Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Insights blog.
Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Slicing through CISA’s KEV Catalog

Slicing through CISA’s KEV Catalog
Dive into the critical insights of CISA's Known Exploited Vulnerabilities (KEV) Catalog with Bitsight’s latest blog! Discover how KEVs, which signal urgent cybersecurity risks, are being tracked and mitigated across industries. Learn why addressing these vulnerabilities quickly is vital and how it impacts organizational security.

Dridex is a banking trojan that uses an affiliate system for its botnets. We have documented the Dridex communication and P2P protocols in the past. In this post we want to shed some light about all the known botnets, their respective geographic targets, and how they are organized.
On February 12, 2013, President Barack Obama issued Executive Order 13636, “Improving Critical Infrastructure Cybersecurity,” which called for collaboration between government and the private sector to create a set of standards for organizations to identify, assess, and manage cybersecurity risk. This led to the NIST Cybersecurity Framework (CSF), a way for organizations to manage cybersecurity risk without the need for additional regulatory requirements. According to the Trends in Security Framework Adoption Survey earlier this year by Tenable Network Security, nearly a third of the organizations they surveyed leverage the NIST Cybersecurity Framework, with many respondents viewing it as an industry best practice.
Vendor security is becoming a focal point of risk management for many organizations. In many ways, this trend started with the Target breach from 2013, which highlighted the extensive financial and reputational impact of a third party security breach. Gartner estimates that by 2019, the need for transparency into operational and security activities within a vendor's value network will drive demand for vendor security by 30%.
With third parties becoming a major attack vector into organizations, Bitsight is focused on enabling security and vendor risk professionals to better prioritize their efforts when it comes to identifying and monitoring cyber security risks across their vendor ecosystem. Bitsight Security Ratings customers can now prioritize issues and receive customized alerts when the aggregate performance of multiple companies change.

In this article, we will be detailing an issue we discovered affecting a number of low-cost devices. It allowed for adversaries to remotely execute commands on the devices as a privileged user if they were in a position to conduct a Man-in-the-Middle attack. The binary responsible appears to be an insecure implementation of an OTA (Over-the-air) mechanism for device updates associated to the software company, Ragentek Group, in China. All transactions from the binary to the third-party endpoint occur over an unencrypted channel, which not only exposes user-specific information during these communications, but would allow an adversary to issue commands supported by the protocol. One of these commands allows for the execution of system commands. This issue affected devices out of the box.

Bolek is a recent malware from the Kbot/Carberp family. We first heard about this malware from the cert.pl blog post in May 2016, and since then, a few others have published additional information about it (links below).

Ransomware has been all the talk lately in the security industry- and deservedly so. These attacks have surged in the last year: hospitals, banks, and local police departments have all been infected with ransomware. Organizations have been paralyzed for days and weeks as a result of ransomware infections. In March, a MedStar Health clinic in Baltimore reportedly turned away patients and had trouble accessing electronic medical records. In a separate incident, the University of Calgary paid a $20,000 ransom earlier this year after malware encrypted the university's email servers. In addition to a financial loss for organizations that decide to pay ransoms, these attacks have the potential to cause severe operational disruptions for companies.

From time to time we have the opportunity to sinkhole domains that have an high volume of traffic and are part of a mobile device botnet. In the beginning of July we registered a domain that we found to be part of the AndroidBauts family with over 550,000 devices for a 24h period, affecting mostly India and Indonesia from a total of 216 countries. The piece of software that triggers this traffic was present in four (already removed) Google Play Store applications.
In June 2016, we observed an all time high of number of infections worldwide, breaking the previous record and raising the number of unique active observed IPs to 20,579,894 measured over a 7 day time window.

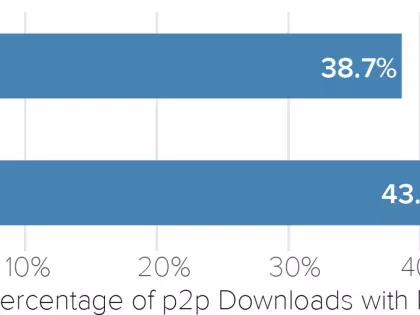
Despite all the complex cybersecurity threats facing organizations around the globe, employee behavior often leads to security compromise. In a recent Experian survey, 66% of data protection and privacy training professionals say employees at their organizations are the weakest security link. Yet beyond training and educating employees, there are policies and controls organizations can implement to further reduce risk. By eliminating Illicit peer-to-peer file sharing and properly configuring email security protocols, organizations can diminish the likelihood that employees will inadvertently introduce malware into company networks.

Anubis Networks began monitoring Necurs, a malware family known for it's rootkit capabilities, in August 2015. Since then we have been able to observe approximately 50.000 unique IP addresses connecting to our sinkhole over a 24 hour time period. However, we recently discovered that we were only seeing a small part of the whole botnet.
Bitsight is proud to announce the release of our latest research report, ”Bitsight Insights Global View: Revealing Security Metrics Across Major World Economies”. This report looks at the Security Ratings of a random sample of 250 companies from the United States, the United Kingdom, Singapore, Germany, China and Brazil from May 1, 2015 to May 1, 2016. Security and risk professionals can use the findings of this report can utilize these findings to better understand the potential cyber risks of doing business in foreign countries.

Bitsight is proud to announce the release of new features that provide expanded data breadth to all customers. These new innovations enable customers to better identify risks in third party networks and their own networks. Annotations, a new innovation in the security ratings market that allows customers to add tags to specific parts of their network asset maps, providing context for customers to take appropriate action with new events on their network or the network of a third party. Furthering Bitsight’s mission to provide actionable data, Patching Cadence, the newest Diligence risk vector, is expanding data breadth in the platform. This risk vector evaluates a company’s responsiveness in patching major vulnerabilities. Learn more about these features that are helping customers better manage and streamline their security risk management efforts:

GhostPush is an Android malware that was first discovered in September 2015. Once installed on a user’s device, it will display unsolicited advertising, and install unwanted applications on the user’s device. This malware is also known for rooting the user’s device and making itself very hard to uninstall.
This is the final entry in a three-part series on Bitsight’s new Event Store. In the first and second posts, we described some key components of the architecture. Because of the limited number of access patterns we had to support (bulk inserts, mostly in chronological order; full scans, coarsely filtered by key range and time), we were able to implement a simple NoSQL-style database, using flat Parquet files on Amazon’s S3 as the storage layer.