New! The Security Ratings report is now the Executive Report. Request your report to see enhanced analysis such as your rating, likelihood of ransomware incidents, and likelihood of data breach incidents.
Are Vendors Meeting Your Company’s Security Standards?

When it comes to vendor risk management, organizations ultimately need their vendors to meet the same standard of security performance they hold for their own organization. For years, the Finance industry has been a trailblazer in managing the risk posed by vendors, suppliers, and business partners. However, are vendors in the Finance supply chain meeting the same level of security performance held by Finance organizations?
To answer this question, Bitsight researchers looked at the security performance of more than 5,200 Legal, Technology, and Business Services global organizations whose security rating is tracked and monitored by hundreds of Finance firms using the Bitsight Security Rating platform. These industries represent a set of critical vendors and business partners in Financial Services supply chains, consisting of: legal organizations, accounting and human resources firms, management consulting and outsourcing firms, and information technology and software providers.
The Performance Gap
A significant gap exists between Finance firms and companies in their supply chain. As of September 1st 2017, the mean rating of Finance companies in this study was 710.
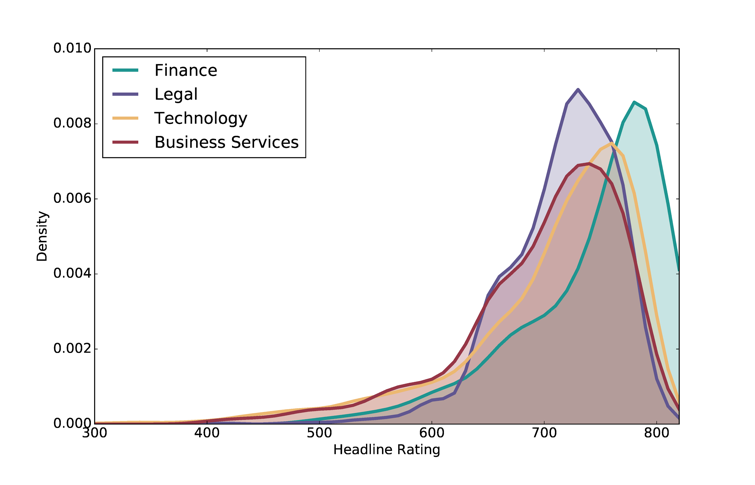
The spread of Bitsight Security Ratings amongst Finance Firms and monitored Legal, Technology, and Business Services organizations as of September 1st 2017.
However, the mean ratings for Legal Organizations, Technology Firms, and Business Services firms were 680, 670, and 660 respectively. While managing third-party cyber risk is a relatively new initiative for businesses, this performance gap illustrates the challenge Finance firms have in raising the security performance of key vendors and business partners.
Outdated Vendor Systems Present A Large Risk

What risks do vendors running outdated operating systems and browsers present for Finance organizations? Those in the Finance supply chain with a Desktop Software Grade of “B” or lower were more than twice as likely to have had a botnet in the past year. This means that outdated desktop operating systems and browsers that exist within a supply chain are correlated to more immediate risks of system compromise and data loss.
A vendor with outdated operating systems or browsers should prompt a discussion about why they have not made updates. Companies should ask vendors about their timeline for updates and continuously monitor their security to ensure progress is being made in this area. Given that outdated systems are likely to lead to machine compromise, it is a proactive way to safeguard your data.
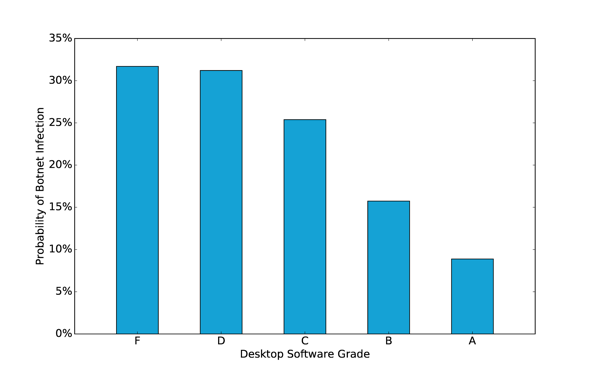
The Bitsight Desktop Software Grade for Business Services, Technology, and Legal firms as of July 1st, 2017. Desktop Software grades are comprised from the number and severity of outdated browsers and operating systems a company has on their network.
What Other Cyber Risks Exist in the Supply Chain?
Outdated systems aren’t the only cybersecurity risk present in supply chains. See how server software versions and peer-to-peer file sharing also present challenges for vendor risk management.



