Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Insights blog.
Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Slicing through CISA’s KEV Catalog

Slicing through CISA’s KEV Catalog
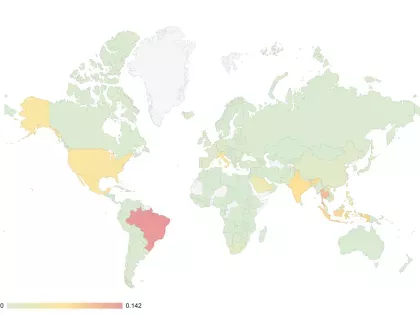
Dive into the critical insights of CISA's Known Exploited Vulnerabilities (KEV) Catalog with Bitsight’s latest blog! Discover how KEVs, which signal urgent cybersecurity risks, are being tracked and mitigated across industries. Learn why addressing these vulnerabilities quickly is vital and how it impacts organizational security.

In 2021, ransomware attacks on government agencies globally increased by 1,885% over 2020 attacks, and the trends are continuing so far in 2022. Learn how to protect your organization from ransomware with three best practices.

Atlassian Confluence has been impacted by vulnerability CVE-2022-26134 allowing for ransomware deployment, data theft, & more. See Bitsight's findings & analysis.

The federal government is using every tool possible to deter and disrupt retaliatory cyberattacks against critical national infrastructure. With the Strengthening American Cybersecurity Act, agencies are required to report cybersecurity incidents within a 72 hour period. Learn more.
In November 2021, a new version of the Emotet botnet emerged. How did this happen? What is the botnet doing today? And how can organizations avoid becoming victims? Get the answers and more.

Ransomware isn’t going away; security leaders need to get inside the brain of ransomware sleuths and learn how attacks develop to better identify early indicators of ransomware in their network. Read on to learn how ransomware attacks happen.

This article contains tips for security and risk professionals to manage risk from their Single Sign-On (SSO) providers and better protect their users’ credentials.

What is cyber insurance underwriting, how has it evolved, and what you can expect when you apply for cyber insurance.

Organizations remain concerned about the potential implications to their own security posture as a result of the Okta cyber attack. It's important to identify where risks are present throughout your third parties landscape.

As internet use continues moving toward a mobile-centric experience, it has become essential to consider mobile applications when crafting a security strategy. Bitsight’s latest research demonstrates exactly why. We are excited to announce that Bitsight Insights: Mobile Application Risk Report is available now.

Learn how to use cyber risk data to protect your organization and its financial assets.

You can’t reduce the cyber risks faced by your organization if you don’t know what you’re up against. That’s the purpose of a vulnerability probe.

While the ongoing wave of digital transformation opens exciting opportunities for innovation, it also widens your attack surface.

Today’s opportunistic hackers are seasoned professionals who are getting more adept at exploiting your organization’s digital attack surface. To do this they employ a variety of attack vectors.

Given the recent security breaches and reported hacking attempts, it is increasingly important for companies to have a handle on their most sensitive data. Sensitive data can include employees’ personal information, customer information, trade secrets, and other types of data that would cause internal breaches to company information if obtained by a hacker. To identify your organizations’ sensitive data points, refer to our recent article highlighting 5 examples of sensitive data.

Working from home introduces significant cyber risk to any organization. However, recent events reveal that it’s not a case of “if” but “when” bad actors will exploit the rampant vulnerabilities on home networks.