Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Insights blog.
Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Slicing through CISA’s KEV Catalog

Slicing through CISA’s KEV Catalog
Dive into the critical insights of CISA's Known Exploited Vulnerabilities (KEV) Catalog with Bitsight’s latest blog! Discover how KEVs, which signal urgent cybersecurity risks, are being tracked and mitigated across industries. Learn why addressing these vulnerabilities quickly is vital and how it impacts organizational security.
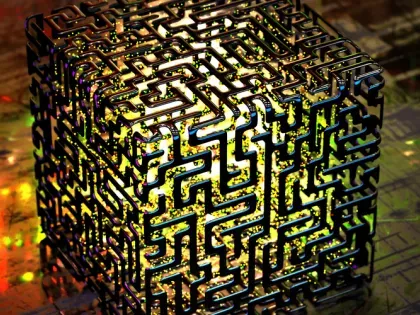
Quantum computing has the ability to change the world, both for better and worse, and while it may be far off in the future, security teams need to start preparing for the new reality it will usher in.

This week, Microsoft ended support for the Windows 7 operating system. Among other implications, Microsoft will no longer issue security patches for the nine-year-old OS. Any organization relying on the OS moving forward could be susceptible to a security issue, attack or data breach unless they purchased extended support from Microsoft.

Companies must build a “trust and verify” strategy when it comes to managing third party risk. Requesting documentation about a supplier’s security performance is good – but how can you verify it? How can you continuously review performance?

Cyber risk and regulatory compliance are two sides of the same coin in the Financial Services sector. Together, they spur Financial Services companies to take action to protect customers, their business and the global financial ecosystem from the malicious cyber attacks or the risk of critical system failures.

The evolution of the technology environment and related security threats is so fast paced it often seems businesses and regulators are playing an endless game of catch-up.

The regulatory environment is evolving rapidly as national and international regulatory bodies attempt to keep pace with changing business models, technology infrastructure and continuously escalating cyberthreats.

About 25 years ago, the evolution of the overall digital ecosystem necessitated the creation of the first CISO role. Now, 61% of companies have a CISO.

Management consultants, accountants, public safety offices, marketing firms, and many more business and professional services organizations are high-value targets for cybercriminals due to the range of confidential client information they handle. Companies in this sector should all have solid security postures — and many do. But there’s still an alarming number of enterprises that do not.

Cyber attacks are occurring more frequently and banks, insurance companies, and other financial services firms are prime targets. Due to the nature of these businesses and the sensitivity of their data, financial firms are hit with approximately 300 times more cyber attacks than businesses in other industries.

A new report from the Information Security Forum (ISF) contains some fascinating insights into how hackers probe and exploit people's psychological vulnerabilities to gain access to corporate systems. From phishing to "whaling" (targeting high level executives) to "baiting" (offering something in return for credentials or information), hackers are using several tactics to gain a foothold. They also know the best time to deploy those tactics – at the end of the day, for example, when a person is tired and may not make the best decisions.

Technology companies — along with their partner ecosystems — are some of the most targeted organizations when it comes to cyber-attacks. In 2018, enterprises invested an average of 3.5 million on cloud apps, platforms, and services — making the sensitive information held in those platforms a top target for hackers.

Healthcare is under attack. Hospitals, doctors’ networks, insurance companies, and others are prime targets for hackers due to the valuable protected health information (PHI) they store and the vital role they play in our nation’s critical infrastructure.

Cybersecurity threats are becoming more sophisticated, targeted, and potentially catastrophic. This is particularly true of the most dominant form of cyberattack – ransomware.
Stress and burnout is emerging as perhaps the biggest threat to corporate security. Long hours, alert overload, and a lack of visibility into their IT infrastructure have many security professionals reconsidering their chosen careers.

2019 has already been rife with cybersecurity woes. Unfortunately, as we enter the second half of the year, things are going from bad to worse.