26134 should serve as a reminder to firms that patching cadence should not be overlooked. Now is a great time to reconvene as a firm and determine the efficacy of your current patching policies – as well as your third-party supply chain partners – and to make any improvements moving forward.
Patching cadence is particularly important to assess given the difficulty that some organizations have in implementing patches on a timely basis – even for a vulnerability as significant as Confluence. Bitsight observes that organizations are remediating Confluence at varying rates. U.S. and EMEA organizations – together comprising 70% of potentially vulnerable organizations1 – appear to be remediating faster than other organizations; however, there are still many organizations that have not remediated at the time of writing.
170% of potentially vulnerable organizations are headquartered in the United States and EMEA – 34% in the United States; and 36% in EMEA.
It is important not to assume that all organizations are remediating in the same timely fashion. Analyzing the risk of individual organizations, Bitsight finds many high-profile private sector and government organizations are still potentially vulnerable to CVE-2022-26134, including:
- A major metropolitan city located on the East Coast of the United States.
- A Fortune 500 technology firm.
- A State university system located on the West Coast of the United States.
- A national government located in Western Europe.
- A major metropolitan city located in Western Europe.
- A national APAC government.
- A national Ministry of Education located in APAC.
Outlined by the above list, Bitsight has identified that some of the largest organizations in the world are still potentially vulnerable to CVE-2022-26134. Adding to concerns, these organizations likely collect, store, and share large volumes of sensitive information. The fact that these organizations may still be vulnerable highlights the need for organizations to not only take seriously their own patching cadence but also the patching cadence of their third parties.
What can organizations do moving forward?
The Confluence vulnerability is one characterized by potential data theft, ransomware deployment, and third-party risk. Future vulnerabilities similar or greater in magnitude will inevitably present themselves as threats to your organization, either directly or indirectly via a third party. Properly managing your third-party footprint, patching cadence, and better understanding your attack surface, are all ways your organization can better defend itself against cyberattacks made possible by vulnerabilities like CVE-2022-26134.




